Best Cybersecurity Software Shortlist
Here’s my shortlist of the best cybersecurity software:
The best cybersecurity software helps you detect threats early, block unauthorized access, and protect sensitive data across endpoints, networks, and cloud environments.
If you’ve dealt with agents that bog down system performance, alerts that flood your inbox without context, or tools that don’t work well together, you know how frustrating it is to piece together a reliable security posture. Many teams also run into problems with visibility, especially when supporting hybrid or remote environments, or trying to layer protection across legacy infrastructure.
I’ve tested and implemented dozens of cybersecurity tools in enterprise and SaaS environments, working closely with teams to secure everything from endpoints to cloud-based services. This guide breaks down the platforms that offer clean integrations, meaningful alerting, and the visibility you need to respond quickly without getting buried in noise.
Why Trust Our Software Reviews
Best Cybersecurity Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for compliance-focused TPRM programs | Free demo available | Pricing upon request | Website | |
| 2 | Best for real-time behavioral detection | 30-day free trial + free demo available | Pricing upon request | Website | |
| 3 | Best for continuous vulnerability detection | Free demo available | From $69/month | Website | |
| 4 | Best for secure VPN privacy | 30-day free trial | From $119.99/year (billed annually) | Website | |
| 5 | Best for Google Workspace and Microsoft 365 | Free demo available | From $4/user/month (billed annually) | Website | |
| 6 | Best for DNS-level threat blocking | 14-day free trial + free demo available | From $7/user/month (billed annually) | Website | |
| 7 | Best for AI-driven auto-triage | Free plan available | From $34/developer/month | Website | |
| 8 | Best for company-wide password policies | Free plan available | From $1.79/user/month | Website | |
| 9 | Best for real-time threat alerts | Not available | Pricing upon request | Website | |
| 10 | Best for context-aware code security | Free plan available | From $200/month | Website | |
| 11 | Best for code-to-cloud security | Free plan available + free demo | From $350/month | Website | |
| 12 | Best for real-time log visibility | Free demo available | From $0.09/GB/month | Website | |
| 13 | Best for managing and securing IT infrastructure | 30-day free trial available | From $795/50 endpoints/year | Website | |
| 14 | Best for integrated DLP and CASB capabilities | Free demo available | Pricing upon request | Website | |
| 15 | Best with DNS security and ransomware protection | Free trial + free demo available | Pricing upon request | Website | |
| 16 | Best rootkit scanner | 14-day free trial + free demo available | From $49.99/year | Website | |
| 17 | Best for proactive threat detection | 30-day free trial + free demo available | From $338.50/year | Website | |
| 18 | Best for securing applications | Free demo + 15-day free trial available | From $7/host/month (billed annually) | Website | |
| 19 | Best for ITOps teams | Free trial available | From $59.99/device (billed annually) | Website | |
| 20 | Best for full-stack observability | Free trial + free demo available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Cybersecurity Software Reviews
Below are my picks for the best cybersecurity software with brief but detailed rundowns to help you compare their strengths, weaknesses, and pricing:
Prevalent is a cybersecurity platform focused on reducing risks tied to third-party vendors. It helps you assess, monitor, and manage vendor security throughout the relationship lifecycle, offering tools for compliance, risk validation, and incident response along the way.
Why I Picked Prevalent: I picked Prevalent because third-party risk is one of the most overlooked cybersecurity vulnerabilities, and this platform helps you stay ahead of it. I like how it centralizes risk data, continuously monitors vendors for emerging threats, and categorizes them by inherent risk level. This can give your security team the clarity needed to prioritize efforts and address vulnerabilities tied to external vendors. Prevalent also supports compliance reporting, so you can meet regulatory standards with less manual work.
Prevalent Standout Features & Integrations:
Features include tools for remediation management, making it easier to close gaps when risks are identified. Its platform offers continuous monitoring to validate vendor controls against evolving threats, and AI-powered risk scoring helps prioritize vendors based on their exposure levels. Additionally, the system provides reporting to support regulatory compliance across industries.
Integrations include BitSight Security Ratings, ServiceNow, SecZetta, Source Defense, and Connector Marketplace.
Pros and Cons
Pros:
- Strong security protocols to protect data
- Users can tailor reports according to specific needs
- Extensive functionalities for managing vendor risk
Cons:
- Challenges in migrating data can complicate the initial setup
- The platform is complex and comes with a learning curve
Radware is a cybersecurity solution built to defend against malicious automated traffic. It uses machine learning and behavioral analysis to detect and block harmful bots in real time, helping organizations prevent fraud, account takeovers, scraping, and DDoS attacks. As part of Radware’s unified security suite, it integrates bot management with broader network and application protection capabilities.
Why I picked Radware: I picked Radware because it goes beyond simple IP filtering by using AI-based behavior modeling to distinguish legitimate users from bots with high accuracy. If you’re facing issues with credential stuffing, web scraping, or fake traffic distorting analytics, this tool helps you stay a step ahead. I also like that it works across multiple environments, integrating seamlessly with CDNs and SIEM platforms so you can view all your bot protection data in one place.
Radware standout features and integrations:
Features include AI-based detection, deep behavioral analysis, and threat protection for account takeovers, DDoS, and web scraping. It also offers advanced fingerprinting, anomaly detection, and detailed traffic analytics for visibility into malicious activity.
Integrations include Akamai CDN, VMware, Splunk, ArcSight, ELK, Ubuntu, and RedHat.
Pros and Cons
Pros:
- Strong integration with SIEM tools
- Comprehensive traffic analytics reporting
- Accurate AI-based bot detection
Cons:
- Interface could be more intuitive
- Limited pricing transparency available
Astra Pentest is a cybersecurity platform that helps you identify and remediate vulnerabilities across web applications, networks, APIs, and cloud environments. It combines automated scanning with expert-led manual penetration testing, giving organizations continuous visibility into their security posture.
Why I picked Astra Pentest: I picked Astra Pentest because it blends automation with human insight. Its scanner runs more than 8,000 tests, which can uncover everything from common misconfigurations to complex zero-day vulnerabilities. I also like that you can schedule continuous scans and integrate them directly into your CI/CD pipeline—so you’re notified of risks before code ever goes live. If you’re responsible for keeping production systems secure, this tool helps you stay proactive instead of reactive.
Astra Pentest standout features and integrations:
Features include automated and manual penetration testing, continuous vulnerability scanning, detailed remediation reporting, and compliance mapping for ISO 27001, SOC 2, PCI-DSS, HIPAA, and GDPR. It also includes a centralized vulnerability management dashboard that makes it easier to track fixes and verify patches.
Integrations include GitHub, Jira, Slack, Jenkins, and Azure.
Pros and Cons
Pros:
- Excellent compliance reporting options
- Integrates easily with CI/CD tools
- Combines automated and manual testing
Cons:
- Pricing available upon request
- Occasional false positives reported
Norton offers a suite of cybersecurity solutions tailored for small businesses, with a focus on secure VPN privacy alongside core security needs. Small business owners may find Norton appealing if they want to protect business data and online activity without relying on complex IT setups. With features such as device security, VPN access, and identity protection, Norton supports everyday security requirements in an increasingly digital environment.
Why I Picked Norton
I picked Norton for its focus on secure VPN privacy, which helps protect online activity for small teams without complex setup. The VPN works alongside device security to reduce exposure to common threats like malware and ransomware. Norton also includes identity protection through LifeLock, which monitors for identity misuse and sends alerts to help safeguard sensitive business information.
Norton Key Features
In addition to secure VPN privacy, Norton offers:
- Cloud Backup: Safeguard your business data with secure cloud storage options.
- Password Manager: Simplify and secure your password management with an encrypted vault.
- Dark Web Monitoring: Receive alerts if your information is found on the dark web.
- 24/7 Business Tech Support: Access round-the-clock support for any technical issues or virus removal assistance.
Norton Integrations
Native integrations are not currently listed by Norton.
Pros and Cons
Pros:
- Frequent updates address new and evolving online threats
- Covers multiple devices under one subscription
- Strong device protection against malware and ransomware
Cons:
- VPN features may have usage limits on lower plans
- Users report increased advertisements within the software
Material Security's platform provides a specialized solution for those looking to protect their cloud workspaces, particularly for Google Workspace and Microsoft 365 users. Designed with a focus on enhancing security without stifling collaboration, it is ideal for organizations that need to address advanced threats, manage data sharing, and detect risky behaviors.
Why I Picked Material Security
I picked Material Security because it excels at providing comprehensive protection for cloud-based environments, a critical need for organizations leveraging Google Workspace and Microsoft 365. Its standout feature is the automated threat response capability, which allows you to swiftly handle phishing attempts and other email threats without manual intervention.
Additionally, Material Security’s file security feature manages sensitive data sharing effectively, ensuring that your team’s information remains confidential and secure. The visibility into third-party app usage is another crucial feature that helps in monitoring and managing potential security risks.
Material Security Key Features
In addition to its automated threat response and file security, here are some other key features:
- Email Security: Automatically detects and remediates malicious emails that bypass native controls, essential for combating phishing threats.
- Account Security: Provides tools to identify and mitigate risky behaviors, strengthening overall account protection.
- Proactive Incident Response: Enables a proactive approach to handling security incidents, reducing the impact on your organization.
- SOC 2 Type 2 Certification: Ensures compliance and accountability, with documented code changes and isolated deployments for customer environments.
Material Security Integrations
Integrations include Google Workspace, Microsoft 365, and an API for custom integrations.
Pros and Cons
Pros:
- Enables secure file sharing within email communications.
- Supports advanced threat protection for email accounts.
- Automates phishing response to improve response times.
Cons:
- Limited native integrations with other security tools.
- Dependency on cloud infrastructure may introduce latency issues.
NordLayer is a network access security solution designed to help businesses protect their digital environments. It offers tools like business VPN, Zero Trust Network Access (ZTNA), and threat protection to ensure secure connections for remote employees and safeguard sensitive company resources.
Why I picked NordLayer: I like its DNS filtering capability that blocks access to malicious websites by evaluating requests at the DNS level, preventing harmful content from reaching your devices. By stopping threats before they can cause damage, your team can browse the internet more safely. It also offers download protection that scans files in real-time during the download process, removing any malicious code immediately.
NordLayer standout features and integrations:
Features include internet access security, private access security, network connectors, compliance aid, identity and access management, cloud network integration, centralized control panel, dedicated IP addresses, site-to-site VPN, network segmentation, single sign-on (SSO), multi-factor authentication (MFA).
Integrations include Entra ID, Okta, OneLogin, JumpCloud, Google Workspace, Google Cloud, IBM Cloud, and AWS.
Pros and Cons
Pros:
- Security measures like AES-256 encryption and multi-factor authentication
- Extensive access control and session monitoring
- Utilizes a zero-trust framework
Cons:
- Server setup can be complex
- Number of available server locations could be expanded
Corgea is built for businesses and professionals who take cybersecurity seriously. It uses AI-driven tools to identify and fix insecure code, helping developers and security teams automate the detection of vulnerabilities like business logic flaws and sensitive data leaks. This automation can streamline application security work significantly. By improving web safety while boosting productivity, Corgea addresses the need for cybersecurity tools that are both efficient and effective.
Why I Picked Corgea
I picked Corgea for its AI-driven auto-triage, which cuts down on false positives, a common problem with security tools. This lets your team focus on real threats instead of sorting through unnecessary alerts. Corgea also automatically issues security patches, making it easier to address vulnerabilities quickly. Together, these features make Corgea a strong choice for organizations that want to strengthen their application security operations without adding extra overhead.
Corgea Key Features
In addition to its AI-driven auto-triage, Corgea offers several other features that enhance its functionality as a cybersecurity tool.
- Customizable Policies: Allows your team to set security policies in natural language, making it easier to tailor the software to your specific security needs.
- Secrets Detection: Identifies and alerts you about potential privacy leaks of sensitive information, such as AWS keys and authentication credentials.
- SAST Auto-Fix: Automatically fixes code vulnerabilities detected by Static Application Security Testing, reducing manual intervention and improving security response times.
- Dependency Scanning: Scans for vulnerable dependencies across various programming languages, ensuring that third-party components do not compromise your application's security.
Corgea Integrations
Native integrations are not currently listed by Corgea.
Pros and Cons
Pros:
- Business logic flaw detection
- Automatic secure code fixes
- AI-driven vulnerability detection
Cons:
- AppSec-focused, not full stack
- No runtime protection features
NordPass is a business password manager designed to enhance cybersecurity for organizations by securely managing passwords and sensitive information. It provides a centralized, encrypted vault for storing complex credentials, ensuring that your data remains protected while simplifying access for employees.
Why I Picked NordPass: I chose NordPass for its strong security features, including company-wide password policies, compliance with ISO 27001 and SOC 2 standards, and robust encryption under a zero-knowledge policy. Its Security Dashboard also helps monitor password health and address potential breaches, making NordPass a reliable choice for protecting an organization’s digital assets.
NordPass standout features and integrations:
Features include a built-in authenticator for managing passwords and TOTP codes, which adds an extra layer of security to your accounts. The sharing hub provides centralized control of shared credentials, ensuring that sensitive information is only accessible to those who need it. Additionally, NordPass offers seamless synchronization across devices, allowing your team to access their credentials from anywhere without compromising security.
Integrations include Entra ID, MS ADFS, Okta, Google Workspace, Splunk®, and Microsoft Sentinel.
Pros and Cons
Pros:
- Centralized control through sharing hub
- Easy integrations with major ID providers
- Strong encryption with zero-knowledge policy
Cons:
- Offline access issues reported frequently
- Autofill functionality occasionally inconsistent
NordStellar is an external threat intelligence platform designed to boost your organization’s cybersecurity. It offers an array of features that help businesses stay ahead of potential threats by providing real-time alerts and monitoring dark web activities.
Why I Picked NordStellar: I picked NordStellar because it offers advanced cyber threat monitoring with real-time alerts for data breaches and account takeovers, helping protect sensitive business information from unauthorized access. Its attack surface management automates asset discovery and scans for vulnerabilities, while brand protection tools prevent misuse of your company’s assets online. With centralized intelligence that unifies breach data, dark web insights, and attack surface information, NordStellar gives you full visibility and control over your organization’s security landscape.
NordStellar standout features and integrations:
Features include risk assessments that help you understand potential vulnerabilities, threat exposure management to keep track of emerging threats, and actionable insights that guide your security strategies. These features work together to provide a holistic view of your cybersecurity posture, making it easier for you to make informed decisions about your organization’s security needs. The platform's focus on privacy and data protection ensures that your information remains secure while you benefit from its comprehensive threat management capabilities.
Integrations include Splunk, QRadar, Datadog, Fortinet, Sentinel, Elastic, and Cortex.
Pros and Cons
Pros:
- Centralized threat intelligence platform
- Automated asset discovery system
- Real-time alerts for breaches
Cons:
- Limited pricing transparency available
- Minimum five-user annual plan
ZeroPath helps your engineering and security teams by embedding AI-native code security into the development pipeline, allowing you to catch hidden vulnerabilities like business-logic flaws, auth bypasses or flawed dependencies long before release. If you’re a DevOps or DevSecOps team in a tech-forward company—whether in fintech, healthcare or SaaS—and you’re tired of being flooded by false positives from traditional SAST tools, this tool might be the key.
Why I Picked Zeropath
I picked ZeroPath because it targets one of the most critical challenges in application security today: reducing noise while elevating detection quality. Its AI-native SAST engine identifies exploitable vulnerabilities by understanding code context (rather than relying purely on pattern matching), and it auto-generates remediation patches—so your team spends less time triaging non-issues and more time shipping secure code. These features align closely with what modern engineering orgs need: tools that support speed and safety without forcing a trade-off.
Zeropath Key Features
In addition to its core functionalities, ZeroPath offers:
- Custom Code Policies: You can define arbitrary security rules using natural-language policy syntax and enforce them across your repositories.
- Secrets Detection: The tool scans for leaked or hardcoded credentials and validates them with context to reduce false alarms.
- Infrastructure as Code (IaC) Scanning: It analyzes your IaC configurations (e.g., for cloud infrastructure) for misconfigurations and vulnerabilities.
- Security Intelligence & Risk Dashboard: Provides executive-level dashboards, compliance reporting (e.g., SOC2/ISO27001) and vulnerability trends and metrics across all your repos.
Zeropath Integrations
Integrations include GitHub, GitLab, Bitbucket, Azure DevOps, Jira, Jenkins, Slack, Microsoft Teams, and CircleCI.
Pros and Cons
Pros:
- Supports one-click patches that match your team’s code style.
- Gives clear, context-aware vulnerability fixes for developers.
- Unified platform for SAST, SCA, IaC and secrets scans.
Cons:
- You may need time to adjust your workflow around its automation.
- Not ideal if you're looking for broader cybersecurity features outside of AppSec.
Aikido Security is tailored for developers and businesses that seek to enhance their software security from code to cloud. By automating threat detection and response, it addresses the challenges of managing security across diverse environments, ensuring that your applications remain robust and secure.
Why I Picked Aikido Security
I picked Aikido Security because it excels in providing comprehensive code-to-cloud security, which is crucial for any organization looking to safeguard their software assets. Aikido's integration of static and dynamic code analysis ensures that vulnerabilities are identified and addressed early in the development process. Additionally, its cloud security posture management offers visibility into potential risks across your cloud infrastructure. These features, combined with AI-driven automated fixes, make Aikido a reliable choice for maintaining a strong security posture.
Aikido Security Key Features
In addition to its comprehensive code-to-cloud security, I also found several features that enhance Aikido's appeal:
- Secrets Detection: Identifies exposed API keys and sensitive information within your code, preventing unauthorized access.
- Runtime Protection: Provides an in-app firewall to block critical injection attacks and manage API rate limits.
- Container Image Scanning: Analyzes container OS for security issues, ensuring your containerized applications are secure.
- Autonomous Pentests: Automates penetration testing to uncover vulnerabilities before they can be exploited.
Aikido Security Integrations
Integrations include GitHub, GitLab, Bitbucket, Jira, Microsoft Teams, Slack, Google Cloud, AWS, Azure, and Docker.
Pros and Cons
Pros:
- Scalable for growing teams
- Offers actionable insights
- Has a comprehensive dashboard and customizable reports
Cons:
- Does not have endpoint security or intrusion detection capabilities
- Ignores vulnerabilities if no fix is available
Logmanager is a log management and Security Information and Event Management (SIEM) platform that helps organizations detect, analyze, and respond to security incidents in real time. It centralizes log data from across your infrastructure to provide complete visibility into network activity, compliance status, and potential threats. As a cybersecurity solution, it strengthens your security posture through continuous monitoring and actionable analytics.
Why I picked Logmanager: I picked Logmanager for its ability to deliver immediate insights from diverse log sources without complex setup. You can spot anomalies, detect potential intrusions, and respond faster thanks to its real-time monitoring and advanced search capabilities. I also like that it simplifies compliance for frameworks like GDPR, DORA, and HIPAA, giving you automated alerts and reports that keep you audit-ready with minimal manual effort.
Logmanager standout features and integrations:
Features include real-time log monitoring, advanced security analytics, compliance reporting, high availability, and customizable dashboards that help you track security performance at a glance. It supports over 140 log sources and offers a no-code configuration interface, making it easy to adapt to any IT environment.
Integrations include Cookiebot, Google, HubSpot, Microsoft 365, Apache Tomcat, Cisco ASA, Fortinet Products, MySQL, NGINX, and VMware.
Pros and Cons
Pros:
- Strong compliance reporting support
- Comprehensive log analysis tools
- Quick deployment and setup
Cons:
- Some features require expertise
- Interface could be more modern
Best for managing and securing IT infrastructure
ManageEngine Desktop Central is an integrated endpoint management solution designed to assist in the administration and security of IT assets within an organization.
Why I picked ManageEngine Desktop Central: ManageEngine Desktop Central provides a unified solution for endpoint management and security, which is essential for protecting an organization's IT infrastructure. This integration allows for centralized control over various devices, contributing to improved security measures and simplified IT operations. Additionally, the platform's automated patching system and proactive security features are particularly notable, as they help maintain system integrity and protect against vulnerabilities without the need for constant manual intervention.
ManageEngine Desktop Central standout features and integrations:
Features include vulnerability remediation, next-gen antivirus, browser security, application control, data security, remote desktop management, patch management, software deployment, endpoint security, and identity and access management. It also offers OS imaging and deployment, configuration management, and reporting and auditing to ensure compliance with various regulatory requirements.
Integrations include ServiceNow, Jira, Zoho Desk, Zendesk, Jira Service Desk, Microsoft SCCM, IBM BigFix, Slack, Microsoft Teams, Trello, Zapier, ManageEngine ServiceDesk Plus, Microsoft Intune, and more.
Pros and Cons
Pros:
- Extensive customization and configurations
- Consistent patch management
- Secure remote control and desktop sharing
Cons:
- Limited mobile device management features
- Steep learning curve
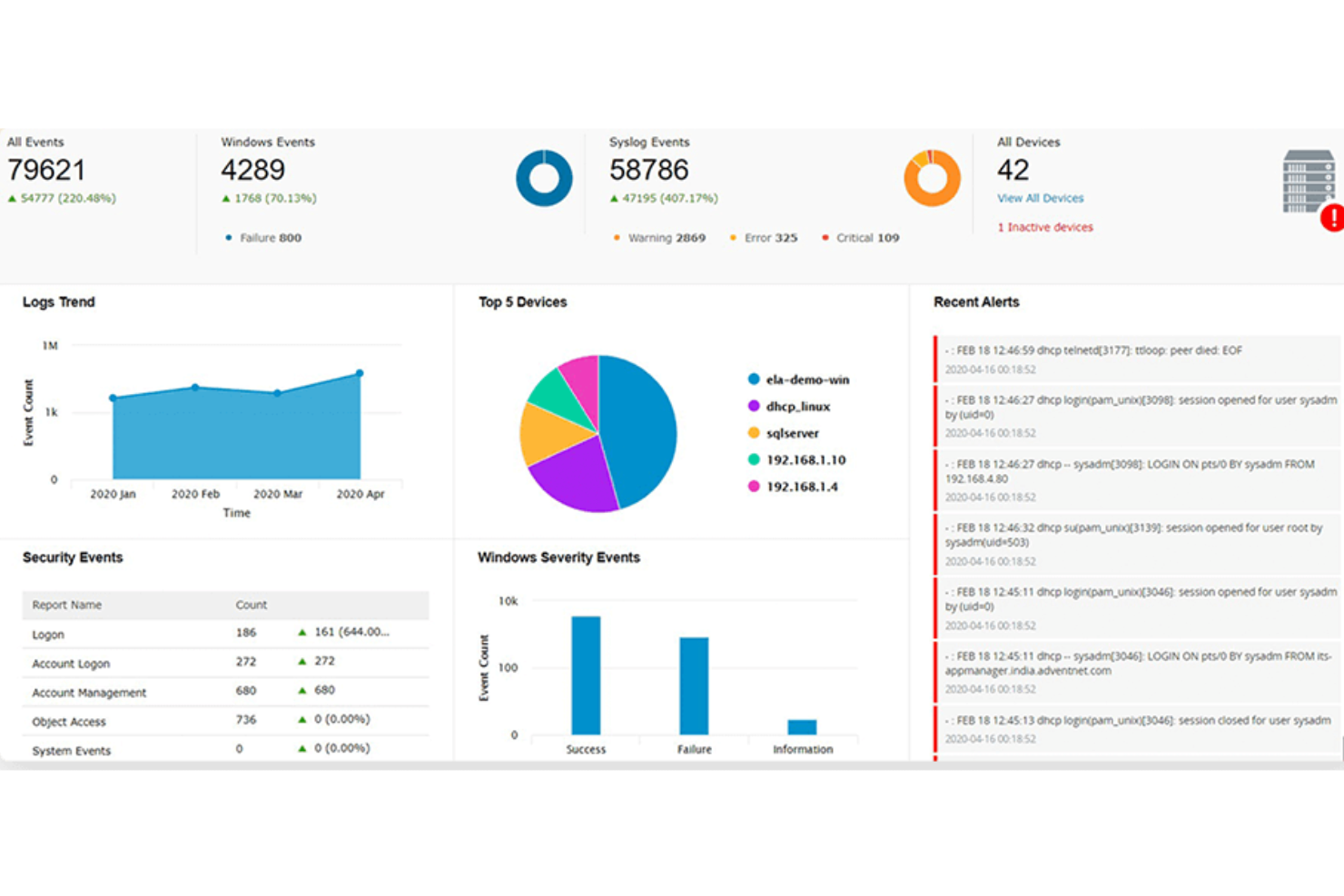
ManageEngine Log360 is a security information and event management (SIEM) solution designed to help organizations manage and analyze logs from various sources, including on-premises, cloud, and hybrid environments.
Why I picked ManageEngine Log360: It offers a comprehensive feature set that addresses a wide range of security needs. Its ability to integrate SIEM, DLP, and CASB functionalities into a single platform makes it particularly stand out. The software excels in threat detection and response through its machine learning-based anomaly detection and rule-based attack detection techniques. Furthermore, its ability to provide real-time insights and analytics across on-premises, cloud, and hybrid environments ensures thorough security coverage.
ManageEngine Log360 standout features and integrations:
Features include advanced security analytics, log management, real-time Active Directory change auditing, compliance management, incident management, user and entity behavior analytics, automated threat response, security event correlation, alerting and reporting, forensic analysis, and data aggregation.
Integrations include Microsoft Active Directory, Office 365, Google Workspace, AWS, Azure, Salesforce, Box, Dropbox, ServiceNow, Jira, Slack, IBM QRadar, Splunk, SolarWinds, Palo Alto Networks, Fortinet, Cisco, and Sophos.
Pros and Cons
Pros:
- Threat intelligence features
- Robust compliance management capabilities
- Real-time log collection and analysis
Cons:
- The tool requires regular maintenance and updates
- Setup and configuration process can be complex
In an era where digital threats are increasingly sophisticated, Heimdal emerges as a cybersecurity solution tailored for businesses across sectors like healthcare, finance, and education. It offers a holistic approach to security with features designed to protect your data and systems. If you're looking to safeguard your organization against cyber threats while ensuring compliance with industry regulations, Heimdal's comprehensive platform addresses these critical needs effectively.
Why I Picked Heimdal
I picked Heimdal for its unique ability to unify security operations through its Extended Detection and Response (XDR) capabilities. This feature allows your team to detect and respond to threats across the entire digital environment. Another standout feature is its DNS Security, which proactively blocks malicious websites and prevents data breaches. Heimdal's Ransomware Encryption Protection is also notable, offering an added layer of defence against unauthorized file encryption, a critical concern for any organization.
Heimdal Key Features
In addition to its XDR capabilities, Heimdal offers:
- Privileged Access Management: This feature controls and monitors user access to sensitive systems and data, minimizing the risk of insider threats.
- Patch & Asset Management: Automatically updates and manages software patches across all endpoints, reducing vulnerabilities.
- AI-Powered Email Security: Protects against phishing attacks and malware by analyzing email content using advanced AI algorithms.
- Threat Hunting: Enables proactive threat detection and response by continuously monitoring and analyzing suspicious activities.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
Malwarebytes provides anti-malware and cybersecurity services for devices used by both personal and business customers.
Why I picked Malwarebytes: I chose malwarebytes because it provides a free rootkit scanner that makes it easier to find these notoriously difficult-to-detect forms of malware. It uses the same approach to heuristics and anomaly detection that goes into addressing zero-day attacks so you can deal with rootkits as soon as possible. I also liked their antivirus and VPN products.
Malwarebytes standout features and integrations:
Features that I took note of while evaluating Malwarebytes’ rootkit scanner include automatic repairs of any system files and services that might have been damaged by an infection. It also scans first and provides you with a list of rootkits it discovers so you can review them before taking action. This way, you can ensure that it doesn’t interfere with any ethical hacking exercises you have in progress.
Integrations are pre-built for ServiceNow, Slack, Datto RMM, Azure Sentinel, IBM QRadar, Splunk, Rapid7, Addigy, Atera, and ConnectWise.
Pros and Cons
Pros:
- Premium plans are relatively cheap, especially for businesses
- Free antivirus and rootkit scanner
- Beginner-friendly and intuitive design
Cons:
- Some features are Windows-only
- Free plan is a comprehensive enough security solution on its own
ESET PROTECT Complete is a comprehensive cybersecurity software focusing on prevention, detection, and response.
Why I picked ESET PROTECT Complete: This software takes a proactive approach to managing cyber threats. Leveraging technologies like AI, the platform helps prevent breaches and investigate incidents while providing an easy-to-understand interface that captures all you need to know in a single dashboard. You'll also have access to detailed reports with actionable steps to keep your IT infrastructure secure.
ESET PROTECT Complete standout features and integrations:
The platform offers a full suite of protection features, including its Management Console, Endpoint Protection, File Server Security, Full Disk Encryption, Advanced Threat Defense, Mail Security, and Cloud App Protection. This allows you to monitor the security of your entire business environment and receive real-time insights to minimize operational disruptions.
Integrations include ConnectWise Automate, Datto RMM, NinjaOne, Kaseya VSA, ATERA, and more.
Pros and Cons
Pros:
- Protection for all your devices and apps
- Allows for remote management
- Wide variety of detailed reports
Cons:
- May slow down devices during scans and updates
- Can be expensive for some users
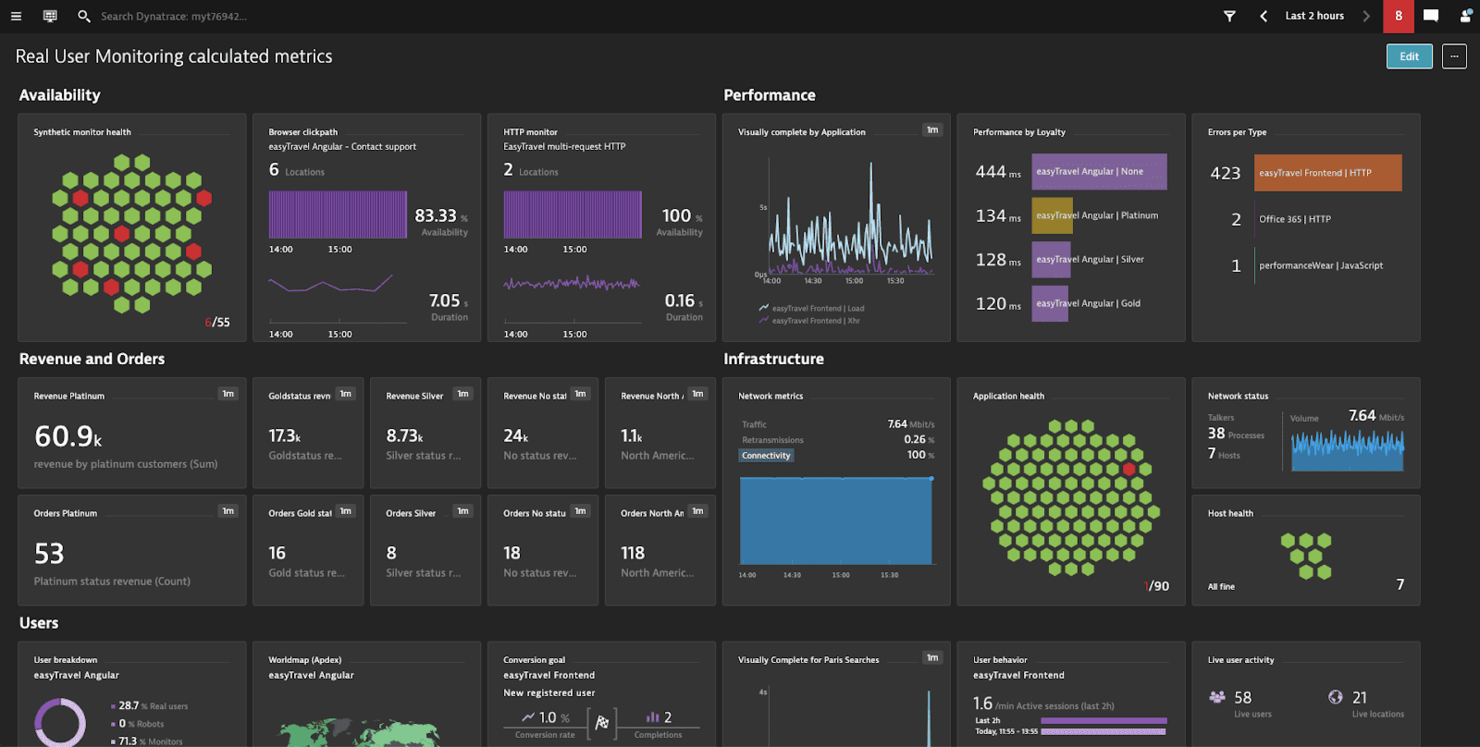
Dynatrace is a cloud-based monitoring, observability, automation, and analytics solution for systems such as infrastructure and applications.
Why I picked Dynatrace: One of Dynatrace’s main offerings is its application performance monitoring (APM) solution, whose security features I tested. Whenever it found an issue, it sent me a single concise notification with actionable information that identified the root cause down to the exact line of code.
Dynatrace standout features and integrations:
Features that made me like Dynatrace’s APM tools include the automatic detection of all application dependencies and extending its scope, something I believe is useful for large complex systems or those that rely on microservices. It also provides usage metrics from both synthetic and real users to increase the pool of information you have for making decisions that affect performance and security.
Integrations are pre-built for GitLab, Google Cloud, AWS, Azure, Jenkins, Docker, Kubernetes, JFrog, PagerDuty, and LaunchDarkly.
Pros and Cons
Pros:
- Easy to deploy
- Makes debugging easier
- Robust application monitoring features
Cons:
- Only practical for enterprise applications
- Customer support is unresponsive at times
CrowdStrike Falcon is a cloud-based security platform that analyzes networks for malware and similar threats.
Why I picked CrowdStrike Falcon: The CrowdStrike Falcon Discover feature scanned my network and identified applications, users, and devices that didn’t meet compliance standards. ITOps teams in charge of IT infrastructure can also choose higher product tiers for advanced capabilities like automated threat intelligence and managed threat-hunting services.
CrowdStrike Falcon standout features and integrations:
Features that make CrowdStrike Falcon ideal for ITOps include Falcon Spotlight, which boosts visibility across your systems so you can pinpoint and address vulnerabilities across endpoints. You can also use Falcon Forensics to collect cybersecurity incident data for analysis so you can strengthen your systems against future attacks.
Integrations are pre-built for AWS CloudTrail, Google Chronicle, Darktrace, Coralogix, and IBM Security Verify.
Pros and Cons
Pros:
- Easy setup process
- Works with extended internet of things (XIoT) systems
- Provides strong ITOps-specific tools
Cons:
- Visit WebsiteOpens new window
- Occasional conflict with other anti-malware tools
- UI takes a while to get used to
New Relic is a software analytics and performance monitoring platform designed to help organizations maintain the health and performance of their applications and infrastructure.
Why I picked New Relic: The platform's full-stack observability capabilities allow users to gain a holistic view of their entire tech stack, from the application layer down to the underlying infrastructure. Key cybersecurity features include vulnerability management and interactive application security testing (IAST), which help identify and address security weaknesses in the code and infrastructure. These tools enable organizations to maintain a secure environment by proactively detecting and mitigating potential threats before they can cause significant damage.
New Relic standout features and integrations:
Features include application performance monitoring (APM), real-time infrastructure monitoring, browser monitoring, mobile application monitoring, synthetic monitoring, centralized logging, intelligent alerting, AI-powered insights, and customizable dashboards.
Integrations include AWS, Azure, Google Cloud, Kubernetes, Docker, Jenkins, Slack, PagerDuty, ServiceNow, Splunk, and Datadog.
Pros and Cons
Pros:
- Real-time issue visibility
- Customizable alerts and notifications
- Good support for application-specific metrics
Cons:
- New users may find it challenging to get accustomed to all the features
- Limited support for non-application monitoring
Other Cybersecurity Software
While I was making my evaluations, I found these tools that didn’t make the main list, but might still be a good choice for other use cases:
- Datadog
For educational institutions
- NETSCOUT
DDoS protection features
- Zygon
For SaaS security posture management
- Teramind
For insider threat detection
- Sprinto
For companies in highly regulated industries
- Sophos
For small businesses
- Amazon CloudWatch
For AWS
- Azure Sphere
For IoT devices
- Microsoft Intune
For endpoint security
- Bitdefender
Browser protection features
Related Software and Tool Reviews
If you still haven't found what you're looking for here, check out these other types of tools that we've tested and evaluated.
- Network Monitoring Software
- Server Monitoring Software
- SD-Wan Solutions
- Infrastructure Monitoring Tools
- Packet Sniffer
- Application Monitoring Tools
Selection Criteria for Cybersecurity Software
In my journey of researching various cybersecurity solutions, I've developed a comprehensive criteria framework to ensure my selection process is fair and consistent. Here's how I assessed each tool that made it onto my list:
Core Cybersecurity Software Functionality: 25% of total weighting score.
To be considered for inclusion on my list of the best cybersecurity solutions, the solution had to fulfill common use cases. These include:
- Protecting against external threats
- Securing sensitive data from unauthorized access
- Ensuring compliance with data protection regulations
- Providing visibility into network and device security status
- Facilitating swift incident response and recovery
Additional Standout Features: 25% of total weighting score.
- Advanced predictive analytics capabilities for foreseeing potential threats before they become imminent.
- Innovative user behavior analytics to detect insider threats or compromised accounts.
- Artificial intelligence and machine learning features for improved threat detection and response times.
- Comprehensive security coverage across both on-premises and cloud environments, providing a unified security posture.
Usability: 10% of total weighting score. Important considerations include:
- An intuitive user interface that simplifies complex security operations.
- Dashboards that provide at-a-glance insights into security posture and alerts.
- A balance between powerful features and ease of use to accommodate users with varying levels of technical expertise.
Onboarding: 10% of total weighting score. Effective onboarding is evaluated based on:
- Comprehensive training materials, such as videos and interactive tutorials.
- Quick setup processes with guided product tours to help new users navigate the platform.
- Support services like chatbots and webinars to assist with initial configuration and deployment.
Customer Support: 10% of total weighting score. Key aspects include:
- Responsive and knowledgeable support teams available through multiple channels (e.g., live chat, email, phone).
- A rich knowledge base or community forums for self-service support.
- Dedicated account managers for enterprise clients.
Value For Money: 10% of total weighting score. This involves:
- Assessing the pricing structure against the breadth and depth of features offered.
- Considering the scalability of the solution to support business growth without disproportionate cost increases.
- Evaluating any hidden costs, such as those for additional modules or support services.
Customer Reviews: 10% of total weighting score. Evaluation focuses on:
- Consistency in positive feedback across key areas such as ease of use, customer support, and effectiveness of the solution.
- Real-world testimonials highlighting specific scenarios where the tool provided significant value.
- Reviews that detail how the solution addresses and mitigates specific security challenges.
Through this criteria framework, I ensure that the cybersecurity tools not only meet generic expectations but also stand out for their ability to address the unique needs and challenges faced by different organizations.
How to Choose Cybersecurity Software
As you're shortlisting, trialing, and selecting cybersecurity software, consider the following:
- What problem are you trying to solve - Start by identifying the cybersecurity feature gap you're trying to fill to clarify the features and functionality the tool needs to provide.
- Who will need to use it - To evaluate cost and requirements, consider who'll be using the platform and how many licenses you'll need. You'll need to evaluate if it'll just be the IT team, or the whole organization that will require access. When that's clear, it's worth considering if you're prioritizing ease of use for all, or speed for your technical power users.
- What other tools it needs to work with - Clarify what tools you're replacing, what tools are staying, and the tools you'll need to integrate with. This could include your cloud infrastructure, DMARC software, networks, and data sources, and your overall tech stack. You might also need to decide if the tools will need to integrate together, or alternatively, if you can replace multiple tools with one consolidated cybersecurity software.
- What outcomes are important - Consider the result that the tool needs to deliver to be considered a success. Think about what capability you want to gain, or what you want to improve, and how you will be measuring success. You could compare cybersecurity software offerings until you’re blue in the face, but if you aren’t thinking about the outcomes you want to drive, you could be wasting a lot of valuable time.
- How it would work within your organization - Consider the solutions alongside your workflows and delivery methodology. Evaluate what's working well, and the areas that are causing issues that need to be addressed. Remember every business is different — don’t assume that because a tool is popular that it'll work in your organization.
2025 Trends in Cybersecurity Software
In 2025, the increasing complexity and sophistication of cyber threats makes updates in the features and functionalities of cybersecurity software all the more important, especially for financial services cybersecurity. A review of product updates, press releases, and release logs from the most rapidly evolving and popular cybersecurity tools reveals key trends in software and technology designed to protect and secure company devices and infrastructure. Here are some of the trends I've observed:
Evolving Features
- Enhanced Endpoint Security: With the rise of remote work, there's a notable emphasis on advanced endpoint protection solutions. These offer more comprehensive defenses against attacks targeting remote devices, including zero trust security models.
- Cloud Security Enhancements: As companies continue to migrate to cloud platforms, the demand for cloud-specific security features has grown. Tools are evolving to offer better visibility, control, and protection for cloud environments, including multi-cloud and hybrid cloud configurations.
Novel and Unusual Functionality
- Behavioral Analytics for Insider Threat Detection: Some cybersecurity tools are introducing sophisticated user behavior analytics to identify and mitigate insider threats. This unusual feature relies on monitoring user activities to detect anomalies that could indicate a security risk.
- Decentralized Security Operations: A novel approach being explored is the decentralization of cybersecurity operations, leveraging blockchain technology for enhanced security and integrity of data across networks.
Declining in Importance
- Traditional Signature-Based Antivirus: The reliance on traditional signature-based antivirus solutions is diminishing, as these are less effective against zero-day exploits and advanced persistent threats (APTs). The market is shifting towards solutions that offer more dynamic and behavioral-based detection methods.
As cyber threats evolve, so do the tools designed to combat them. Staying up to date with these trends helps businesses make smarter choices about the software and solutions they implement, ensuring they're not just suitable for current needs, but future ones.
What is Cybersecurity Software?
Cybersecurity software is used to protect systems, networks, and data from threats like malware, phishing, and unauthorized access. It's typically used by IT teams, security professionals, and managed service providers who need to monitor vulnerabilities, manage incidents, and keep business operations safe.
DNS security services, threat detection, access control, and activity logging features help with identifying risks, stopping intrusions, and tracking events. These tools help reduce downtime, support compliance, and make it easier to protect both internal and customer-facing systems.
Features
Here are the core features I looked for in my research of cybersecurity software:
- Real-Time Threat Detection: This feature allows for the immediate identification of threats as they occur. It's vital for minimizing the window of opportunity for attackers to exploit vulnerabilities, ensuring that your devices and networks remain secure.
- Automated Incident Response: Software (such as unified threat management software) with this capability can automatically take predefined actions against detected threats. It reduces the time and resources required for manual intervention, streamlining the process of mitigating cyber threats efficiently.
- Endpoint Security: This ensures the protection of individual devices (endpoints) that connect to your network. With the proliferation of remote work, securing each endpoint is essential to safeguard against threats that target devices outside traditional network defenses.
- Advanced Firewall Protection: Robust firewall software acts as a barrier between your network and untrusted external networks. It filters incoming and outgoing traffic based on an established set of security rules, crucial for preventing unauthorized access to your network resources.
- Multi-factor Authentication (MFA): MFA requires users to provide multiple forms of verification before gaining access. This feature adds an additional layer of security, significantly reducing the risk of unauthorized access through compromised credentials.
- Cloud Security: Specifically designed to protect cloud-based infrastructure and data, this feature ensures that your assets in the cloud are as secure as those on physical devices or on-premises networks. It's critical for businesses leveraging cloud computing.
- Encryption Tools: Encryption safeguards sensitive data by converting it into unreadable code for unauthorized users. This feature is indispensable for protecting data integrity and confidentiality, particularly for information stored on cloud platforms or transmitted across networks. For management of encrypted keys, PKI software is available to allow the highest level of control.
- Security Information and Event Management (SIEM): SIEM provides an overview of the security landscape across your organization by collecting and analyzing security data from various sources. This feature is key for detecting patterns and potential security incidents before they escalate.
- Vulnerability Scanning: Regular scanning for vulnerabilities allows for the identification and patching of security gaps in software and systems. This proactive measure is crucial for preventing attackers from exploiting known vulnerabilities.
- Data Loss Prevention (DLP): DLP technologies prevent sensitive data from being lost, misused, or accessed by unauthorized users. This feature is essential for maintaining the confidentiality and integrity of critical business data, ensuring compliance with data protection regulations.
Common Cybersecurity Software AI Features
Beyond the standard cybersecurity software features listed above, many of these solutions are incorporating AI with features like:
- AI-powered threat intelligence: This feature uses artificial intelligence to analyze vast amounts of data and quickly identify new or evolving threats. You get early warnings and proactive defense against emerging attacks.
- Anomaly detection: AI automatically spots abnormal patterns or behaviors that could indicate a cyberattack. It helps you catch sneaky threats that traditional methods might miss.
- Automated incident response: When a threat is detected, AI systems can automatically quarantine devices or block suspicious actions, speeding up response times and reducing the impact of attacks.
- Predictive risk assessment: AI evaluates your systems and predicts where vulnerabilities might crop up in the future. You can fix weak spots before they turn into bigger problems.
- Phishing detection: AI scans emails and communications to catch phishing attempts by analyzing language, sender behavior, and intent. This helps stop scams before anyone clicks a dangerous link.
Selecting cybersecurity software that encompasses these features can significantly enhance your organization's ability to defend against and respond to cyber threats. By deciding which features to prioritize, you can build a resilient digital environment that supports your company's goals, operations, and growth.
Benefits
Cybersecurity software plays a crucial role in safeguarding organizations from the myriad of cyber threats lurking online. Here are five specific key benefits that cybersecurity software provides to users and organizations:
- Enhanced Threat Detection and Response: Cybersecurity software offers sophisticated mechanisms to detect and respond to threats in real-time. Intrusion detection software allows businesses to identify potential security breaches quickly and mitigate them before they can cause significant damage.
- Improved Compliance with Regulations: Many cybersecurity solutions come equipped with features designed to help organizations comply with data protection laws and industry regulations. This not only helps avoid legal penalties but also strengthens trust with customers and partners by demonstrating a commitment to data security.
- Protection Against Data Breaches: By implementing robust encryption, firewall audit software, and intrusion detection systems, cybersecurity software significantly reduces the risk of data breaches. This protection is essential for safeguarding sensitive information and maintaining the integrity and confidentiality of business data.
- Enhanced Productivity: Cybersecurity threats can disrupt business operations and lead to costly downtime. By preventing attacks and minimizing their impact, cybersecurity software ensures that employees can maintain productivity without interruption from malicious activities.
- Brand Reputation and Trust: Effective cybersecurity measures protect not only data and systems but also the reputation of the organization. Customers are more likely to trust and engage with businesses that can demonstrate a strong commitment to securing their information.
The benefits of investing in cybersecurity software extend far beyond simple risk mitigation. For organizations looking to navigate the complexities of the digital landscape, these tools offer a vital line of defense, enhancing overall resilience and fostering a secure environment for growth and innovation. For companies based in the United States, working with a cybersecurity company in Chicago or another major city provides a crucial layer of protection and insight for each project.
Costs & Pricing
Cybersecurity solutions come in various plans and pricing options, each designed to cater to different needs, from small businesses seeking basic protection to large enterprises requiring advanced security measures. Understanding these options will help you make an informed decision that aligns with your organization's specific security needs and budget constraints.
Plan Comparison Table for Cybersecurity Software
Here's an outline of the common plan options for cybersecurity software:
| Plan Type | Average Price | Common Features | Best For |
|---|---|---|---|
| Free | $0 | Basic protection, limited features, recommended for personal use or very small businesses | Personal use, very small businesses with minimal online presence |
| Basic | $10 - $30/month | Antivirus, firewall, email security, web filtering | Small businesses with basic security needs, home offices |
| Standard | $30 - $70/month | Basic features plus endpoint protection, mobile security, VPN | Growing businesses, startups, organizations with some sensitive data |
| Premium | $70 - $150/month | Standard features plus advanced threat protection, identity management, security analytics | Mid-sized businesses with expanding security needs, organizations with customer data |
| Enterprise | Custom Pricing | Premium features plus scalability options, dedicated support, BAS software, full-suite solutions | Large enterprises, organizations with complex IT infrastructure, businesses handling highly sensitive data |
When selecting a cybersecurity software plan, consider both your immediate and future security needs, as well as your budget. The right plan should offer a balance of comprehensive protection without overextending your financial resources.
Cybersecurity Software FAQs
Here are some answers to common questions about cybersecurity software:
How do I evaluate cybersecurity software for integration with my existing tech stack?
What are the most important compliance standards to consider when choosing cybersecurity software?
How do I measure the ROI of a cybersecurity solution for my organization?
Can cybersecurity tools help automate threat detection and response?
What are common challenges when deploying cybersecurity software at scale?
What are cybersecurity best practices?
Is Windows Defender good enough, or do I need an antivirus?
What’s Next
If you're in the process of researching database monitoring tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.