Best Intrusion Detection Software Shortlist
Keeping your systems safe is an ongoing challenge. Intrusion detection software acts as an early warning system—monitoring your network, spotting unusual activity, and alerting your team before threats spread.
This guide shares expert-curated insights to help you choose the right tool for your organization, based on security features, usability, and reliability.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Intrusion Detection Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for user and entity behavior analytics | Free demo available | Pricing upon request | Website | |
| 2 | Best for endpoint detection and response | Free trial + free demo available | Pricing upon request | Website | |
| 3 | Best for centralized event management | 30-day free trial | From $2,877/year | Website | |
| 4 | Best for large enterprise environments | Not available | Pricing upon request | Website | |
| 5 | Best for integrated threat intelligence | Not available | Pricing upon request | Website | |
| 6 | Best for multi-layered security strategies | Not available | Pricing upon request | Website | |
| 7 | Best for targeted attack identification | Not available | Pricing upon request | Website | |
| 8 | Best for versatility in threat detection | Not available | Pricing upon request | Website | |
| 9 | Best for advanced threat intelligence | Not available | Pricing upon request | Website | |
| 10 | Best for open-source enthusiasts | Free demo available | From $29.99/year (billed annually) | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Intrusion Detection Software Reviews
ManageEngine Log360 is a comprehensive security information and event management (SIEM) solution designed to enhance organizational security by integrating essential capabilities such as User and Entity Behavior Analytics (UEBA), Data Loss Prevention (DLP), and Cloud Access Security Broker (CASB).
Why I Picked ManageEngine Log360: Log360 aggregates data from various sources, including Intrusion Detection Systems (IDS), firewalls, and Active Directory, to provide immediate alerts on potential intrusions. The platform also leverages advanced analytics and machine learning to detect anomalous behavior, which is essential for identifying insider threats and sophisticated cyber-attacks that traditional methods might miss. The UEBA feature also uses machine learning to identify unusual patterns and behaviors, providing deeper insights into potential security threats.
Standout features & integrations:
The platform's integrated compliance management ensures that organizations meet regulatory requirements, providing real-time notifications of compliance violations. It also offers automated incident response workflows to simplify the process of addressing security incidents. Integrations include Microsoft Exchange, Amazon Web Services (AWS), Microsoft Entra ID, Microsoft Azure, and Active Directory.
Pros and Cons
Pros:
- Provides real-time monitoring and alerting
- Effective for auditing all IT levels in an organization
- Excellent visibility across systems
Cons:
- Potential performance issues with large data volumes
- Initial setup can be complex
New Product Updates from ManageEngine Log360
ManageEngine Log360 Adds New Log Source Integrations
ManageEngine Log360 introduced new integration support for NetFlow Analyzer and Firewall Analyzer, along with enhanced audit log parsing for OpManager products. The updates help teams centralize log collection and improve monitoring and analysis workflows. For more information, visit ManageEngine Log360's official site.
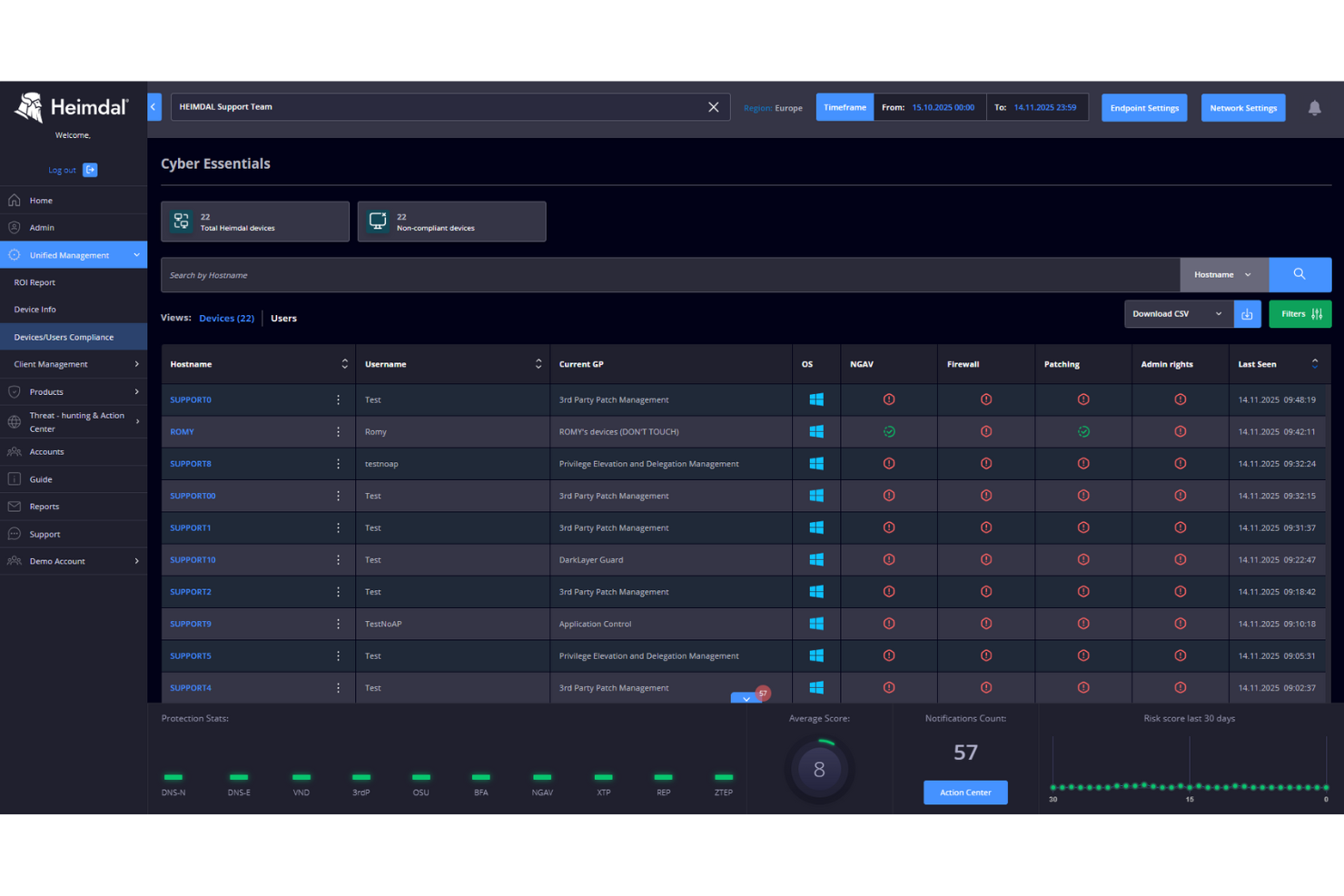
In the realm of intrusion detection software, Heimdal stands out as a versatile solution that addresses the multifaceted challenges faced by modern businesses. Its unified cybersecurity platform is designed to appeal to enterprises and managed service providers seeking to enhance their security posture against sophisticated threats. By integrating threat detection, response, and prevention capabilities, Heimdal helps organizations mitigate risks and maintain operational continuity in an increasingly complex threat landscape.
Why I Picked Heimdal
I picked Heimdal for its robust Endpoint Detection & Response (EDR) capabilities, which are crucial for any intrusion detection software. The EDR feature continuously monitors endpoints to detect and respond to threats, ensuring that your network remains secure from potential breaches. Additionally, Heimdal's Threat Hunting functionality proactively identifies and mitigates potential threats before they can cause harm. These features cater to businesses looking to enhance their security measures and protect sensitive data from evolving cyber threats.
Heimdal Key Features
In addition to its standout EDR and Threat Hunting capabilities, I also found other features beneficial for intrusion detection:
- Network Security: Protects against network-based attacks through DNS security and other strategic measures.
- Managed Services: Provides 24/7 security operations center (SOC) services for continuous monitoring and response.
- Privilege Elevation & Delegation Management: Manages privilege access to prevent unauthorized breaches.
- Ransomware Encryption Protection: Shields devices and cloud workspaces from ransomware attacks.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
Best for centralized event management
SolarWinds Security Event Manager (SEM) is designed to simplify the process of identifying and responding to security threats, failed audits, and operational issues. The tool stands out for its ability to centralize and interpret high volumes of log data from multiple sources.
Why I Picked SolarWinds Security Event Manager: During my evaluation, SolarWinds SEM's approach to centralizing events caught my attention. In my judgment, and after comparing it with several other platforms, I determined that it offers a differentiated and efficient solution for organizations that grapple with data sprawl. Its prowess in centralized event management makes it an invaluable tool for many security professionals.
Standout features & integrations:
The core strength of SolarWinds SEM lies in its log correlation technology, which quickly pinpoints potential issues by analyzing patterns. Additionally, its integrations with other SolarWinds products allow organizations to have a broader, more holistic view of their IT environments.
Pros and Cons
Pros:
- Supports numerous device and application logs
- Streamlined event visualization tools
- Efficient log correlation capabilities
Cons:
- Some users report performance lags with high data volumes
- Reporting capabilities may need enhancements
- The learning curve for new users
Cisco IDS, stemming from a legacy of robust security solutions, specializes in safeguarding expansive enterprise networks. Its capabilities to handle high traffic volumes without compromise make it an optimal choice for large-scale operations.
Why I Picked Cisco IDS: When I embarked on selecting a tool adept for extensive enterprise frameworks, Cisco IDS's reputation and performance benchmarks became undeniable. Its prowess in managing intricate and vast network architectures made it stand out in my assessment. For businesses operating on a grand scale seeking unwavering intrusion detection, Cisco IDS is, in my opinion, a compelling choice.
Standout features & integrations:
Cisco IDS boasts of its advanced threat detection algorithms, enabling swift identification of suspicious activities. It incorporates threat intelligence updates to stay ahead of evolving risks. Integration capabilities span across Cisco's suite of security products, fostering a holistic security approach.
Pros and Cons
Pros:
- Robust integration within Cisco's security ecosystem
- Continual threat intelligence updates
- Tailored for handling high network traffic volumes
Cons:
- Requires dedicated personnel for optimal management
- Pricier than some alternative solutions
- Initial setup can be complex for newcomers
McAfee's IDS rises above by not just detecting intrusions but by providing integrated threat intelligence to inform timely countermeasures. This integration results in an enriched understanding of threats, placing it high on the list for businesses prioritizing intelligence-driven defense.
Why I Picked IDS by McAfee: Upon comparing various tools, the intelligence fusion within McAfee's IDS caught my attention. This integration, a differentiator in its league, led me to judge it superior for those keen on coupling detection with actionable intelligence. If integrated threat insights are the goal, IDS by McAfee aligns perfectly with such demands.
Standout features & integrations:
McAfee's IDS takes pride in its adaptive threat detection mechanisms, refining its processes with real-time intelligence feeds. Its cloud-based analytics further elevate its detection accuracy. For integrations, it pairs effectively with other McAfee security products and a range of third-party SIEM systems.
Pros and Cons
Pros:
- Wide-ranging compatibility with SIEM solutions
- Cloud-enhanced analytics for precise detection
- Real-time threat intelligence integration
Cons:
- Licensing complexities for expansive deployments.
- Reliance on the cloud may not suit all organizations
- Some learning curve for full feature utilization
Check Point IDS operates as an integral component of Check Point's comprehensive security suite, emphasizing a multi-layered approach to threat mitigation. This approach ensures that threats, regardless of their origin or nature, are tackled at various levels, providing robust protection.
Why I Picked Check Point IDS: My judgment was steered towards Check Point IDS after observing its holistic, multi-layered defense mechanism. After determining its performance and comparing it with other tools, I concluded that for organizations seeking a multi-tiered security strategy, Check Point IDS would be a commendable choice.
Standout features & integrations:
Check Point IDS excels in its threat prevention technologies, which encompass intrusion prevention, antivirus, and anti-bot modules. Additionally, its integration with Check Point's security gateway broadens the scope of protection.
Pros and Cons
Pros:
- Regularly updated with the latest threat intelligence
- Part of the broader Check Point security ecosystem
- Comprehensive multi-layered threat prevention
Cons:
- Licensing can be complex with various modules and features.
- The user interface might be overwhelming for newcomers
- Requires dedicated hardware for optimal performance
Trend Micro Deep Discovery is a dedicated solution designed to detect, analyze, and respond to today's stealthy ransomware, its variants, and targeted attacks. The tool's specialization in uncovering targeted and sophisticated threats sets it apart in the security landscape.
Why I Picked Trend Micro Deep Discovery: My decision to highlight Trend Micro Deep Discovery was influenced by its focused approach to targeted threat detection. After comparing and assessing several solutions, I was convinced that its ability to identify concealed attacks gives organizations a significant upper hand.
Standout features & integrations:
Deep Discovery excels in its specialized detection engines and custom sandbox analysis. Its integrations with other Trend Micro solutions provide layered security and enhanced visibility across the digital environment.
Pros and Cons
Pros:
- Supports a wide range of virtual and physical network appliances
- Offers in-depth threat insights and intelligence
- Specialized in detecting hidden threats
Cons:
- May require additional resources for larger networks.
- Licensing model may be complicated for some users
- Can be complex to set up initially
Juniper IDP is known for its extensive threat detection methodologies, making it a preferred choice for organizations that require varied approaches to safeguard their digital infrastructure. Its ability to adapt to different threat landscapes proves it's truly built for versatile detection.
Why I Picked Juniper IDP: In the process of selecting a tool that offers a broad spectrum of threat detection techniques, Juniper IDP emerged as a prominent security software contender. The versatility it exhibited in its detection methods compared favorably against its peers. For organizations that face multifaceted threat vectors and need a flexible solution, I believe Juniper IDP fits the bill.
Standout features & integrations:
Juniper IDP boasts signature-based, anomaly-based, and behavior-based detection techniques, offering a layered defense strategy. It integrates effectively with Juniper's broader security portfolio, ensuring a more cohesive approach to threat management.
Pros and Cons
Pros:
- Customizable detection rules for specialized environments
- Integration within Juniper's ecosystem
- Comprehensive threat detection methodologies
Cons:
- Software updates may occasionally disrupt configurations
- Potential for false positives with aggressive settings
- Requires a steep learning curve for maximum efficiency
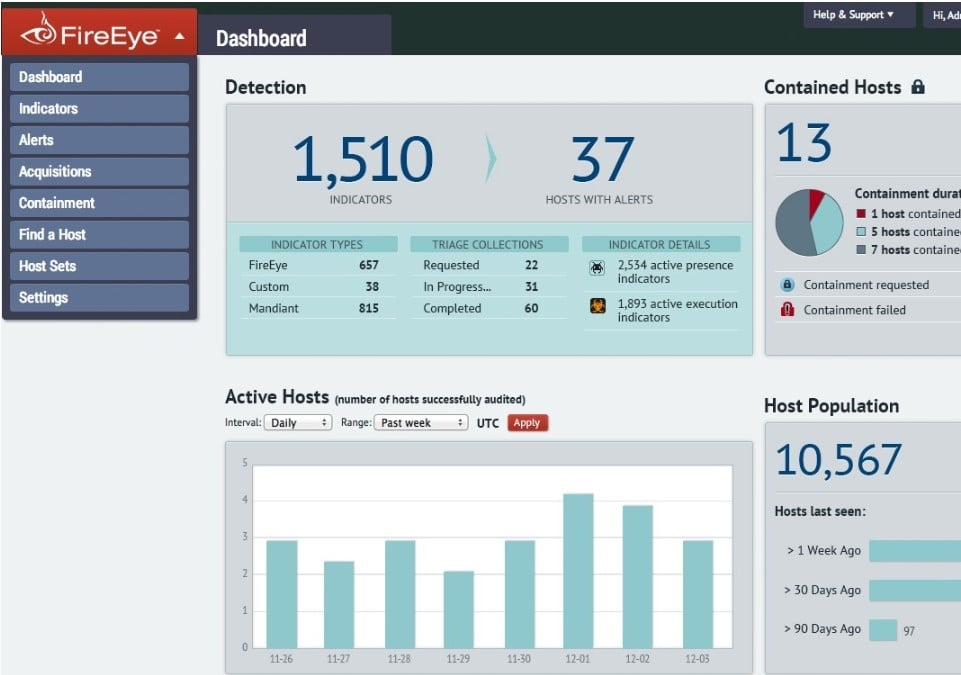
FireEye Network Security serves as a comprehensive platform that focuses on advanced threat detection, prevention, and investigation. What differentiates this tool is its rich threat intelligence, offering insights that many other platforms might miss.
Why I Picked FireEye Network Security: After deliberating on various security platforms and their offerings, I gravitated towards FireEye due to its renowned advanced threat intelligence capabilities. I believe that in the evolving threat landscape, FireEye's approach to detecting and tackling sophisticated threats places it ahead of many competitors.
Standout features & integrations:
FireEye's strength is its MVX architecture which identifies and blocks complex threats in real-time. Furthermore, its integration capabilities with third-party solutions make it versatile in diverse IT environments.
Pros and Cons
Pros:
- Ability to sandbox suspicious content for analysis
- Comprehensive threat analytics and reporting
- Strong emphasis on zero-day and new threat vectors
Cons:
- Requires careful configuration for optimal results
- May generate false positives if not tuned properly
- Can be resource-intensive
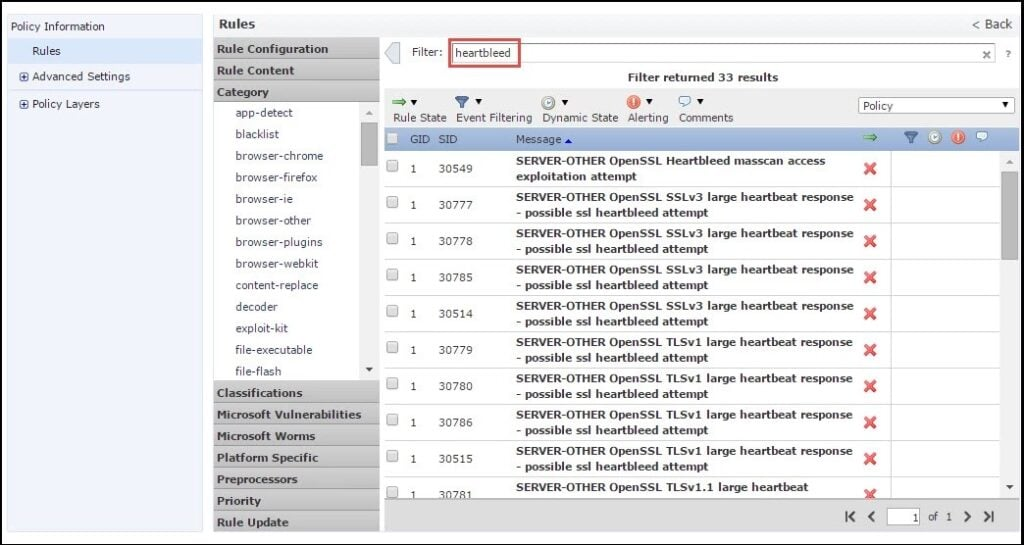
Snort stands as one of the pioneers in intrusion detection, with its robust and open-source nature allowing for in-depth network protection. Catering to those who value transparency and customization, Snort's open-source model offers users a direct line of sight into its inner workings, making it a prime choice for enthusiasts.
Why I Picked Snort: I chose Snort because, in my journey of comparing various intrusion detection tools, its open-source nature stood out. This tool has garnered respect and loyalty in the cybersecurity community for its adaptability and transparency. Given its commitment to providing a platform that enthusiasts can both trust and tinker with, I determined that Snort is best for those who deeply value open-source paradigms.
Standout features & integrations:
Snort's rule-driven language allows users to fine-tune detection protocols, while its capabilities in real-time traffic analysis ensure timely insights into network activity. Beyond its core features, Snort integrates well with other security platforms and databases, enhancing its usability and scope within larger cybersecurity frameworks.
Pros and Cons
Pros:
- Real-time traffic analysis captures anomalies swiftly
- Rule-driven language for tailored detection
- The open-source nature ensures transparency
Cons:
- Lacks a graphical user interface out of the box.
- Regular updates might demand frequent configuration tweaks
- Initial setup can be complex for novices
Other Intrusion Detection Software
Below is a list of additional intrusion detection software that I shortlisted, but did not make it to the top 10. Definitely worth checking them out.
- Tripwire
For system integrity monitoring
- Ossec
For log management and analysis
- Zeek
For network traffic analysis
- RSA NetWitness
For real-time incident response
- LogRhythm
Good for comprehensive log management
- Suricata
Good for high-performance network IDS, IPS, and network security monitoring
- Security Onion
Good for intrusion detection, enterprise security monitoring, and log management
- Darktrace
Good for AI-driven threat detection
- Kismet
Good for wireless network detection
- Nagios Core
Good for infrastructure monitoring
- Fidelis Network
Good for deep session inspection
- WatchGuard Network Security
Good for modular security solutions
- Vectra Cognito
Good for automating threat detection
- Fortinet FortiGate
Good for broad security integrations
- Hillstone Network-Based IDS
Good for layered threat prevention
Intrusion Detection-Related Software Reviews
- Intrusion Prevention Software
- Endpoint Protection Software
- Intrusion Detection and Prevention Systems
Intrusion Detection Software Selection Criteria
When selecting the best intrusion detection software to include in this list, I considered common buyer needs and pain points like network security and threat detection. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detecting unauthorized access
- Monitoring network traffic
- Alerting on suspicious activity
- Logging security events
- Supporting compliance requirements
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Advanced threat intelligence
- Real-time data analysis
- Customizable detection rules
- Integration with other security tools
- Machine learning capabilities
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Customizable dashboards
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Step-by-step setup guides
- Supportive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Access to live chat
- Comprehensive knowledge base
- Responsive email support
- Dedicated account managers
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Transparent billing practices
- Flexible subscription plans
- Cost versus feature set
- Discounts for annual billing
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Positive feedback on reliability
- User satisfaction with features
- Comments on ease of use
- Feedback on support quality
- Overall product recommendation
How to Choose Intrusion Detection Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your team? Consider the number of devices and users you plan to add over the next few years. Make sure it supports future needs. |
| Integrations | Check if the tool integrates with your existing systems like firewalls, SIEMs, or other security tools. Avoid compatibility issues that disrupt workflows. |
| Customizability | Look for tools that let you tailor alerts and monitoring to your specific security policies. Avoid rigid systems that don’t adapt to your needs. |
| Ease of use | Is the interface intuitive for your team? Test demos to ensure low training time and easy navigation. Don’t overlook user-friendliness in complex systems. |
| Implementation and onboarding | How smooth is the setup process? Consider time, resources, and support needed to get started. Avoid tools with complex, lengthy onboarding phases. |
| Cost | Compare the total cost, including hidden fees. Consider your budget for setup, maintenance, and future upgrades. Don’t just look at the sticker price. |
| Security safeguards | Ensure the tool has strong encryption and data protection measures. Check for compliance with industry standards like GDPR or HIPAA. Don’t compromise on security. |
| Support availability | Assess the vendor’s support options. Is there 24/7 help available? Consider response times and support channels like chat, phone, or email. |
What Is Intrusion Detection Software?
Intrusion detection software is a tool that monitors network or system activities for malicious activities or policy violations. IT security professionals and network administrators typically use these tools to protect sensitive data and ensure network security.
Real-time monitoring, alerting, and logging capabilities help with identifying threats, responding quickly, and maintaining compliance. Overall, these tools provide essential security by detecting and mitigating potential threats before they cause harm.
Features
When selecting intrusion detection software, keep an eye out for the following key features:
- Real-time monitoring: Continuously observes network traffic to detect suspicious activities as they occur, helping prevent potential breaches before they escalate.
- Alerting system: Sends instant notifications to security teams when anomalies or threats are detected, allowing for quick response and mitigation.
- Logging capabilities: Records detailed logs of network activities, providing valuable data for analysis and compliance reporting.
- Threat intelligence: Utilizes up-to-date threat data to identify known and emerging threats, enhancing the accuracy of threat detection.
- Customizable rules: Allows users to set specific detection parameters tailored to their organization's security policies, ensuring relevant threat identification.
- Integration support: Connects with existing security tools and systems to provide a unified and comprehensive security infrastructure.
- File integrity monitoring: Tracks changes to critical files and system configurations, alerting users to unauthorized modifications that may indicate a security breach.
- Sandboxing: Isolates and analyzes suspicious files in a controlled environment to understand their behavior without risking the network.
- Advanced threat detection: Employs techniques like anomaly detection to identify sophisticated threats that traditional methods might miss.
- User-friendly interface: Offers an intuitive design that simplifies navigation and operation, reducing the learning curve for security teams.
Benefits
Implementing intrusion detection software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: By monitoring network traffic in real-time, intrusion detection software helps identify and neutralize threats before they cause damage.
- Quick response: Instant alerts enable security teams to react promptly to potential breaches, minimizing the impact on your systems.
- Compliance support: Detailed logging and reporting aid in meeting regulatory requirements, ensuring your business stays compliant with industry standards.
- Resource efficiency: Automating threat detection processes reduces the need for manual monitoring, freeing up your team to focus on other tasks.
- Improved threat detection: Advanced threat intelligence and customizable rules allow for more accurate identification of both known and emerging threats.
- Data protection: By tracking changes to critical files, these tools help safeguard sensitive information from unauthorized access.
- Integration capabilities: Seamless integration with existing security tools creates a comprehensive security ecosystem, improving overall protection.
Costs & Pricing
Selecting intrusion detection software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in intrusion detection software solutions:
Plan Comparison Table for Intrusion Detection Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited alerts, and community support. |
| Personal Plan | $10-$30/user/month | Real-time alerts, basic reporting, and user-friendly interface. |
| Business Plan | $50-$100/user/month | Advanced threat detection, integration support, and customizable dashboards. |
| Enterprise Plan | $150-$300/user/month | Full packet capture, compliance reporting, and dedicated support services. |
Intrusion Detection Software FAQs
How is an IDS different from a firewall?
An IDS detects and alerts on suspicious activity, while a firewall blocks or allows network traffic based on rules. IDS focuses on detection, not prevention.
Can IDS stop attacks automatically?
Not on its own. IDS detects threats, while intrusion prevention systems (IPS) block them. Using both provides stronger protection.
How often should IDS be updated?
Regularly. Frequent updates ensure your system recognizes the latest threats and vulnerabilities.
What are the main challenges of using IDS?
False positives, complex configurations, and high resource use can occur if not tuned properly. Regular review and maintenance help minimize these issues.
Do small businesses need IDS?
Yes. Even small networks face security risks. Lightweight or cloud-based IDS options offer affordable, effective protection.
What’s Next:
If you're in the process of researching intrusion detection software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.