10 Best Security Risk Assessment Tools Shortlist
In today’s connected world, keeping your information safe is more important than ever. Companies face many kinds of online risks, from stolen data to unsafe systems, and it can be hard to spot them all. That’s why security risk assessment tools exist — they help you find weak spots early and keep your business protected.
These tools make it simple to check where problems might happen, stay organized, and follow safety rules. They give your team a clear picture of what needs attention so you can act before issues grow.
In this guide, you’ll discover the best security risk assessment tools that help keep your information secure and your business running smoothly. Whether you manage a small team or a big company, these tools make staying safe online easier.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Security Risk Assessment Tools Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for third-party vendor risk assessments | Free demo available | Pricing upon request | Website | |
| 2 | Best for real-time risk insights | Free demo available | Pricing upon request | Website | |
| 3 | Best for AI-generated remediation | Free demo available | From $69/month | Website | |
| 4 | Best for real-time threat alerts | Not available | Pricing upon request | Website | |
| 5 | Best for comprehensive code-to-cloud security scans | Free plan available + free demo | From $350/month | Website | |
| 6 | Best for IT-specific risk management | Free demo available | Pricing upon request | Website | |
| 7 | Best for security management and tailored assessments | 7-day free trial | Pricing upon request | Website | |
| 8 | Best for CyberGRC governance and analytics | Free demo available | Pricing upon request | Website | |
| 9 | Best for IT security and integrated risk management | Free demo available. | Pricing upon request | Website | |
| 10 | Best for process-driven cybersecurity risk analysis | Not available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Security Risk Assessment Tools Reviews
Prevalent is a third-party risk management platform designed to assist organizations in managing vendor and supplier risks throughout their lifecycle. It is intended for various teams such as risk management, procurement, security, and compliance across industries including finance, healthcare, and retail.
Why I Picked Prevalent: Prevalent focuses on monitoring a wide range of cyber threats and vulnerabilities that can impact your vendor relationships. With its vendor cyber intelligence feature, Prevalent provides insights into third-party cyber incidents by analyzing data from over 1,500 criminal forums, dark websites, code repositories, and vulnerability databases. This allows your team to see if any of your vendors are affected by exposed credentials or potential security breaches. Prevalent also tracks operational and financial risks, monitoring vendors’ network health and identifying vulnerabilities that could compromise data security.
Standout features & integrations:
Beyond cyber monitoring, Prevalent offers additional tools to help you keep your vendor risk in check. Its breach event notification feature alerts you when a third-party vendor experiences a data incident, so your team can respond proactively. The platform also provides real-time reputational insights and a risk register that centralizes all assessment and monitoring data. Integrations include Active Directory, BitSight, ServiceNow, SecZetta, and Source Defense.
Pros and Cons
Pros:
- Extensive functionalities for managing vendor risk
- Users can tailor reports according to specific needs
- Strong security protocols to protect data
Cons:
- The platform is complex and comes with a learning curve
- Challenges in migrating data can complicate the initial setup
Mitratech's Alyne is a comprehensive governance, risk, and compliance (GRC) platform designed to help organizations identify, assess, and monitor risks across various domains, including cybersecurity, privacy, and regulatory compliance.
Why I Picked Mitratech: Its real-time risk insights and automated assessments enhance the process of identifying potential security vulnerabilities. With its built-in libraries of controls and frameworks aligned with global standards, such as ISO 27001 and NIST, Alyne ensures that businesses have a structured approach to managing security risks effectively.
Standout features & integrations:
The platform includes real-time integrations with third-party data providers like Black Kite and SecurityScorecard, enhancing its ability to provide comprehensive risk assessments. Additionally, Alyne's cloud-based, AI-driven design allows for continuous risk monitoring and management. Integrations include Black Kite, SecurityScorecard, LeanIX, Snowflake, Tableau, Microsoft Azure, AWS, and other data providers.
Pros and Cons
Pros:
- Actionable insights
- Customizable assessments
- AI-enabled platform
Cons:
- Potential challenges integrating with some third-party tools
- No free trial available
Astra Pentest is a security risk assessment tool that helps you identify and fix vulnerabilities in your systems. It combines automated and manual testing to provide a thorough evaluation of your security posture.
Why I Picked Astra Pentest: I picked Astra Pentest because it runs over 8,000 automated tests, covering OWASP Top 10 vulnerabilities and compliance standards like GDPR and ISO 27001. Its built-in vulnerability management dashboard lets you classify, prioritize, and fix issues efficiently, with AI-generated remediation steps to guide your team through every fix.
Standout features & integrations:
Features include integration with CI/CD pipelines, which allows for continuous security testing throughout your development process. You also get the chance to collaborate with security experts in real-time, so when you encounter complex vulnerabilities, you can consult directly with professionals. Detailed reports are provided, highlighting vulnerabilities and offering actionable insights for remediation.
Integrations include Slack, Salesforce, Jira, Atlassian, GitHub, GitLab, and Astra API Security Platform.
Pros and Cons
Pros:
- Compliance support for major standards
- Over 8,000 vulnerability checks
- Hybrid automated and manual testing
Cons:
- Manual testing turnaround times vary
- Requires setup by security experts
NordStellar is a cybersecurity tool designed to help businesses manage their security risks. It centralizes threat intelligence from multiple sources, providing real-time alerts and a comprehensive view of vulnerabilities.
Why I Picked NordStellar: I picked NordStellar because it offers data breach monitoring, which helps you identify compromised data and respond quickly to minimize damage. This feature is crucial for keeping your sensitive information secure and maintaining trust with your customers. Additionally, the dark web monitoring alerts you to potential threats emerging from the dark web, allowing you to take proactive measures. Another reason I chose NordStellar is its attack surface management. This feature identifies and helps secure vulnerable entry points, reducing the risk of cyberattacks. By prioritizing risks, your team can focus on the most pressing threats, ensuring that your cybersecurity efforts are targeted and effective.
Standout features & integrations:
Features include brand protection, which helps you monitor and safeguard your company's reputation online. The platform also provides centralized breach information, making it easier for you to manage and prioritize risks. With real-time alerts, you're always informed about potential threats, enabling you to respond swiftly and minimize potential harm. Integrations include Splunk, QRadar, and Datadog.
Pros and Cons
Pros:
- Attack surface management identifies vulnerabilities
- Dark web monitoring detects breaches
- Real-time alerts enable swift response
Cons:
- Interface complexity increases learning curve
- Pricing details require demo request
Aikido Security is a comprehensive DevSecOps platform designed to secure code and cloud environments. It offers features such as vulnerability management, generating SBOMs, and protecting applications at runtime.
Why I Picked AIkido Security: I like that Aikido Security offers an all-in-one platform that integrates various essential security scanning capabilities, including static application security testing (SAST), dynamic application security testing (DAST), infrastructure as code (IaC) scanning, software composition analysis (SCA), and cloud security posture management (CSPM). This integration allows organizations to cover their entire security landscape from code to cloud, ensuring that all potential vulnerabilities are identified and addressed.
Standout features & integrations:
Features include secrets detection that scans code for leaked and exposed API keys, passwords, certificates, encryption keys, and other sensitive information to prevent unauthorized access. It also offers malware detection, surface monitoring, and container image scanning. Integrations include Amazon Web Services (AWS), Google Cloud, Microsoft Azure Cloud, Drata, Vanta, AWS Elastic Container Registry, Docker Hub, Jira, Asana, and GitHub.
Pros and Cons
Pros:
- User-friendly interface
- Provides actionable insights
- Offers a comprehensive dashboard and customizable reports
Cons:
- Ignores vulnerabilities if no fix is available
- Does not have endpoint security or intrusion detection capabilities
New Product Updates from Aikido Security
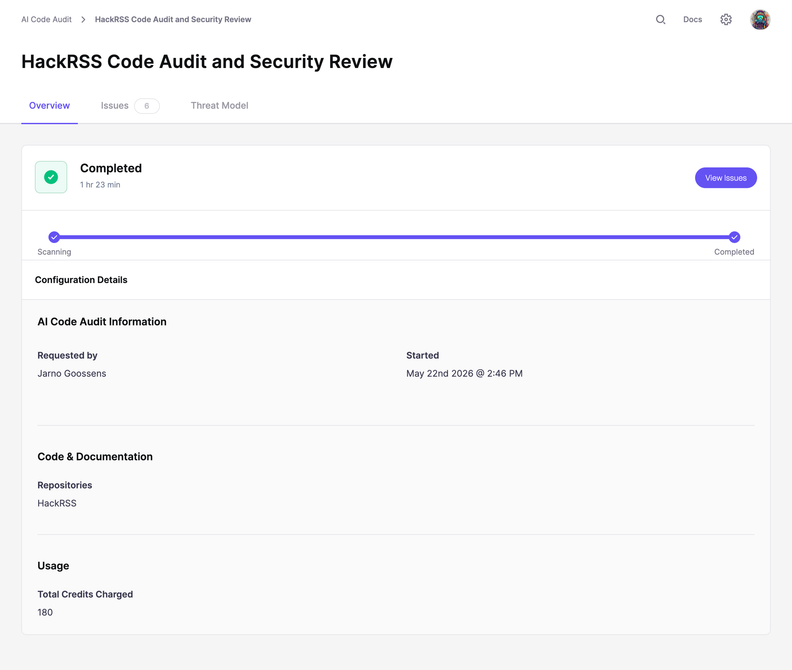
Aikido Security Adds Code Audit for Source Code Analysis
Aikido Security introduces Code Audit, bringing pentest-grade security reasoning directly to your source code to uncover logic flaws and vulnerabilities missed by pattern scanners. For more information, visit Aikido Security's official site.
LogicGate provides a platform designed to streamline IT-related risk management activities. Its specialized focus gives organizations the tools they need to identify, evaluate, and prioritize IT risks efficiently.
Why I Picked LogicGate: I chose LogicGate after meticulous comparison with other tools because of its tailored approach to IT risk management. In a landscape of more generalized solutions, LogicGate stands apart with features honed for the unique challenges IT departments face. Its ability to handle IT-specific vulnerabilities, threats, and compliance checks convinced me of its status as the premier choice for IT-focused risk management.
Standout features & integrations:
LogicGate boasts workflow automation for risk mitigation and integrated IT compliance frameworks, offering a bird‘s-eye view of IT risk landscapes. It integrates with popular ITSM solutions, enhancing its capabilities by ingesting data for a richer risk assessment.
Pros and Cons
Pros:
- Incorporation of IT compliance frameworks
- Workflow automation for risk mitigation
- Tailored for IT risk management
Cons:
- Pricing information isn't readily available
- Requires some learning curve for new users
- Might not be suitable for non-IT risk assessments
Connectwise offers tailored security assessments and streamlined management solutions to meet your organization's specific needs. Achieve the best possible security management with ease.
Why I Picked Connectwise: Connectwise's customized security management and assessments make it the ideal option for businesses with unique needs. Its hybrid approach and tailored solutions set it apart from other tools that offer one-size-fits-all solutions.
Standout features & integrations:
Connectwise excels with its automated detection and response capabilities, ensuring swift actions against potential security threats. Its custom-tailored risk assessments are designed with adaptability in mind, catering to businesses of all sizes and industries. In terms of integrations, Connectwise plays well with various third-party applications, enhancing its versatility in diverse IT environments.
Pros and Cons
Pros:
- Versatile integrations with third-party applications expand its utility in different IT setups.
- Custom-tailored risk assessments fit the unique needs of each organization.
- Automated detection and response provide timely security interventions.
Cons:
- The wide array of features could be overwhelming for smaller businesses that only need basic security management
- Might have a steeper learning curve for those unfamiliar with tailored assessments
- Lack of transparent pricing can be a barrier for some potential users
MetricStream streamlines CyberGRC initiatives with a focus on governance and analytics, simplifying cybersecurity and compliance management.
Why I Picked MetricStream: I chose MetricStream for its emphasis on CyberGRC governance, which other tools often overlook. Its analytical capabilities and governance-centric approach set it apart from other options in the market. Given the increasing number of cyber threats facing organizations, I believe MetricStream's expertise in CyberGRC governance and analytics is crucial for firms looking to strengthen their defense mechanisms.
Standout features & integrations:
MetricStream is well-regarded for its robust reporting capabilities that provide insights into an organization's cybersecurity posture. Its workflow automation aids in streamlining compliance processes, thereby ensuring that nothing falls through the cracks. On the integration front, MetricStream is compatible with several IT security tools, threat intelligence feeds, and regulatory databases, which ensures that the organization remains updated and compliant.
Pros and Cons
Pros:
- Extensive integration with IT security tools and regulatory databases
- Workflow automation for streamlined compliance processes
- Robust reporting capabilities for deep insights
Cons:
- Pricing information isn't readily available, which might deter potential customers
- Requires specialized training to maximize its capabilities
- Initial setup may be complex for some organizations
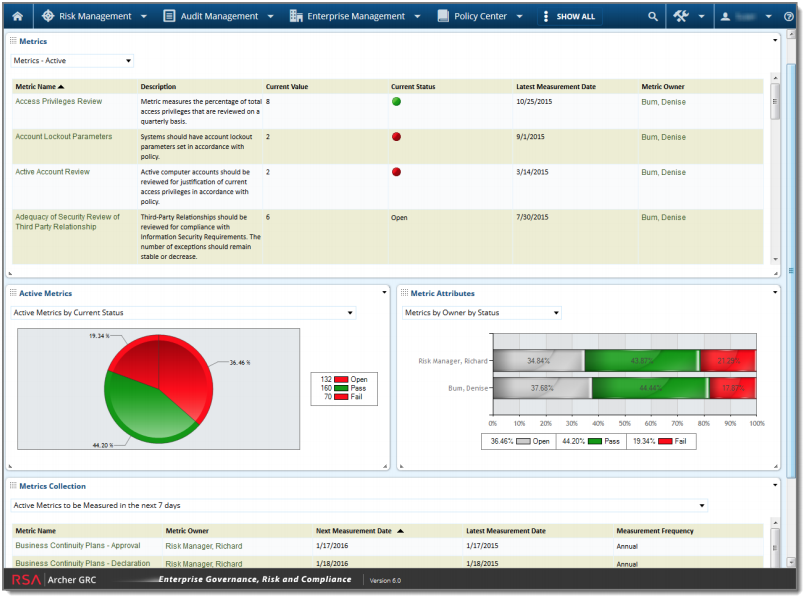
Archer is a comprehensive tool geared towards managing IT security risks while offering integrated risk management capabilities. With a strong emphasis on addressing IT security challenges and consolidating risk data across the enterprise, it's designed to provide a holistic view of an organization's risk landscape.
Why I Picked Archer: Archer came to my attention after meticulous scrutiny of various risk management tools. Its dual emphasis on IT security and holistic, integrated risk management differentiates it from its peers. Given its capability to bring IT security risks into the broader integrated risk management framework, Archer is ideally suited for organizations aiming to combine these two pivotal functions.
Standout features & integrations:
Archer offers a dynamic dashboard that simplifies the visualization of complex risk data, aiding decision-making. Its advanced analytics allow for deep dives into the risk data, enabling organizations to unearth hidden insights. Integration-wise, Archer offers compatibility with a wide range of IT security tools and enterprise platforms, allowing data flow and improved risk response.
Pros and Cons
Pros:
- Wide range of integrations with IT security tools
- Advanced analytics for detailed risk assessments
- Dynamic dashboard for easy risk visualization
Cons:
- Lack of transparent pricing structure
- Deployment might be time-consuming for larger enterprises
- Interface might be challenging for beginners
ProcessUnity offers organizations a structured way to handle cybersecurity risks by focusing on established processes. The emphasis on process-driven risk analysis ensures that vulnerabilities are identified and tackled systematically, mirroring its designation as the best for such an approach.
Why I Picked ProcessUnity: Among the numerous tools I evaluated, ProcessUnity distinguished itself through its systematic and process-driven approach to cybersecurity risks. I chose it for its consistent workflow emphasis workflows, streamlining the complex risk management task. Given its focus on systematic risk analysis, I've determined that ProcessUnity is the best for organizations seeking a process-centric methodology to address cybersecurity threats.
Standout features & integrations:
ProcessUnity has dynamic risk registries and automated assessments, ensuring a continual risk evaluation loop. Its dashboard provides an intuitive interface, allowing users to navigate risk metrics and derive actionable insights effortlessly. As for integrations, ProcessUnity syncs with a range of third-party risk intelligence providers, enriching its native data with external threat landscapes.
Pros and Cons
Pros:
- Integrates efficiently with third-party risk intelligence sources
- Intuitive dashboard for clear risk visualization
- Dynamic risk registries for continuous assessment
Cons:
- Limited inbuilt threat intelligence data compared to some competitors
- Might require some training for optimal utilization
- Pricing information not readily available
Other Noteworthy Security Risk Assessment Tools
Below is a list of additional security risk assessment tools that I shortlisted but did not make it to the top 10. Definitely worth checking them out.
- IBM Security Guardium Data Risk Manager
For data-centric risk management
- IBM OpenPages
For operational risk and compliance management
- Tenable Vulnerability Management
For vulnerability detection and response
- Qualys VMDR
For dynamic vulnerability management
- Cybereason
For focused cyber posture assessments
- FAIR Risk Management
For quantitative risk analysis methods
- Riskonnect
For comprehensive risk management integration
- NowSecure
For mobile app risk management
- Frontline Vulnerability Manager
Good for proactive vulnerability management strategies
- Microsoft Defender for Cloud
Good for cloud-native endpoint protection
- Bitsight
Good for data-driven cybersecurity analysis
- Nexpose
Good for dynamic asset discovery and risk assessment
- AT&T Cybersecurity
Good for extensive cyber threat detection
- NetWitness
Good for streamlined incident response practices
- SecurityScorecard
Good for real-time security posture monitoring
Related Security Risk Assessment Tool Reviews
- Risk Management Software
- Vulnerability Management Tools
- DAST Tools
- Intrusion Detection and Prevention Systems
Security Risk Assessment Tool Selection Criteria
When selecting the best security risk assessment tools to include in this list, I considered common buyer needs and pain points like identifying vulnerabilities and ensuring compliance with industry standards. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Identify and assess vulnerabilities
- Monitor security threats
- Generate compliance reports
- Provide risk mitigation strategies
- Support incident response
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat intelligence
- Automated remediation workflows
- Customizable risk dashboards
- Integration with third-party tools
- Advanced data analytics
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Customizable settings
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Supportive chatbots
- Comprehensive webinars
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple support channels
- Fast response times
- Access to a knowledge base
- Personalized assistance
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Discounts for annual billing
- Transparent pricing structure
- Cost-benefit ratio
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on reliability
- Comments on ease of use
- Experiences with customer support
- Opinions on value for money
How to Choose Security Risk Assessment Tools
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the tool grow with your organization? Consider how it handles increased data and users as your company expands. Look for flexible plans that accommodate growth. |
| Integrations | Does it work with your existing systems? Check for compatibility with your current software stack to avoid operational disruptions. |
| Customizability | Can you tailor the tool to your needs? Ensure it offers customization options that fit your workflows and business processes. |
| Ease of use | Is the interface intuitive? Test the tool's usability to ensure your team can adopt it quickly without extensive training. |
| Implementation and onboarding | How long will setup take? Evaluate the onboarding process, including training resources and support, to minimize downtime during implementation. |
| Cost | Does the pricing fit your budget? Compare pricing models and consider additional costs like setup fees or premium support. |
| Security safeguards | Are data protection measures robust? Verify the tool's security features, like encryption and access controls, to protect sensitive information. |
| Compliance requirements | Does it meet regulatory standards? Ensure it aligns with industry-specific regulations to avoid compliance issues. |
What Are Security Risk Assessment Tools?
Security risk assessment tools are software solutions designed to identify, evaluate, and manage security risks within an organization. IT security professionals, risk managers, and compliance officers typically use these tools to protect sensitive data and ensure regulatory compliance.
Features like real-time monitoring, automated reporting, and vulnerability assessments help with identifying threats, managing risks, and maintaining compliance. Overall, these tools provide essential insights and support for safeguarding an organization's digital assets.
Features
When selecting security risk assessment tools, keep an eye out for the following key features:
- Real-time monitoring: Continuously tracks your systems to detect and alert you to potential security threats as they arise.
- Automated reporting: Generates detailed reports on security status and compliance, saving time and ensuring accurate documentation.
- Vulnerability assessments: Identifies weaknesses in your systems and helps prioritize remediation efforts to reduce risk exposure.
- Risk quantification: Measures the potential impact of identified risks, allowing you to make informed decisions about risk management.
- Customizable dashboards: Offers tailored views of your security data, so you can focus on the most relevant information for your needs.
- Compliance tracking: Ensures your organization meets industry standards and regulatory requirements, reducing the risk of penalties.
- Workflow automation: Streamlines security processes and responses, increasing efficiency and reducing manual intervention.
- Data discovery and classification: Finds and categorizes sensitive data, aiding in its protection and compliance with data regulations.
- Threat intelligence: Provides insights into emerging threats to help you proactively defend against potential attacks.
- Integration capabilities: Connects with existing systems and tools for seamless data exchange and improved security operations.
Benefits
Implementing security risk assessment tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved threat detection: Real-time monitoring helps identify potential security threats quickly, allowing for faster response and mitigation.
- Enhanced compliance: Automated reporting and compliance tracking ensure your organization meets regulatory standards, reducing the risk of penalties.
- Efficient risk management: Vulnerability assessments and risk quantification prioritize risks, enabling informed decision-making and resource allocation.
- Time savings: Workflow automation streamlines processes, reducing manual tasks and freeing up your team to focus on strategic initiatives.
- Data protection: Data discovery and classification safeguard sensitive information, helping maintain privacy and compliance with data regulations.
- Proactive defense: Threat intelligence provides insights into emerging threats, allowing you to prepare and defend against potential attacks.
- Customizable insights: Customizable dashboards offer tailored views of security data, helping you focus on the most relevant information for your needs.
Costs & Pricing
Selecting security risk assessment tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in security risk assessment tools solutions:
Plan Comparison Table for Security Risk Assessment Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0/user/month | Basic vulnerability scanning, limited reporting, and community support. |
| Personal Plan | $10-$30/user/month | Real-time monitoring, automated reports, and basic compliance tracking. |
| Business Plan | $40-$80/user/month | Advanced risk assessments, workflow automation, and customizable dashboards. |
| Enterprise Plan | $100-$200/user/month | Full integration capabilities, comprehensive data protection, and dedicated customer support. |
Security Risk Assessment Tools FAQs
Who uses security risk assessment tools?
They’re mainly used by IT teams, business owners, and compliance officers who want to understand and manage possible risks in their operations.
How often should a security risk assessment be done?
It’s best to perform one regularly at least a few times a year or whenever you make major changes to your systems or software.
Can small businesses use these tools?
Yes. Many options are simple enough for smaller teams to use. They help businesses of any size spot risks early and stay organized.
Do these tools work with other software?
Most of them do. They can connect with common work systems, making it easier to keep everything in one place and avoid repeating tasks.
How long does setup usually take?
Setup time depends on how complex your system is. Some tools can be ready in a few hours, while others might take a few days to fully configure.
What challenges do teams face when using these tools?
The main challenges include learning how to use the software, managing large amounts of information, and making sure results are understood and acted upon.
What’s the difference between a security scan and a full risk assessment?
A security scan checks for technical issues, like unsafe files or weak passwords. A full risk assessment looks at the bigger picture, including people, processes, and how your systems are managed overall.
How do these tools help with long-term safety planning?
They record and track risks over time, helping teams see patterns and make better plans for preventing future problems.
What’s Next:
If you're in the process of researching security risk assessment tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.