10 Best Packet Sniffer Tools Shortlist
Finding the right packet sniffer can significantly streamline network troubleshooting and boost security monitoring, whether you’re analyzing traffic patterns, detecting anomalies, or optimizing network performance.
However, the sheer number of available network analysis tools - combined with the challenge of deciphering complex data and choosing the right features - can make selecting the best option overwhelming.
In this article, I draw on my network security experience and hands-on testing of dozens of packet sniffers to explain what these tools offer, who they’re best suited for, and how they can help enhance network visibility, identify threats, and improve overall performance.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Packet Sniffer Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for sFlow packet sampling | 30-day free trial + free demo available | From $10/month (billed annually) | Website | |
| 2 | Best for deep packet analysis | Free download available | Free to use (open source) | Website | |
| 3 | Best or bandwidth and traffic monitoring | Free demo available | From $17.20/user/month for 10 interfaces (billed annually) | Website | |
| 4 | Best for debugging web traffic | Free demo available | Pricing upon request | Website | |
| 5 | Best for network discovery and auditing | Not available | Free to use | Website | |
| 6 | Best for command-line packet capture | Not available | Free forever | Website | |
| 7 | Best for intrusion detection and prevention | Free demo available | From $29.99/year (billed annually) | Website | |
| 8 | Best for passive network forensics | Not available | Pricing upon request | Website | |
| 9 | Best for wireless network detection | Not available | Free forever | Website | |
| 10 | Best for network troubleshooting and diagnostics | Not available | Pricing upon request | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Packet Sniffer Reviews
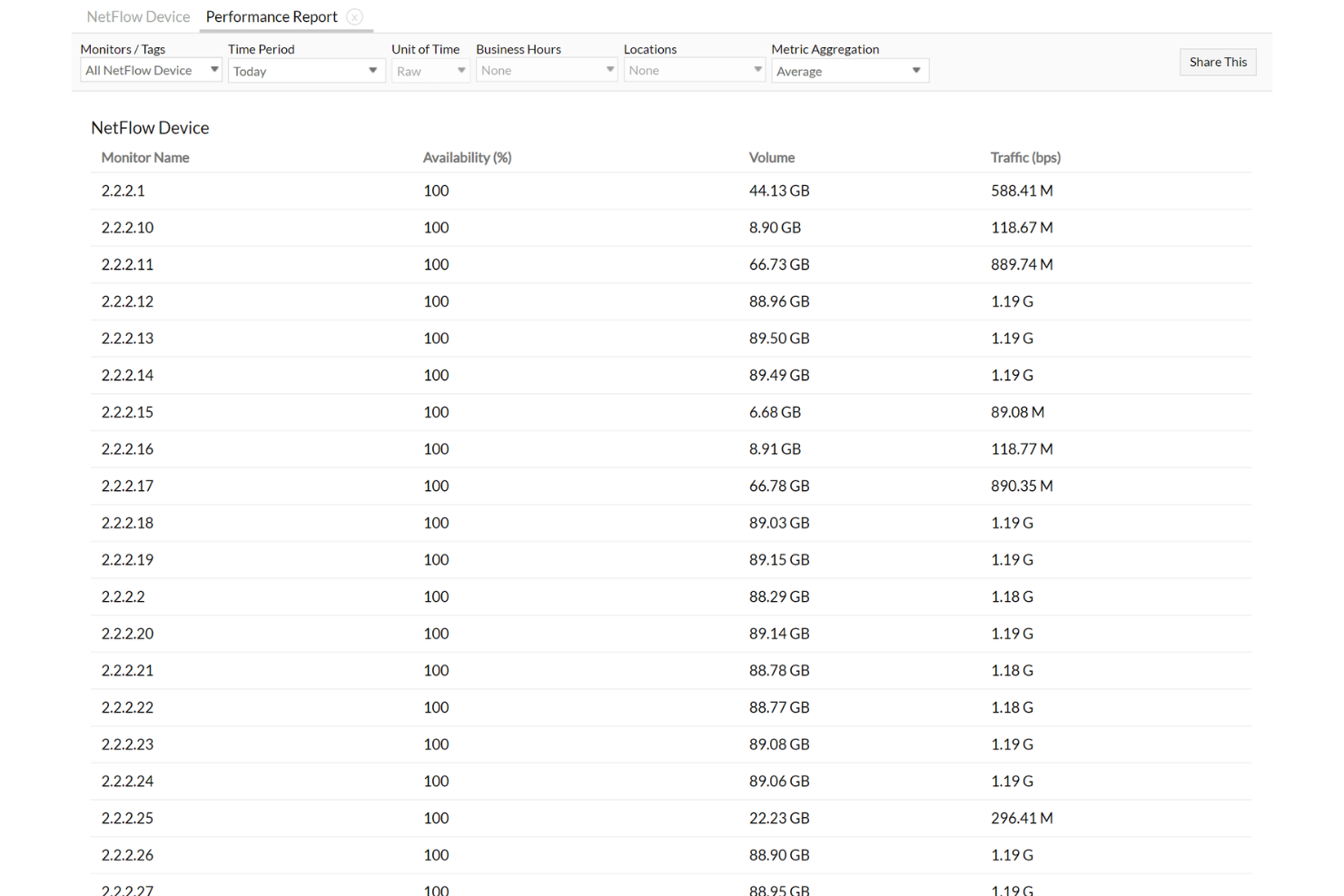
Site24x7 is on this list because of how precise and reliable its sFlow packet sampling is, especially at scale. When I’m working with distributed teams that need deep visibility into network traffic patterns across multiple locations, Site24x7 delivers accurate, real-time packet data. I appreciate its sFlow collector and live traffic analytics, which give you quick insight for both troubleshooting and ongoing capacity planning.
Site24x7’s Best For
- IT teams monitoring network traffic with sFlow sampling
- Organizations managing multi-site or distributed network environments
Site24x7’s Not Great For
- Anyone needing deep packet inspection or payload capture
- Teams focused on on-premises-only or offline analysis
What sets Site24x7 apart
Site24x7 takes a network monitoring approach that’s driven more by high-level traffic visibility than by forensic detail. I see teams use it when they want to keep tabs on live network flows across distributed environments, similar to SolarWinds NetFlow Analyzer but with more emphasis on cloud-first operations and simplified deployment. In practice, you rely on sFlow to visualize trends, not to drill into individual packet contents.
Tradeoffs with Site24x7
By focusing on sFlow and aggregate traffic data, you lose the ability to capture and inspect packet payloads, so forensic analysis and deep debugging require other tools.
Pros and Cons
Pros:
- Flexible customization options for dashboards and reports
- Reliable real-time alerts that enable prompt issue resolution
- Comprehensive monitoring capabilities across various IT infrastructure components
Cons:
- Limited integration options with certain third-party tools
- Configuration complexity can be challenging for new users
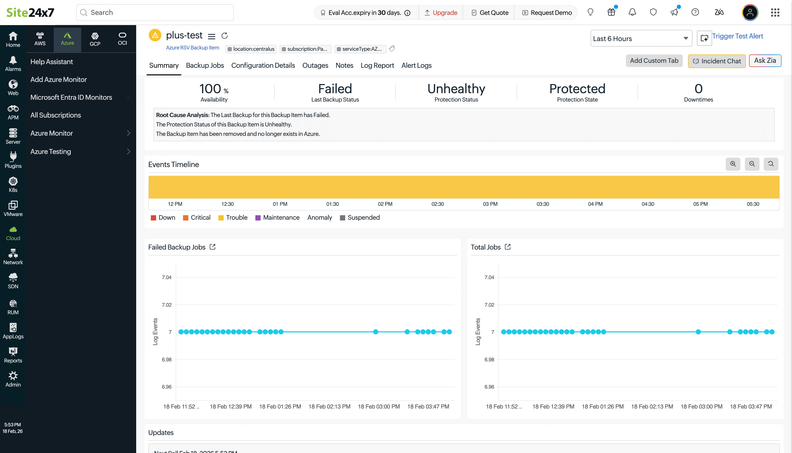
New Product Updates from Site24x7
Site24x7 Adds Azure Backup and Multi-Cloud Monitoring Updates
Site24x7’s new update adds per-item Azure Recovery Services Vault backup monitoring and extends monitoring to five new cloud providers, giving you deeper backup insights and unified multi-cloud visibility. For more information, visit Site24x7’s official site.
Wireshark earns its spot here because it gives me the level of detail I rarely find anywhere else when analyzing network traffic. What sets it apart is the depth you get slicing live or historical packet captures, letting you drill into protocol data, inspect headers, and decode proprietary formats.
I appreciate being able to filter, search, and follow specific streams for root-cause analysis. For troubleshooting tricky connectivity issues or catching subtle security threats, you gain near surgical visibility.
Wireshark’s Best For
- Network engineers needing deep protocol and packet analysis
- Security analysts investigating advanced network threats and anomalies
Wireshark’s Not Great For
- Beginners who need a simple, guided packet sniffer
- Teams seeking automated insights rather than manual investigation
What sets Wireshark apart
Wireshark is built around letting you see everything happening on your network at the lowest possible level. It expects you to drill into packets and protocol details, not just watch for basic traffic flows like you might with tools such as tcpdump or SolarWinds. In practice, this works well when you need to understand exactly how data moves or hunt for obscure issues that other tools simply gloss over.
Tradeoffs with Wireshark
Wireshark optimizes for hands-on, manual inspection, but you sacrifice simplicity. If you want automated analysis or a quick readout, tools that abstract away packet detail are a better fit.
Pros and Cons
Pros:
- Robust filtering capabilities
- Supports a wide range of data network protocols
- Comprehensive packet data analysis
Cons:
- Potential security risks if used carelessly on public networks.
- Requires significant system resources for large captures
- Steeper learning curve for beginners
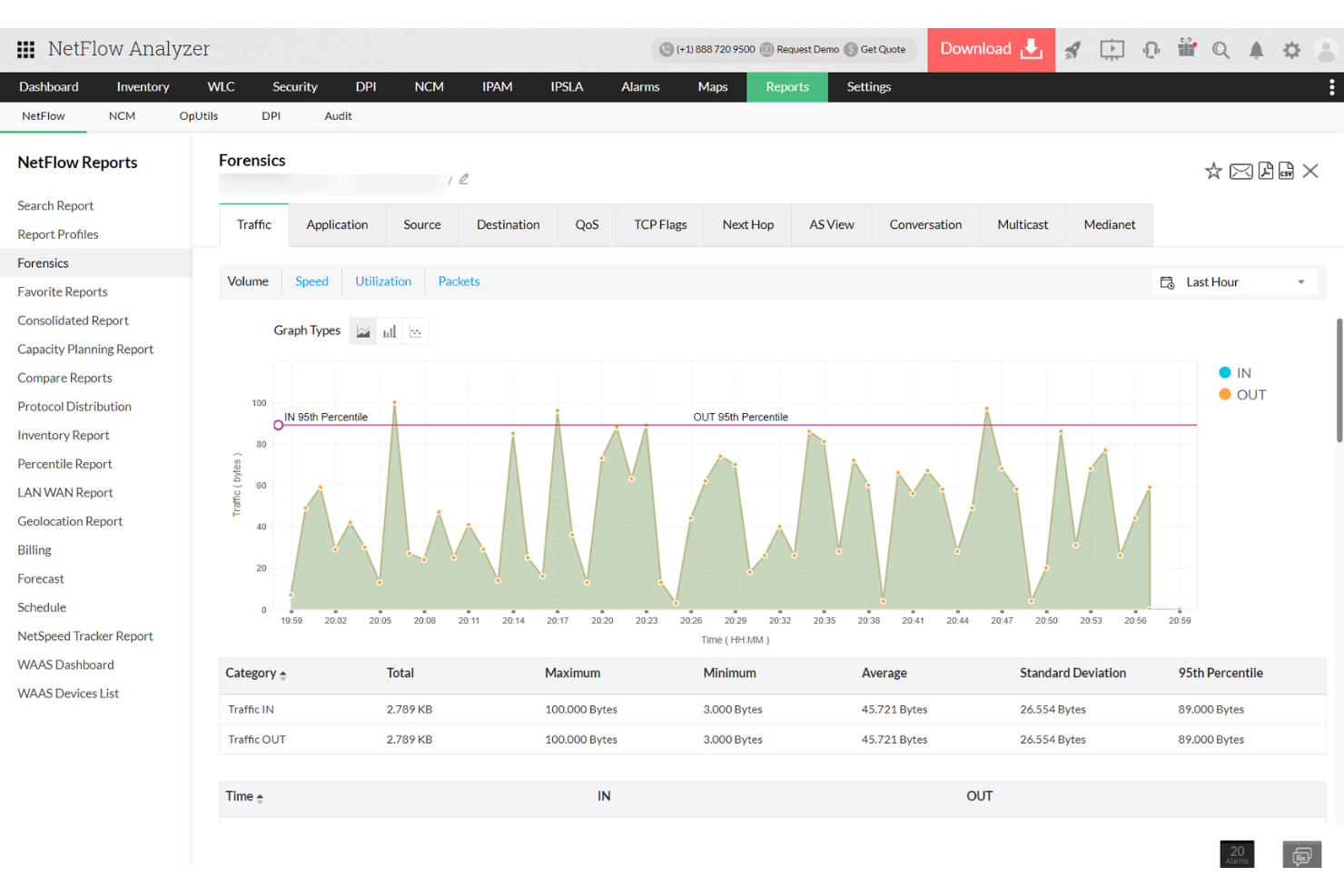
ManageEngine NetFlow Analyzer is on my list because it excels at drilling into bandwidth usage and live traffic patterns right down to the application or interface. I typically bring it up when teams need to catch network congestion or spot excessive traffic from specific IPs.
You get real-time monitoring, flow-based traffic analysis, and usage forensics all in one dashboard. What I like most is how easily you can trace network spikes to root causes and prioritize troubleshooting.
NetFlow Analyzer’s Best For
- Network teams monitoring bandwidth usage and traffic in real time
- Organizations diagnosing congestion and analyzing usage by application or host
NetFlow Analyzer’s Not Great For
- Packet-level inspection or deep packet analysis tasks
- Environments needing protocol decoding beyond flow-based data
What Sets NetFlow Analyzer Apart
NetFlow Analyzer stands out because it’s built around flow-level visibility that focuses on the big picture of bandwidth consumption and traffic origins. Unlike packet sniffers like Wireshark, it doesn’t chase after every individual packet detail. In practice, I’ve seen it used by network admins who want to catch congestion, abnormal traffic, or spikes at a high level before diving into protocol-level analysis elsewhere.
Tradeoffs with NetFlow Analyzer
NetFlow Analyzer optimizes for surface-level monitoring and traffic analysis, but this comes at the cost of lacking access to full packet payloads, so you won’t be able to do deep forensic or content inspection within it.
Pros and Cons
Pros:
- Utilizes Cisco NBAR for deep insights into application traffic
- Displays traffic patterns and trends through intuitive graphs and charts
- Monitors network traffic in real-time
Cons:
- Manual setup for device compatibility
- Slow reporting during peak times
Fiddler makes this list because few tools give you such fine control over inspecting and manipulating HTTP, HTTPS, and WebSocket traffic in real time. I suggest teams use it when they need to dig deep into web traffic, debug tricky sessions, or simulate network conditions to trigger specific issues.
What I like is how you can modify requests and responses on the fly, making it easy to validate fixes or uncover hidden problems with browser or API traffic.
Fiddler’s Best For
- Developers debugging HTTP, HTTPS, and WebSocket traffic
- Teams that need to inspect and modify web sessions
Fiddler’s Not Great For
- Deep packet-level network analysis (full packet capture)
- Monitoring encrypted traffic without manual certificate setup
What sets Fiddler apart
Fiddler is focused on giving you direct, hands-on access to HTTP, HTTPS, and WebSocket traffic as it flows. Unlike network-level packet capture tools like Wireshark, Fiddler assumes you want to work at the application layer. In practice, this is good for debugging, reverse engineering, and simulating traffic. You can actively modify traffic and replay sessions, which is different from traditional packet sniffers.
Tradeoffs with Fiddler
Fiddler optimizes for visibility and control at the web protocol level, but you lose deep insight into lower-level or non-HTTP traffic, so it’s not suited for full-stack network analysis.
Pros and Cons
Pros:
- Compatible with multiple development and testing tools
- Composer' tool aids in creating custom requests for testing
- Detailed traffic logging enables thorough inspection
Cons:
- The tool's performance may vary across different operating systems.
- Requires configuration for capturing traffic from certain devices
- Some features might be overwhelming for beginners
NMap makes my list because it’s one of the first tools I reach for when I need to map out active hosts and audit network assets. I like that NMap digs deeper than most packet sniffers by using network discovery scans alongside packet capture, so you see what’s running, which ports are open, and potential vulnerabilities.
I appreciate its command-line flexibility, letting you script complex scans and automate reporting. This comes in handy for teams running regular audits or troubleshooting inconsistent network behavior.
NMap’s Best For
- Network engineers auditing assets, open ports, and services
- Security pros or admins mapping and scanning large networks
NMap’s Not Great For
- Beginners who want a plug-and-play packet sniffer
- Real-time traffic analysis or deep packet inspection
What sets NMap apart
NMap stands out by putting discovery and audit workflows front and center. Instead of focusing on live packet capture like Wireshark, NMap treats your network like an asset map, highlighting what’s out there, how it responds, and what might be exposed. In practice, I use it to quickly survey environments and identify targets or misconfigurations before going deeper with more granular tools.
Tradeoffs with NMap
NMap prioritizes visibility and asset mapping, but you lose real-time data capture and analysis. This means you still need a true packet sniffer for traffic content or protocol troubleshooting.
Pros and Cons
Pros:
- Established reputation with years of proven reliability
- NSE allows for custom script creation, offering a tailored scanning experience.
- Comprehensive scanning capabilities cover a wide range of network attributes.
Cons:
- Command-line interface may not be user-friendly for all, requiring familiarity or additional training.
- Scans, if not configured properly, can be intrusive and disruptive to some network devices
- Steep learning curve for newcomers
Tcpdump earns its spot for those moments when you need granular, real-time packet capture straight from the command line. I think it’s especially good when you want precise filtering on busy networks or need evidence for a security review.
What I like is how Tcpdump lets you dig into live traffic with fine-grained capture rules and output formats. In practice, I see teams use it when diagnosing intermittent connectivity, validating firewall rules, or grabbing proof in incident response work.
Tcpdump’s Best For
- Network engineers troubleshooting at packet level
- Security teams capturing evidence from live traffic
Tcpdump’s Not Great For
- Anyone wanting a graphical interface or visual analysis
- Beginners needing guided setup or protocol decoding
What sets Tcpdump apart
Tcpdump stands out by sticking with a command-line-first approach that expects you to know the exact traffic or protocols you need to capture. Unlike Wireshark, which gives you a visual interface for building filters and browsing sessions, Tcpdump focuses on precision and speed in live environments. This works well when you need quick packet insights right from the terminal, without launching a GUI or storing gigabytes of data.
Tradeoffs with Tcpdump
Tcpdump optimizes for speed, transparency, and low resource usage, but you lose visual flow analysis and protocol breakdowns, so troubleshooting complex streams is slower without complementary tools.
Pros and Cons
Pros:
- Portable across multiple platforms
- Fine-grained packet filtering with BPF
- Lightweight with minimal system resource usage
Cons:
- Initial learning curve for beginners due to command-line nature.
- Might require supplemental tools for in-depth analysis
- Lacks a graphical user interface
Snort is on my list because it brings real network intrusion detection and prevention capabilities together with packet sniffing, which I rarely see handled at this level. You get deep packet inspection, real-time packet logging, and alerting based on flexible rules sets. I like how you can set up custom detection rules that respond instantly to suspicious traffic patterns, helping you catch issues as they happen. This works best for teams that need strong perimeter monitoring built right into packet analysis.
Snort’s Best For
- Security and network engineering teams needing intrusion detection
- Organizations that want packet sniffing with threat prevention
Snort’s Not Great For
- Users who just want simple packet capture and analysis
- Teams looking for a beginner-friendly interface
What sets Snort apart
Snort stands out by combining real-time packet sniffing with live intrusion detection in a way that expects you to think defensively, not just analytically. Unlike Wireshark, which focuses on capturing and analyzing traffic, Snort expects you to define and enforce rules for blocking threats as they cross the wire. In practice, this is good for admins who want active control over network security instead of just post-event diagnostics.
Tradeoffs with Snort
Snort is optimized for threat prevention and rule-based analysis, but its focus on detection and response means you lose some of the visual forensics and traffic exploration you get from traditional packet analyzers.
Pros and Cons
Pros:
- Supported by a vast and active community providing continuous updates
- Signature-based detection system offers extensive coverage against different types of attacks
- Real-time traffic analysis facilitates instant threat detection
Cons:
- May generate false positives, requiring careful configuration and tuning.
- As an open-source tool, it might lack some of the advanced features available in commercial solutions
- The initial setup can be complex for beginners
Network Miner stands out when you want to run deep packet inspection without creating extra network noise. I like how it passively reconstructs sessions, credentials, and files from captured traffic, which makes it valuable in forensics or when you can't risk interrupting live environments.
I've found it especially useful during incident investigations where stealth is a top priority.
Network Miner's Best For
- Investigators needing passive network forensics and packet analysis
- Teams analyzing evidence without altering network traffic
Network Miner's Not Great For
- Real-time monitoring or live intrusion detection
- Users wanting detailed active traffic manipulation or interception
What sets Network Miner apart
Network Miner is designed to let you investigate captured network data quietly, without disrupting anything on the network itself. Unlike tools like Wireshark that expect you to work interactively and follow live traffic, Network Miner sits off to the side and lets you pull apart evidence after the fact. I find it works best when you need to examine full sessions for forensics, especially when you don’t want to risk tipping off anyone monitoring activity.
Tradeoffs with Network Miner
Network Miner optimizes for passive, post-capture analysis, so you miss out on interactive real-time monitoring and quick response capabilities that more active packet sniffers provide.
Pros and Cons
Pros:
- Passive approach ensures minimal interference with network operations
- Comprehensive host-centric view of network interactions
- Efficient file extraction from network traffic
Cons:
- Limited customization options compared to some competitors.
- Not optimized for real-time intrusion detection
- Might require a learning curve for those unfamiliar with forensics
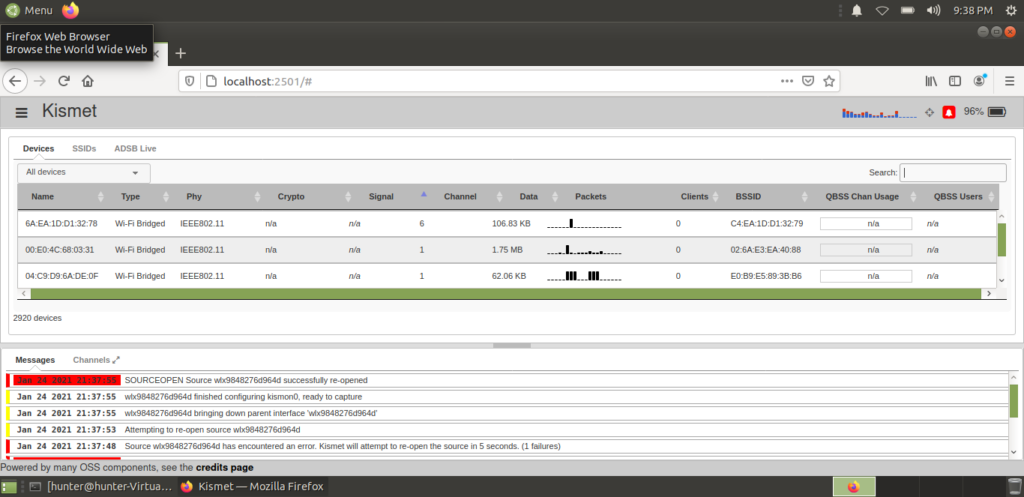
Kismet earns its spot for handling passive wireless network detection and packet sniffing in environments that other tools miss. I regularly see security teams use its real-time detection of hidden or rogue devices across both Wi-Fi and Bluetooth spectrums. The plugin system is excellent for tailoring scans and extending support to less common hardware, which I genuinely appreciate when working with complex deployments.
Kismet’s Best For
- Wireless security teams scanning for unauthorized or hidden devices
- Packet sniffing across Wi-Fi, Bluetooth, and non-traditional networks
Kismet’s Not Great For
- Wired network packet analysis or Ethernet-specific workflows
- Beginners who need guided setup or simple dashboards
What sets Kismet apart
Kismet approaches wireless packet sniffing like a toolkit for specialists who want total transparency of the wireless environment. Unlike Wireshark, which focuses on dissecting captured packets, Kismet emphasizes real-time discovery and live monitoring for signals many tools miss. I see organizations rely on it for tracking rogue access points and monitoring less-standard protocols alongside Wi-Fi.
Tradeoffs with Kismet
Kismet optimizes for breadth in wireless detection, but you lose out on wired analysis and get a steeper learning curve, especially if you’re new to command-line or Linux systems.
Pros and Cons
Pros:
- Equipped with real-time intrusion detection
- Offers support for a multitude of wireless protocols
- Exceptional at detecting hidden wireless networks
Cons:
- Interface may not be intuitive for all users.
- Resource-intensive when handling large network scans
- Might be overwhelming for beginners
Omnipeek is on this list because it’s consistently reliable for advanced packet capture and real-time traffic analysis during tough network troubleshooting scenarios. When I’ve worked with teams trying to pinpoint bottlenecks or zero in on intermittent issues, Omnipeek’s deep packet inspection and flow analytics have offered visibility that typical sniffers can’t match.
What stands out for me is the way protocol analysis is layered right into the UI, so you can quickly drill into anomalies without a lot of manual parsing.
Omnipeek’s Best For
- Network engineers troubleshooting complex, multi-protocol environments
- Teams needing detailed, real-time packet and protocol analysis
Omnipeek’s Not Great For
- Beginners looking for basic packet sniffing only
- Organizations with minimal need for protocol-level diagnostics
What sets Omnipeek apart
Omnipeek stands out for how directly it puts detailed, real-time packet analysis in front of you during active troubleshooting. Unlike Wireshark, which is more focused on in-depth post-capture inspection, Omnipeek is designed for teams who need to watch live network traffic and quickly spot protocol anomalies as they happen. This approach works best when network slowdowns or intermittent problems demand immediate investigation.
Tradeoffs with Omnipeek
Omnipeek optimizes for advanced, real-time diagnostics, but that focus means it’s less approachable for those just needing basic capture or simple visualization.
Pros and Cons
Pros:
- Adaptable with numerous third-party integrations
- Real-time insights facilitate swift issue identification and resolution
- Mastery in detailed packet capture and network analysis
Cons:
- Some features might be excessive for small-scale network environments.
- Pricier than some basic diagnostic tools
- Steeper learning curve for newcomers to network analysis
Other Noteworthy Packet Sniffer
Below is a list of additional packet sniffers that I shortlisted but did not make it to the top 12. Definitely still worth checking out!
- Ettercap
For man-in-the-middle attacks
- CommView
For real-time packet capture and analysis
- Colasoft Capsa
For real-time network diagnostics
- PRTG
For customizable packet monitoring
- SolarWinds Network Performance Monitor
For scalable network performance monitoring
- ManageEngine NetFlow Analyzer
For bandwidth monitoring and traffic analysis
- NirSoft's SmartSniff
Good for straightforward packet capture without complex configurations
- netsniff-ng
Good for efficient packet capturing on Linux systems
- TCPView
Good for real-time monitoring of TCP/UDP endpoints on Windows
- Iperf
Good for bandwidth performance measurement and tuning
- KisMAC2
Good for advanced Wi-Fi network discovery on macOS platforms
Packet Sniffer Selection Criteria
When selecting the best packet sniffer to include in this list, I considered common buyer needs and pain points like network performance monitoring and data packet analysis. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Monitor network traffic
- Capture data packets
- Analyze protocol layers
- Diagnose network issues
- Filter specific data streams
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time data visualization
- Customizable alerts
- Integration with security tools
- Cloud compatibility
- Advanced filtering options
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Easy navigation
- Customizable dashboard
- Minimal learning curve
- Accessibility on multiple devices
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Use of chatbots for guidance
- Availability of setup templates
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple support channels
- Comprehensive FAQ section
- Response time efficiency
- Access to community forums
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Feature set relative to cost
- Availability of free trials
- Flexible pricing plans
- Cost transparency
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Consistency of positive feedback
- Mention of ease of use
- Reliability of the tool
- Quality of customer support
- Value for money perception
How to Choose Packet Sniffer
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the tool grow with your network needs? Consider if it supports increasing data loads and user numbers without performance drops. |
| Integrations | Does it work with your current tools? Check compatibility with existing systems like security software and network management tools. |
| Customizability | Can you tailor it to your needs? Look for adjustable settings and dashboards that fit your specific monitoring requirements. |
| Ease of use | Is the interface straightforward? Ensure your team can navigate it easily without extensive training. |
| Implementation and onboarding | How quickly can you start using it? Evaluate the time and resources needed for setup and training. |
| Cost | Does it fit your budget? Compare pricing models and watch for hidden fees or long-term contracts. |
| Security safeguards | Does it protect data effectively? Assess encryption standards and compliance with data protection regulations. |
| Support availability | Can you get help when needed? Verify the availability of tech support and resources like forums or knowledge bases. |
What Is a Packet Sniffer?
A packet sniffer, also known as a network sniffer or packet analyzer, is a diagnostic tool that captures, analyzes, and deciphers data packets as they traverse various network interfaces. It can operate in promiscuous mode, observing data regardless of its intended destination.
Such tools become indispensable, especially when dealing with routers and their traffic. Network administrators and IT professionals use them as network performance monitors, gaining insights into traffic patterns and potential root causes of issues.
This packet capture tool provides detailed views, enabling users to understand network behaviors. Beyond just an adapter for viewing data, it is a frontline defense against threats and ensures the network's optimal condition.
Features
When selecting a packet sniffer, keep an eye out for the following key features:
- Real-time data visualization: Displays network traffic in real-time, helping you quickly identify issues as they occur.
- Customizable alerts: Allows you to set specific triggers for alerts, ensuring you stay informed about critical network events.
- Protocol analysis: Analyzes various protocol layers to diagnose and troubleshoot network problems efficiently.
- Advanced filtering options: Lets you filter data packets based on criteria, streamlining the analysis process.
- Integration capabilities: Works seamlessly with existing network management and security tools to enhance functionality.
- Data packet capture: Collects data packets traveling across the network, providing insights into traffic patterns.
- User-friendly interface: Ensures easy navigation and operation, reducing the learning curve for new users.
- Encryption standards: Protects sensitive data with robust encryption, ensuring compliance with data protection regulations.
- Scalability: Supports growing network demands, accommodating increased data loads and user numbers.
Benefits
Implementing packet sniffer provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved network performance: By analyzing traffic in real-time, you can quickly identify and address bottlenecks and inefficiencies.
- Enhanced security: Customizable alerts and protocol analysis help detect suspicious activities and potential threats early.
- Efficient troubleshooting: Advanced filtering options and data packet capture allow for precise issue identification and resolution.
- Cost savings: Early detection of network issues prevents costly downtime and reduces the need for extensive IT intervention.
- Scalability support: The ability to handle growing network demands ensures your tools evolve with your business needs.
- Compliance assurance: Encryption standards and data protection features help meet regulatory requirements, safeguarding sensitive information.
Costs & Pricing
Selecting a packet sniffer requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in packet sniffer solutions:
Plan Comparison Table for Packet Sniffer
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic packet capture, limited data analysis, and community support. |
| Personal Plan | $5-$25/user/month | Advanced filtering, real-time monitoring, and email alerts. |
| Business Plan | $30-$75/user/month | Protocol analysis, integration with other tools, and customizable dashboards. |
| Enterprise Plan | $100+/user/month | Full data encryption, priority customer support, and scalability for large networks. |
Most Common Questions Regarding Packet Sniffers (FAQ's)
Which are the cheapest and most expensive packet sniffers?
The cheapest options typically include freemium tools or basic versions of commercial tools. Examples are Wireshark, which is free, and some entry-level versions of commercial products. On the other end, tools like SolarWinds or CommView offer advanced functionalities and cater to large enterprises, making them some of the pricier options on the market.
Are there any free packet sniffer options?
Yes, there are free packet sniffers available. Wireshark is one of the most renowned free options, widely recognized for its comprehensive functionality. However, while free tools provide essential features for advanced capabilities or enterprise-grade needs, a commercial tool might be more suitable.
What should you consider when choosing a packet sniffer?
When selecting a packet sniffer, consider factors like scalability, integration capabilities, ease of use, and security safeguards. Evaluate how well it fits your network’s needs and ensure it supports your team’s workflow to maximize its effectiveness.
Can packet sniffers capture encrypted data?
Packet sniffers can capture encrypted data packets, but they cannot decrypt them without the proper encryption keys. While they can see the data flow, they can’t access the content, maintaining a level of security for encrypted communications.
Other Network Security Software Reviews
- Network Intrusion Detection Systems
- Network Security Software
- Intrusion Detection and Prevention Systems
What’s Next?
Boost your SaaS growth and leadership skills.
Subscribe to our newsletter for the latest insights from CTOs and aspiring tech leaders.
We'll help you scale smarter and lead stronger with guides, resources, and strategies from top experts!