10 Best Data Loss Prevention Software Shortlist
Here's my pick of the 10 best software from the 26 tools reviewed.
In today's digital world, keeping your data safe is a top priority. Data loss can be a nightmare for you and your team, leading to lost time, money, and trust. That's where data loss prevention software comes in—it helps you protect sensitive information and ensure compliance with regulations.
I test and review software independently, focusing on what truly matters to tech experts like you. In my experience, finding the right data loss prevention tools can make all the difference in safeguarding your business.
In this article, I'll share my top picks for data loss prevention software. You'll get an unbiased look at features, pros and cons, and how these tools can alleviate your challenges. Let's dive in and find the best fit for your needs.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Data Loss Prevention Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for insider threat detection | Free trial + free demo available | From $14/user/month (billed annually) | Website | |
| 2 | Best for threat detection and response | Not available | From $15/user/month (billed annually) | Website | |
| 3 | Best for large-scale enterprise data protection | Not available | Customized price upon request | Website | |
| 4 | Best for holistic data protection across hybrid cloud environments | Not available | Pricing upon request | Website | |
| 5 | Best for database security and compliance | 30-day free trial available | Pricing upon request | Website | |
| 6 | Best for advanced machine learning-based protection | Not available | Pricing upon request | Website | |
| 7 | Best for context-aware data security | Not available | From $10/user/month (billed annually) | Website | |
| 8 | Best for integrated endpoint and network security | Not available | From $15/user/month | Website | |
| 9 | Best for cloud-native environments | Not available | From $10/user/month (billed annually) | Website | |
| 10 | Best for USB and peripheral device control | Not available | From $17.99/user/month (billed annually) | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Data Loss Prevention Software Reviews
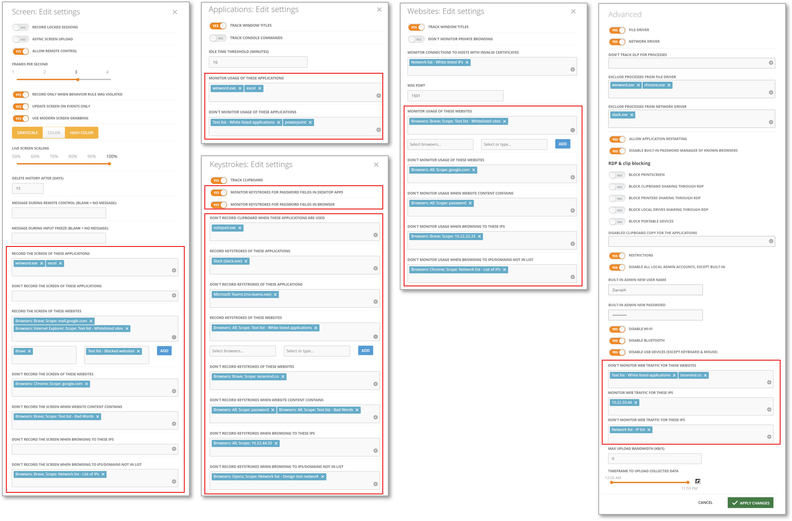
Teramind is a security tool that helps monitor user behavior and protect sensitive data from leaking or being misused. It works as an endpoint-based solution that watches what users do on their devices, applications, networks, and files. Its data loss prevention (DLP) capability focuses on detecting and blocking risky actions in real time to prevent unauthorized data exfiltration.
Why I Picked Teramind:
I picked Teramind because it blends behavior analytics with content awareness to catch insider threats that simple rules often miss. It tracks baseline user behavior so it can spot anomalies (e.g., someone suddenly transferring large volumes of sensitive files) rather than relying solely on fixed rules. Its zero-trust data governance monitors data access continuously, even for privileged users, helping you enforce least-privilege policies. When a risky behavior is detected, Teramind lets you intervene immediately—with notifications, blocking, or session termination—to stop data loss before damage happens.
Standout features and integrations:
Other features include a comprehensive content analysis engine that can find sensitive data even in complex file formats or in embedded text (not just in plain documents). It also supports full forensic-ready incident response by capturing detailed timelines, session playback, and screen recordings so you can trace exactly what happened. Integrations include ServiceNow, Splunk, HP ArcSight, IBM QRadar, McAfee, LogRhythm, NetIQ, Microsoft Purview, JIRA, Zendesk, Redmine, and Active Directory.
Pros and Cons
Pros:
- Blocks data leaks proactively, not just detect after
- Granular risk scoring helps reduce false positives
- Catches insider threats missed by rule-only systems
Cons:
- Requires endpoint agent installation on every device
- No database fingerprinting of structured data
New Product Updates from Teramind
Teramind Enhances Tracking Flexibility, Mac Parity, and Security Controls
Teramind introduces flexible monitoring configuration, expanded Mac agent capabilities, and stronger security and data protection controls. These updates give organizations more precise tracking, improved cross-platform monitoring, and tighter privacy-focused security. For more information, visit Teramind’s official site.
Proofpoint Enterprise DLP is a comprehensive data security solution that excels in threat detection and response. It leverages advanced analytics to swiftly identify and respond to threats, ensuring the safety of sensitive data. It’s exceptional threat detection and response performance makes it a perfect choice for organizations that prioritize immediate action against data breaches.
Why I Picked Proofpoint Enterprise Data Loss Prevention:
I selected Proofpoint Enterprise DLP for its excellence in threat detection and response. This tool stands apart because of its ability to swiftly detect potential data loss threats and respond proactively, thereby reducing the potential damage from data breaches. It is "best for" the threat detection and response use case because it focuses on swiftly identifying and remedying threats.
Standout features and integrations:
Proofpoint Enterprise DLP is renowned for its advanced threat detection, comprehensive visibility, and rapid response capabilities. Additionally, the tool integrates with other Proofpoint solutions like Proofpoint endpoint DLP and provides efficient email and cloud application security.
Pros and Cons
Pros:
- Provides comprehensive visibility into data security.
- Integrates with other Proofpoint solutions.
- Exceptional threat detection and response capabilities.
Cons:
- May be complex for small businesses to deploy and manage.
- Extra costs may apply for advanced features.
- Higher starting price compared to other DLP solutions.
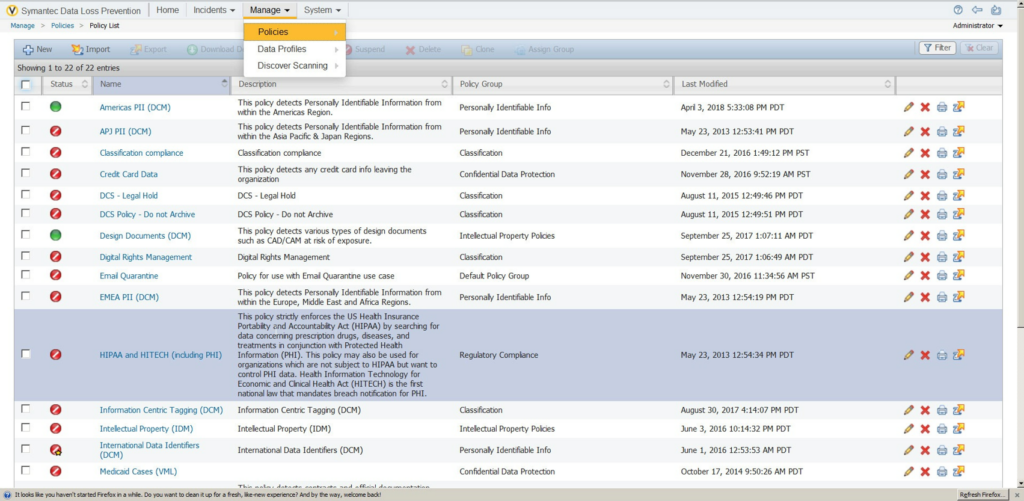
Symantec Data Loss Prevention (Broadcom Symantec DLP) is a comprehensive solution designed to discover, monitor, and protect sensitive information across all business points. With its capability to scale and meet the needs of large enterprises, it excels in enterprise data protection.
Why I Picked Symantec Data Loss Prevention:
I selected Symantec Data Loss Prevention for its robust capabilities in large-scale data protection. Its high scalability makes it a fit choice for extensive enterprises. Judging its potential, I determined it to be the best tool for large-scale enterprise data protection as it can efficiently handle the complex and vast data structures that large businesses typically have.
Standout features and integrations:
Critical features of Symantec Data Loss Prevention include precise incident detection, unified policy management, and detailed data risk analysis. Its deep integration with other Symantec products, like Symantec Endpoint Protection and Symantec CloudSOC, makes it a highly versatile tool.
Pros and Cons
Pros:
- Integrates deeply with other Symantec products.
- Offers unified policy management.
- Can handle large-scale enterprise requirements.
Cons:
- Setup and management could be time-consuming.
- It might be too complex for smaller organizations.
- Pricing information is not readily available.
Best for holistic data protection across hybrid cloud environments
IBM Data Security provides a comprehensive solution for managing and protecting data across diverse environments. It's specifically designed for hybrid cloud environments, providing robust security measures to safeguard sensitive information, making it ideally suited for businesses that rely on these systems.
Why I Picked IBM Data Security:
I chose IBM Data Security for this list mainly because of its comprehensive approach to data protection across hybrid cloud environments. Unlike other data security tools, IBM's solution stands out for its holistic, integrative strategy encompassing a wide range of data protection functionalities. I concluded that it is the best for hybrid cloud environments based on its dedicated features and capabilities tailored to these specific setups.
Standout features and integrations:
IBM Data Security offers a variety of notable features, including data activity monitoring, data risk analysis, and a unified data security platform. As for integrations, IBM Data Security provides compatibility with various IBM solutions and other third-party systems, which can be crucial for businesses operating in complex, hybrid cloud environments.
Pros and Cons
Pros:
- Wide range of compatible integrations.
- Offers a unified platform for all data security needs.
- Comprehensive solution for data protection in hybrid cloud environments.
Cons:
- Potential learning curve due to its wide array of features.
- It may be too complex for small businesses.
- Pricing information is not readily available.
Imperva is a cybersecurity software that protects your data and applications comprehensively. It focuses on safeguarding databases, often prime targets for attackers, and offers tools for achieving compliance with regulatory standards.
Why I Picked Imperva:
Imperva caught my attention because of its strong emphasis on database security. While many tools protect data at rest and in transit, Imperva stands out due to its specific focus on databases, a crucial component of data security often overlooked by other platforms. I've selected it as "best for" database security and compliance due to its robust features that protect database environments and aid in meeting compliance regulations.
Standout features and integrations:
Imperva provides robust database security features like data risk analytics, real-time activity monitoring, and automated threat responses. It also integrates with other security tools and technologies, enhancing its overall threat-detection capabilities and making it a comprehensive solution for data security.
Pros and Cons
Pros:
- Integrates with other security tools for comprehensive protection.
- Helps in achieving compliance with regulatory standards.
- Strong focus on database security.
Cons:
- Depending on the size of the database, system performance may be affected.
- Customization options may be complex for beginners.
- Pricing might be high for small businesses.
Forcepoint Data Loss Prevention is a powerful tool that helps companies protect sensitive data through advanced machine learning capabilities. It is designed to ensure secure business operations while maintaining regulatory compliance, and its machine-learning prowess makes it exceptional in recognizing and preventing potential data breaches.
Why I Picked Forcepoint Data Loss Prevention:
I chose Forcepoint Data Loss Prevention due to its impressive use of advanced machine learning techniques. Comparing it with others in the market, it stands out because of its intelligent algorithms that can understand, recognize, and prevent a vast array of data threats. Users can protect personally identifiable information (PII) and protected health information (PHI), company financials, trade secrets, credit card data, etc., even in images. It will let users follow intellectual property in both structured and unstructured forms. It’s best for advanced machine learning-based protection as its technology goes beyond traditional methods, offering superior protection against data loss.
Standout features and integrations:
Forcepoint DLP's features include incident risk ranking, data discovery, and an advanced policy engine. It integrates effectively with other Forcepoint solutions like Web Security, Email Security, Check Point DLP, and User and Entity Behavior Analytics, creating a holistic approach to data protection.
Pros and Cons
Pros:
- Provides integrations with other Forcepoint solutions.
- Offers a comprehensive suite of features.
- Utilizes advanced machine learning for protection.
Cons:
- Machine learning models may require time for optimal calibration.
- It might be overly complex for smaller businesses.
- Pricing is not transparent and requires direct contact.
Egress Data Loss Prevention offers robust data security solutions that are context-aware, allowing for efficient protection of sensitive data in varying contexts. Its dynamic approach to data loss prevention adjusts to the specific context of your data, thereby enhancing security.
Why I Picked Egress Data Loss Prevention:
I chose Egress Data Loss Prevention due to its dynamic, context-aware approach to data security. This tool stands out as it intelligently adjusts its data protection mechanisms based on the context of your data, unlike many traditional, static DLP tools. It’s the best solution for context-aware data security as it intricately understands the various contexts in which data loss can occur and adjusts its strategies accordingly.
Standout features and integrations:
Egress Data Loss Prevention boasts context-aware data protection, accidental send prevention, and sophisticated machine-learning algorithms for better threat detection. These features work in harmony to provide robust data protection. The software also integrates well with common platforms such as Microsoft 365 and Google Workspace, allowing for a smooth flow of work and data.
Pros and Cons
Pros:
- Utilizes advanced machine learning for threat detection.
- Integrates well with Microsoft 365 and Google Workspace.
- Offers context-aware data security.
Cons:
- The setup might require a learning curve.
- It may be overwhelming for small businesses.
- Advanced features might result in extra costs.
Trellix Data Loss Prevention (formally McAfee Enterprises and FireEye, rebranded as Trellix following the 2021 merger) is a solution that helps organizations protect their sensitive information across all endpoints and network traffic. This tool provides integrated security for endpoints and networks, making it ideal for businesses seeking a comprehensive security solution.
Why I Picked Trellix Data Loss Prevention:
I picked Trellix for its integrated approach to data loss prevention. Many solutions focus primarily on either endpoint security or network security, but Trellix combines both aspects, ensuring comprehensive data protection. I deemed it best for integrated endpoint and network security due to its well-rounded feature set that covers both areas effectively.
Standout features and integrations:
Trellix Data Loss Prevention offers robust features, including real-time visibility into data movement, customizable security policies, and automatic enforcement actions. It integrates with several other security platforms and IT systems, enhancing its ability to protect sensitive data effectively.
Pros and Cons
Pros:
- Easy integration with other security and IT platforms.
- Real-time visibility into data movement.
- Provides both endpoint and network security.
Cons:
- The interface may require help to navigate for beginners.
- Requires time for setup and policy configuration.
- It might be pricey for smaller businesses.
Nightfall DLP is a robust cloud DLP solution that shines in cloud-based environments. Specializing in protecting cloud data platforms, it's perfect for organizations that heavily use cloud services and need a secure, effective way to prevent data loss.
Why I Picked Nightfall DLP:
Among the myriad data loss prevention tools available, Nightfall DLP's unique focus on cloud-based operations caught my attention. I selected it because it is capable of securing critical data within cloud-native environments, which sets it apart from many other data loss prevention tools. Thus, Nightfall DLP is the best tool for cloud-native environments, considering its adeptness at providing protection for data residing in the cloud.
Standout features and integrations:
Nightfall DLP comes with noteworthy features such as machine learning-powered detection, policy automation, and comprehensive compliance controls, which all contribute to its strength in cloud-native security. It provides essential integrations with popular cloud storage platforms and other Software-as-a-Service (SaaS) apps, enhancing its ability to protect data across diverse cloud environments.
Pros and Cons
Pros:
- Extensive cloud platform integrations.
- Machine learning-enhanced detection.
- Excellent cloud-native environment protection.
Cons:
- The user interface may take time to master.
- Some advanced features might come with extra costs.
- It might be over-specialized for non-cloud-native businesses.
Best for USB and peripheral device control
Endpoint Protector DLP Software is a data protection tool that provides robust security measures for USB and peripheral devices. The software ensures data security by monitoring and controlling data transfers through peripheral devices, thereby excelling in preventing data leakage via these channels.
Why I Picked Endpoint Protector DLP Software:
I chose Endpoint Protector DLP Software for its superior USB and peripheral device control. The tool sets itself apart with its focused approach to data transfers through peripheral devices, a feature many other market tools do not offer. I believe it is "best for" organizations that handle sensitive data regularly transferred through peripheral devices.
Standout features and integrations:
Endpoint Protector DLP Software has features like content discovery, device control, and content-aware protection. Moreover, the tool can integrate with existing IT environments, supporting Windows, Linux, and Mac to streamline data protection processes.
Pros and Cons
Pros:
- Compatible with Windows, Linux, and Mac.
- Content-aware protection enhances data security.
- Excellent control over USB and peripheral devices.
Cons:
- It could be complex to configure for first-time users.
- Additional costs for more advanced features.
- Higher starting price compared to some competitors.
Other Data Loss Prevention Software
Below is a list of additional data loss prevention software that I shortlisted but did not make it to the top 10. Definitely worth checking them out.
- Safetica ONE
For data leak prevention via behavioral analysis
- 2B Advice PrIME
For privacy and compliance management
- GTT DLP
For comprehensive data visibility
- LastPass
Good for password management in businesses of all sizes
- NordLayer
Good for advanced network security with threat prevention
- Varonis Data Security Platform
Good for extensive data security and threat detection
- Spirion
Good for businesses needing precise personal data discovery and protection
- Tessian
Good for preventing data loss through emails and human interactions
- Cove
Good for reliable data backup and recovery solutions
- GTB Data Loss Prevention
Good for comprehensive data loss protection across various platforms
- Clearswift Data Loss Prevention
Good for adaptable and dynamic data loss prevention
- Digital Guardian DLP
Good for businesses requiring context-aware data loss prevention
- Teramind DLP
Good for user-focused data loss prevention and user behavior analytics
- Fidelis Network
Good for organizations looking for network traffic analysis and data leakage prevention
- Laminar
Good for businesses seeking automated threat detection and response
- Cyberhaven
Good for organizations needing behavioral data loss prevention
Related Reviews
Data Loss Prevention Software Selection Criteria
When selecting the best data loss prevention software to include in this list, I considered common buyer needs and pain points like data security and compliance with regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Protect sensitive data
- Monitor data access
- Control data transfer
- Enforce compliance policies
- Detect data breaches
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat detection
- Advanced analytics
- Customizable alerts
- Integration with cloud services
- Machine learning capabilities
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Easy navigation
- Customizable dashboards
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive documentation
- Templates for quick setup
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple contact channels
- Response time
- Knowledgeable staff
- Access to a community forum
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Feature set relative to cost
- Discounts for longer commitments
- Cost of add-ons
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction scores
- Frequency of updates
- Ease of implementation
- Support responsiveness
- User feedback on features
How to Choose Data Loss Prevention Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your business? Consider user limits, data capacity, and how easy it is to upgrade or expand features as your needs evolve. |
| Integrations | Does it work with your existing tools? Check compatibility with your current systems and any future tech you plan to implement. |
| Customizability | Can you tailor it to your processes? Look for options to adjust settings, workflows, and reports to fit your team's specific needs. |
| Ease of use | Is the interface user-friendly? Ensure your team can navigate the software without extensive training. Test for intuitive design and functionality. |
| Implementation and onboarding | How quick is setup? Assess the time and resources needed to get started, including training materials and support during the initial phase. |
| Cost | Does it fit your budget? Compare pricing models, such as subscription vs. one-time fees, and consider any hidden costs like add-ons or updates. |
| Security safeguards | How does it protect your data? Evaluate encryption standards, data backup options, and access controls to ensure robust security measures. |
| Compliance requirements | Does it meet industry standards? Verify if the software complies with regulations relevant to your sector, like GDPR or HIPAA. |
What Is Data Loss Prevention Software?
Data loss prevention software is a tool designed to protect sensitive data from being lost, stolen, or accessed by unauthorized users. IT professionals, compliance officers, and data security teams generally use these tools to safeguard information and ensure regulatory compliance.
Monitoring, data encryption, and access control features help with preventing data breaches and maintaining data integrity. When incidents do occur, digital forensics software can help investigate and analyze the breach. Overall, these tools provide peace of mind by securing valuable information and supporting compliance efforts.
Features
When selecting data loss prevention software, keep an eye out for the following key features:
- Data monitoring: Tracks data movement and access to identify unusual activities and prevent unauthorized access.
- Encryption: Protects sensitive information by converting it into unreadable code, ensuring data security even if accessed.
- Access control: Limits who can view or edit data, reducing the risk of internal and external breaches.
- Compliance management: Helps ensure adherence to industry regulations like GDPR or HIPAA, avoiding costly fines and penalties.
- Real-time alerts: Notifies users immediately of potential data breaches or policy violations, allowing for quick response.
- Integration capabilities: Works seamlessly with existing systems and software, enhancing overall security infrastructure.
- Data classification: Categorizes data based on sensitivity, helping prioritize protection efforts effectively.
- Customizable policies: Allows tailoring of security measures to fit specific organizational needs and workflows.
- Audit trails: Provides detailed logs of data access and changes, aiding in forensic analysis and accountability.
- User training support: Offers resources and tools to educate employees on data protection practices, reducing human error.
Benefits
Implementing data loss prevention software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Protects sensitive information with encryption and access controls, reducing the risk of data breaches.
- Regulatory compliance: Helps your organization meet industry standards like GDPR or HIPAA, avoiding costly fines and penalties.
- Real-time response: Sends instant alerts for suspicious activities, allowing your team to act quickly and mitigate potential threats.
- Data visibility: Provides insights into data movement and access, helping you monitor and manage information effectively.
- Cost savings: Prevents data breaches and associated costs by maintaining data integrity and protecting against unauthorized access.
- Tailored protection: Offers customizable policies to fit your specific business needs, ensuring targeted and efficient data security measures.
- User accountability: Tracks data access and changes with audit trails, fostering a culture of responsibility and transparency within your team.
Costs & Pricing
Selecting data loss prevention software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in data loss prevention software solutions:
Plan Comparison Table for Data Loss Prevention Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited data protection, and basic reporting. |
| Personal Plan | $5-$25/user/month | Enhanced encryption, access controls, and standard compliance tools. |
| Business Plan | $30-$75/user/month | Advanced analytics, customizable policies, and integration capabilities. |
| Enterprise Plan | $100-$200/user/month | Real-time alerts, comprehensive audit trails, and dedicated support. |
Most Asked Questions Regarding Data Loss Prevention Software (FAQs)
How do DLP policies work?
DLP policies define rules and actions to protect data from unauthorized access or leaks. They monitor data activity, detect violations, and apply corrective measures like blocking or alerting. These policies are essential for maintaining data security and preventing breaches.
What are the four types of DLP?
The four main types of DLP are network, endpoint, cloud, and application. Network DLP monitors data in transit, endpoint DLP secures data on devices, cloud DLP protects cloud-stored data, and application DLP focuses on securing data within specific applications.
How do you implement DLP software?
Implementing DLP software involves assessing your data protection needs, selecting a suitable solution, and configuring policies to address vulnerabilities. Train your team on usage and monitor the system regularly to ensure it effectively protects sensitive information.
What are DLP guidelines?
DLP guidelines help you identify, monitor, and protect sensitive data at rest, in motion, and in use. They dictate how data is handled across various locations and transmission methods. Implementing these guidelines ensures that sensitive information remains secure and compliant with regulations.
What’s Next:
If you're in the process of researching data loss prevention software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.