Best SIEM Tools Shortlist
Here’s my shortlist of the best SIEM tools:
Finding the right Security Information and Event Management (SIEM) tools can be the difference between catching threats in minutes or missing them entirely.
With nearly a decade in cybersecurity and infrastructure monitoring, I’ve evaluated dozens of SIEM platforms across enterprise, SaaS, and hybrid environments. The best ones don’t just centralize logs—they correlate events, automate incident detection, and help security teams respond faster under pressure.
In this guide, I’ll share the SIEM tools that have consistently proven reliable, scalable, and integration-ready in real-world security operations. Each recommendation is based on firsthand experience using these platforms to strengthen visibility, compliance, and response time across growing engineering teams.
Why Trust Our Software Reviews?
We’ve been testing and reviewing software since 2023. As IT and data specialists ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different IT use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our review methodology.
Best SIEM Tools Summary
This comparison chart summarizes pricing details for my top SIEM tool selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for threat intelligence | Free demo available | Pricing upon request | Website | |
| 2 | Best for small and mid-sized businesses | Free demo available | From $0.09/GB/month | Website | |
| 3 | Best for continuous monitoring and rapid response | Free trial + free demo available | Pricing upon request | Website | |
| 4 | Best enterprise-focused SIEM | 30-day free trial | From $2,877/year | Website | |
| 5 | Best for advanced threat detection | Free demo available | Pricing upon request | Website | |
| 6 | Best for multi-cloud enterprises | 31-day free trial | From $2.46/GB (pay-as-you-go) | Website | |
| 7 | Best for a range of integrations | 14-day free trial | From $95/month | Website | |
| 8 | Best for SIEM visualizations | 14-day free trial | From $15/host/month | Website | |
| 9 | Best for real-time threat detection | Free demo available. | Pricing varies by licensing model, deployment type, and feature set. | Website | |
| 10 | Best for rapid threat response | Not available | Starts at $1,075 per month | Website | |
| 11 | Best for workflow automation | Not available | Pricing upon request | Website | |
| 12 | Best endpoint protection | 30-day free trial | From $3.82/asset/month | Website | |
| 13 | Best for risk-based alerting | 14-day free trial | Pricing upon request | Website | |
| 14 | Best for file integrity monitoring | 30-day free trial available | From $29/user/month (billed annually) | Website | |
| 15 | Best for IT solution providers | Free trial upon request | Pricing upon request | Website | |
| 16 | Best for scaling log management | Free trial upon request | Pricing upon request | Website | |
| 17 | Best for real-time log management | Not available | From $10/user/month (billed annually) | Website | |
| 18 | Best for on-premise deployments | Free demo available | Pricing upon request | Website | |
| 19 | Best for advanced threat detection | Free demo available | Contact vendor for pricing | Website | |
| 20 | Best for centralized data ingestion | Free trial available | From $70/month | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best SIEM Software Reviews
Below are my detailed summaries of the best SIEM software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
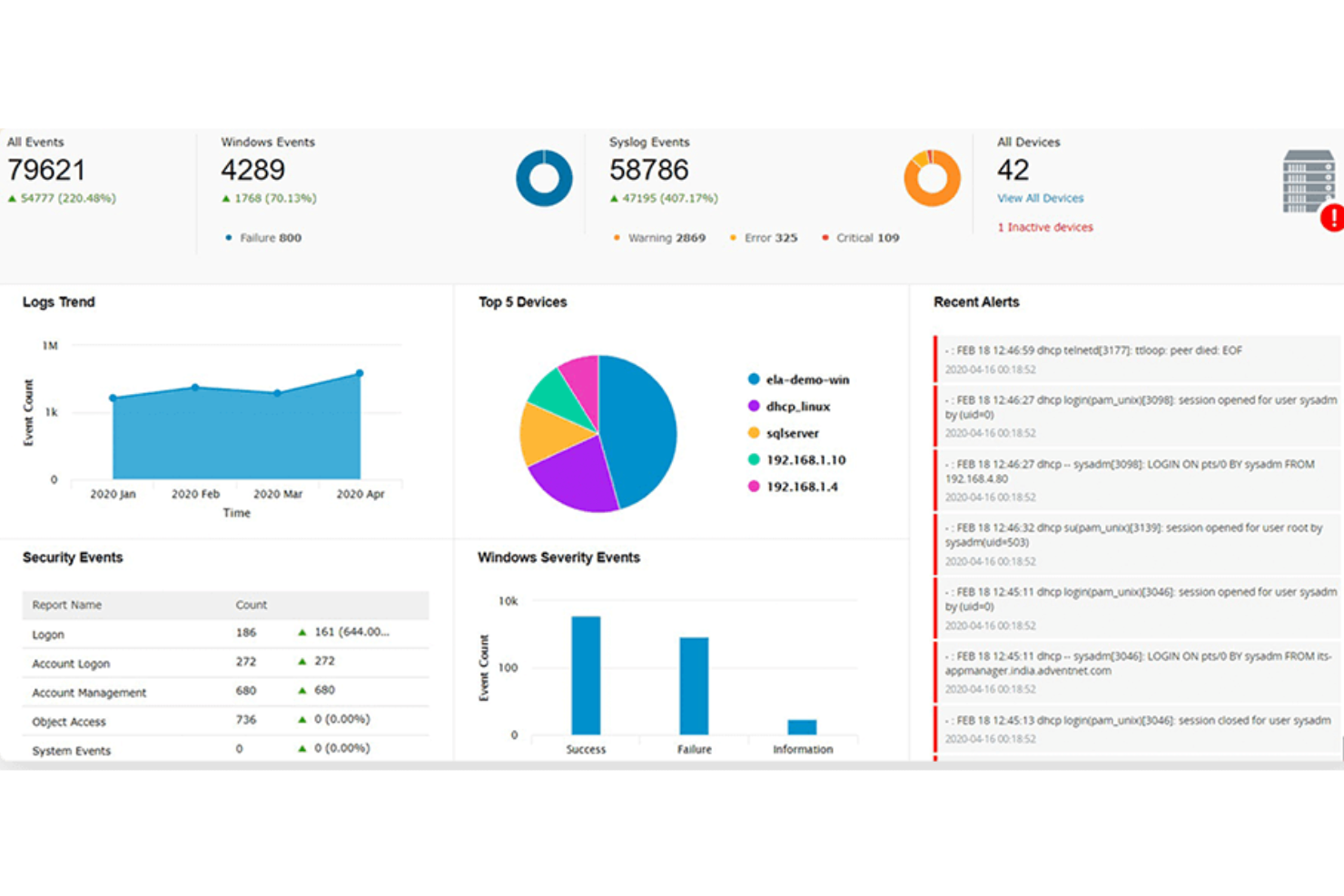
ManageEngine Log360 is a security information and event management (SIEM) solution designed to help organizations monitor and manage their IT infrastructure.
Why I picked ManageEngine Log360: I picked ManageEngine Log360 because of its comprehensive approach to security management. It integrates various functionalities like threat intelligence, machine learning-based anomaly detection, and rule-based attack detection to provide a robust security framework. The software's ability to offer real-time insights and analytics across on-premises, cloud, and hybrid environments ensures a thorough and dynamic approach to threat detection and response.
ManageEngine Log360 Standout Features and Integrations:
Features include its User and Entity Behavior Analytics (UEBA). This feature uses advanced machine learning algorithms to establish baselines of normal activity and then detect deviations that may indicate potential threats. Another notable feature is its automated threat response, which can reduce the time between threat detection and mitigation by automating the response process.
Integrations include Microsoft Active Directory, Office 365, Google Workspace, AWS, Azure, Salesforce, Box, ServiceNow, Jira, Slack, IBM QRadar, Splunk, SolarWinds, Palo Alto Networks, Fortinet, Cisco, and Sophos.
Pros and Cons
Pros:
- Threat intelligence features
- Real-time alerts
- Centralized management of logs and security events
Cons:
- Requires regular maintenance and updates
- Deployment can be complex
Logmanager gives small and mid-sized businesses a SIEM that’s easy to deploy and maintain without hiring a dedicated security engineer. It helps your team detect threats faster by unifying logs from across your environment and providing clear context for investigating incidents.
Why I Picked Logmanager
I picked Logmanager because it lets you manage SIEM capabilities without juggling complex setup steps, thanks to its out-of-the-box parsers, alerts, and dashboards. You can gain visibility across your entire infrastructure by centralizing logs from over 140 supported sources, helping you detect suspicious events with reliable context. Its no-code automation tools let your team adapt rules, alerts, and workflows without scripting. I also like that it supports compliance initiatives by giving you quick access to historical logs and audit-ready reporting.
Logmanager Key Features
These features reinforce Logmanager’s value for teams that need scalable log analysis without enterprise overhead:
- Predefined Dashboards: Surface system performance, security events, and compliance status at a glance.
- Compliance Reporting: Generates audit-ready insights aligned with standards like GDPR, ISO 27001, and NIS2.
- High-Speed Search: Enables rapid filtering and log retrieval during investigations.
- Custom Alerting: Lets teams define conditions that trigger notifications for high-risk activity.
Logmanager Integrations
Integrations include Apache Tomcat, Aruba Networks, CheckPoint Firewall, Cisco devices, Dell iDRAC, ESET Remote Administrator, Fortinet products, IBM AIX Syslog, Microsoft products, and MySQL.
Pros and Cons
Pros:
- Scales with growing log volume across hybrid environments
- Fast search improves incident investigation times
- Customizable dashboards give full infrastructure visibility
Cons:
- Pricing may be high for very small teams
- Some customization workflows require deeper SIEM familiarity
In a world where cyber threats evolve daily, Heimdal stands out as a versatile solution for those seeking a Security Information and Event Management (SIEM) tool. Tailored for industries like healthcare, government, and critical infrastructure, it addresses compliance and data governance challenges. With features like threat hunting and endpoint security, Heimdal helps your organization stay ahead of potential security breaches, ensuring peace of mind for IT professionals and business leaders alike.
Why I Picked Heimdal
I picked Heimdal because of its unique combination of Managed Extended Detection and Response (MXDR) and 24/7 Security Operations Center (SOC) support. These features are crucial for businesses needing continuous monitoring and rapid incident response. Heimdal's ability to integrate with third-party applications enhances its flexibility, and its focus on compliance with standards like ISO 27001 and HIPAA ensures that your organization meets industry regulations. The platform's comprehensive threat detection capabilities address the critical need for proactive security measures, making it a solid choice for any organization.
Heimdal Key Features
In addition to its robust MXDR and SOC capabilities, I also found Heimdal offers several other valuable features:
- Threat Hunting: This feature allows you to actively search for potential threats within your network, providing an additional layer of security.
- Vulnerability Management: Heimdal helps identify and address vulnerabilities within your systems to prevent potential breaches.
- Endpoint Security: It provides advanced protection for endpoint devices, ensuring that all access points are secure.
- Email Security: This feature protects against email-based threats, including phishing and fraud attempts, safeguarding your organization's communication channels.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
SolarWinds Security Event Manager is a SIEM platform that aggregates, analyzes, and reports log data in one location. Advanced threat detection capabilities help organizations detect and respond to security incidents in real-time.
Why I picked SolarWinds Security Event Manager: I selected SolarWinds Security Event Manager because it offers an extensive list of pre-built connectors. This gives enterprises a more comprehensive view of their environment. Intuitive visualizations like charts and graphs make it easy to identify and respond to security issues.
SolarWinds Security Event Manager Standout Features and Integrations:
Features that I found particularly impressive about SolarWinds Security Event Manager are its Active Response tool, which lets you automate actions to respond to certain activities. For example, you can create a rule that automatically logs users off if they try to send sensitive data to public clouds. The platform also offers out-of-the-box support for security mandates like GDPR, HIPAA, and PCI DSS.
Integrations include hundreds of pre-built connectors for anti-virus software, firewalls, physical infrastructure devices, network services, and more. Notable connectors include Microsoft Security Security Essentials, Cisco Firesight, Sentinel IPS, and Dell Server Administrator.
Pros and Cons
Pros:
- Offers compliance management and reporting
- List of pre-built connectors is continuously updated
- Supports multiple network protocols
Cons:
- Implementation may require specialized expertise
- Plans can get costly depending on the number of licenses you need
IBM Security QRadar SIEM is a scalable SIEM platform that collects security-related data from endpoint devices and applications across a network. It enables security teams to monitor their IT infrastructure from one location.
Why I picked IBM Security QRadar: I chose IBM Security QRadar SIEM for its advanced threat detection capabilities. It uses AI with network and user behavior analytics to detect security threats in near real-time. I also liked that the platform assigned each offense a magnitude score based on severity, which made it easier for me to prioritize the most critical issues.
IBM Security QRadar SIEM Standout Features and Integrations:
Features that differentiate IBM Security QRadar SIEM, in my opinion, include its native integrations with over 700 security products, which offers extensive network visibility. Another feature that stood out to me is the platform’s security operations center (SOC). I could easily drill down into each threat and get more details about each.
Integrations are available natively with over 370 applications and 450 device support modules (DSM) like Amazon AWS Network Firewall, Cisco ACE Firewall, and Google Cloud Audit Logs. You can also use IBM’s Universal Cloud REST API to create custom integrations.
Pros and Cons
Pros:
- Offers on-premise and cloud deployments
- Complies with security and privacy frameworks like ISO 27001
- Supports a broad range of event log sources
Cons:
- Performance may slow down when working with large data sets
- Large-scale deployments can be difficult to implement
Microsoft Azure Sentinel is a cloud-based SIEM solution that can ingest data from a range of sources and detect threats before they escalate. It’s built on the Azure platform, which provides flexibility and scalability.
Why I picked Microsoft Azure Sentinel: What makes Microsoft Azure Sentinel an impressive SIEM tool, in my opinion, is its ability to collect and analyze data at cloud scale — something important to consider, especially if your company uses multiple cloud providers. I also like that it integrates natively with the Azure cloud computing platform, as this means it can automatically scale to fit all security needs.
Microsoft Azure Sentinel Standout Features and Integrations:
Features that I feel distinguish Microsoft Azure Sentinel include its advanced security analytics, which uses AI to detect threats and reduce the number of false positives. This makes it easier to prioritize incidents that pose legitimate threats. The platform also offers a workflow management system with pre-defined rules to automate security tasks at scale.
Integrations include over 130 pre-built data connectors to sources like AWS, Citrix, Elastic, Ivanti, and Juniper. You can also use the platform’s REST APIs to integrate with other data connectors.
Pros and Cons
Pros:
- Can automatically scale to fit your security needs
- Offers flexible pay-as-you-go pricing
- Integrates with other Microsoft security products
Cons:
- Requires a significant investment upfront to implement the solution
- Not suitable for smaller businesses
Elastic Security gives you a holistic view of your data no matter where it resides. It provides centralized log management and rapid response capabilities to boost network security.
Why I picked Elastic Security: I put Elastic Security on this list because of its impressive scope of native integrations. It can ingest metrics, logs, and events from a range of data sources, allowing you to get a more complete view of your security posture. One-click integrations made it easy for me to add new sources and expand SIEM visibility.
Elastic Security Standout Features and Integrations:
Features that I feel are worth mentioning about Elastic Security include its interactive tools that help you conduct a root cause analysis of an incident and implement new rules to prevent future instances. You can also use rules that Elastic threat researchers and community members created to enhance threat detection.
Integrations are available natively with applications, databases, network devices, and workplace tools. Notable integrations include AWS, Apache Spark, Microsoft Azure, Cisco Umbrella, and Jira. You can also use the platform’s REST APIs to connect to more sources.
Pros and Cons
Pros:
- Offers flexible pricing options
- One-click integrations make it easy to add new data sources
- Ability to ingest and analyze data at cloud scale
Cons:
- May not be suitable for organizations with complex security needs
- Not as robust as other SIEM solutions on the market
Datadog Cloud SIEM is a cloud-native SIEM solution that analyzes operational and security logs across your technology stack, giving operational teams a high-level view of the company’s security posture.
Why I picked Datadog Cloud SIEM: During my testing, I was impressed by the visualizations that the platform offered. The interface made it easy to visualize activities across users and services. This level of visibility greatly improved collaboration, as my team and I could drill down into incidents and get to the root cause of security threats.
Datadog Cloud SIEM Standout Features and Integrations:
Features that make Datadog Cloud SIEM stand out to me include its out-of-the-box threat detection rules that enable companies to improve their network security without spending huge amounts of time configuring them. For companies with specific requirements, Data Cloud SIEM includes a code-free editor that lets you create your own rules.
Integrations are available natively with over 600 applications, identity providers, and endpoints. Notable integrations include AWS, Azure DevOps, Redis, and Jira.
Pros and Cons
Pros:
- Data intake is fast and reliable
- Offers advanced search filters to narrow down your search
- Cloud-native solution allows for greater scalability
Cons:
- Log parsing could be improved
- Free plan has limited functionality
Introduction
Fortinet FortiSIEM is a sophisticated Security Information and Event Management (SIEM) tool designed to elevate your security operations. It offers a comprehensive suite of features that help you detect threats in real time and automate incident responses, ensuring your network remains secure and compliant.
Why I Picked
I chose Fortinet FortiSIEM for its exceptional capability in real-time threat detection. This feature allows you to identify potential security threats as they occur, providing you with the opportunity to respond promptly and minimize risk. Additionally, FortiSIEM's advanced analytics offer deep security insights, enabling your team to understand and mitigate vulnerabilities more effectively.
Another reason FortiSIEM stands out is its automated incident response. This functionality streamlines the process of handling security incidents, reducing the burden on your team and allowing them to focus on more strategic tasks. With FortiSIEM, you can ensure that incidents are managed quickly and efficiently, minimizing downtime and potential damage.
Standout Features
Features include a configuration management database (CMDB) that offers comprehensive asset monitoring, ensuring you have visibility over your entire network. The tool supports over 2800 correlation rules that help in identifying patterns indicative of potential threats. Additionally, FortiSIEM provides built-in SOAR automation, which simplifies security operations by automating routine tasks, allowing your team to concentrate on more critical issues.
Integrations
Integrations include AWS, Microsoft Azure, Google Cloud, Oracle Cloud, Cisco, ServiceNow, Salesforce, Jira, Bitdefender, Citrix, Claroty, and Acronis.
Introduction
AlienVault USM is a unified security management platform designed to bring together multiple security capabilities — asset discovery, vulnerability assessment, intrusion detection, behavioral monitoring and SIEM (security information and event management) — into a single console. AT&T Cybersecurity
Available as both on-premises (USM Appliance) and cloud/ hybrid (USM Anywhere) deployments, it aims to enable organizations of varying sizes to detect threats, respond to incidents and support compliance from day one.
Why I Picked It
I selected AlienVault USM because it stands out in the crowded security-management tool market by offering a true “all-in-one” foundation: many organizations struggle with multiple point solutions (one for SIEM, one for IDS, one for vulnerability scanning, etc.), and USM consolidates those into a unified platform.
The fact that it integrates built-in threat intelligence (via AT&T/Alien Labs) and supports both on-premises and cloud environments gives it flexibility and real-world practicality for today’s hybrid IT world.
Standout Features
- Asset discovery & inventory: It automatically detects devices, servers, cloud assets, etc., helping organizations build a complete inventory of what needs protection.
- Vulnerability assessment: Continuous scanning of assets to identify patches missing, misconfigurations and other exposures.
- Intrusion detection + behavioral monitoring: Network IDS, host IDS, and behavioural analytics (UEBA-style) help detect anomalous user or entity activity.
- SIEM & event correlation: Log collection, normalization and correlation across devices and environments to provide actionable alerts and reports.
- Integrated threat intelligence: The platform taps into AT&T Alien Labs and the open threat exchange (OTX) to feed real-time threat data, which improves detection and prioritization.
- Deployment flexibility: Options to deploy as an appliance, virtual sensor, or cloud service, enabling on-prem, hybrid, or full-cloud use.
Integrations
AlienVault USM supports extensive integrations via its “AlienApps” / “BlueApps” architecture and plugin library. These integrations allow you to leverage existing security tools and infrastructure rather than rebuild everything.
For example, it can integrate with cloud platforms (AWS, Azure), identity systems (SSO/SAML), endpoint/security tools, and ticketing/ITSM systems. It also supports generic webhook ingestion for custom event feeds.
The broad plugin list (covering hundreds of vendors/devices) means your log sources, firewalls, endpoints, cloud services, etc., can feed into USM for unified visibility.
Pros and Cons
Pros:
- Positive feedback on performance and reliability.
- Regular updates that improve functionality and security.
- Effective threat detection and response capabilities.
Cons:
- Limited customization options for advanced users.
- Occasional issues with system performance and speed.
ArcSight Enterprise Security Manager delivers real-time threat detection and analytics. It helps organizations reduce their threat exposure and comply with regulatory requirements.
Why I picked ArcSight Enterprise Security Manager: What I liked about ArcSight Enterprise Security Manager is its powerful workflow automation features. Once it detects a threat, it classifies and automatically assigns a case to an analyst. You can manually set up these workflows or “playbooks” based on your needs.
ArcSight Enterprise Security Manager Standout Features and Integrations:
Features that make ArcSight Enterprise Security Manager stand out are its event correlation engine which can track thousands of events per second and send alerts if it detects suspicious activity. I found customizing these rule sets to fit a range of SIEM use cases straightforward.
Integrations are available natively with ArcSight Intelligence to enhance threat detection and ArcSight Recon to improve log management. ArcSight Enterprise Security Manager also integrates natively with SOC tools like Qualys, AhnLab, and Satrix.
Pros and Cons
Pros:
- Dashboards and reports are highly customizable
- Intelligent risk scoring helps you prioritize security threats
- Real-time correlation engine helps to identify threats accurately
Cons:
- No pricing information is available
- Laggy response times when querying the database
Rapid7 InsightIDR is a cloud-based platform that combines SIEM and extended detection and response (XDR) capabilities to enhance threat detection and reduce response times.
Why I picked Rapid7 InsightIDR: I chose Rapid7 InsightIDR because it offers extensive endpoint protection for devices connected to a network. Enhanced Endpoint Telemetry (EET) provides detailed activity logs on all endpoint devices. It gives context surrounding each incident so that security teams can respond faster.
Rapid7 InsightIDR Standout Features and Integrations:
Features that I feel make Rapid7 InsightIDR a SIEM tool worth considering include its intrusion detection system that can quickly recognize suspicious activities. It provides traffic metadata, giving you a clear picture of what’s happening on the network. Another feature worth mentioning is the pre-built workflows that allow you to automate responses to common threats.
Integrations are available natively with various cloud services, DevOps platforms, and firewalls. Notable partners include Atlassian, AWS, Cisco, ServiceNow, and Snyk.
Pros and Cons
Pros:
- Specialized training available from Rapid7
- Includes relevant context around each alert
- Straightforward installation process
Cons:
- Limited ticket system integrations
- Steep initial learning curve
Splunk Enterprise Security is a modern SIEM solution that helps companies gain a unified view of their security posture, with advanced threat detection, risk-based alerts, and flexible deployment options. Fergal Glynn, CMO and AI Security Advocate of Mindgard, shared: “My most favorite Splunk feature is Risk-Based Alerting. It only fires when a real threat surpasses set thresholds. It helps me cut through noise and simply shows me the alerts that truly matter.”
Why I picked Splunk Enterprise Security: Splunk Enterprise Security offers all the features you’d expect from a SIEM tool — threat detection, security analytics, rapid response, etc. But what makes Splunk stand out is its risk-based alerting, which triggers alerts when incidents cross certain thresholds. This helps cut down on “alert fatigue” and false positives, so your team can prioritize risks that pose real threats.
Splunk Enterprise Security Standout Features and Integrations:
Features that I feel are worth highlighting here include its out-of-the-box detections for over 1,300 threats, which include detailed descriptions and techniques to address them. Splunk Enterprise Security also includes automated playbooks that provide rapid responses and resolutions to common security threats.
Integrations are available natively with over 1,000 platforms. Notable integrations include AWS, Google Cloud Platform, Kubernetes, OpenShift, and MongoDB.
Pros and Cons
Pros:
- Provides an extensive range of integrations
- Offers a built-in risk analysis dashboard
- Capable of ingesting terabytes of data per day
Cons:
- Configuring alerts is a time-consuming process
- High licensing costs may be too expensive for small businesses
ManageEngine EventLog Analyzer is a SIEM solution with a real-time log correlation engine that alerts you to suspicious activities in your network. Steve Morris, Founder and CEO at NEWMEDIA.COM, noted, “Compliance reporting went from monthly soup to dashboards. Audits are now a drop-down export instead of a forensic report.”
Why I picked ManageEngine EventLog Analyzer: ManageEngine EventLog Analyzer offers impressive log management features in a single console. But the main reason I put this platform here is that it offers a file integrity monitoring (FIM) module that detects unauthorized modifications to sensitive files and system folders. It provides audit trails of any changes made to a file and notifies administrators of incidents that could indicate a breach.
ManageEngine EventLog Analyzer Standout Features and Integrations:
Features that differentiate ManageEngine EventLog Analyzer include its built-in syslog server that collects log data from network devices like servers, routers, and firewalls. The dashboard made it easy for me to drill down and gain insights into any security event.
Integrations include native support for over 750 log sources, such as database platforms, endpoint security solutions, firewalls, routers, and web servers. Notable integrations include AWS Cloud Trail, Microsoft SQL Server, Symantec Endpoint Protection, SonicWall, and Solaris.
Pros and Cons
Pros:
- Available for Windows Server and Linux
- Offers compliance reports for HIPAA, ISO 27011, and more
- Provides advanced log search functionality
Cons:
- Steep initial learning curve
- Free edition has limited functionality
ConnectWise SIEM, formerly Perch, is a SIEM platform that enables IT solution providers to help their clients protect their networks against cybersecurity attacks.
Why I picked ConnectWise SIEM: ConnectWise SIEM deserves a spot on this list, in my opinion, because it’s specifically built for IT service providers. It offers flexible on-premise and cloud deployments and comprehensive risk assessments that help you understand the state of your clients’ IT infrastructure. One thing I liked is that ConnectWise SIEM performs automated network scans and prioritizes potential threats based on their impact.
ConnectWise SIEM Standout Features and Integrations:
Features that make ConnectWise SIEM a good fit for IT solution providers are its service level objectives (SLOs) that you can set for your clients. I think SLOs are a great way to set clear expectations and help clients see the value of a SIEM platform. ConnectWise SIEM also enables you to help companies meet compliance and regulatory requirements.
Integrations are available natively through the ConnectWise Marketplace. Notable partners include Fortinet, Perimeter 81, Orbitera, SonicWall, and Trend Micro.
Pros and Cons
Pros:
- Allows you to create customer-facing reports
- Integrates with other ConnectWise products
- Offers flexible on- and off-premise deployments
Cons:
- Certain integrations may not be available
- Some users report issues with scalability
Exabeam SIEM is a cloud-native SIEM tool that can collect, store, and analyze log data at scale. It uses advanced behavioral analytics to detect threats that other tools may miss.
Why I picked Exabeam SIEM: I picked Exabeam SIEM for its extensive log management capabilities. The platform boasts over 9,000 pre-built log parsers that can turn large volumes of log data into machine-readable text. With the query-builder wizard, security analysts can instantly query log data and refine their search over multiple iterations.
Exabeam SIEM Standout Features and Integrations:
Features that stood out to me about Exabeam SIEM include its intuitive correlation rule builder. Normally, I find it tedious to work with correlation rules as they can result in false positives if they’re not properly set up. But I found it easy to build correlation rules in Exabeam Fusion SIEM that fit my specific use cases.
Integrations include pre-built connectors with over 540 third-party security tools across 292 vendors. Notable data sources include AWS CloudTrail, Google Cloud Platform, Microsoft SQL Server, Tanium Core Platform, and OpenShift.
Pros and Cons
Pros:
- Uses AI and machine learning to detect security threats in real-time
- Provides extensive documentation to learn the platform
- Offers user and entity behavior analytics (UEBA) to identify risky users
Cons:
- Pre-built UEBA rules may generate false positives
- Configuring correlation rules can be time-consuming
Introduction
Graylog is a platform that offers a range of Security Information and Event Management (SIEM) solutions specifically designed to enhance cybersecurity for enterprises. It focuses on data collection, analysis, and visualization, enabling organizations to monitor and respond to security threats.
Why I Picked
I picked Graylog as a good SIEM tool because of its real-time log management capabilities. This feature allows you to monitor security events as they happen, which is crucial for identifying and mitigating potential security incidents promptly. Additionally, Graylog offers contextual risk scoring, which helps reduce false positives, saving you time and resources in managing alerts and focusing on genuine threats.
Another reason to consider Graylog is its automated workflows for incident response. These workflows streamline the process of responding to security threats, enabling your team to act quickly and efficiently. The platform's support for flexible deployment options, whether cloud, on-prem, or hybrid, also ensures that you can integrate it into your existing infrastructure without major disruptions.
Standout Features
Features include intelligent threat detection, which helps in identifying potential threats before they become problematic. The platform also offers adversary campaign intelligence, providing insights into the tactics and strategies used by attackers. Additionally, Graylog's threat coverage analysis allows you to evaluate and strengthen your defenses by understanding the areas that need improvement.
Integrations
Integrations include AWS Kinesis/CloudWatch Input, Palo Alto Networks Input, IPFIX Input, Forwarder, and Script Alert Notification.
Pros and Cons
Pros:
- The flexibility to create customizable dashboards for data visualization is a significant advantage.
- The platform's capability to send real-time alerts for suspicious activities is highly valued.
- Users appreciate Graylog's ability to efficiently manage and analyze large volumes of log data.
Cons:
- On occasion, performance issues are reported, particularly when handling very large datasets.
- The documentation is sometimes found lacking, especially for advanced configurations.
LogRhythm SIEM is a centralized log management platform that helps security teams identify and respond to security threats.
Why I picked LogRhythm SIEM: I put LogRhythm SIEM on this list because it offers a robust on-premise solution, which makes it a great option for companies that are subject to regulatory requirements. It provides a host of modules that help companies in highly regulated industries comply with requirements like HIPAA, GDPR, and FISMA. The modules can detect violations in real-time and create reports for compliance audits.
LogRhythm SIEM Standout Features and Integrations:
Features that impressed me about LogRhythm SIEM are its log management features, which can consolidate log and event data from hundreds of sources. The platform also uses machine learning to identify users in the network who deviate from normal patterns and may pose a security risk.
Integrations are available natively with over 950 log sources and cloud providers like AWS, Fortinet, Qualsys, SentinelOne, and VMWare.
Pros and Cons
Pros:
- Lets you easily customize dashboards
- Offers numerous filtering options
- Provides a user-friendly interface
Cons:
- On-premise deployments can be complex
- Searching for older logs is a difficult process
Introduction
Securonix is a security information and event management (SIEM) tool that helps you detect and respond to security threats. It uses advanced analytics and machine learning to provide comprehensive security monitoring and threat detection capabilities.
Why I Picked
I picked Securonix because of its ability to leverage machine learning for threat detection. It helps your team identify anomalies and potential threats by analyzing user behavior and network activity. This means you can catch threats that traditional signature-based systems might miss, giving you an edge in cybersecurity. Additionally, Securonix aligns alerts with frameworks like MITRE ATT&CK, which helps you understand and respond to threats more effectively.
Another reason Securonix stands out is its focus on monitoring insider threats. By providing detailed insights into user activities, it helps you detect suspicious behavior before it escalates into a full-blown security incident. This focus on insider threat detection ensures that your organization is protected from both external and internal risks.
Standout Features
Features include its cloud-native architecture, which allows for scalability and flexibility, making it easier for your team to manage security across various environments. The continuous threat content delivery keeps your security team informed of the latest threats, ensuring you're always prepared. Additionally, its real-time data access facilitates faster investigations, allowing you to quickly respond to incidents and minimize potential damage.
Integrations
Integrations include Amazon Web Services (AWS), Google Cloud Platform (GCP), Microsoft Azure, Microsoft 365, ThreatQuotient, Palo Alto XSOAR, ServiceNow Security Incident, CrowdStrike Falcon, Okta, IBM QRadar SIEM, Microsoft Exchange, and Snowflake.
Pros and Cons
Pros:
- Strong integration with various data sources: Securonix integrates well with a wide range of data sources, enhancing its utility.
- User-friendly interface: Many users find the interface intuitive and easy to navigate.
- Advanced threat detection capabilities: Users appreciate its ability to detect threats effectively using advanced analytics.
Cons:
- Customization complexity: Some users find the customization options challenging, particularly role-based access controls.
- Performance issues with large data volumes: Some users report performance challenges when handling large volumes of data.
Introduction
Logpoint Converged SIEM is a cybersecurity solution that consolidates different security functions to enhance threat detection and incident response. It provides organizations of all sizes with a comprehensive platform to centralize data and manage risks.
Why I Picked
I picked Logpoint Converged SIEM because it centralizes data ingestion for security and compliance, which improves threat detection and response. This feature is vital for your team as it allows you to have a unified view of security data, making it easier to identify and address potential threats. Additionally, Logpoint's automation capabilities, with over 80 automated playbooks, streamline investigations and responses. This reduces the workload on your security teams, enabling them to focus on more strategic tasks.
Another reason for choosing Logpoint is its case management feature, which facilitates tracking and collaboration on incident investigations. This ensures thorough oversight and helps your team to manage incidents more effectively. The platform also includes Logpoint NDR, which utilizes AI and machine learning to identify advanced threats before they escalate, providing an added layer of security.
Standout Features
Features include centralized data ingestion, which improves security and compliance by offering a unified view of security data. Automation is another key feature, with over 80 playbooks that reduce the workload on security teams by streamlining investigations and responses. Lastly, the case management feature facilitates tracking and collaboration on incident investigations, ensuring thorough oversight and efficient incident management.
Integrations
Integrations include Checkpoint Firewall, Cisco, Cisco Umbrella, CrowdStrike, CiscoAmp, DUO Security, and more.
Pros and Cons
Pros:
- Users value the ease of management with Logpoint, finding it simple and quick to learn compared to competitors.
- Users value the ease of use of Logpoint, finding it simple to learn compared to other SIEM platforms.
- Users find the easy integrations of Logpoint, like UEBA and SAP, seamless and agent-free, enhancing efficiency.
Cons:
- Users find the poor reporting capabilities of Logpoint limiting, lacking essential functions compared to other SIEMs like Splunk.
- Users find the reporting capability inadequate, suggesting improvements for better functionality and user experience.
Other SIEM Software
Here’s a shortlist of a few more SIEM tools that didn’t make it to my top list but are still worth considering:
- RSA NetWitness
For full-packet capture monitoring
- Paessler PRTG
For small to medium-sized organizations
- Trellix Security Operations and Analytics
For unifying security tools
Related Software Reviews
If you still haven't found what you're looking for here, check out these alternative tools that we've tested and evaluated.
- Network Monitoring Software
- Server Monitoring Software
- SD-Wan Solutions
- Infrastructure Monitoring Tools
- Packet Sniffer
- Application Monitoring Tools
SIEM Tool Selection Criteria
When selecting the best SIEM tools to include in this list, I considered common buyer needs and pain points like simplifying threat detection and improving compliance reporting. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Real-time threat detection
- Log management and analysis
- Incident response software
- Compliance reporting
- Alerting and notification
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Advanced behavioral analytics
- Threat intelligence integration
- Automated response actions
- User and entity behavior analytics (UEBA)
- Cloud security tools
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- User-friendly dashboards
- Easy-to-navigate interface
- Simple report generation
- Clear visualizations of security events
- Minimal training required
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Comprehensive training materials
- Step-by-step setup guides
- Availability of onboarding webinars
- Interactive tutorials and demos
- Ease of migrating from previous solutions
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Quick response times
- Multiple support channels (email, chat, phone)
- Availability of 24/7 support
- Dedicated support representatives
- Helpful documentation and knowledge base
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Clear pricing structures
- Flexible licensing models
- Availability of scalable pricing
- Transparent costs without hidden fees
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall recommendations from current users
- Positive feedback on detection accuracy
- User satisfaction with ease of use
- Reliability and stability of the tool
- Experiences with customer support
How to Choose SIEM Tools
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Check if the tool can handle increasing data volumes and additional devices smoothly as your organization grows. Look for cloud or hybrid deployments for easier scaling. |
| Integrations | Make sure the SIEM integrates with your existing systems, including endpoints, firewalls, and cloud services, for unified monitoring and faster incident detection. |
| Customizability | Verify if the software lets you tailor alerts, dashboards, and reports according to your security requirements, avoiding unnecessary noise and improving efficiency. |
| Ease of Use | Choose a tool with intuitive interfaces, clear dashboards, and simple workflows so your team can quickly respond to security incidents without extensive training. |
| Budget | Consider pricing models carefully—whether per event, per device, or a flat fee—and select one that aligns best with your budget and expected data growth. |
| Security Safeguards | Confirm the tool provides robust security measures, including data encryption, role-based access, and compliance with regulatory standards like GDPR or HIPAA. |
| Threat Intelligence | Look for built-in threat intelligence or integration options, enabling you to proactively detect and respond to emerging threats faster. |
| Support Quality | Ensure reliable customer support is available, ideally 24/7, to help your team promptly resolve any issues or incidents that arise. |
What Are SIEM Tools?
A SIEM tool is a software platform that collects, analyzes, and correlates security data from across your IT ecosystem to identify potential threats and compliance risks.
By aggregating logs and events from servers, applications, firewalls, and endpoints, SIEM tools provide a centralized view of security activity. They enable real-time monitoring, incident detection, and response automation—helping teams strengthen threat detection capabilities while simplifying regulatory reporting and audit readiness.
Features like log management software, real-time monitoring, and compliance reporting help organizations secure their IT infrastructure and mitigate cyberattacks.
Features of SIEM Tools
When selecting SIEM tools, keep an eye out for these key features:
- Log management: Collects, stores, and organizes log data from a range of devices and applications so you can easily find patterns, spot issues, and stay compliant with regulations.
- Real-time monitoring: Constantly watches network activity and system events to help you catch unauthorized access or potential threats as they happen.
- Threat detection: Uses correlation rules and analytics to automatically flag suspicious behavior or anomalies, letting you stay a step ahead of cyber attackers.
- Incident response: Streamlines how you investigate alerts, assign tasks, and document your actions so you can respond quickly and efficiently during a security incident.
- Alerting and notification: Instantly notifies you when high-risk activities or policy violations occur, so you’re never left in the dark about urgent issues.
- Compliance reporting: Generates ready-made and customizable reports to demonstrate your organization meets industry standards and regulatory requirements.
- Data visualization: Turns technical data into easy-to-read charts and dashboards, helping you and your team spot patterns and trends without getting lost in the weeds.
- Integration capabilities: Connects easily with other security solutions and IT infrastructure, so you can build a security ecosystem that supports your organization’s unique needs.
- User and entity behavior analytics: Tracks user actions and device behaviors to reveal unusual activities, helping you catch insider threats or compromised accounts.
- Forensic analysis: Allows you to go back in time by reviewing historical data, so you can dig deep into past security events and improve your future defenses.
Common SIEM Tools AI Features
Beyond the standard SIEM tools features listed above, many of these solutions are incorporating AI with features like:
- Automated threat intelligence: Leverages AI to gather, process, and integrate external threat data, giving you real-time context about evolving cyber threats.
- Anomaly detection: Learns your organization’s normal activity patterns using AI, then flags deviations that might indicate stealthy attacks or new vulnerabilities.
- Predictive analytics: Uses AI models to forecast potential security risks based on trends in your network, so you can proactively prepare for incidents before they happen.
- Automated incident triage: Employs AI to prioritize, investigate, and even resolve certain alerts, helping you manage alert overload and focus on critical issues.
- Natural language processing (NLP): Allows the SIEM tool to interpret and correlate log messages and security data, even from unstructured sources, using AI-driven language models.
Benefits of SIEM Tools
Implementing SIEM tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Faster response: Real-time alerts help your team quickly address security incidents before they escalate.
- Simpler compliance: Built-in reporting makes it easy to meet regulatory requirements like GDPR or HIPAA.
- Better visibility: Centralized log management gives your security team clear insights into network activity.
- Reduced threat risk: User behavior analytics identify suspicious activities early, lowering your risk of breaches.
- Improved productivity: Automation of routine tasks frees your security team to focus on more critical issues.
- Enhanced decision-making: Visual dashboards clearly show security trends, enabling smarter decisions.
- Lower security costs: Early detection and response reduce the financial impact of security incidents.
Costs and Pricing of SIEM Tools
Selecting SIEM tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in SIEM tools solutions:
Plan Comparison Table for SIEM Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic log collection, limited monitoring, and simple alerts. |
| Personal Plan | $50-$100/user/month | Real-time threat detection, basic compliance reporting, and email notifications. |
| Business Plan | $100-$500/user/month | Advanced analytics, user behavior monitoring, customizable dashboards, and detailed compliance reporting. |
| Enterprise Plan | $500-$1500+/user/month | AI-driven analytics, incident automation, advanced threat intelligence, dedicated support, and comprehensive integrations. |
SIEM Tool FAQs
Here are some answers to common questions about SIEM Tools:
What are the three main roles of a SIEM tool?
How do SIEM tools detect threats?
What should I look for when evaluating SIEM integrations with existing tech stacks?
How can a SIEM system help reduce alert fatigue in my security team?
What are common mistakes to avoid during SIEM deployment?
How do I measure the ROI of a SIEM tool?
Can SIEM platforms help with compliance audits and reporting?
Final Thoughts
Cyberattacks on corporate networks increased by 38% in 2022 compared to 2021, a figure that will likely continue to rise as hackers exploit vulnerabilities for personal gain. SIEM tools are powerful solutions that can detect and even stop potential security threats in their tracks. If your company has yet to implement a SIEM solution, use this list to kickstart your research.
Subscribe to The CTO Club newsletter for more insights.