IBM QRadar Review 2026: Key Features, Pros, Cons, and Pricing
IBM QRadar is a SIEM tool that helps IT teams detect, investigate, and respond to security threats across complex environments. It provides advanced analytics, automated threat intelligence, and flexible deployment options for specialists managing large-scale infrastructure.
In this review, you’ll find a detailed look at QRadar’s features, best and worst use cases, pros and cons, and current pricing to help you decide if it fits your security strategy.
IBM Security QRadar SIEM Evaluation Summary
- Pricing upon request
- Free demo available
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
IBM Security QRadar SIEM Overview
When judging IBM QRadar as a SIEM Tool, its advanced analytics, broad integration options, and strong threat detection set it apart for organizations with complex security needs. The interface can feel dated, and onboarding may require more time than some competitors, but its depth of functionality and responsive support make it a top choice for enterprises prioritizing thorough investigation and compliance.
Pricing is on the higher end, yet justified for those needing scalable, customizable deployments. If you’re selecting a SIEM for a large, regulated environment, QRadar’s capabilities often outweigh its steeper learning curve.
pros
-
Streamlines compliance reporting for regulated industries
-
Strong user and network behavior analytics capabilities
-
Advanced threat detection with real-time analytics
cons
-
Pricing is higher than many mid-market SIEM solutions
-
Initial setup and tuning require significant time investment
-
Interface can feel outdated compared to newer tools
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Our Review Methodology
How We Test & Score Tools
We’ve spent years building, refining, and improving our software testing and scoring system. The rubric is designed to capture the nuances of software selection and what makes a tool effective, focusing on critical aspects of the decision-making process.
Below, you can see exactly how our testing and scoring works across seven criteria. It allows us to provide an unbiased evaluation of the software based on core functionality, standout features, ease of use, onboarding, customer support, integrations, customer reviews, and value for money.
Core Functionality (25% of final scoring)
The starting point of our evaluation is always the core functionality of the tool. Does it have the basic features and functions that a user would expect to see? Are any of those core features locked to higher-tiered pricing plans? At its core, we expect a tool to stand up against the baseline capabilities of its competitors.
Standout Features (25% of final scoring)
Next, we evaluate uncommon standout features that go above and beyond the core functionality typically found in tools of its kind. A high score reflects specialized or unique features that make the product faster, more efficient, or offer additional value to the user.
We also evaluate how easy it is to integrate with other tools typically found in the tech stack to expand the functionality and utility of the software. Tools offering plentiful native integrations, 3rd party connections, and API access to build custom integrations score best.
Ease of Use (10% of final scoring)
We consider how quick and easy it is to execute the tasks defined in the core functionality using the tool. High scoring software is well designed, intuitive to use, offers mobile apps, provides templates, and makes relatively complex tasks seem simple.
Onboarding (10% of final scoring)
We know how important rapid team adoption is for a new platform, so we evaluate how easy it is to learn and use a tool with minimal training. We evaluate how quickly a team member can get set up and start using the tool with no experience. High scoring solutions indicate little or no support is required.
Customer Support (10% of final scoring)
We review how quick and easy it is to get unstuck and find help by phone, live chat, or knowledge base. Tools and companies that provide real-time support score best, while chatbots score worst.
Customer Reviews (10% of final scoring)
Beyond our own testing and evaluation, we consider the net promoter score from current and past customers. We review their likelihood, given the option, to choose the tool again for the core functionality. A high scoring software reflects a high net promoter score from current or past customers.
Value for Money (10% of final scoring)
Lastly, in consideration of all the other criteria, we review the average price of entry level plans against the core features and consider the value of the other evaluation criteria. Software that delivers more, for less, will score higher.
Core Features
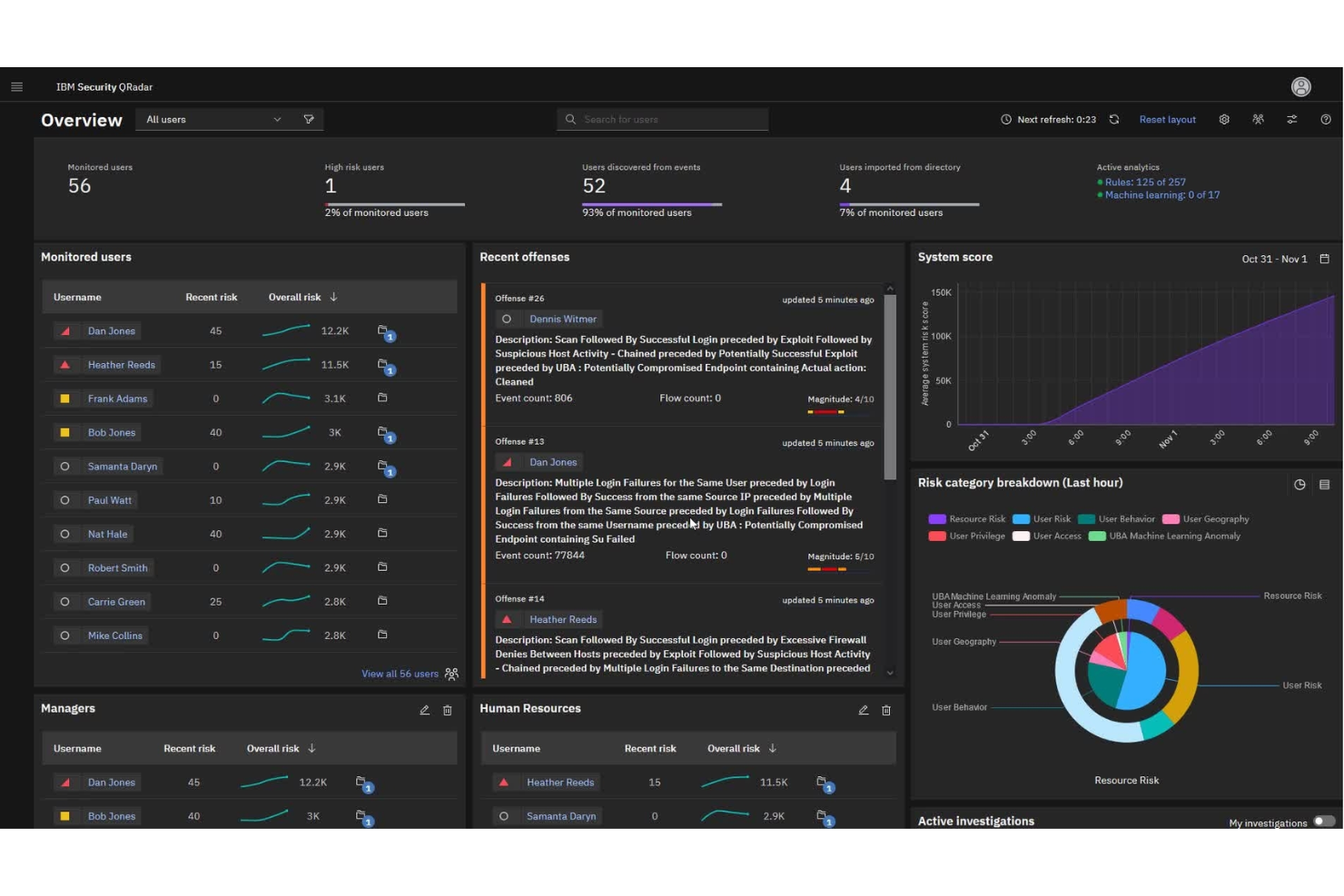
User Behavior Analytics
Detects insider threats by analyzing user actions and highlighting risky behavior. Helps uncover anomalous activity with clear, actionable insights.
Network Threat Analytics
Monitors network traffic in real time to identify suspicious patterns. Provides deep visibility into lateral movement and advanced attacks.
Sigma Community Rules
Supports thousands of open source Sigma rules for flexible, up-to-date threat detection. Lets analysts quickly import new detection logic as threats evolve.
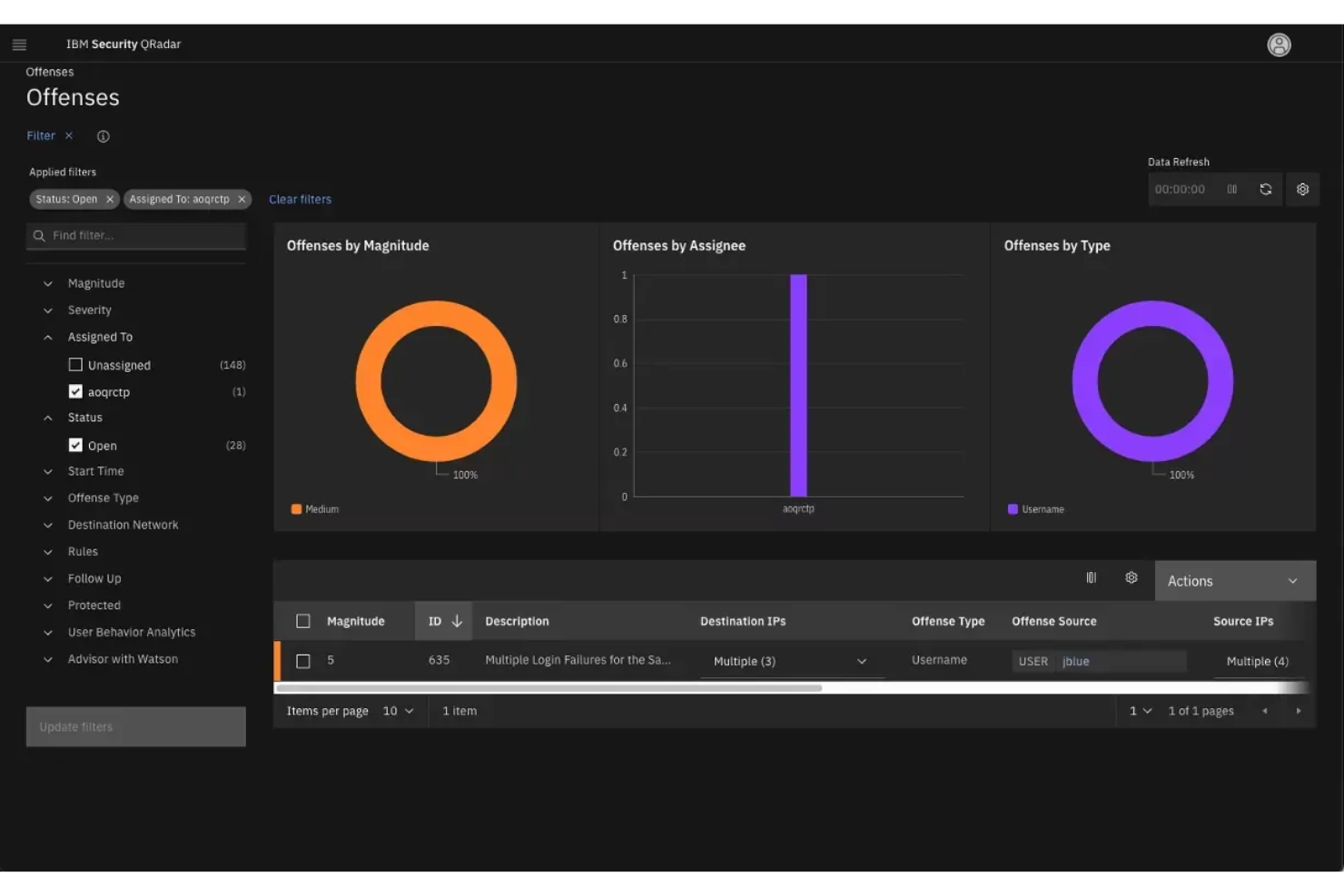
Advanced Threat Detection
Correlates data from multiple sources to spot sophisticated attacks. Automates alerting and prioritization to reduce manual investigation time.
Threat Hunting
Enables analysts to search across datasets for hidden threats. Turns disparate security data into actionable intelligence for proactive defense.
Compliance Reporting
Generates audit-ready reports for regulations like HIPAA and FISMA. Streamlines evidence collection and documentation for internal and external audits.
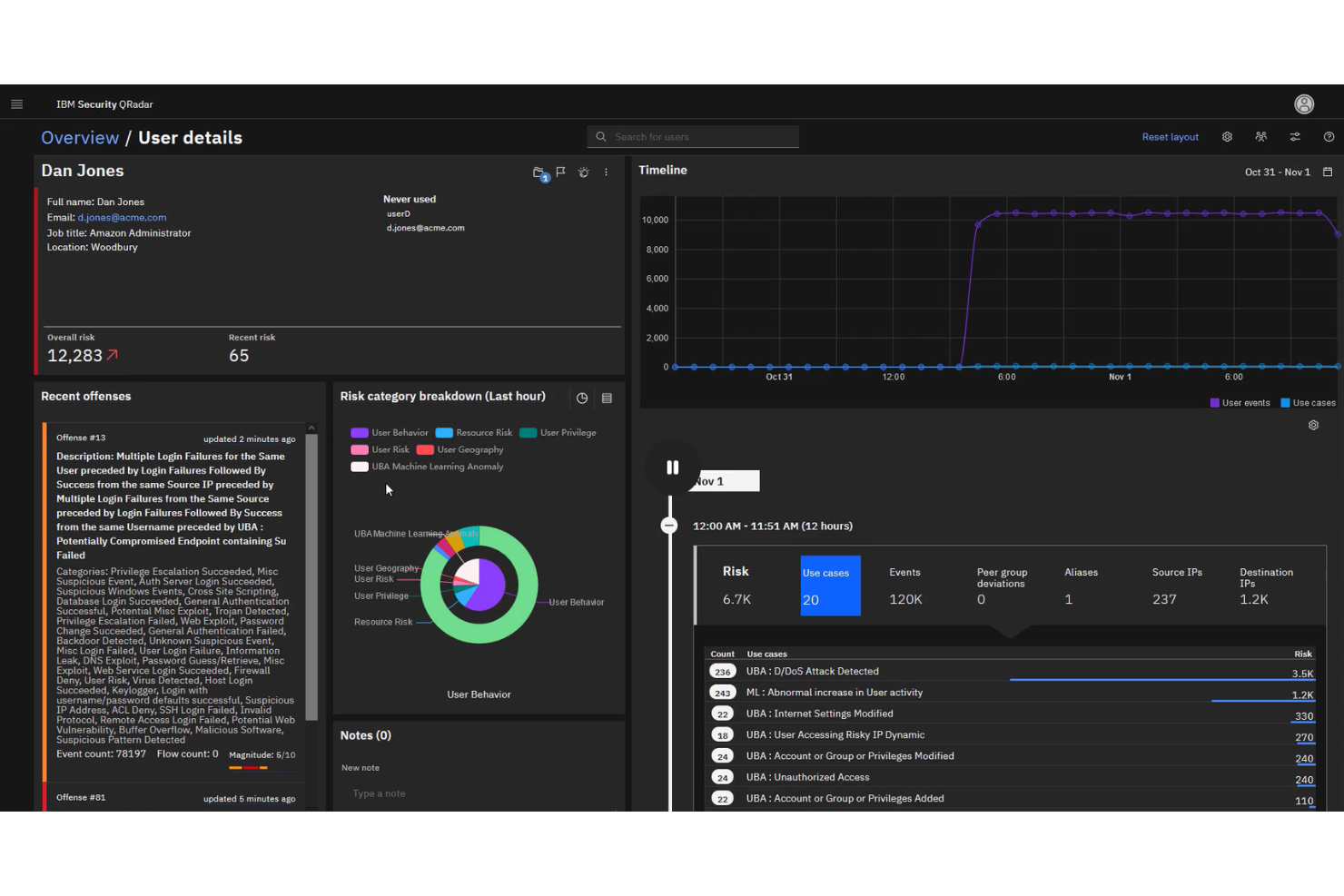
Ease of Use
IBM QRadar offers deep functionality but can feel complex and overwhelming, especially during initial setup and tuning. Many users report that the interface is less intuitive than newer SIEM tools, requiring more training and expertise to navigate.
However, once configured, its dashboards and automated workflows provide clear visibility and efficient investigation paths for experienced security teams. The learning curve is offset by the platform’s powerful analytics and customization options.
Integrations
IBM QRadar integrates with AWS, Microsoft, Google Cloud, Palo Alto Networks, CrowdStrike, Trend Micro, Cisco, Splunk, Tenable, and Mimecast, among others.
IBM QRadar also offers a robust API and supports custom integrations, allowing connections with a wide range of third-party tools and platforms.
IBM Security QRadar SIEM Specs
- 2-Factor Authentication
- Anti-Virus
- API
- Bug Tracking
- Dashboard
- Data Export
- Data Import
- Data Visualization
- Email Integration
- External Integrations
- Firewall
- Google Apps Integration
- Malware Protection
- Multi-User
- Network Traffic Monitoring
- Network Visualization
- Notifications
- Third-Party Plugins/Add-Ons







