Best Web Application Penetration Testing Tools Shortlist
The best web application penetration testing tools help teams uncover vulnerabilities early, validate security controls, and protect sensitive data across complex applications. When misconfigurations slip through reviews, automated scanners miss high-risk issues, or gaps appear between manual testing and CI/CD pipelines, security weaknesses can go unnoticed and become costly to fix later.
The right penetration testing platform gives security teams accurate findings, clear reporting, and workflows that fit naturally into existing development processes. As a Chief Technology Officer with over 20 years of experience testing and implementing security tools in active web environments, I’ve evaluated the top solutions based on accuracy, integration quality, and ease of use. Each review covers features, pros and cons, and ideal use cases to help your team choose the best web application penetration testing tool for stronger, more reliable application security.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Web Application Penetration Testing Tools Summary
This comparison chart summarizes pricing details for my top WAPT tool selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for proactive, automated penetration testing | 14-day free trial + free demo available | From $149/month | Website | |
| 2 | Best for continuous vulnerability scanning & pentesting for 9300+ test cases | Free demo available | From $69/month | Website | |
| 3 | Best for hybrid AI + human pentesting | Free plan available | From $200/month | Website | |
| 4 | Best for business logic vulnerability detection | Free demo available | Pricing upon request | Website | |
| 5 | Best for AI pentests | Free plan available + free demo | From $350/month | Website | |
| 6 | Best for configuring scan profiles | Free demo available | Pricing upon request | Website | |
| 7 | Network protocol analyzer that is fully open source, and tracks your network and traffic for cyber security | Free download available | Free to use (open source) | Website | |
| 8 | Best fully managed web application firewall (WAF) solution | 14-day free trial + free demo | From $99/month | Website | |
| 9 | Best for real-time performance monitoring | Free trial + free demo available | Pricing upon request | Website | |
| 10 | Best for DeepScan technology in complex web applications | Free demo available | Pricing upon request | Website |
-

QA Wolf
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

NordLayer
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.3 -

Intruder
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Web Application Penetration Testing Tool Reviews
Below are my detailed summaries of the best web application penetration testing tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
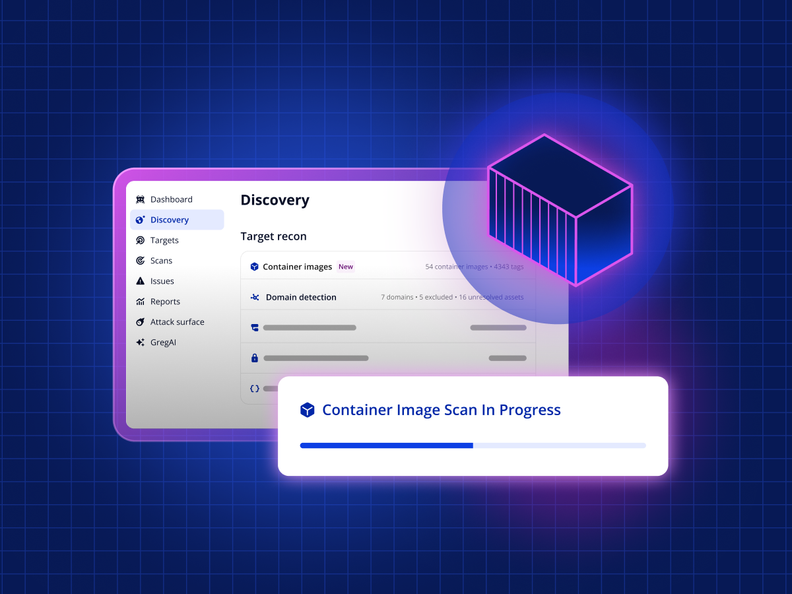
Intruder is a vulnerability management tool designed to help businesses identify and address security weaknesses across their digital infrastructure. It provides continuous network monitoring, automated vulnerability scanning, and proactive threat response, which collectively contribute to a more secure IT environment for companies aiming to minimize their attack surface.
I chose this platform for my list because of its automation capabilities. It uses underlying vulnerability scanners to take a proactive approach to vulnerability management. This automated scanning feature allows for regular and systematic vulnerability assessments of digital assets with minimal manual effort. Meanwhile, the tool's continuous monitoring and real-time threat monitoring capabilities ensure that security statuses are always current, adapting to new threats and environmental changes.
The software integrates natively with Slack, Microsoft Teams, Jira, Github, and Gitlab. Other integrations can be accessed through Zapier and API.
Paid plans start from $196 per month, per application. A 14-day free trial is also available.
New Product Updates from Intruder
Intruder Unveils Agentless Container Image Scanning
Intruder introduces agentless container image scanning across cloud platforms. This update helps teams detect vulnerabilities before deployment with less setup. For more information, visit Intruder’s official site.
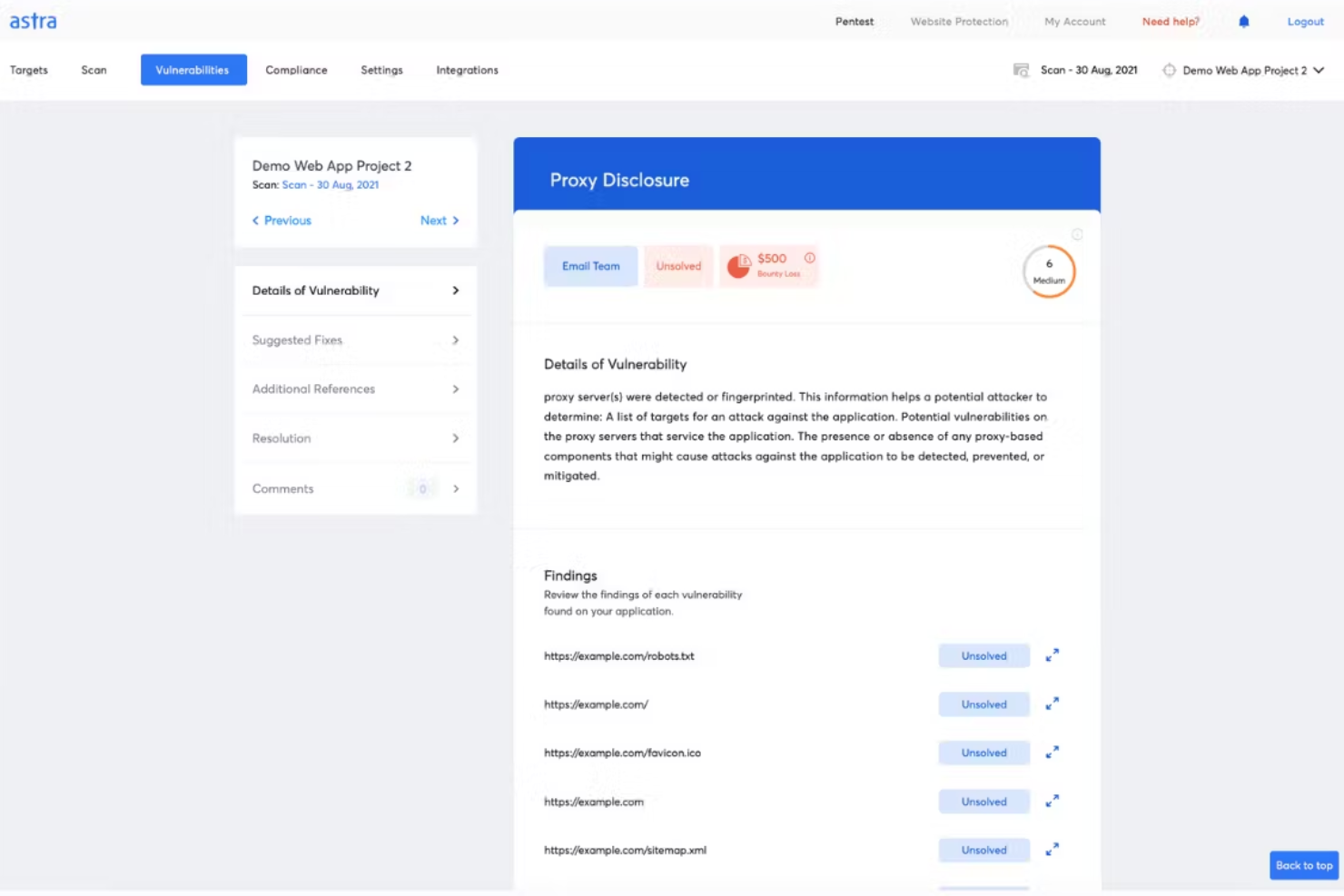
Best for continuous vulnerability scanning & pentesting for 9300+ test cases
Astra Pentest is a developer-friendly pentest platform featuring an automated vulnerability scanner and manual pentesting by security experts to ensure zero false positives. The platform's vulnerability scanner runs 9300+ test cases covering OWASP, SANS, ISO, SOC, and other standards. This AI-powered business logic test cases feature ensures deep security testing coverage. Additionally, the AI-powered conversational chatbot gives engineers contextual insights on fixing vulnerabilities.
Astra's pentest platform provides a collaborative dashboard that allows team members and security experts to work together efficiently, and it offers a publicly verifiable security certificate to help build trust with customers and partners. The platform also provides real-time support from security experts and emphasizes continuous scanning, which enables ongoing monitoring and detection of security issues.
Furthermore, like the vulnerability scanner, the penetration testing tool covers a wide range of security standards and offers compliance testing for regulations such as ISO 27001, HIPAA, SOC2, and GDPR. The software can also scan progressive web apps, single-page apps, and behind logged-in pages. Integrations include GitHub, GitLab, Slack, Jira, and more.
Paid plans start at $199/month for the Scanner package and they have a free demo available.
Zeropath is an AI-native application security platform designed to meet the needs of security-conscious companies aiming to enhance their web application security processes. By offering advanced tools like Static Application Security Testing (SAST) and automated vulnerability remediation, Zeropath empowers your team to detect and address vulnerabilities efficiently.
Why I Picked Zeropath
I picked ZeroPath because it brings together continuous AI-driven testing and human-led attack analysis, which is ideal if you’re looking for a web application penetration testing tool that goes beyond surface-level checks. You get automated reconnaissance and vulnerability discovery that runs 24/7, giving your team visibility into security gaps as soon as they emerge. Expert pentesters then validate findings and explore complex attack chains, so you’re not left wondering which issues are real or exploitable. This combination lets your team prioritize meaningful vulnerabilities and act on them with confidence.
Zeropath Key Features
In addition to its continuous AI + human testing approach, your team can also take advantage of:
- Automated Vulnerability Remediation: This feature provides automated fixes for identified vulnerabilities, streamlining the resolution process for your development team.
- Real-Time Feedback: Zeropath delivers immediate insights into security issues as they arise, allowing your team to address them promptly.
- Automatic retesting of fixes: Once your team applies a patch, ZeroPath validates the fix to confirm the issue is resolved.
- SARIF Comparison: This feature allows for detailed analysis and comparison of security reports, enhancing your team's ability to track and manage vulnerabilities.
- Real-time vulnerability detection: The platform alerts you as soon as new weaknesses appear in changing application environments.
Zeropath Integrations
Integrations include GitHub, GitLab, Azure DevOps, and Bitbucket.
Pros and Cons
Pros:
- Proof-of-concept exploits clarify real-world risk for teams
- AI reconnaissance expands coverage of hidden attack surfaces
- Continuous monitoring catches new vulnerabilities around the clock
Cons:
- You may need time to adjust your workflow around its automation
- Not ideal for teams wanting only traditional point-in-time tests
Escape is a web application penetration testing tool designed for organizations needing to address modern digital security challenges. It specializes in detecting business logic vulnerabilities that traditional scanners often miss, making it particularly suited for industries like finance, healthcare, and technology. By integrating into existing tech stacks, Escape helps ensure continuous security validation, aligning with the fast-paced deployment cycles of contemporary applications.
Why I Picked Escape
I picked Escape because it excels at identifying complex business-logic vulnerabilities through AI-powered Dynamic Application Security Testing (DAST), setting it apart from traditional tools. This focus on business logic security is crucial for organizations facing sophisticated cyber threats. Additionally, Escape’s integration with CI/CD pipelines ensures that security testing keeps pace with rapid development cycles, providing real-time insights and actionable remediation advice. These features make Escape a compelling choice for teams aiming to enhance their security posture without slowing down innovation.
Escape Key Features
In addition to business logic testing capabilities, Escape offers:
- API Discovery: Automatically identifies and documents APIs within your application, ensuring comprehensive security coverage.
- GraphQL Security Testing: Provides specialized testing for GraphQL APIs, addressing unique vulnerabilities associated with this technology.
- Compliance Reporting: Generates detailed reports to help meet industry compliance standards, simplifying the audit process.
- Sensitive Data Leak Detection: Identifies potential data leaks within your applications, helping to safeguard sensitive information.
Escape Integrations
Escape integrates with modern tech stacks, including CI/CD platforms, to provide seamless security validation. Native integrations include GitHub, GitLab, Jenkins, JIRA, Slack, Bitbucket, Azure DevOps, AWS, Docker, and Kubernetes.
Pros and Cons
Pros:
- Strong API vulnerability detection, including coverage for REST and GraphQL endpoints
- Advanced scanning technology that finds a wide range of security issues
- Continuous scanning and verification that support ongoing security monitoring
Cons:
- Requires technical familiarity to use advanced features effectively
- Platform upgrades can take time to apply and adapt to
Aikido Security’s Attack module delivers autonomous AI penetration testing that mirrors real attacker behavior, providing validated results in hours instead of weeks. It can be used as a standalone pentesting tool or as part of the broader Aikido platform, which also includes modules for code, cloud, and runtime protection. Together, these tools give teams continuous visibility into vulnerabilities across their entire environment.
Aikido Security also includes robust DAST capabilities for black-box testing. It examines your web applications and APIs from the outside without needing access to source code, helping you simulate real-world attacks and uncover potential weaknesses. This approach gives your team a clearer view of external risks and what needs to be fixed to strengthen your defenses.
Another helpful feature is authenticated DAST scanning. By logging in as a user before testing, Aikido can assess a greater portion of the application, identifying vulnerabilities that unauthenticated scans may miss. The platform also provides static application security testing (SAST) to detect issues such as SQL injection and cross-site scripting directly in your codebase.
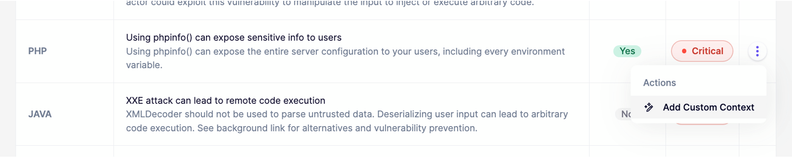
New Product Updates from Aikido Security
Aikido Security Enhances AI Pentest and AutoTriage Accuracy
Aikido Security introduces AI Pentest vulnerability escalation and custom context for AutoTriage to enhance exploitability assessment and reduce false positives. For more information, visit Aikido Security's official site.
Invicti offers a security platform that not only identifies vulnerabilities but also validates and prioritizes them, ensuring your digital assets remain protected. Designed for businesses ranging from IT and financial services to healthcare and government sectors, it addresses the challenge of safeguarding web applications and APIs against potential exploits. By integrating seamlessly into your development pipeline, Invicti helps maintain a robust security posture without disrupting your workflow.
Why I Picked Invicti
I picked Invicti for its exceptional capability in configuring pre-set scan profiles, a feature that stands out in the realm of web application penetration testing tools. This functionality allows you to customize and automate scanning processes, ensuring that security checks are both comprehensive and consistent. The platform also includes dynamic application security testing (DAST) with a high accuracy rate, which is crucial for pinpointing vulnerabilities effectively. Additionally, its seamless integration with CI/CD pipelines means you can maintain security without slowing down your development cycle.
Invicti Key Features
In addition to its pre-set scan profiles, Invicti offers several key features that enhance your security management:
- DAST Engine: Provides a high accuracy rate of 99.98% using AI innovations to quickly identify vulnerabilities.
- Software Composition Analysis (SCA): Identifies vulnerabilities in open-source components, allowing you to address risks in your software supply chain.
- Container Security: Offers scanning for container images to detect vulnerabilities before deployment.
- Role-Based Access Control: Ensures that only authorized personnel have access to critical security functions, enhancing data protection.
Invicti Integrations
Integrations include Bitbucket, Azure API Management, Mend.io, Amazon API Gateway, Kubernetes, Apigee API Hub, MuleSoft Anypoint Exchange, Azure Boards, FogBugz, and Bugzilla.
Network protocol analyzer that is fully open source, and tracks your network and traffic for cyber security
Wireshark is a powerful open source network packet sniffer equipped for the deep inspection of hundreds of different protocols, with more being added all the time. Wireshark runs on multiple platforms, including Windows, macOS, Linux, Solaris, NetBSD, FreeBSD, and many others.Wireshark can read live data from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others in a wide range of file formats. Data can easily be exported, compressed and decompressed for offline analysis, and the platform also has a user-friendly built-in network protocol debugging environment.Wireshark integrates with a wide range of tools, including network software emulators like GNS3.Wireshark is open source and free to use.
AppTrana is a web application firewall (WAF) used for penetration testing, behavioral-based DDoS protection, mitigating bot attacks, and defending against the OWASP top 10 vulnerabilities. AppTrana is employed by security-conscious companies across myriad industries, such as Axis Bank, Jet Aviation, Niva Health Insurance, and TRL Transport.
AppTrana is a fully managed security solution, which means that their web security expert team takes on the analyzing and updating of security policies so you don't have to. Higher-level accounts will get a named account manager to assist them; the highest subscription level comes with quarterly service reviews (highly recommended!).
Key features include unlimited application security scanning, manual pen-testing of applications, managed CDN, false positive monitoring, custom SSL certificates, and risk-based API Protection. Their website is packed full of detailed feature explanations as well as a blog, learning center, whitepapers, infographics, and datasheets, so I highly recommend you take a look around for yourself.
AppTrana costs from $99/month/app and comes with a free 14-day trial.
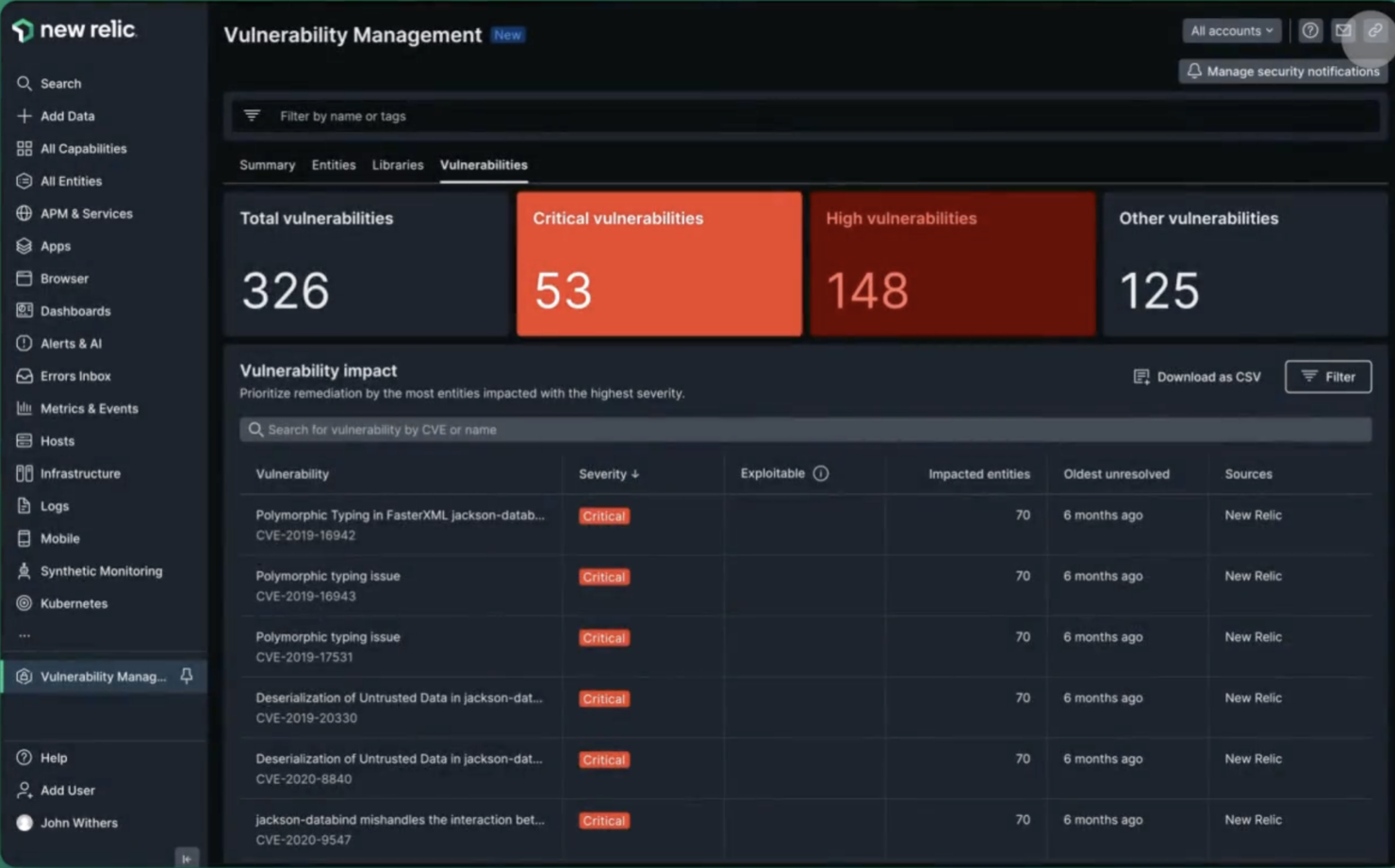
New Relic is a real-time monitoring tool designed to help you track application performance, identify bottlenecks, and resolve issues before they become problems. Steve Morris, Founder and CEO at NEWMEDIA.COM, explained: “At petascale, ingest costs can sneak up and bite you in the a**. Using drop filter rules and the NerdGraph API, we eliminated duplicate log payloads and muddy chatter from some of our wackier metrics.”
The platform includes real-time performance monitoring that lets you see exactly how an app is performing in real time so you can spot any issues as they happen and fix them straight away. It also includes detailed analytics, which allow you to drill down into an app's performance data to find out exactly what's going on. And it's all presented in a really easy-to-understand way.
Key features include backend monitoring, Kubernetes monitoring, mobile monitoring, model performance monitoring, infrastructure monitoring, log management, error tracking, network monitoring, vulnerability management, and browser monitoring.
Integrations include over 500 apps, like AWS, Google Cloud, and Microsoft Azure; CI/CD tools like Jenkins, CircleCI, and Travis CI; communication tools like Slack and PagerDuty; and other monitoring and analytics tools like Grafana, Datadog, and Splunk. It also has an API you can use to build custom integrations.
New Relic costs from $49/user/month and offers a free plan for 1 user and 100 GB/month of data ingest.
Acunetix is a comprehensive web application and API security scanner designed to help organizations automate their application security testing. It offers a robust suite of features, including API discovery and security, which allows users to find and test APIs without disrupting development workflows.
Acunetix uses DeepScan Technology, which allows the tool to fully automate the crawling of complex custom HTML5 websites and web applications, including client-side single-page applications (SPAs). This technology enables Acunetix to interact with JavaScript-rich web applications just like a real user would, ensuring that even the most intricate parts of a web application are thoroughly tested.
Another significant feature is the Login Sequence Recorder (LSR), which simplifies the process of authenticated web application testing. This tool allows users to record a series of actions and/or restrictions and replay them to authenticate a page, making it easier to test web applications that require login credentials.
Integrations include Azure Boards, BitBucket, Bugzilla, DefectDojo, FogBugz, Freshservice, GitHub, GitLab Issues, Invicti Standard, Jazz Team Server, Jira, and Kafka.
Pricing is available upon request.
Other Web Application Penetration Testing Tools
Here are some additional web application penetration testing tools options that didn’t make it onto my shortlist, but are still worth checking out:
- Medusa
For thread-based parallel testing
- Burp Suite
Provides a passive scan feature
- Amass
For external asset discovery
- Gobuster
For developers
- Nessus
Easy to use credential and non credential scans
- NMap
Lightweight solution to web application penetration testing
- John the Ripper
Penetration testing tool and password cracker which allows you to test the strength of your passwords
- Metasploit
Automate manual tests and streamline your process
- Zed Attack Proxy (ZAP)
Focuses on being the “middleman proxy” between browser and application
- Core Impact
For replicating multi-staged attacks
- SQLMap
For SQL injection techniques
- Pcloudy
For functional experience testing
- Wfuzz
For uncovering hidden vulnerabilities
- Web site software development
For data security emphasis
Web Application Penetration Testing Tools Selection Criteria
When selecting the best web application penetration testing tools to include in this list, I considered common buyer needs and pain points like identifying vulnerabilities and ensuring data protection. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Identify security vulnerabilities
- Provide automated scanning
- Generate detailed reports
- Support multiple web technologies
- Offer real-time alerts
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Machine learning integration
- Customizable dashboards
- Multi-language support
- Cloud-based deployment
- Advanced threat intelligence
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Customizable user settings
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Use of templates for setup
- Chatbot assistance
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multiple support channels
- Response time
- Access to a knowledge base
- Availability of dedicated account managers
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Availability of free trials
- Pricing transparency
- Flexible subscription plans
- Discounts for bulk purchases
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction rating
- Feedback on ease of use
- Comments on feature effectiveness
- Support service feedback
- Pricing satisfaction
How to Choose a Web Application Penetration Testing Tool
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the tool scale with your growing needs? Consider the number of users and applications it can handle without performance issues. |
| Integrations | Does it integrate with your existing systems? Look for compatibility with other security tools and development platforms you already use. |
| Customizability | Can you tailor the tool to fit your specific workflows? Check if it allows for customization of dashboards and reports. |
| Ease of use | Is the tool user-friendly for your team? Evaluate the learning curve and whether it requires extensive training or technical expertise. |
| Implementation and onboarding | How long will it take to get up and running? Consider the setup complexity and availability of resources like tutorials and support during implementation. |
| Cost | Does the pricing fit your budget? Compare the cost against the features offered and look for hidden fees or long-term contracts. |
| Security safeguards | Are there strong security measures in place? Ensure the tool complies with your security standards and offers data protection features. |
| Compliance requirements | Does it meet industry compliance standards? Verify if the tool supports necessary regulations like GDPR or PCI-DSS for your specific sector. |
What Are Web Application Penetration Testing Tools?
Web application penetration testing tools identify security vulnerabilities in web applications. Security professionals and developers typically use these tools to protect sensitive data and ensure application safety.
Automated scanning, real-time alerts, and detailed reporting capabilities help with identifying threats and maintaining security standards. Overall, these tools are essential for safeguarding web applications against potential attacks.
Features
When selecting web application penetration testing tools, keep an eye out for the following key features:
- Comprehensive vulnerability scanning: This feature automatically scans your web apps for a wide range of security vulnerabilities like SQL injection, cross-site scripting, and misconfigured security settings. It helps you catch hidden threats early, so you’re not left playing security whack-a-mole.
- Authentication testing: This checks whether your application’s login and session management mechanisms are secure. By simulating different types of attacks, you find out if credentials, sessions, and permissions are watertight or need work.
- Reporting and analytics: Clear, detailed reports summarize scan findings in a way you can actually act on. These tools sort vulnerabilities by severity, offer remediation steps, and often allow you to export results for sharing with your team (or showing off a little).
- Customizable test cases: You get to tweak or create your own test scenarios to address unique risks in your environment. This puts you in control, so your testing isn’t stuck in a “one-size-fits-all” rut.
- Integration capabilities: These tools connect with your other security or development platforms, such as CI/CD pipelines, ticketing systems, or security dashboards. It helps keep your workflow smooth, so you’re not always jumping between tabs.
- Crawling and discovery: This explores your entire web application, mapping out public and hidden content. You won’t miss sections of your app that need securing because the tool brings them all to light.
- False positive reduction: Nobody wants to waste time on fake threats. Tools with good false positive reduction help you focus on genuine security problems instead of chasing ghosts.
- Compliance checks: Many tools check your web applications for compliance with standards like OWASP Top 10 or PCI DSS. This helps you make sure you’re meeting industry requirements, which can keep both auditors and customers happy.
Common Web Application Penetration Testing Tools AI Features
Beyond the standard web application penetration testing tools features listed above, many of these solutions are incorporating AI with features like:
- Automated threat detection: Here, AI learns from previous scans and new threat data to spot security issues that might slip past regular scans. The system gets smarter, so you don’t have to spot every tricky vulnerability yourself.
- Intelligent prioritization: AI analyzes scan data, predicts the real-world impact of vulnerabilities, and ranks them by risk. You get actionable insights on what to tackle first, not just a long laundry list of issues.
- Adaptive crawling: AI-powered crawlers learn the structure of even complex or dynamic websites, discovering hidden routes or content more effectively than traditional tools. It means fewer missed spots during your security review.
- Contextual attack simulation: With AI, these tools tailor simulated attacks based on your app’s unique features and user behavior, giving you a more accurate sense of your real exposure.
- Anomaly detection: AI watches your web app for behaviors that aren’t normal—like unusual login patterns or unexpected data requests—and flags them for review. You get advanced warning of oddball threats before they blow up.
Benefits
Implementing web application penetration testing tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security: By identifying vulnerabilities with automated scanning, your team can address threats before they become serious issues.
- Time efficiency: Real-time alerts and automated processes save your team time, allowing them to focus on other critical tasks.
- Enhanced compliance: Compliance support ensures your business meets industry regulations, reducing legal risks.
- Informed decision-making: Detailed reporting provides insights that help prioritize security measures and allocate resources effectively.
- Customizable experience: Customizable dashboards let users focus on relevant data, improving workflow efficiency and user satisfaction.
- Ease of use: A user-friendly interface reduces the learning curve, making it easier for your team to adopt and use the tools effectively.
Costs & Pricing
Selecting web application penetration testing tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in web application penetration testing tools solutions:
Plan Comparison Table for Web Application Penetration Testing Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic scanning capabilities, limited reporting, and community support. |
| Personal Plan | $10-$30/user/month | Automated scanning, real-time alerts, customizable dashboards, and email support. |
| Business Plan | $50-$100/user/month | Detailed reporting, integration capabilities, compliance support, and phone support. |
| Enterprise Plan | $150-$300/user/month | Advanced threat intelligence, dedicated account manager, full customization, and 24/7 support. |
Web Application Penetration Testing Tool FAQs
Here are some answers to common questions about WAPT tools:
How often should you conduct web application penetration testing?
It’s recommended to conduct penetration testing at least annually, or whenever significant changes are made to the application. Regular testing helps identify new vulnerabilities that could arise from updates or changes in the application’s environment.
Can penetration testing tools replace manual testing?
No, penetration testing tools complement but don’t replace manual testing. Automated tools can quickly identify known vulnerabilities, but manual testing is essential for uncovering complex logic flaws and contextual security issues that require human insight and expertise.
How do you ensure the findings from penetration testing are addressed?
After testing, prioritize addressing vulnerabilities based on risk levels. Develop a remediation plan with clear timelines and responsibilities. Regularly update your security practices and conduct follow-up tests to verify that issues have been resolved.
What’s Next:
If you're in the process of researching web application penetration testing tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.