10 Best Security Testing Tools Shortlist
Here’s my shortlist of the best security testing tools:
Security vulnerabilities aren’t just a risk—they’re an ongoing challenge. Your team needs to find weaknesses before attackers do, but manual testing is time-consuming, automated scans can flood you with false positives, and keeping up with evolving threats isn’t easy. Whether you're securing cloud applications, testing APIs, or ensuring compliance, picking the right security testing tool is critical.
That’s why I’ve spent time testing and evaluating security tools that actually help teams identify vulnerabilities, automate testing, and focus on real threats without slowing down development. In this guide, you’ll find detailed insights into the best security testing tools available today, along with their key features, ideal users, and how they can help protect your systems.
Why Trust Our Software Reviews
Best Security Testing Tools Summary
Below are my detailed summaries of the best security testing tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for code quality analysis | Free plan available (up to 5 users) | From $65/month | Website | |
| 2 | Best for auto-triage features | Free plan available | From $34/developer/month | Website | |
| 3 | Best for proactive vulnerability detection | Free plan available + free demo | From $350/month | Website | |
| 4 | Best for comprehensive vulnerability analysis | Free demo available | From $69/month | Website | |
| 5 | Best for context-aware code analysis | Free plan available | From $200/month | Website | |
| 6 | Best for team collaboration | Free demo available | Pricing upon request | Website | |
| 7 | Best for real-time monitoring | Free plan + free demo available | Pricing upon request | Website | |
| 8 | Best for web vulnerability scanning | Not available | Pricing upon request | Website | |
| 9 | Best for open-source management | Free demo available | From $18.67/user/month (billed annually) | Website | |
| 10 | Best for penetration testing | Not available | Free to use | Website |
-

QA Wolf
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

NordLayer
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.3.7 -

Intruder
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Security Testing Tool Reviews
Below are my detailed summaries of the best security testing tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
SonarQube is a fully featured integrated code security (SAST, SCA) and code quality solution for both self-managed and cloud deployments. It analyzes first-party, AI-generated, and open source code to detect vulnerabilities, bugs, and maintainability issues early in the development lifecycle. The platform also provides AI-powered fix suggestions to reduce manual debugging and includes built-in secrets detection covering over 400 patterns.
Why I picked SonarQube: I selected SonarQube for its balanced focus on code quality and security across multiple programming languages. It delivers clear insights into reliability and maintainability while fitting naturally into CI/CD pipelines. Its combination of customizable quality gates and security analysis helps teams uphold consistent and secure coding standards.
Standout features & integrations:
Features include support for 35 programming languages, customizable quality gates, detailed static analysis, and secrets detection for more than 400 patterns.
Integrations include Jenkins, GitHub, GitLab, Bitbucket, Azure DevOps, Bamboo, Travis CI, CircleCI, TeamCity, and Visual Studio. A free SonarQube IDE extension is available for VS Code, JetBrains IDEs, Cursor, Windsurf, and others..
Pros and Cons
Pros:
- Extensive language support
- Enhances coding standards
- Integrates with CI/CD pipelines
Cons:
- Requires setup and configuration
- Can be resource-intensive
New Product Updates from SonarQube
SonarQube Cloud Introduces Architecture Management
SonarQube Cloud now offers architecture management to automatically map your project's structure, ensuring design integrity and resolving deviations seamlessly. For more information, visit SonarQube's official site.
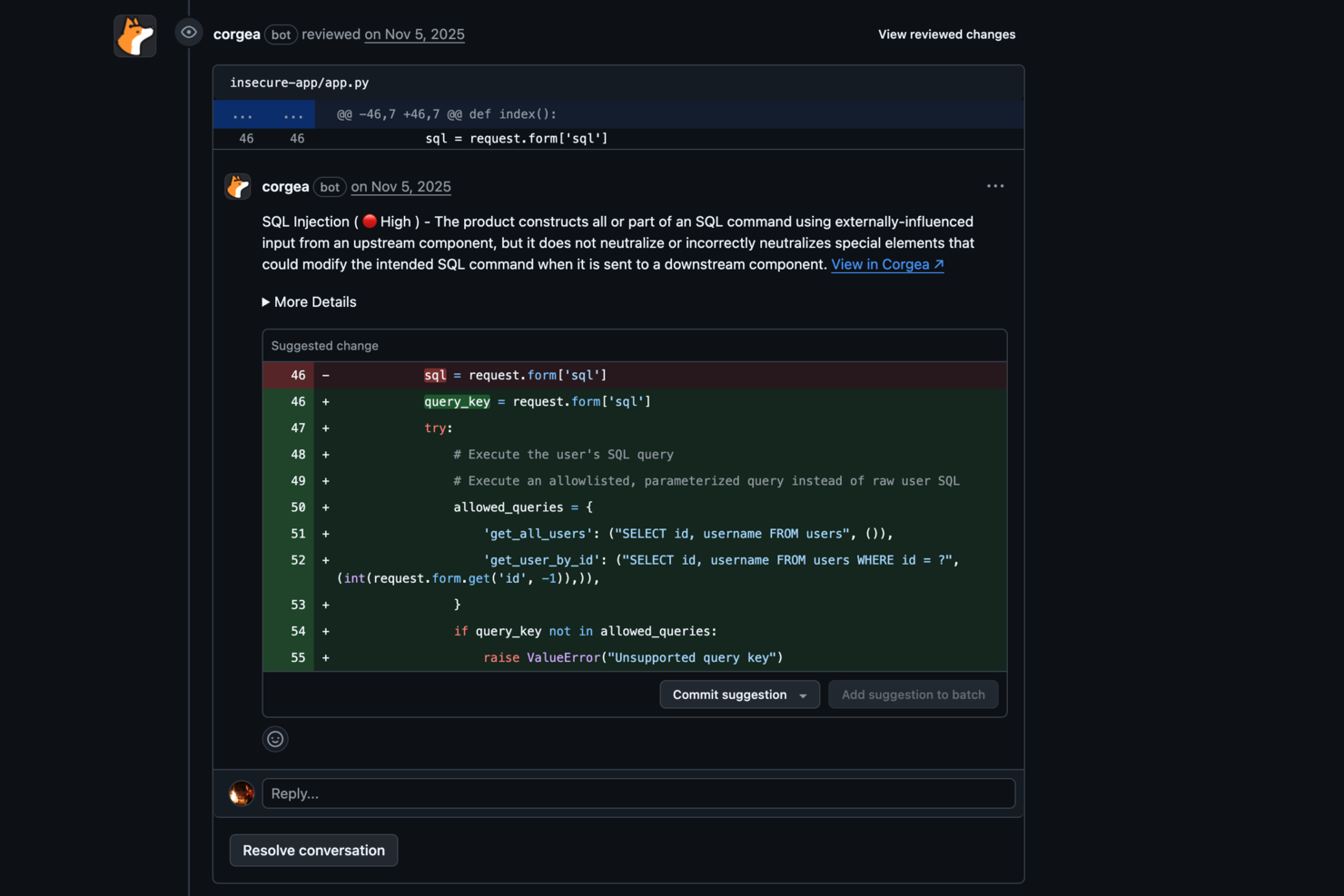
Corgea enhances your team's security capabilities by pinpointing and fixing insecure code, making it an ideal solution for CTOs seeking to safeguard their digital assets. Its AI-driven technology appeals to industries that require stringent security measures, such as finance and healthcare, by addressing vulnerabilities that could compromise sensitive data. By integrating into your existing workflows, Corgea helps your team efficiently manage security risks, ensuring peace of mind and allowing you to focus on innovation.
Why I Picked Corgea
I picked Corgea for its AI-driven Static Application Security Testing (SAST), which excels in identifying complex vulnerabilities that traditional methods might miss. The auto-triage feature significantly reduces false positives, saving your team time and allowing them to focus on actual threats. Additionally, Corgea's customizable detection policies let you tailor the tool to your specific security needs, ensuring comprehensive protection against emerging threats.
Corgea Key Features
In addition to its core strengths, Corgea offers several other features that enhance its utility:
- Dependency Scanning: This feature checks for vulnerabilities in your project's dependencies across multiple programming languages.
- SAST Auto-Fix: Automatically generates security patches, reducing the manual effort required to secure your codebase.
- Privacy Leak Detection: Identifies sensitive information such as AWS keys and authentication credentials to prevent privacy breaches.
- Multi-Language Support: Supports a wide range of programming languages, including Java, Python, and Ruby, ensuring compatibility with your projects.
Corgea Integrations
Integrations include GitHub Actions, GitLab CI, Jenkins, Azure DevOps, JIRA, Slack, Zapier, and webhooks.
Pros and Cons
Pros:
- Broad CI/CD integrations
- Automated secure code fixes
- AI detects complex vulnerabilities
Cons:
- Focused mainly on code security
- Setup required for CI integrations
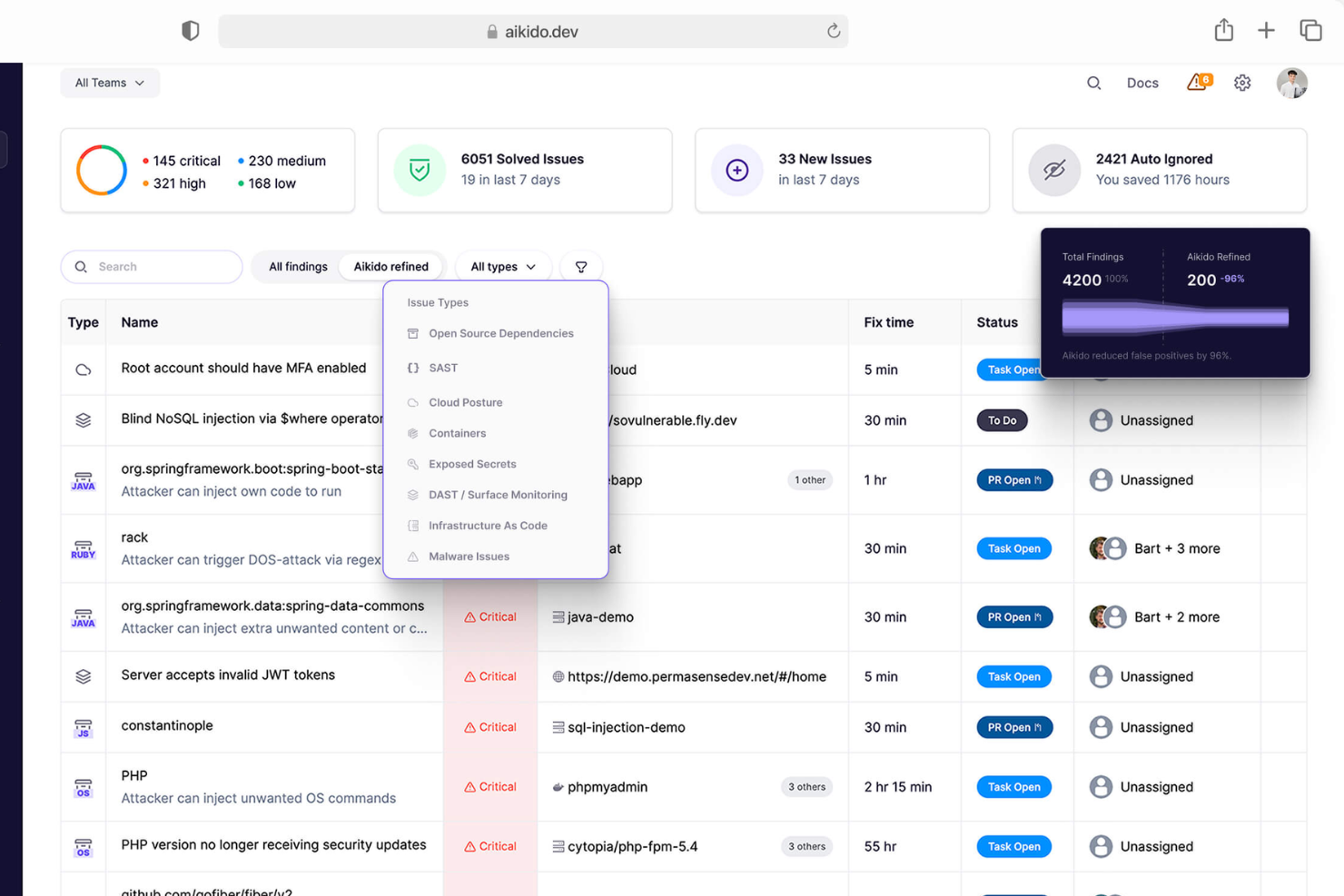
Aikido Security is a comprehensive platform designed to secure your entire stack, from code to cloud. It consolidates various security scanners into one centralized system, allowing you to monitor and protect your applications.
Why I picked Aikido Security: I like that it offers static application security testing (SAST). Aikido scans your source code for security risks before issues can be merged, helping you catch vulnerabilities early in the development process. This proactive approach ensures that potential threats are addressed promptly, reducing the likelihood of security breaches. Another notable feature is Aikido's cloud posture management (CSPM). It detects cloud infrastructure risks, such as misconfigurations and vulnerabilities in virtual machines and container images, across major cloud providers.
Standout features & integrations:
Features include open source dependency scanning (SCA), which continuously monitors your code for known vulnerabilities and generates software bills of materials (SBOMs). Additionally, Aikido's surface monitoring (DAST) dynamically tests your web application's front-end and APIs to identify vulnerabilities through simulated attacks.
Integrations include GitHub, GitLab, BitBucket, Azure Pipelines, Drata, Vanta, Asana, ClickUp, Monday.com, Microsoft Teams, and Jira.
Pros and Cons
Pros:
- Has a comprehensive dashboard and customizable reports
- Offers actionable insights
- Scalable for growing teams
Cons:
- Ignores vulnerabilities if no fix is available
- Does not have endpoint security or intrusion detection capabilities
New Product Updates from Aikido Security
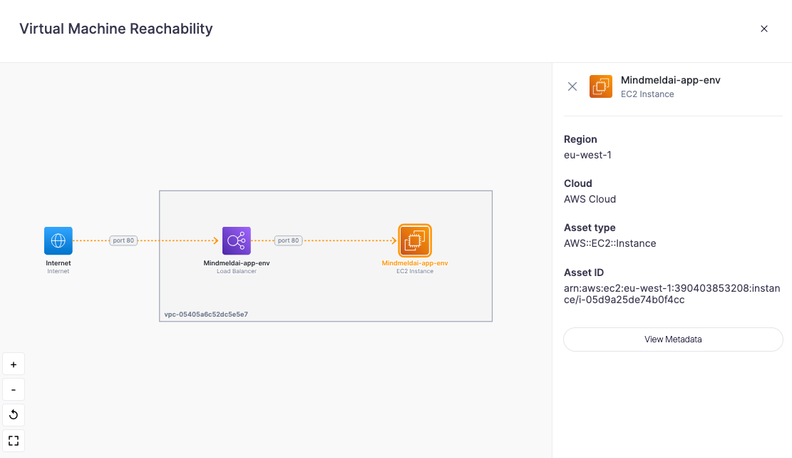
Aikido Security Adds Continuous Pentesting, VM Reachability, and IDE Scanning
Aikido Security introduces Aikido Infinite continuous pentesting, cloud VM reachability diagrams, and full workspace scanning across IDEs. These updates help teams identify exploitable vulnerabilities faster and strengthen security checks during development. For more information, visit Aikido Security’s official site.
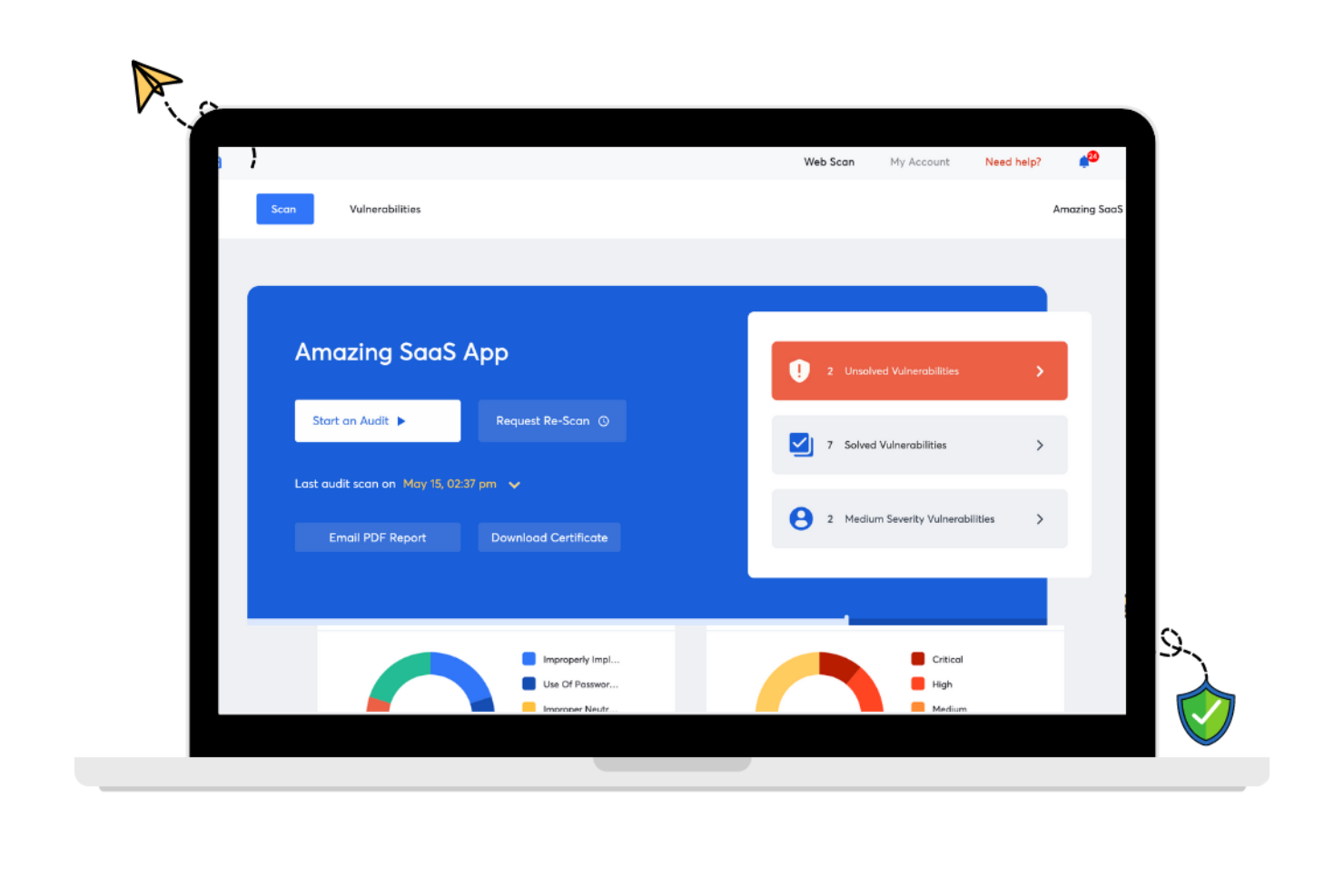
Astra Pentest is a security testing tool designed to safeguard your digital assets. It provides a thorough analysis of your web applications, networks, and more, ensuring vulnerabilities are identified and addressed.
Why I Picked Astra Pentest: I chose Astra Pentest because it offers both automated and manual testing, enabling a thorough evaluation of your system's security. This feature ensures that you get a comprehensive analysis of vulnerabilities, which is crucial for maintaining robust security standards. Additionally, Astra Pentest provides a detailed vulnerability management dashboard, helping you to efficiently track and manage any issues that are discovered. Another reason I picked Astra Pentest is its focus on compliance testing. It helps you ensure that your systems meet international security standards like SOC2 and HIPAA. This compliance feature is particularly beneficial for organizations that need to adhere to strict regulatory requirements. Moreover, Astra Pentest offers continuous scanning and re-testing, providing peace of mind that your systems remain secure over time.
Standout features & integrations:
Features include a publicly verifiable pentest certificate, which adds an extra layer of trust and assurance for your stakeholders. The tool’s integration with CI/CD pipelines allows for automated security checks during the development process, minimizing vulnerabilities before they reach production. Furthermore, Astra Pentest offers real-time remediation support, enabling your team to quickly resolve any identified issues.
Integrations include Slack, JIRA, GitHub, GitLab, Circle CI, Jenkins, and others that are not explicitly listed in the retrieved data.
Pros and Cons
Pros:
- Provides compliance-specific security scans
- Integrates with major CI/CD tools
- Combines automated and manual testing
Cons:
- Customer support response time varies
- Performance issues during heavy scans
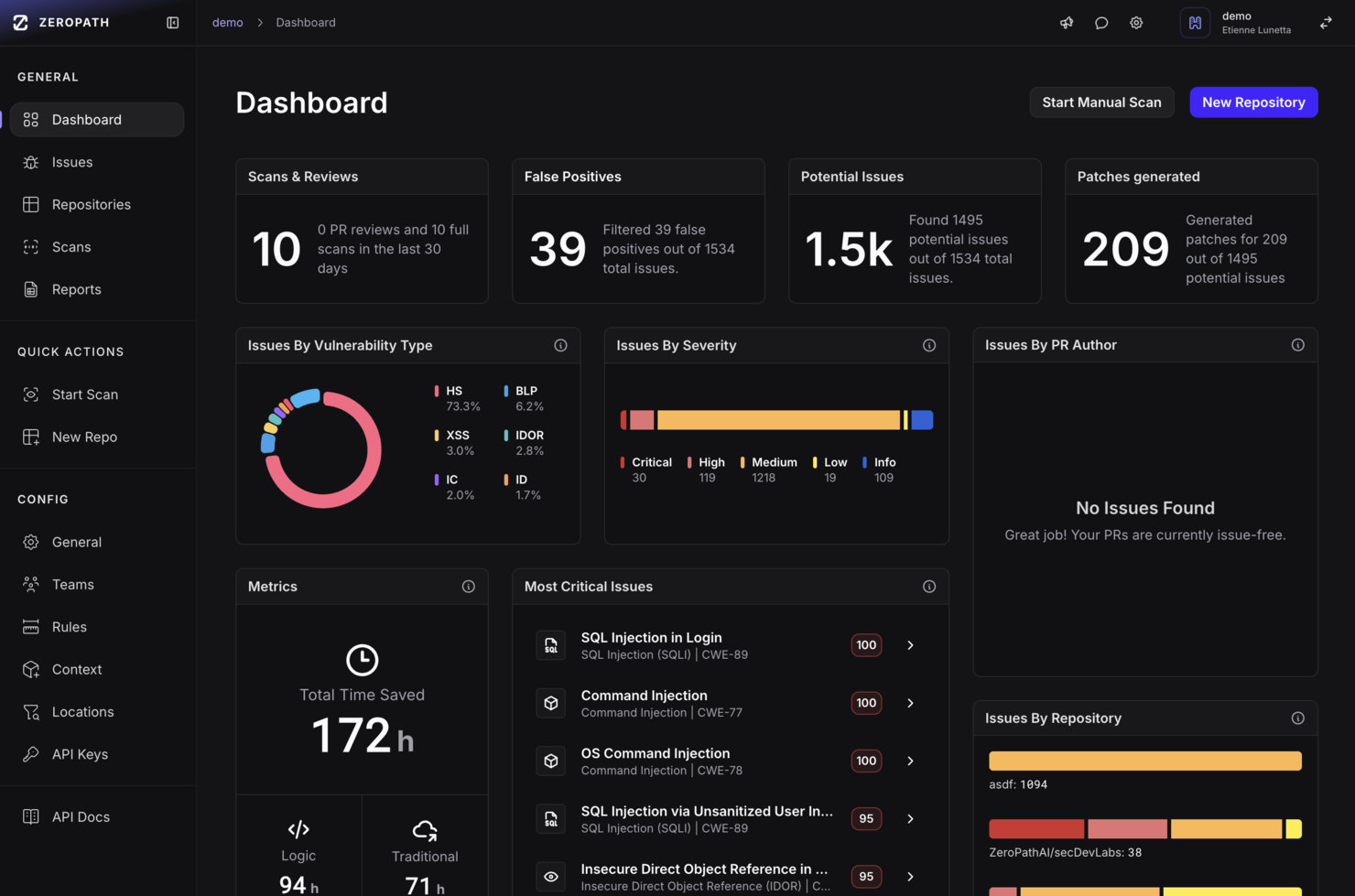
ZeroPath is designed for development teams and security professionals who want to embed deeper vulnerability detection into their codebase without sifting through countless false alarms. You’re likely in a fast-moving engineering environment where developers need actionable feedback and your security team wants meaningful results instead of noise. ZeroPath appeals to organizations building complex applications (for example, fintech, healthcare, or SaaS) where business logic, authorization flows, and modern threat classes matter.
Why I Picked Zeropath
I picked ZeroPath because it puts context-aware code analysis at the heart of application security. It uses an AI SAST engine that understands your application’s logic and can surface authorization bypasses, dependency risks and complex flaws rather than generic issues. It also offers autofix capabilities—once it finds a vulnerability, it can suggest or even generate pull-request patches you can review. These features align if your goal is to move faster while keeping risk in check.
Zeropath Key Features
In addition to those core strengths, you’ll find these features useful for your team:
- Version Control Integration: Native support for GitHub, GitLab, Bitbucket, and Azure DevOps allows for quick setup and seamless integration into your workflow.
- IaC misconfiguration detection: Infrastructure-as-Code issues (e.g., Terraform, CloudFormation, Kubernetes configs) are scanned for security flaws.
- Secrets scanning: It detects leaked secrets or hard-coded credentials across your repositories and alerts you to them.
- Automated Compliance Reporting: Generate compliance reports for standards like SOC 2 and ISO 27001, ensuring your organization meets regulatory requirements.
Zeropath Integrations
Integrations include GitHub, GitLab, Bitbucket, Azure DevOps, Jira, Linear, Slack, and existing security tools like Snyk, Semgrep, and Checkmarx.
Pros and Cons
Pros:
- It catches logic flaws and hidden risks you might miss in normal scans.
- Cuts down noisy findings so your team can focus on real issues.
- Gives you clear fixes that speed up your security reviews.
Cons:
- Integration options may not be extensive enough for complex enterprise environments.
- You may need time to adjust your workflow around its automation.
QA Wolf is a security testing tool designed for teams seeking efficient collaboration in quality assurance. This tool is ideal for teams aiming to enhance their testing capabilities and reduce deployment times.
Why I picked QA Wolf: QA Wolf offers unique features that facilitate team collaboration. Its ability to automate 80% of test coverage within four months stands out. The platform supports unlimited parallel test runs, reducing QA cycle times significantly. Additionally, its integration of AI to investigate failed tests adds value to its collaborative approach, ensuring speed and accuracy. It combines AI efficiency with human oversight, making it a reliable choice for team collaboration.
Standout features & integrations:
Features include automated testing using Playwright for web and Appium for mobile, which allows for quick automation of tests. The tool supports unlimited parallel test runs, significantly cutting down QA cycle times. It also employs AI to investigate failed tests, ensuring quick identification and resolution of issues.
Integrations include Jenkins, CircleCI, GitHub Actions, Azure DevOps, Travis CI, GitLab CI, Bamboo, TeamCity, and Bitbucket Pipelines.
Pros and Cons
Pros:
- Rapid test automation
- Significant time savings
- Efficient bug reporting
Cons:
- Limited pricing transparency
- Potential learning curve for new users
New Relic is a comprehensive observability platform designed for businesses requiring real-time monitoring and application performance enhancement.
Why I picked New Relic: The platform excels in real-time monitoring with its Application Performance Monitoring (APM) and Interactive Application Security Testing (IAST). It supports over 780 integrations, making it highly adaptable for various tech stacks. Its usage-based pricing model offers flexibility, catering to different organizational needs. The proactive threat management and zero-day vulnerability alerts are key features that align with its USP of real-time monitoring.
Standout features & integrations:
Features include end-to-end observability, which allows for comprehensive monitoring of applications. The platform offers real-time threat management to address vulnerabilities as they arise. Users also benefit from zero-day vulnerability alerts, enhancing security measures.
Integrations include AWS, Azure, Google Cloud Platform, Kubernetes, Docker, Jenkins, GitHub, Slack, PagerDuty, and Microsoft Teams.
Pros and Cons
Pros:
- Extensive integration options
- Real-time threat alerts
- Enhances team collaboration
Cons:
- May overwhelm with data
- Limited support for smaller teams
Wapiti is an open-source web application vulnerability scanner designed for security professionals and developers. It identifies vulnerabilities in web applications by performing black-box testing, which simulates attacks on your web applications to expose weaknesses.
Why I picked Wapiti: Wapiti offers a straightforward approach to web vulnerability scanning with its black-box testing methodology. It can detect a variety of vulnerabilities, such as SQL injection and cross-site scripting, ensuring comprehensive coverage for your web applications. The tool's ability to perform both GET and POST HTTP attack methods enhances its effectiveness. Its command-line interface allows for flexible and customizable scanning options, making it a valuable tool for web vulnerability scanning.
Standout features & integrations:
Features include the ability to detect a wide range of vulnerabilities, providing thorough security assessments. The tool supports both GET and POST HTTP attack methods, ensuring comprehensive testing. Wapiti's command-line interface allows for flexible and customizable scanning options, catering to your specific needs.
Integrations include compatibility with various web technologies and platforms, such as HTML5, XML, JSON, SOAP, and AJAX.
Pros and Cons
Pros:
- Supports multiple attack methods
- Customizable scanning options
- Simple command-line interface
Cons:
- Limited user interface
- Can be resource-intensive
Sonatype is a security testing tool focusing on open-source management and software supply chain security. It serves development teams and enterprises by ensuring the safety and compliance of open-source components.
Why I picked Sonatype: Sonatype excels in open-source management with its Nexus platform, which automates security checks and compliance. It provides real-time monitoring of open-source components, helping your team address vulnerabilities quickly. The tool also offers detailed insights into component health, ensuring you make informed decisions. Its ability to integrate with various development environments enhances its utility for managing open-source security.
Standout features & integrations:
Features include automated policy enforcement, which helps maintain compliance across your projects. It offers component intelligence, giving you insights into the quality and security of open-source components. The platform also provides real-time alerts on vulnerabilities, allowing you to act swiftly.
Integrations include Jenkins, GitHub, GitLab, Bitbucket, Bamboo, Azure DevOps, Jira, Eclipse, IntelliJ IDEA, and Visual Studio.
Pros and Cons
Pros:
- Strong focus on open-source security
- Real-time vulnerability alerts
- Detailed component insights
Cons:
- Can be complex to configure
- High learning curve for beginners
Zed Attack Proxy (ZAP) is an open-source web application security scanner designed for security professionals and developers. It performs penetration testing to identify vulnerabilities in web applications, helping you secure your online assets.
Why I picked Zed Attack Proxy (ZAP): ZAP provides an intuitive interface suitable for both beginners and experienced testers. It offers automated scanners and a set of tools that allow you to discover security vulnerabilities manually. Its ability to function as a proxy server enables you to intercept and modify traffic, enhancing its utility for penetration testing. The community-driven nature of ZAP ensures continuous updates and improvements, making it a reliable choice for comprehensive testing.
Standout features & integrations:
Features include automated scanners that quickly identify security vulnerabilities in web applications. The tool allows you to intercept and modify web traffic, providing a deeper analysis of potential issues. ZAP also offers a range of manual testing tools, giving you flexibility in how you conduct your security assessments.
Integrations include compatibility with Jenkins, Docker, GitHub Actions, GitLab, Azure DevOps, Bamboo, TeamCity, Travis CI, and CircleCI.
Pros and Cons
Pros:
- Supports manual and automated testing
- Intuitive interface for all users
- Offers traffic interception capabilities
Cons:
- Limited documentation for beginners
- Frequent updates may disrupt use
Other Security Testing Tools
Here are some additional security testing tools options that didn’t make it onto my shortlist, but are still worth checking out:
- SQLMap
For SQL injection testing
- ImmuniWeb
For AI-driven security
- BeEF (Browser Exploitation Framework)
For browser security testing
- Vega
For web app security
- Mend.io
For vulnerability scanning
- NowSecure
For automated mobile app security testing
- Snyk
For developer-first security
- Invicti
For automated web app testing
- Intruder
For continuous vulnerability scanning
- Astra Pentest
For continuous pentesting
- Tenable
For continuous vulnerability assessment
- UnderDefense
For managed detection and response
- Burp Suite
For manual security testing
- Probely
For scalable security assessments
- Cyberpion
For external attack surface management
- Wfuzz
For web application fuzzing
- Google Nogotofail
For network traffic testing
Security Testing Tool Selection Criteria
When selecting the best security testing tools to include in this list, I considered common buyer needs and pain points like vulnerability detection and integration with existing systems. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect vulnerabilities
- Perform penetration testing
- Conduct web application scanning
- Provide security reporting
- Support compliance requirements
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat alerts
- Integration with CI/CD pipelines
- Customizable dashboards
- AI-driven analysis
- Automated remediation suggestions
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Ease of navigation
- Minimal learning curve
- Customizable user settings
- Accessibility across devices
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates and guides
- Presence of chatbots for support
- Regular webinars for users
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Live chat options
- Comprehensive knowledge base
- Responsive email support
- Dedicated account managers
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Transparent pricing structure
- Features included in base price
- Discounts for annual billing
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction rating
- Feedback on feature effectiveness
- Comments on ease of use
- Opinions on customer support
- Insights on reliability and uptime
How to Choose Security Testing Tools
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
| Scalability | Ensure the tool can grow with your team. Consider if it can handle increased workloads and user demands. |
| Integrations | Look for compatibility with your existing tools like CI/CD pipelines and version control systems. |
| Customizability | Check if the tool allows you to tailor settings to meet your specific testing needs and workflows. |
| Ease of Use | Choose a tool with an intuitive interface. It should minimize the learning curve for your team. |
| Budget | Align the tool's cost with your financial constraints. Assess if it offers value for money. |
| Security Safeguards | Verify the tool's capabilities in protecting sensitive data and adhering to compliance standards. |
| Support | Consider the availability of customer support and resources like tutorials and guides. |
| Performance | Evaluate the tool's speed and accuracy in detecting vulnerabilities without affecting system performance. |
Trends in Security Testing Tools
In my research, I sourced countless product updates, press releases, and release logs from different security testing tools vendors. Here are some of the emerging trends I’m keeping an eye on:
- AI and Machine Learning: These technologies are being used to enhance vulnerability detection and analysis. They can identify patterns and predict potential threats faster than traditional methods. Vendors like ImmuniWeb are incorporating AI to provide smarter threat assessments.
- Cloud Security Focus: With more businesses moving to the cloud, tools are now emphasizing cloud-specific security testing. This ensures that cloud environments are as secure as on-premise ones. Solutions like Snyk are tailoring their offerings to address cloud vulnerabilities.
- Real-time Threat Intelligence: Users want up-to-the-minute insights into potential threats. Tools are integrating real-time threat feeds to provide immediate alerts and recommendations. This trend is crucial for businesses to react quickly to security incidents.
- DevSecOps Tools Integration: Security testing is becoming an integral part of the DevOps lifecycle. Tools are now designed to fit seamlessly into CI/CD pipelines, promoting a shift-left approach to security. This integration helps catch issues earlier in the development process.
- User Behavior Analytics: Analyzing user behavior is becoming a key feature to detect anomalies that could indicate security breaches. This trend helps identify insider threats and unusual access patterns. It's becoming a vital part of comprehensive security strategies.
What Are Security Testing Tools?
Security testing tools are software solutions designed to identify vulnerabilities and weaknesses in systems, applications, and networks. These tools are commonly used by security professionals, developers, and IT teams to enhance the security posture of their organizations. Features like vulnerability detection, real-time threat intelligence, and cloud security focus help with protecting sensitive data and ensuring compliance. Overall, these tools provide essential support in maintaining secure and resilient IT environments.
Features of Security Testing Tools
When selecting security testing tools, keep an eye out for the following key features:
- Vulnerability detection: Identifies weaknesses and security holes in applications, helping prevent potential breaches.
- Real-time threat intelligence: Provides up-to-the-minute alerts on emerging threats, allowing for immediate response and mitigation.
- Cloud security focus: Ensures that cloud environments are protected, addressing the unique challenges of cloud-based systems.
- DevSecOps integration: Fits into CI/CD pipelines, enabling security checks throughout the development process to catch issues early.
- User behavior analytics: Monitors and analyzes user activities to detect unusual patterns that may indicate security threats.
- Automated scanning: Conducts regular and automated security assessments, reducing the need for manual intervention and saving time.
- Customizable dashboards: Offers tailored views and reports, allowing teams to focus on the most relevant security metrics and insights.
- AI and machine learning capabilities: Enhances threat detection and analysis, providing smarter and faster security assessments.
- Compliance support: Helps ensure that systems meet industry-specific regulations and standards, reducing the risk of compliance violations.
- Manual testing tools: Provides options for in-depth, manual assessments for security professionals who require detailed analysis.
Benefits of Security Testing Tools
Implementing security testing tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security posture: By identifying and fixing vulnerabilities, these tools help protect your systems from potential threats.
- Time savings: Automated scanning reduces the need for manual checks, freeing up your team to focus on other tasks.
- Improved compliance: Tools with compliance support ensure that you meet industry standards, reducing the risk of penalties.
- Early issue detection: Integration with other DevOps security tools allows for security checks throughout development, catching problems before they escalate.
- Informed decision-making: Customizable dashboards and detailed reports provide insights that guide your security strategies.
- Proactive threat management: Real-time threat intelligence keeps you informed about emerging threats, allowing for swift action.
- Scalability: As your business grows, these tools can adapt to increased demands, ensuring ongoing security coverage.
Costs and Pricing of Security Testing Tools
Selecting security testing tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in security testing tools solutions:
Plan Comparison Table for Security Testing Tools
| Plan Type | Average Price | Common Features |
| Free Plan | $0 | Basic vulnerability scanning, limited support, and community access. |
| Personal Plan | $10-$30 /user /month | Advanced scanning capabilities, basic reporting, and email support. |
| Business Plan | $50-$100 /user /month | Comprehensive scanning, real-time alerts, compliance checks, and phone support. |
| Enterprise Plan | $150-$300/user /month | Full feature set, dedicated account management, custom integrations, and 24/7 support. |
Security Testing Tools FAQs
Here are some answers to common questions about security testing tools:
What tool is used for security testing?
Security testing involves tools like Burp Suite and OWASP ZAP for web applications, and Nmap and Wireshark for network analysis. These tools detect and mitigate security issues across different domains. They provide advanced capabilities that are essential for thorough security testing.
What are the three types of security testing?
The three main types of security testing are vulnerability scanning, penetration testing, and static analysis. Vulnerability scanning uses automated tools to identify weaknesses. Penetration testing simulates attacks to find security gaps. Static analysis examines source code for potential vulnerabilities.
Is security testing functional or nonfunctional?
Security testing is considered a form of non-functional testing. It focuses on how a system behaves under unexpected conditions rather than specific functionalities. Non-functional tests, including security testing, assess the system’s resilience and ability to handle threats.
What are the six basic principles of security testing?
The six basic principles are confidentiality, integrity, availability, authentication, authorization, and non-repudiation. These principles ensure data is protected from unauthorized access, remains accurate and accessible, and actions are accountable. They form the foundation of effective security testing.
How often should security testing be conducted?
Regular security testing is crucial to maintaining a secure environment. Ideally, conduct testing at least quarterly and after any significant system changes. This helps identify new vulnerabilities and ensures ongoing protection against evolving threats.
Can security testing tools integrate with CI/CD pipelines?
Yes, many security testing tools offer integration with CI/CD pipelines. This integration allows for continuous security checks during the development process. It helps catch vulnerabilities early and ensures that security is part of the software development lifecycle.
What's Next?
If you're in the process of researching security testing tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.