Best Endpoint Security Software Shortlist
The best endpoint security software helps teams detect threats early, prevent unauthorized access, reduce malware incidents, and maintain consistent protection across laptops, servers, and mobile devices. These tools give security teams the visibility and control they need to respond quickly without interrupting everyday work.
Organizations often pursue endpoint security solutions when unmanaged devices introduce vulnerabilities, misconfigurations allow attackers to bypass defenses, or manual investigation processes slow response times. These issues increase the risk of breaches, create operational bottlenecks, and make it difficult for security and IT teams to collaborate effectively.
With over 20 years in the industry as a Chief Technology Officer, I’ve tested and reviewed dozens of endpoint security software platforms across real environments to evaluate their detection accuracy, integration depth, and usability. This guide highlights the top endpoint security software that improve visibility, support faster response, and strengthen protection across distributed environments. Each review covers features, pros and cons, and best-fit use cases to help you choose the right tool.
Table of Contents
- Best Software Shortlist
- Why Trust Our Software Reviews?
- Compare Specs
- Reviews
- Other Endpoint Security Software
- Related Software Reviews
- Endpoint Security Software Selection Criteria
- How to Choose Endpoint Security Software
- Trends in Endpoint Security Software
- What Is Endpoint Security?
- Features
- Benefits
- Costs and Pricing
- FAQs
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Endpoint Security Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for endpoint security for distributed teams | Free demo available | from $5/person/month | Website | |
| 2 | Best for continuous monitoring | 30-day free trial + free demo available | From $149/technician/month (billed annually) | Website | |
| 3 | Best for multi-OS endpoint management | 14-day free trial | From $2/device/month | Website | |
| 4 | Best for automated incident response | 21-day free trial + free demo available | From $149/technician/month (billed annually) | Website | |
| 5 | Best for ransomware encryption protection | Free trial + free demo available | Pricing upon request | Website | |
| 6 | Best for real-time visibility and remediation | Free trial available | Pricing upon request | Website | |
| 7 | Best for protecting business data for small-to-medium-sized companies | 30-day free trial available | From $118.99/5 devices/year | Website | |
| 8 | Best for endpoint scanning and response | 30-day free trial + free demo available | From $39.95/device (billed annually) | Website | |
| 9 | Best for malware and attack prevention for small businesses | Not available | From $16.90/endpoint/year | Website | |
| 10 | Best for preventing cyber attacks for medium-sized businesses | 30-day free trial available | From $539/10 nodes/year | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
The 10 Best Endpoint Security Software Reviews
Below are my detailed summaries of the best endpoint security software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Deel IT is a global-first IT solution that helps you manage and automate your company's IT operations across more than 130 countries. It streamlines equipment and software management, making tasks like onboarding and offboarding straightforward, no matter where your distributed team members are located.
Why I picked Deel IT: I chose Deel IT because of its integrated mobile device management (MDM) and endpoint protection features. These tools allow you to automatically secure devices by configuring them with necessary security measures and business-critical applications before they're delivered to your employees. This approach reduces risks associated with manual setups and ensures that devices are ready for immediate use upon arrival.
Deel IT Standout Features & Integrations:
Features include the ability to grant and revoke application access remotely. This means you can control who has access to specific software and data, enhancing your organization's security posture. It also offers device lifecycle management, which covers everything from purchasing and provisioning to monitoring and recovering assets remotely.
Integrations include Hubstaff, QuickBooks, Google Workspace, Slack, JIRA, Brex, Dropbox, Microsoft 365, SAP S/4HANA, Airtable, Google Sheets, and HubSpot.
Pros and Cons
Pros:
- Simplifies global equipment procurement and deployment
- Provides comprehensive asset tracking and visibility
- Includes robust security features like MDM and endpoint protection
Cons:
- Mobile app is limited compared to desktop version
- Not ideal for businesses with complex asset management and IT needs
Atera is an all-in-one IT management platform that helps you monitor, manage, and secure your IT environment. It offers a unified solution combining remote monitoring and management (RMM), professional services automation (PSA), and endpoint protection tools, making it a good fit for small businesses and managed service providers (MSPs).
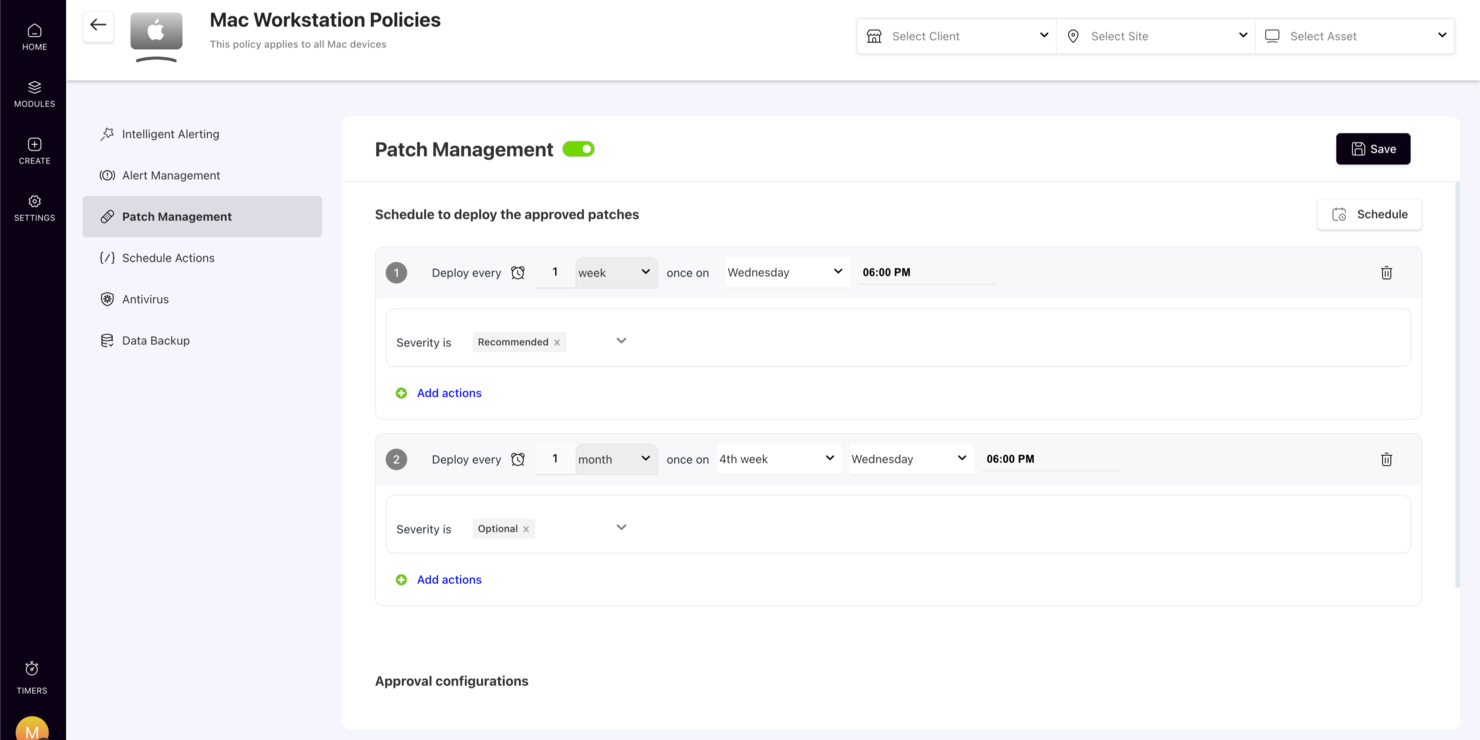
Why I picked Atera: I chose Atera for its continuous monitoring capabilities, which allow you to proactively manage endpoints across your IT environment. Its automated patch management feature helps reduce security vulnerabilities by keeping devices up to date without manual effort. I also like that Atera integrates easily with leading antivirus tools, adding another layer of protection through partnerships with providers like Bitdefender.
Atera Standout Features & Integrations:
Standout features include network discovery for identifying and monitoring all devices on your network and role-based access control to manage who can access sensitive areas of your IT infrastructure. Atera also supports compliance with key standards like ISO/IEC and GDPR, giving you additional confidence in its security posture.
Integrations include Xero, Control D, Cynet All-in-One Cybersecurity Platform, Domotz, TeamViewer, QuickBooks Online, AnyDesk, Zapier, Acronis, Splashtop, Webroot, and Bitdefender.
Pros and Cons
Pros:
- Consolidates various IT management functions like RMM, helpdesk, and ticketing
- Integrated well with third-party tools
- Centralized dashboard for key metrics
Cons:
- Not comprehensive for larger MSPs
- Learning curve for new users due to breadth of features
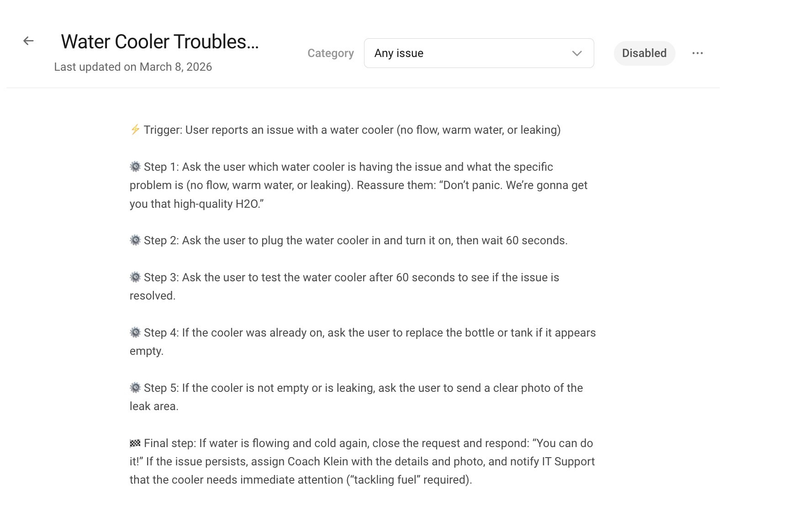
New Product Updates from Atera
Atera Enhances IT Autopilot With Automation and File Support
Atera’s IT Autopilot gets three major boosts: you can now attach common files for deeper analysis, automate IT tasks with clear workflows, and choose how the system follows up when users go silent. These updates help streamline IT operations and improve resolution efficiency. For more information, visit Atera’s official site.
Scalefusion is a unified mobile device and endpoint management solution that offers a wide range of features for managing devices and users, including location tracking, application management, geofencing, and more. The platform has a user-friendly interface and versatile deployment options for businesses of all sizes.
Why I picked Scalefusion: I chose Scalefusion for its multi-OS endpoint management capabilities. The platform enables businesses to manage and secure a wide range of devices, including smartphones, tablets, laptops, and desktops across various operating systems such as iOS, Android, Windows, and macOS. It allows IT administrators to manage this diverse range of devices from a single dashboard.
Scalefusion Standout Features & Integrations:
Features that are compelling about Scalefusion are its content management capabilities that allow users to manage and distribute content on enrolled devices, pitstops for insights into distance traveled by devices, and role-based access control. It also offers real-time location tracking, geofencing, and reports on compliance.
Integrations include Google Workspace, Google Maps, Google Drive, Okta, Azure AD, Office 365 AD, Samsung Knox, Lenovo, Kyocera, Jira, Freshservice, Janam, and more.
Pros and Cons
Pros:
- API available for customizations
- Simple deployment and configuration
- Detailed granular control over device lockdown
Cons:
- Messaging is unavailable when offline
- Occasional lag for remote locking and unlocking
New Product Updates from Scalefusion
Scalefusion Introduces Apple TV Management
Scalefusion now supports Apple TV management, enabling IT teams to configure and monitor devices. For more information, visit Scalefusion's official site.
SuperOps offers a tailored IT management platform for those seeking endpoint protection, especially appealing to Managed Service Providers (MSPs) and IT teams. It addresses the need for enhanced security and operational efficiency across various devices. By consolidating multiple tools into one solution, SuperOps helps automate workflows and ensure compliance, making it a valuable asset for IT professionals and service providers.
Why I Picked SuperOps
I picked SuperOps for its emphasis on unified endpoint management, which is crucial for maintaining security across diverse devices. With its cross-platform mobile device management, you can ensure seamless oversight and protection regardless of the operating system. Additionally, the platform's automated ticketing system aids in quick incident response, a feature that can significantly reduce downtime and enhance security measures.
SuperOps Key Features
In addition to its standout features, SuperOps offers several other functionalities:
- Software Governance: Manages application discovery, approval, and removal, ensuring compliance and reducing security risks.
- Patch Management: Provides proactive patch management for Windows devices to address vulnerabilities promptly.
- Service Desk Management: Streamlines IT support with automated ticketing and service workflows, improving response times.
- Asset Management: Offers comprehensive visibility and control over IT assets to maintain security and compliance.
SuperOps Integrations
Integrations include Microsoft 365, Google Workspace, Slack, QuickBooks, Xero, FreshBooks, Stripe, PayPal, Zapier, and an API for custom integrations.
Pros and Cons
Pros:
- Strong MSP focused workflow tools
- Cross platform device support
- Unified endpoint and asset management
Cons:
- Patch management focused on Windows
- Not a dedicated antivirus solution
New Product Updates from SuperOps
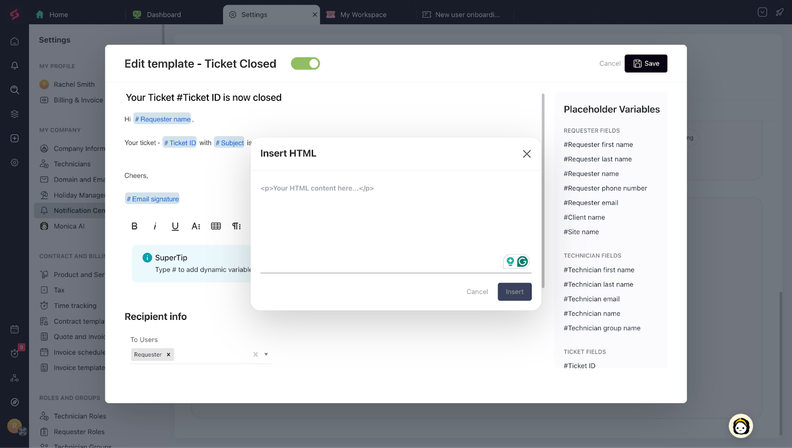
SuperOps Adds HTML Support for Ticket Closure Emails
SuperOps introduces HTML embedding for ticket closure emails. This update allows teams to include custom content such as CSAT survey links and branded elements in resolution emails. For more information, visit SuperOps’ official site.
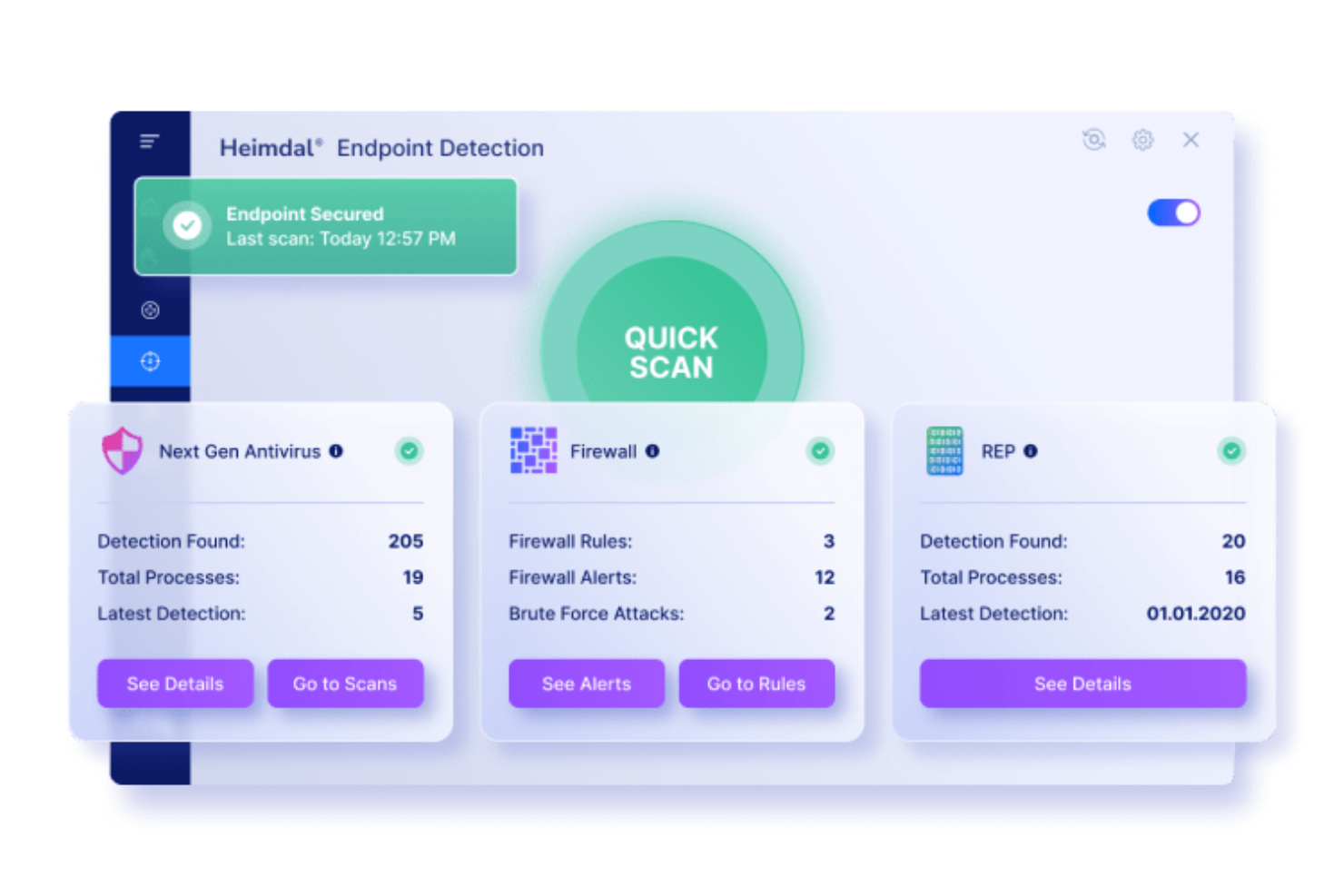
For those seeking a robust endpoint protection solution, Heimdal presents a compelling option tailored to meet the cybersecurity needs of various industries. Designed for businesses in sectors like healthcare, education, and government, Heimdal offers advanced features to protect critical infrastructures and sensitive data. By leveraging machine learning and behavioural analysis, Heimdal addresses the complexities of modern cyber threats, ensuring organizations can operate securely and confidently.
Why I Picked Heimdal
I picked Heimdal as a standout choice for endpoint protection due to its integration of next-gen antivirus and firewall capabilities, which offer real-time threat detection and blocking. The inclusion of ransomware encryption protection ensures data remains uncompromised during attacks, a crucial feature in today's threat landscape. Additionally, Heimdal's Endpoint Detection and Response (EDR) system provides continuous monitoring and quick response to potential threats, making it a reliable ally in maintaining cybersecurity.
Heimdal Key Features
In addition to its robust antivirus and EDR solutions, Heimdal offers several other features that can enhance your endpoint protection strategy:
- Threat Intelligence: This feature provides real-time monitoring and automated threat remediation, crucial for staying ahead of evolving threats.
- Patch and Vulnerability Management: Ensures your systems are always up-to-date, reducing the risk of exploitation from known vulnerabilities.
- Privileged Access Management: Controls and secures access to sensitive systems, mitigating the risk of insider threats.
- Data Loss Prevention (DLP): Protects against unauthorized access and data breaches, safeguarding sensitive information.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
Within endpoint protection and management, HCL BigFix provides a solution focused on security, compliance, and control. Tailored for IT professionals and security teams across various industries, it addresses the critical challenges of maintaining compliance and securing endpoints against vulnerabilities. By offering a unified platform that integrates asset discovery, automated patching, and real-time compliance monitoring, HCL BigFix aims to simplify endpoint management while ensuring your systems remain secure and operational.
Why I Picked HCL BigFix
I picked HCL BigFix for its unique real-time visibility and automated remediation, which are crucial to any endpoint protection strategy. This platform excels with automated patch management, keeping your systems up to date and protected against known vulnerabilities. Additionally, its compliance monitoring tools help you adhere to industry standards without manual oversight. These functionalities make it an appealing choice for organizations that prioritize security and efficiency in managing their IT environments.
HCL BigFix Key Features
In addition to real-time visibility and remediation, HCL BigFix offers:
- AI-Driven Automation: This feature leverages artificial intelligence to automate routine tasks, reducing manual intervention and optimizing IT operations.
- Risk-Based Prioritization: It helps your team focus on the most critical vulnerabilities by assessing and prioritizing risks based on impact and likelihood.
- Unified Workspace Management: This feature provides an integrated view of all endpoints, simplifying management across diverse IT environments.
- Intelligent Runbook Automation: It offers automated workflows for common IT tasks, improving response times and reducing errors.
HCL BigFix Integrations
Integrations include ServiceNow, Forescout, Resilient, Qradar, VMware ESXi, Google Cloud, AWS, Azure, and partnerships with other cloud services.
Pros and Cons
Pros:
- Automates patch management across diverse operating systems
- Effective in risk-based prioritization of vulnerabilities
- Comprehensive asset discovery and inventory capabilities
Cons:
- Can be resource-intensive on older systems
- Some users report challenges with deployment and updates
Best for protecting business data for small-to-medium-sized companies
Bitdefender GravityZone is a cloud-based cybersecurity application for workplace devices. It defends against viruses, malware, and other threats.
Why I picked Bitdefender GravityZone: I picked Bitdefender GravityZone for its strong security and user-friendly management. I felt it was a great choice of cybersecurity tool for small-to-medium-sized businesses due to its ease of use, allowing businesses to focus on core activities without the need for dedicated specialists.
Bitdefender GravityZone Standout Features & Integrations:
Features I believe that stood out include a single, user-friendly platform that supports various devices such as desktops, laptops, and physical devices. It employs machine learning and behavioral analysis for advanced threat detection, and can be used through cloud or on-prem management consoles.
Integrations rely on API keys from Bitdefender GravityZone to operate and include pre-built plug-ins such as Amazon AWS, Microsoft Active Directory, and ConnectWise Automate to give control over agent and agentless devices.
Pros and Cons
Pros:
- Granular control of security settings
- Ability to assign policies for automated deployments with customized settings
- Runs efficiently on low-end computers
Cons:
- Network printers are blocked by default, causing initial difficulties and frustrations.
- Locating quarantined emails can sometimes be challenging
Apex One is an endpoint security solution that proactively protects against vulnerabilities by virtually patching them. It scans for vulnerabilities based on criteria such as severity and Common Vulnerabilities and Exposures (CVE) listing, providing comprehensive protection for platforms and devices.
Why I picked Apex One: I chose Apex One because it utilizes deep scanning to detect malware, viruses, and other threats on all endpoints. It also collects data from millions of application events to identify and track potential risks, ensuring your product and systems are kept up-to-date with the latest cyber threats.
Apex One Standout Features & Integrations:
Features I found beneficial for endpoint protection and scanning include advanced threat techniques like machine learning, as well as noise-canceling methods such as census and safelisting. This combination minimizes false positives and enhances overall security.
Integrations consist of native plug-ins that enhance security visibility and functionality. Some of the popular plug-ins are IBM QRadar, Fortinet, and Splunk.
Pros and Cons
Pros:
- Behavior monitoring module terminates suspicious processes
- External machines receive direct updates from Apex One servers for protection
- After installing Apex One agents, users can perform full scans and review machine logs
Cons:
- Inability to rename endpoint agent names after they're assigned to a system
- The basic reporting feature is okay but could use improvements
Best for malware and attack prevention for small businesses
Symantec Endpoint Protection is an endpoint security solution designed to protect servers and computers from malware, hackers, and other threats. It applies robust technology, including firewall protection, to ensure the safety and integrity of your systems.
Why I picked Symantec Endpoint Protection: I picked Symantec Endpoint Protection because of its comprehensive features and security measures. The price point, features, and ease of use make it a great starting point for small business owners looking to protect their tech stack. The added firewall feature provides an extra layer of protection.
Symantec Endpoint Protection Standout Features & Integrations:
Features that I found helpful in this software are firewall protection, antivirus solutions, and integration with EDR Consoles. These features team up to keep businesses secure by blocking unauthorized access, defending against harmful software, and providing advanced detection and response capabilities.
Integrations that Symantec uses are primarily native and include Unified Endpoint Management (UEM), REST APIs, and Unified Endpoint Management (UEM).
Pros and Cons
Pros:
- Utilizes advanced threat detection mechanisms
- Offers AI guidance for creating and deploying policies
- Provides robust protection against cybersecurity threats
Cons:
- Resource-intensive and may cause slowdowns on older systems
- Merger with Broadcom may cause support challenges for existing customers.
Kaspersky Business is a security software solution that protects organizations with threat detection and preventing, and configurations to reduce attack surfaces. It offers features like File, Mail, and Web Protection, machine learning analysis, and control over device, web, and application usage.
Why I picked Kaspersky Business: I picked Kaspersky Business for its adaptive protection. Its robust suite of tools struck me as a good fit for medium-sized and scaling business. With automated vulnerability and encryption management, you can proactively detect and mitigate threats.
Kaspersky Business Standout Features & Integrations:
Features I liked the most include a multi-layered protection approach based on AI algorithms and threat analysis. Kaspersky's AI automates manual tasks, freeing up your security teams to focus on critical tasks.
Integrations include native plug-ins such as ConnectWise Manage, Autotask, Tigerpaw, and SolarWinds N-central.
Pros and Cons
Pros:
- Background system scans and adjustments enable uninterrupted user focus
- Kaspersky reduces interruptions with fewer pop-ups and security alerts
- The licensing cost of the product is reasonable
Cons:
- Typically detects and organizes new systems but may miss some additions
- May have performance issues with resource-intensive applications
Other Endpoint Security Software
Here are some additional endpoint security software options that didn’t make it onto my shortlist, but are still worth checking out:
- ESET Endpoint Protection
For preventing ransomware attacks
- Avast Small Business Solutions
For protecting small businesses endpoints
- SentinelOne Endpoint Protection
For protecting your customers' endpoints
- CrowdStrike Falcon Endpoint Protection Enterprise
For defending SaaS Cloud endpoints
- Malwarebytes Endpoint Protection
Low-cost option
- Trellix Endpoint Protection Platform
For centralizing your cybersecurity defense in the cloud
- Heimdal Threat Protection Endpoint
For integrated endpoint protection
- Cynet 360
All-in-one endpoint solution
- Scalefusion OneIdP
For zero trust device access
- Cisco Secure Endpoints
For work-from-home endpoints
- Cortex XDR
For extended endpoint monitoring
- ThreatLocker
For granular control over your endpoints
Related Software Reviews
If you still haven't found what you're looking for here, check out these alternative tools that we've tested and evaluated.
- Network Monitoring Software
- Server Monitoring Software
- SD-Wan Solutions
- Infrastructure Monitoring Tools
- Packet Sniffer
- Application Monitoring Tools
Endpoint Security Software Selection Criteria
When selecting the best endpoint security software to include in this list, I considered common buyer needs and pain points like protecting remote devices from malware and minimizing downtime from security breaches. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect and block malware
- Prevent unauthorized access
- Monitor endpoint activity
- Respond to security incidents
- Manage endpoint devices remotely
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- AI-driven threat detection
- Automated response and remediation
- Zero-trust security framework
- Dark web monitoring
- Cybersecurity software
- Behavioral analysis of endpoint activity
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Ease of setup and configuration
- Intuitive user interface
- Low impact on system performance
- Clear and actionable alerts
- Role-based access control
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos and product tours
- Guided setup or onboarding support
- Access to live webinars or workshops
- Documentation and knowledge base quality
- Availability of migration support
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Response time for urgent issues
- Live chat, phone, and email options
- Dedicated account manager
- Proactive threat notifications
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Transparent pricing structure
- Cost compared to similar solutions
- Availability of a free trial or demo
- Contract flexibility
- Volume discounts for large teams
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Reports on system performance and stability
- Satisfaction with threat detection and response
- Comments on ease of use
- Complaints about false positives
- Praise for customer support quality
How to Choose Endpoint Security Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Make sure the software can grow with your business. It should support more devices and users as your company expands without a drop in performance. |
| Integrations | Ensure the software integrates with your existing systems (like SIEM, threat intelligence, and identity management platforms) to avoid compatibility issues. |
| Customizability | Look for software that lets you adjust security policies, alerts, and response actions to match your business's specific needs. |
| Ease of Use | The interface should be intuitive and easy for your team to navigate. Complicated setups or hard-to-find settings can slow down threat response. |
| Budget | Consider the total cost, including licensing fees, per-user costs, and additional charges for support or extra features. |
| Security Safeguards | Look for features like encryption, multi-factor authentication, and real-time threat monitoring to protect sensitive data. |
| Threat Detection and Response | Ensure the software can quickly detect and respond to threats. Real-time alerts and automated responses are ideal. |
| Support and Training | Check if the provider offers training resources, live support, and onboarding help to ensure your team gets up to speed quickly. |
Trends in Endpoint Security Software
In my research, I sourced countless product updates, press releases, and release logs from different endpoint security software vendors. Here are some of the emerging trends I’m keeping an eye on:
- AI-driven threat detection: More vendors are using machine learning and artificial intelligence to identify and respond to threats in real time, improving accuracy and reducing false positives.
- Zero-trust architecture: Vendors are moving toward zero-trust models, where every access request is verified before being granted, even within internal networks.
- Extended detection and response (XDR): XDR software integrate data from multiple security layers (endpoints, networks, cloud) to provide a more unified view of threats.
- Threat hunting: Some solutions now offer proactive threat hunting, where security teams search for hidden threats rather than waiting for alerts.
- Behavioral analysis: More tools are focusing on analyzing user and device behavior to spot unusual activity and prevent insider threats or compromised credentials.
What Is Endpoint Security?
Endpoint security software protects devices like laptops, servers, and mobile phones from threats such as malware, unauthorized access, and data loss. These tools are used by IT teams, security analysts, and system administrators who need to keep devices safe and reduce risk across an organization.
Threat detection, device monitoring, and policy enforcement features help with spotting issues early, keeping devices compliant, and reducing the chance of an attack spreading. Overall, this software helps teams maintain safer devices and a more secure environment.
Features of Endpoint Security Software
When selecting endpoint security software, keep an eye out for the following key features:
- Threat detection: Monitors endpoints for suspicious activity and potential security breaches in real time.
- Incident response: Automatically isolates and addresses security threats to prevent further damage.
- Device control: Allows you to control which devices can access your network to prevent unauthorized access.
- Patch management: Identifies and fixes vulnerabilities by automatically installing security patches.
- Encryption: Solutions such as VPN software protects sensitive data on endpoints by encrypting it both at rest and in transit.
- Application control: Limits which applications can run on your devices to reduce the risk of malware infections.
- Behavioral analysis: Tracks user and device activity to spot unusual patterns that could indicate a security threat.
- Cloud-based management: Lets you monitor and control endpoint security from a centralized dashboard.
- Threat intelligence: Uses global threat databases to identify and protect against emerging threats.
- Multi-factor authentication: Adds an extra layer of security by requiring additional verification beyond just passwords.
Benefits of Endpoint Security Software
Implementing endpoint security software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved threat detection: Identifies and responds to malware, ransomware, and other threats in real time, reducing the risk of data breaches.
- Better control: Allows you to manage and monitor all endpoints from a single platform, simplifying security management.
- Reduced downtime: Quick threat response minimizes system disruptions, helping your team stay productive.
- Compliance support: Helps you meet industry security standards by ensuring all endpoints are properly secured and monitored.
- Lower risk of data loss: Encryption and backup features protect sensitive data even if a device is compromised.
- Enhanced device protection: Controls which devices can access your network, blocking unauthorized or potentially risky connections.
- Scalability: Expands easily as your business grows, allowing you to add new endpoints without sacrificing protection.
Costs and Pricing of Endpoint Security Software
Selecting endpoint security software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in endpoint security software solutions:
Plan Comparison Table for Endpoint Security Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited device coverage, and minimal reporting. |
| Personal Plan | $5-$25/user/month | Real-time threat monitoring, malware protection, and email security software. |
| Business Plan | $25-$75/user/month | Endpoint detection and response tools (EDR tools), advanced threat intelligence, policy enforcement, and reporting. |
| Enterprise Plan | $75-$150/user/month | AI-based threat detection, 24/7 support, behavioral analysis, custom reporting, and network integration. |
Endpoint Security Software FAQs
Here are some answers to common questions about endpoint security software:
How does endpoint security software differ from traditional antivirus programs?
Can endpoint security software protect against zero-day attacks?
How does endpoint security software integrate with existing IT infrastructure?
What factors should I consider when choosing an endpoint security solution?
How does endpoint security software handle data privacy concerns?
Is endpoint security software suitable for small businesses?
What's Next?
If you're in the process of researching endpoint security software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.