Best XDR Software Shortlist
In today's fast-paced tech environment, managing cybersecurity threats is a constant challenge. You need tools that can keep up with evolving threats and help your team respond effectively. That's where XDR software comes in.
I've spent time testing and reviewing various XDR solutions to bring you an unbiased look at the best options available. In my experience, these tools can significantly improve your threat detection and response capabilities.
In this article, you'll find a detailed analysis of top XDR software, focusing on features, usability, and how they can address your specific needs. My goal is to help you choose the right solution that fits your team's requirements and enhances your cybersecurity strategy.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best XDR Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for advanced AI/ML capabilities | Free trial + free demo available | Pricing upon request | Website | |
| 2 | Best for network-based threat detection | Not available | Pricing upon request | Website | |
| 3 | Best for large-scale threat management and forensic analysis | Free demo available | Pricing upon request | Website | |
| 4 | Best for Azure-based environments needing threat protection | Not available | From $15/user/month (billed annually) | Website | |
| 5 | Best for advanced endpoint protection with deep learning technology | Not available | From $20/user/month | Website | |
| 6 | Best for risk visibility and correlated threat detection across different security layers | Not available | From $25/user/month (billed annually) | Website | |
| 7 | Best for multi-cloud visibility and security analytics | Free demo available | Pricing upon request | Website | |
| 8 | Best for unified threat detection and response across networks, clouds, and endpoints | Free demo available | Pricing upon request | Website | |
| 9 | Best for AI-driven protection against malware and ransomware | Not available | From $12/user/month (billed annually) | Website | |
| 10 | Best for incident response teams requiring user behavior analytics | Not available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best XDR Software Reviews
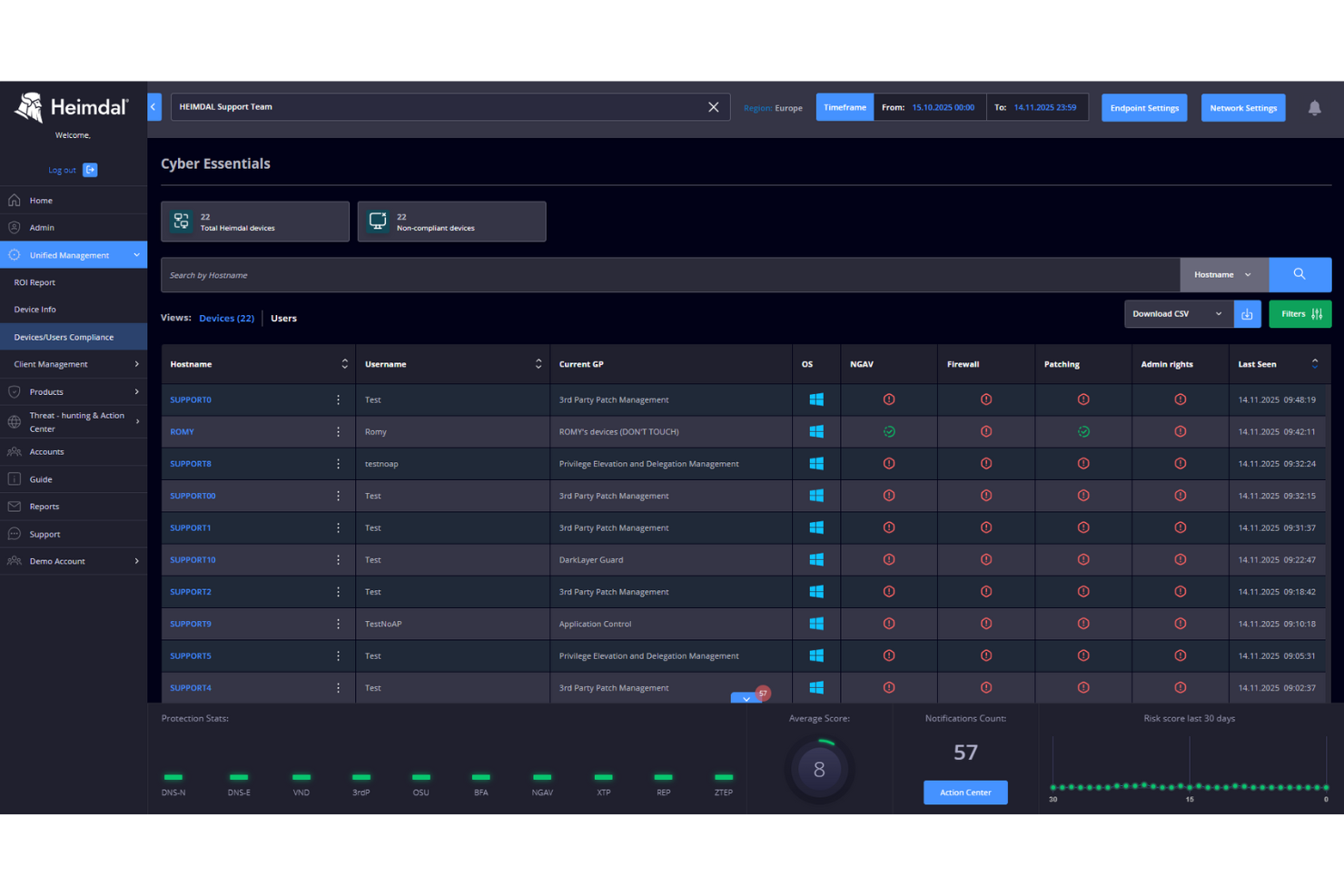
Heimdal's Extended Detection and Response (XDR) solution offers a comprehensive approach to cybersecurity, integrating network security, endpoint protection, threat hunting, and vulnerability management. This makes it particularly appealing to organizations in industries such as healthcare, education, and government that require robust protection against sophisticated cyber threats. By providing a unified platform that consolidates multiple security features, Heimdal addresses the challenge of managing diverse security tools, offering enhanced visibility and faster threat detection and response across IT infrastructures.
Why I Picked Heimdal
I picked Heimdal for its ability to integrate threat detection and response across multiple security domains, which is crucial for XDR software. Heimdal's platform stands out with its advanced AI/ML capabilities that enhance threat detection accuracy and automate responses, reducing the workload on security teams. Additionally, its network security feature provides comprehensive visibility and protection across IT infrastructures, a key requirement for any XDR solution. These features, combined with seamless integration with existing systems, make Heimdal a compelling choice for organizations seeking enhanced cybersecurity measures.
Heimdal Key Features
In addition to its standout features, Heimdal offers several other capabilities that cater to diverse security needs:
- Threat Hunting: Enables proactive identification and mitigation of threats before they cause harm.
- Vulnerability Management: Continuously scans and identifies vulnerabilities within your network to prevent potential breaches.
- Email Protection: Guards against email-based threats, including phishing and malware, ensuring secure communication channels.
- Unified Endpoint Management: Provides a centralized dashboard to manage and monitor all endpoints, improving operational efficiency.
Heimdal Integrations
Integrations include ConnectWise RMM, Autotask PSA, and Heimdal offers API capabilities for custom integrations.
Pros and Cons
Pros:
- Real-time automated threat response
- AI-driven threat detection capabilities
- Unified XDR security platform
Cons:
- May require configuration time
- Pricing available upon request
ExtraHop is a network detection and response (NDR) platform that focuses on the security of your network traffic. The tool offers real-time threat detection and automatic responses to abnormalities, making it ideal for network-based threat detection.
Why I Picked ExtraHop:
I chose ExtraHop because of its advanced machine-learning capabilities, allowing for an in-depth network traffic analysis. Its ability to automatically respond to detected threats also sets it apart from many other security tools. ExtraHop is "best for network-based threat detection" as it excels in uncovering hidden dangers and providing security insights within network traffic.
Standout Features & Integrations:
ExtraHop offers advanced threat detection with real-time insights, machine learning-driven anomaly detection, and automated response capabilities. Its features also include comprehensive visibility, which aids in forensic investigations and compliance. In terms of integrations, ExtraHop works well with a range of platforms, including ServiceNow, Phantom, and Ansible, enhancing its ability to automate responses.
Pros and Cons
Pros:
- Effective integrations with other platforms
- Comprehensive visibility into network traffic
- Advanced threat detection capabilities
Cons:
- Lacks support for non-network endpoints
- May require technical expertise to fully utilize
- Pricing information is not publicly available
Best for large-scale threat management and forensic analysis
IBM Security QRadar SIEM is a security information and event management system that consolidates log events and network flow data from thousands of devices, endpoints, and applications distributed throughout a network. With its ability to correlate this information and identify potential threats, QRadar is best suited for large-scale threat management and forensic analysis.
Why I Picked IBM Security QRadar SIEM:
I selected IBM Security QRadar SIEM for its comprehensive threat detection and response capabilities, especially for large-scale environments. What sets QRadar apart is its ability to gather and correlate data from various sources, making it efficient for forensic analysis. Given its feature-rich platform and scalability, I believe QRadar is best for large-scale threat management and forensic analysis.
Standout Features & Integrations:
QRadar offers advanced threat detection, AI-powered insights, and extensive forensics capabilities. Its incident overview feature visually represents incidents, which can be invaluable during threat hunting. The system integrates with numerous IBM solutions and other third-party applications, broadening its reach across different facets of a network.
Pros and Cons
Pros:
- Extensive integrations with IBM solutions and other third-party applications
- Scalable to accommodate large-scale environments
- Robust threat detection and response capabilities
Cons:
- The user interface may be complex for some users
- May require technical expertise to operate efficiently
- Pricing information isn't publicly available
Best for Azure-based environments needing threat protection
Microsoft Defender for Cloud is a security management tool that provides threat protection for workloads running in Azure, other clouds, and on-premises. It is designed for Azure environments and brings robust threat protection capabilities to these specific workspaces, making it ideal for such environments.
Why I Picked Microsoft Defender for Cloud:
In selecting Microsoft Defender for Cloud, I considered its native Azure integration and comprehensive threat protection features. This tool's ability to offer security management for Azure-based environments differentiates it. Therefore, it is the best option for Azure-based setups that require effective threat protection.
Standout Features & Integrations:
Microsoft Defender for Cloud offers continuous security assessment, advanced threat protection, and just-in-time access. Importantly, it natively integrates with Azure services, providing a unified security management experience.
Pros and Cons
Pros:
- Continuous security assessment capability
- Comprehensive threat protection
- Native integration with Azure services
Cons:
- As a robust tool, it could have a steep learning curve for some users
- Pricing could be high for smaller teams or startups
- The tool is tailored to Azure, so it may not be as effective in non-Azure environments
Best for advanced endpoint protection with deep learning technology
Sophos Intercept X: Next-Gen Endpoint is a top-tier security tool leveraging deep learning technology for proactive threat detection and response. With its focus on utilizing advanced technologies for threat protection, it is particularly suitable for organizations needing sophisticated endpoint protection measures.
Why I Picked Sophos Intercept X: Next-Gen Endpoint:
I picked Sophos Intercept X for its remarkable utilization of deep learning in endpoint security. Its unique approach to endpoint protection, which involves the application of cutting-edge artificial intelligence technologies, set it apart in my selection process. Hence, I consider it to be the best for those in need of advanced endpoint protection powered by deep learning technology.
Standout Features & Integrations:
Sophos Intercept X provides critical features like exploit prevention, active adversary mitigation, and deep learning malware detection. It also integrates well with Sophos' suite of products and services, enabling a comprehensive security posture for organizations.
Pros and Cons
Pros:
- Excellent integration with other Sophos products and services
- Comprehensive suite of endpoint protection features
- Advanced deep learning technology for proactive threat detection
Cons:
- While its deep learning approach is powerful, it might be overkill for businesses with simpler security needs
- The tool's advanced features could have a learning curve for some users
- Pricing might be a bit steep for smaller businesses
Best for risk visibility and correlated threat detection across different security layers
Trend Micro Vision One (XDR) offers extended detection and response solutions, providing high visibility and coordinated threat detection across various security layers. Given its ability to provide deep insight into potential risks and its excellent correlation capabilities, it fits organizations needing comprehensive risk visibility and threat correlation.
Why I Picked Trend Micro Vision One (XDR):
I selected Trend Micro Vision One due to its robust risk visibility and correlation features. It provides security insights across different layers, making it stand out from the pack. Therefore, it's best for those seeking to enhance their ability to detect correlated threats across different security layers.
Standout Features & Integrations:
Trend Micro Vision One offers advanced features like risk insight, prioritized alerts, and automated security operations. It integrates well with various platforms, including cloud infrastructures like AWS and Azure and endpoint platforms like Microsoft Defender.
Pros and Cons
Pros:
- Advanced features like automated security operations
- Rich integration options with various platforms
- Excellent risk visibility and correlation of threat detection
Cons:
- Lack of month-to-month billing option may not suit all businesses
- Some users might find the platform complex due to its extensive features
- The cost might be high for smaller organizations
Wiz is a cloud security platform that delivers full-stack visibility and comprehensive security analytics across multiple cloud infrastructures. It aims to simplify cloud security by providing insights and identifying vulnerabilities in real-time, making it an optimal choice for teams requiring multi-cloud visibility and security analytics.
Why I Picked Wiz:
I picked Wiz for its innovative approach to multi-cloud visibility and security analytics. Its ability to provide deep insights into complex multi-cloud infrastructures sets it apart from many other tools on the market. In my opinion, Wiz is best suited for multi-cloud visibility and security analytics due to its robust security analysis capabilities and ease of use, especially when dealing with complex cloud architectures.
Standout Features & Integrations:
Wiz offers several standout features, including full-stack visibility, real-time vulnerability detection, and advanced security analytics. These features ensure a comprehensive and detailed view of the security landscape across multiple clouds. Wiz also integrates with major cloud platforms like AWS, Azure, and Google Cloud, along with many standard DevOps tools, providing an adaptable solution for diverse IT environments.
Pros and Cons
Pros:
- Integration with major cloud and DevOps tools
- Real-time vulnerability detection
- Comprehensive visibility across multiple clouds
Cons:
- As a focused tool, it may not cover all aspects of cybersecurity outside cloud environments
- May require a certain level of expertise to maximize its features
- Pricing details are not openly available
Best for unified threat detection and response across networks, clouds, and endpoints
Cortex XDR is an extended detection and response platform that provides a unified approach to threat detection and response across networks, clouds, and endpoints. This cohesive security tool enables organizations to correlate data from diverse sources to detect complex threats, which aligns with its positioning as best for unified threat detection and response.
Why I Picked Cortex XDR:
I selected Cortex XDR for its integrated approach to security, capable of unifying threat detection and response across various environments. This comprehensive capability differentiates Cortex XDR from many security tools focusing on specific domains. I believe Cortex XDR is "best for unified threat detection and response across networks, clouds, and endpoints" due to its ability to correlate data across these sources, allowing for a holistic view of the organization's security posture.
Standout Features & Integrations:
Cortex XDR offers advanced features such as behavioral threat detection, automated security operations, and integrated case management. These features make it highly capable of detecting and responding to threats across diverse environments. As for integrations, Cortex XDR can be incorporated with a wide range of Palo Alto Networks products and other third-party solutions, which helps to enhance its security coverage.
Pros and Cons
Pros:
- Comprehensive integrations with Palo Alto Networks products and other solutions
- Advanced behavioral threat detection capabilities
- Unified threat detection and response across various environments
Cons:
- Can be complex to deploy in large or heterogeneous environments
- May have a steep learning curve for users new to the platform
- No publicly available pricing information
Best for AI-driven protection against malware and ransomware
CrowdStrike Falcon Endpoint Protection Platform is a cloud-native solution designed to stop breaches by preventing and responding to all types of attacks. It employs AI to provide superior malware and ransomware protection, hence, it is the top choice for AI-driven protection against such threats.
Why I Picked CrowdStrike Falcon Endpoint Protection Platform:
I chose CrowdStrike Falcon because of its unique combination of technology, threat intelligence, and flexible response options. It stands out due to its AI capabilities, which enable superior malware and ransomware detection and prevention. Given these features, the tool is particularly adept at providing AI-driven protection against malware and ransomware.
Standout Features & Integrations:
Falcon offers features like AI-powered malware and ransomware protection, threat hunting, and comprehensive visibility across the IT environment. Its cloud-native architecture allows it to integrate well with other cloud-based systems and provides extensive APIs for custom integrations.
Pros and Cons
Pros:
- Cloud-native solution offering scalability and ease of integration
- Extensive visibility across the IT environment
- Advanced AI capabilities for malware and ransomware protection
Cons:
- Some users have reported false positives with its detection system
- May require technical expertise to fully leverage its features
- Pricing information isn't publicly available
InsightIDR is a security information and event management (SIEM) solution that identifies and investigates suspicious user behavior. It offers robust user behavior analytics, incident detection, and response tools, positioning it perfectly for incident response teams.
Why I Picked InsightIDR:
I picked InsightIDR because it excels in user behavior analytics, which is crucial in identifying insider threats and compromised accounts. Its comprehensive incident detection and response capabilities further differentiate it from other tools. Therefore, I determined InsightIDR is "best for incident response teams requiring user behavior analytics" because it enables teams to identify and respond to security incidents quickly.
Standout Features & Integrations:
InsightIDR offers automated detection and response capabilities, along with detailed investigation timelines, which are essential for managing incidents effectively. It also provides built-in user behavior analytics that helps identify abnormal user activity. InsightIDR integrates well with other Rapid7 solutions and popular third-party platforms, like AWS, Azure, and Cisco, to provide comprehensive coverage across diverse IT environments.
Pros and Cons
Pros:
- Broad range of integrations
- Comprehensive incident detection and response capabilities
- Advanced user behavior analytics
Cons:
- Some users report the need for frequent rule adjustments to avoid false positives
- Could be complex to set up for less tech-savvy users
- Pricing is not publicly disclosed
Other XDR Software
Below is a list of additional XDR software that I shortlisted but did not make it to the top. Definitely worth checking them out.
- SentinelOne Singularity
For autonomous endpoint protection against all attack vectors
- Microsoft 365 Defender
For comprehensive protection across Microsoft 365 apps and services
- Cynet 360 AutoXDR
For automated threat discovery and response
- Bitdefender GravityZone
Good for small businesses needing robust security
- LogRhythm SIEM
Good for detecting and responding to threats in real-time
- Prisma Cloud
Good for security and compliance across the entire DevOps lifecycle
- Sophos Cloud Optix
Good for visibility and threat response in cloud environments
- CYREBRO
Good for centralized and simplified security operations
- Cybereason Defense Platform
Good for proactive protection against cyber threats
- Armor Anywhere
Good for scalable and flexible cloud security
- B1 Platform by CloudCover
Good for optimizing cloud costs and usage
- NetWitness Platform XDR
Good for comprehensive threat detection and response
- VMware Carbon Black Cloud
Good for cloud-native endpoint protection
- Qomplx
Good for managing cybersecurity, risk, and insurance
- Symantec Storage Protection
Good for safeguarding cloud storage resources
- ContraForce
Good for leveraging machine learning in cyber threat detection
- Cisco SecureX
Good for integrated security across all defenses
Other XDR Software - Related Reviews
XDR Software Selection Criteria
When selecting the best XDR software to include in this list, I considered common buyer needs and pain points like integration with existing security tools and ease of deployment. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect advanced threats
- Automate threat response
- Integrate with existing SIEM tools
- Provide endpoint security
- Monitor network traffic
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- AI-driven threat analysis
- Cross-platform integration
- Real-time analytics dashboard
- Customizable reporting
- Cloud-native architecture
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Minimal learning curve
- Customizable settings
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Webinars and workshops
- Chatbot support
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multichannel support
- Response time
- Knowledgeable staff
- Availability of FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Tiered pricing options
- Free trial availability
- Feature set vs. cost
- Discounts for long-term contracts
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction rating
- Commonly mentioned pros
- Commonly mentioned cons
- Frequency of updates
- Quality of support feedback
How to Choose XDR Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your business? Consider your future needs and ensure the tool can handle increased data volume and user numbers. |
| Integrations | Does it work with your existing tools? Check for compatibility with current security systems and cloud services to avoid operational disruptions. |
| Customizability | Can you tailor it to your needs? Look for flexible settings that let you adjust the software to fit your workflows and reporting requirements. |
| Ease of use | Is it user-friendly for your team? Evaluate the interface and navigation to ensure it minimizes training time and boosts productivity. |
| Implementation and onboarding | How smooth is the setup process? Understand the time and resources needed for deployment and training, and look for support options to assist. |
| Cost | Does it fit your budget? Compare pricing tiers, hidden fees, and long-term costs. Consider ROI and whether a free trial is available. |
| Security safeguards | Are there strong protections? Look for features like encryption and access controls to secure sensitive data and comply with regulations. |
| Support availability | Will you get help when needed? Check for 24/7 support options and evaluate the quality and responsiveness of the vendor's customer service. |
What Is XDR Software?
Extended Detection and Response (XDR) software is a security technology designed to provide unified threat detection and response across various network endpoints, servers, and cloud workloads. Typically adopted by enterprise security teams, XDR solutions help identify, prevent, and respond to various security threats.
Extended Detection and Response (XDR) software is an integrated security platform that consolidates and correlates data from multiple sources, including firewall and antivirus systems, to prevent, detect, and respond to cyber-attacks. The primary value of an XDR platform lies in its ability to cover a broader attack surface, manage services, integrate various network security tools, and provide managed detection and response services (MDR).
Features
When selecting XDR software, keep an eye out for the following key features:
- Advanced analytics: Provides deep insights into threat patterns, helping teams identify and respond to threats quickly.
- Automated response: Enables automatic threat mitigation actions, reducing the time and effort required from security teams.
- Integration capabilities: Allows seamless connection with existing digital forensics software and IT management tools for a unified approach.
- Real-time monitoring: Offers continuous monitoring of network and endpoint activities to detect threats as they occur.
- Customizable reporting: Lets users tailor reports to specific needs, providing clear and actionable insights.
- AI-driven threat detection: Utilizes artificial intelligence to identify complex threats that traditional systems might miss.
- Endpoint security: Protects devices across the network, ensuring comprehensive security coverage.
- User-friendly interface: Ensures ease of use and quick adoption by security teams, minimizing training time.
- Scalability: Supports growth in data volume and user numbers, ensuring the tool remains effective as your organization expands.
- Cloud-native architecture: Provides flexibility and scalability, allowing for easy deployment and management in cloud environments.
Benefits
Implementing XDR software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved threat detection: With advanced analytics and AI-driven capabilities, XDR software helps identify threats that might go unnoticed.
- Faster response times: Automated response features allow for quick mitigation of threats, reducing potential damage.
- Enhanced security integration: Seamless integration with existing tools provides a unified security approach, simplifying management.
- Comprehensive monitoring: Real-time monitoring ensures threats are detected and addressed as they occur, minimizing risk.
- Scalability for growth: The software's ability to scale with your business means it remains effective as your organization expands.
- Cost efficiency: By consolidating multiple security tools into one platform, XDR software can reduce overall security expenses.
- User-friendly experience: A straightforward interface ensures your team can quickly adapt and make the most of the software's capabilities.
Costs & Pricing
Selecting XDR software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in XDR software solutions:
Plan Comparison Table for XDR Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited analytics, and minimal support. |
| Personal Plan | $10-$30/user/month | Advanced analytics, automated alerts, and basic integrations. |
| Business Plan | $40-$70/user/month | Full integration capabilities, real-time monitoring, and customizable reporting. |
| Enterprise Plan | $80-$150/user/month | AI-driven threat detection, comprehensive support, and scalable architecture. |
XDR Software FAQs
Here are some answers to common questions about XDR software:
How does XDR software integrate with existing systems?
XDR software often provides APIs and pre-built connectors to integrate smoothly with your current security tools. You’ll want to ensure compatibility with your SIEM, firewalls, and endpoint solutions to maximize its effectiveness and reduce manual work.
What are the deployment options for XDR software?
XDR solutions can be deployed on-premises, in the cloud, or as a hybrid model. Consider your infrastructure, security policies, and compliance requirements when choosing the deployment method that best suits your needs.
How does XDR handle data privacy and compliance?
XDR software should include features that meet data protection regulations like GDPR or CCPA. Look for tools that offer data encryption, access controls, and compliance reporting to ensure your organization meets legal requirements.
Can XDR software support remote work environments?
Yes, many XDR tools are designed to secure remote and distributed workforces. They provide visibility into off-network activities and protect endpoints used by remote employees, helping maintain security across various locations.
How customizable are XDR alerts and reports?
Most XDR solutions allow you to customize alerts and reports to fit your specific needs. This flexibility helps you focus on the most relevant threats and generate reports that provide actionable insights for your team.
What kind of support and resources are typically available?
XDR vendors often offer 24/7 support, documentation, and training resources. Check if they provide live chat, phone support, and access to a knowledge base to help your team quickly resolve any issues that arise.
What’s Next?
If you're in the process of researching XDR software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.