Cybersecurity protects computer systems, networks, and data from digital attacks, unauthorized access, and damage. Specific cybersecurity threats include various malicious activities aimed at compromising data integrity, privacy, and the functionality of digital systems, such as hacking, viruses, and phishing attacks.
To tackle these challenges, CTOs must leverage cybersecurity tools to effectively detect, prevent, and mitigate threats. From endpoint security software to advanced threat intelligence platforms, the right tools are essential in safeguarding systems, ensuring data privacy, and maintaining trust in today's digital landscape.
Cybersecurity threats are everywhere, and the rapid growth of SaaS, cloud services, and automated critical infrastructure has transformed what was previously a nuisance into a significant threat.
CTOs must protect their tech. No matter the industry or how at-risk you feel, you must anticipate, intercept, and respond to an evolving cybercrime environment.
What Are Cybersecurity Threats?
A cybersecurity threat is any intentional assault on a computer system by malicious actors. These threats take many forms, from simple attempts at unauthorized access by a lone actor to massive multi-national assaults on security systems by multiple vectors, including nation-states and non-state organizations.
Cloud systems are frequently targeted in these attacks, so knowing what you're up against is worth knowing.
According to Taylor, in the past 2-3 years, attackers have shifted from mass, opportunistic phishing to highly targeted, socially engineered attacks.
"They’re using AI to craft more believable emails, mimic executive behavior, and even manipulate voice and video," he states. "The perimeter is no longer the firewall, it's the end user, or human firewall."
"To adapt, organizations must move beyond checkbox training. They need continuous, engaging, and positive reinforcement education - everyone needs coaching, not blame."
Types of Cybersecurity Threats
Cybersecurity threats come in many forms, each with its sneaky way of wreaking havoc. Let's break them down:
- Phishing Attacks: These crafty emails or messages masquerading as legitimate often trick people into handing over sensitive information. They're like digital con artists.
- Malware: This broad category includes viruses, worms, and ransomware. Think of malware as the unwanted intruder that sneaks into your system to steal, damage, or take control.
- Ransomware: A particularly nasty piece of malware. It locks you out of your data and demands payment for its release. It's like a data kidnapper.
- DDoS Attacks (Distributed Denial of Service): Imagine a flood of traffic overwhelming your system, making it impossible to function. That's what a DDoS attack does – it's a digital traffic jam with malicious intent.
- SQL Injection: Here, attackers exploit a database vulnerability to access hidden data, similar to picking a digital lock.
- Zero-Day Exploits: These are attacks on software vulnerabilities unknown to the vendor. It's like someone finding and exploiting a secret passage before it can be sealed.
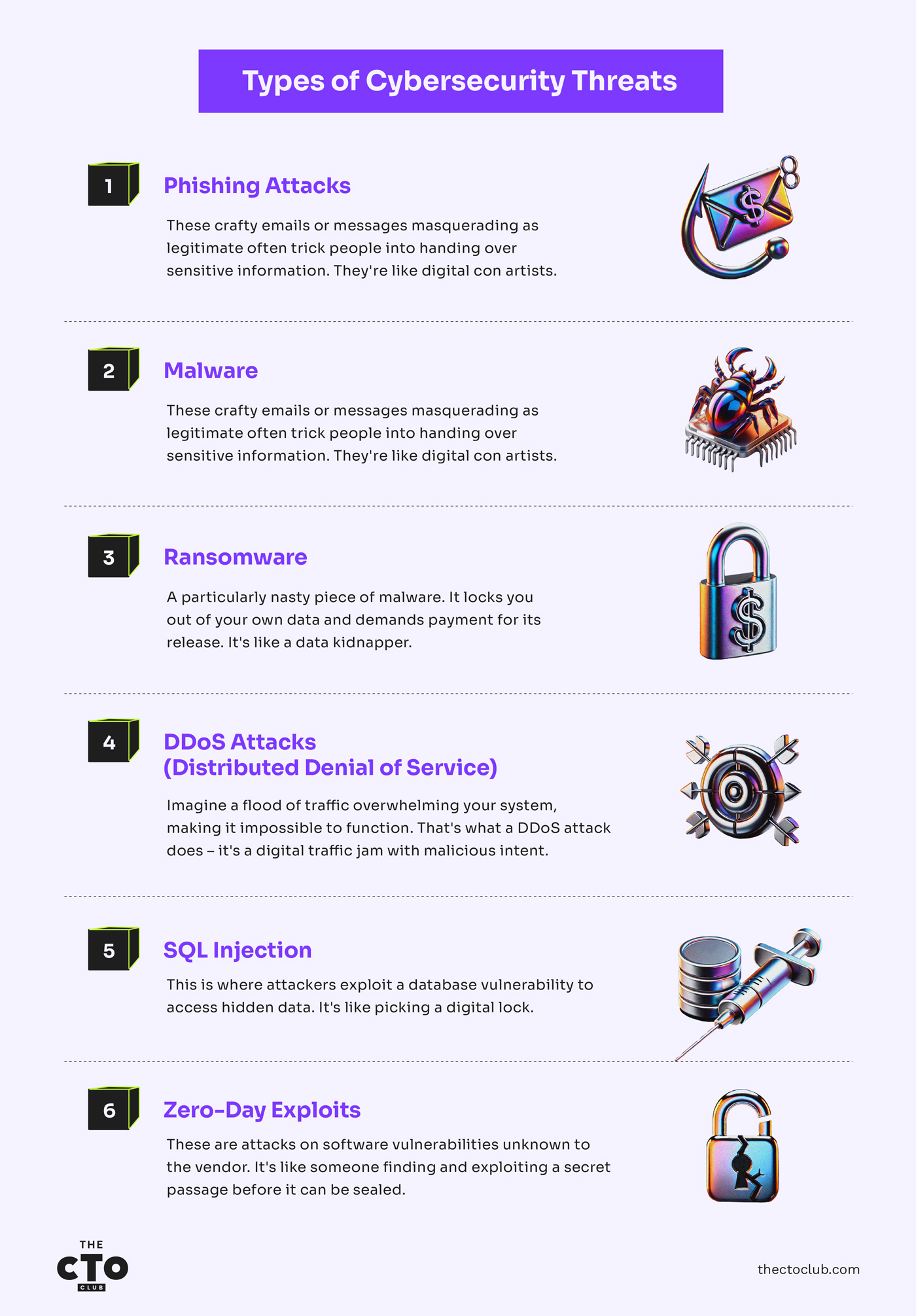
Each threat poses a real risk, and they're constantly evolving. Cybersecurity isn't just an IT issue; it's an essential part of our digital lives. The urgency to protect against these threats has never been greater. Staying informed and vigilant is vital.
Man-in-the-Middle Attacks
Let's be honest – most of us think we understand Man-in-the-Middle attacks. "Oh yeah, someone gets between two communicating parties, I get it."
But after cleaning up the aftermath of these attacks at three different companies, I can tell you there's a world of difference between understanding the concept and recognizing when you're under attack.
What a MitM Attack Looks Like (Not What Your Security Team Thinks)
Forget the textbook definition for a minute. Here's what a Man-in-the-Middle attack actually looks like in the real world:
- It's not obvious: When one of my clients was hit, their traffic was intercepted for 47 days before anyone noticed. No alarms, no noticeable performance issues, just subtle irregularities in transaction data that most monitoring systems missed completely.
- It happens where you least expect it: Everyone focuses on external communications. However, I've seen devastating MitM attacks between internal systems – server to server, app to database – where teams often skip the security controls they'd apply externally.
- It's rarely random. The "spray and pray" days are gone. Today's attackers have been conducting reconnaissance for weeks, identifying high-value communication channels before they strike. They're looking for your payment processing systems, authentication servers, and API gateways.
The mechanics are straightforward but brutally effective:
- The attacker positions themselves between two parties – user-to-app, server-to-server, or device-to-network.
- They establish separate encrypted connections with each side, making both think they're talking directly to each other.
- They decrypt, read, potentially modify, and then re-encrypt the traffic before passing it along.
- Both sides believe they have a secure, private connection when they don't.
The scariest part? A well-executed MitM attack looks precisely like regular traffic to most security tools. I've seen SOCs with million-dollar security stacks completely miss them.
Attack Techniques I've Seen Succeed (Despite "Adequate" Security)
After investigating dozens of these incidents, here are the techniques that consistently bypass even well-funded security programs:
Wi-Fi Eavesdropping: Still Ridiculously Effective
I know, it sounds like Security 101, but it works:
- The airport executive lounge trap: One of my manufacturing clients had their CEO's credentials stolen at an airport lounge. The attacker set up a rogue access point named "Executive_Lounge_Premium" with a better signal than the real network. Within 20 minutes, the CEO connected and unknowingly sent all traffic through the attacker's laptop. The company discovered unusual wire transfers totaling over $1 million three weeks later.
- The hotel network "upgrade": Another common technique involves attackers posing as IT support, claiming they're "upgrading the hotel network" and providing new (malicious) connection details. Your team thinks they're getting better service when routing traffic through an attacker's system.
That said, Craig Taylor, a CISSP-certified cybersecurity professional and Co-Founder of CyberHoot, says the most common misconception is that Man-in-the-Middle (MITM) attacks are only a concern on public Wi-Fi or in unencrypted environments.
"In reality, attackers can exploit poor certificate management, misconfigured VPNs, and even compromised devices inside trusted networks," Taylor adds. "CTOs often overlook internal threats and assume encryption alone is enough".
DNS Spoofing: Redirecting Your Digital Roadmap
DNS is the internet's navigation system, and when compromised, it sends you to destinations that look identical to what you expected but are actually under an attacker's control:
- The silent redirect: A healthcare organization I worked with had its DNS compromised for months. The attacker only redirected specific high-value domains—its payment processor, EHR system, and email portal. Everything looked perfectly normal to users, except all their credentials were being harvested.
- The targeted injection: More sophisticated attackers don't hijack all DNS traffic – they wait for specific high-value queries (like banking websites or payment systems) before injecting fake responses. This selective approach makes detection significantly harder.
The "Session Sidejack" – A Cybersecurity Threat Nobody Talks About
This technique targets active sessions rather than initial connections:
- Cookie theft via unprotected Wi-Fi: An attacker on the same network can steal session cookies from non-HTTPS connections, allowing them to hijack active sessions without login credentials.
- The cross-site timing attack: I've seen attackers use tiny timing differences in responses to determine if users are logged into specific services, then use this information to launch targeted sidejacking attacks.
In one retail company I advised, an attacker stole the session cookies of an authenticated admin and proceeded to exfiltrate customer data for weeks – all while the admin was still actively using the system with no indication anything was wrong.
Business Email Compromise: The Most Profitable MitM
Email-based MitM attacks have exploded in sophistication:
- The invoice modification: Attackers monitor email exchanges between businesses, then intercept and modify PDF invoices to change payment details. I've seen companies lose millions because nobody called to verify the sudden "banking changes" mentioned in an email.
- The lookalike domain trick: One construction company I worked with lost $927,000 when an attacker registered "constructioncorp-invoices.com" (their actual domain was "constructioncorp.com") and started sending emails from it. The subtle difference went unnoticed for weeks.
Supply Chain Cybersecurity Threats
I've watched too many CTOs focus obsessively on hardening their systems while completely ignoring a gaping vulnerability – the software and services flowing into their environment from "trusted" vendors.
Let me be blunt: your supply chain is likely your weakest link, and attackers know it.
What Supply Chain Cybersecurity Threats Look Like
Forget the abstract concept. Here's the reality of modern supply chain attacks:
- The attack you never see coming: When a major logistics company I advised was breached, it wasn't through their heavily defended perimeter—it was through a routine update from a trusted inventory management system. The update was digitally signed, passed all security checks, and was automatically deployed across 400+ servers. The backdoor lived undetected for 143 days.
- The perfect Trojan horse: Supply chain attacks are devastatingly effective because they piggyback on legitimate software from trusted vendors. They run with the same privileges and access as the trusted software itself. I've seen malicious code deployed by your admins who were "doing routine maintenance."
- The blast radius is enormous: When one financial services vendor was compromised through their build pipeline, the malicious code was distributed to 734 banks and credit unions simultaneously. This isn't one system being compromised – it's hundreds or thousands at once.
SaaS companies face considerable third-party risk due to their reliance on partners, contractors, and subcontractors who provide essential services but may lack comparable cybersecurity standards and practices.
"This is especially the case for more boutique organizations, but can also be accounted for by larger entities," states Jeff Le, the managing principal at 100 Mile Strategies and a Visiting Fellow at the National Security Institute. "SaaS companies may not subject their partners to the same level of scrutiny, inventorying, or training rigor as they would their internal business partners and stakeholders."
Governments worldwide face similar challenges, often relying on basic tools like Excel sheets and static lists to track their partners. Effective oversight requires ongoing monitoring beyond internal operations, including a proactive assessment of third-party entities.
"Pen testing and red teaming are helpful, but there needs to be more beyond point-in-time assessments," Le adds.
Why Traditional Security Falls Flat
Your standard security playbook utterly fails against supply chain attacks:
- Signature verification is worthless: The compromised updates are digitally signed by the legitimate vendor using their actual certificates, and your security tools see them as 100% legitimate.
- Behavior monitoring misses it: Since the malicious code runs within a trusted application, its behavior often blends with legitimate activities.
- Vendor assessments give false confidence: I've seen companies with perfect security audit scores become the source of massive supply chain compromises just weeks later.
The SolarWinds attack wasn't an anomaly but a preview of the new normal. Most CTOs I talk to are still wholly unprepared for this reality.
Cybersecurity Threat Defense
Defending against supply chain attacks requires a fundamentally different approach, but it doesn't mean abandoning your vendors or building everything in-house:
- My unpopular opinion: Zero Trust for updates: Even signed updates from trusted vendors should be treated as potentially compromised. One healthcare organization I worked with implemented a 72-hour staging policy for all vendor updates in an isolated environment before wider deployment. Within six months, they caught two compromised updates that would have otherwise sailed through.
- Software bills of materials (SBOMs) are non-negotiable: Start demanding detailed SBOMs from every vendor. When one manufacturing client made this mandatory, they discovered 40% of their vendors couldn't even produce a comprehensive list of the components in their software. That's a red flag you can't ignore.
- Runtime application self-protection (RASP): Implement solutions that detect and block suspicious behaviors regardless of the source. This provides defense even when trusted applications go rogue.
- Vendor segmentation that actually works: Create network segments that limit what your vendors can access, even when their software is functioning as designed. One retailer I advised limited their point-of-sale vendor's software to only accessing what it needed. The attack was contained to a small subset of systems when the vendor was later compromised.
Supply chain attacks aren't going away – they're increasing in frequency and sophistication. But with the right approach, you can dramatically reduce your exposure without grinding business to a halt.
Don't be the CTO explaining to the board why you trusted a vendor's security more than your own. Build security that assumes even your most trusted partners may be compromised, because some will eventually be.
Practical Steps
After implementing MitM protections across various organizations, here's what works in practice:
Technical Controls That Deliver Results
- Certificate pinning with fallbacks: Standard cert pinning breaks too easily. Implement dynamic pinning with proper failure modes. One financial client reduced their MitM exposure by 87% while maintaining 99.9% app availability using this approach.
- DNS over HTTPS (DoH) deployment: Moving your DNS queries to encrypted channels prevents many MitM techniques. It's nearly invisible to users when properly implemented, while dramatically reducing your attack surface.
- Multi-channel authentication: Verify critical actions through a separate channel. When a healthcare client implemented out-of-band verification for provider system access changes, they stopped three MitM attempts in the first month.
- Zero Trust for internal traffic, too: The notion that internal traffic is "safe" is outdated. Implement the same verification for server-to-server communications that you would for external traffic.
Process Changes That Stop Cybersecurity Threats Cold
- The two-channel verification rule: Any financial change (banking details, payment information) requires verification through a different communication channel. This simple policy stopped 94% of attempted financial frauds at one company I worked with.
- The "known contact only" policy: Establish a directory of verified contacts for key vendors and partners and process only financial requests from these pre-verified individuals.
- The transaction anomaly review: Implement automated systems that flag sudden changes in transaction patterns, such as new bank accounts, unusual amounts, or unexpected recipients.
The Human Element: Making Security Intuitive
- Three-minute microtraining: Forget hour-long security training. I've implemented Slack/Teams-delivered 3-minute security videos focused on one specific threat at a time. Engagement and retention skyrocketed compared to traditional training.
- The "pause and verify" culture: Create a culture where verification is celebrated, not seen as an annoyance. Publicly recognize team members who catch potential MitM attempts through verification.
- The simulated attack program: Run regular (but ethical) simulated MitM attacks against your team. The companies that do this see a 76% reduction in successful social engineering attempts over time.
Cybersecurity Threat Implementation
Look, I understand – you're balancing security with business operations.
Here's a phased approach that won't destroy productivity:
- Start with high-value targets: First, protect financial systems, authentication services, and sensitive data transfers. You'll get 80% of the protection benefit with 20% of the effort.
- Layer in verification processes: Add human verification steps for critical changes before implementing technical controls that might disrupt operations.
- Roll out technical controls gradually: Start with monitoring before blocking, implement in test environments first, and have clear rollback procedures.
- Make security visible but not intrusive: The best MitM protections are the ones users barely notice, which still clearly confirms that protection is active.
Word of Warning
I've cleaned up too many messes from successful MitM attacks, and they all have one thing in common – everyone thought "it won't happen to us" or "we're already protected." The reality is that these attacks succeed precisely because they exploit this false confidence.
Don't wait until you're explaining to the board how your company wired $2 million to an attacker's account to start. Start with the basics—encryption, verification, and awareness—and build from there.
Landscape of Threats
Since the Morris worm took down vital computer systems in 1988, malicious code has targeted vulnerabilities in protected networks. Worms are especially relevant in the interconnected SaaS world since they can replicate themselves without a host by moving through networks.
Specific Cybersecurity Threats for SaaS Platforms
Security risks take various forms and have varying effects based on the type of infrastructure they're hitting. For example, 43% of organizations say with some confidence that they've had at least one data breach that can be traced back to a misconfiguration of their SaaS system.
A further 63% say they can't be sure whether SaaS misconfigurations are to blame. Meanwhile, another survey notes that almost half of the surveyed SaaS companies overlook vulnerabilities.
In contrast, only 17% of breaches have targeted IaaS misconfigurations. Part of this seems to be the prevalence of overly complicated permissions structures that practically guarantee regular unauthorized access attempts.
Companies worldwide are currently sitting on top of more than 40 million individual permissions in their various SaaS systems, which might as well be a jungle full of predators as far as data security professionals are concerned.
Even worse are the faulty defense systems many organizations are running. The average company has nearly 4,500 internal user accounts without multi-factor authentication (MFA). Since MFA is arguably the strongest single measure for preventing data breaches, this creates a soft center that can be exploited by basically any hackers who manage to punch through the outer shell.
The unique vulnerability SaaS networks share has led to a rise in the shared responsibility model for defending against cyberattacks. This neatly divides the workload between users and cloud providers.
While the exact location of the split varies somewhat, the basic model has users taking responsibility for the assets they upload to the cloud. At the same time, the cybersecurity provider manages security for the cloud-native applications.
That said, Le notes that CSET is key in aligning leadership and teams around shared expectations and standard operating procedures. He continues that cybersecurity must be a collective responsibility across the organization, not just the domain of the CISO or technical staff, as human error remains the weakest link in the security chain.
"With the proliferation of AI-powered offensive tools, such as ransomware-as-a-service and other nefarious exploits, zero trust principles must be extended to the C-suite and board level to show that security is a priority, not just a slogan," adds Le.
Building a Culture of Awareness
Good information security starts with having a vigilant team that's wise to the threat they're facing. That begins with elevated threat awareness, which you can approach in various ways.
Quarterly or monthly meetings for all staff and an annual training module are good starts.
Employees with access to sensitive information should get more frequent reminders and retraining, ideally monthly or more.
Speak their language: risk, revenue, and reputation. I’ve found success by framing cyber threats as business risks, not technical problems. For example, instead of saying, “We need endpoint protection,” I’ll say, “This investment reduces the chance of a ransomware attack that could halt operations and cost $250K in downtime.”
The Power of Regular Cybersecurity Threat Audits
You must back up your training schedule with regular security audits. This is a fundamental component of most risk management and mitigation strategies. You can review your internal security architecture and external attacks by simulated threat actors.
Ethical hacking efforts can identify weaknesses and exploits in a way that might not show up with less intensive internal reviews.
Invest in the Right Tools and Technologies
While people are essential, they can only do what their tools allow. Take the time to invest in cybersecurity software that will genuinely make your networks more secure.
Essential Cybersecurity Tools for SaaS
Some security tools are so basic that everybody should have them. In addition to ultra-obvious stuff like good firewall protection and strong passwords, try these for starters:
- Cloud access security brokers (CASBs)
- Secure web gateways
- ACL Analytics
Think about how you manage your permissions. Plenty of tools exist to help you restrict unauthorized access to sensitive data while allowing fast and safe logins from authorized parties. These tools are available off the shelf from several companies, but they all fall pretty much into the same four baskets:
- Mandatory access control (MAC)
- Role-based access control (RBAC)
- Discretionary access control (DAC)
- Rule-based access control (RBAC or RB-RBAC)
Evaluating & Selecting Cybersecurity Threat Solutions
As you add security features, it's important not to go hog wild. A tool is a tool, and the world's most expensive hammer is a paperweight when you need a screwdriver. Only invest in the tools you can use, and narrow the focus to equipping teams rather than manning cool new gadgets.
To that end, you need a way to evaluate security tools as you try them out. Ideally, your metrics will be objective and verifiable by all parties, rather than just going with things you like. Focus on a tool's scalability, ability to integrate with your existing operating system and apps, and how well it can be used in a dynamic SaaS ecosystem.
Taylor adds that one unconventional but powerful approach is "positive" phishing. "Organizations that gamify cybersecurity and reward good behavior create a culture of awareness.
It's no longer “gotcha” security, it’s “we got this” security, he continues.
CISA: Your Secret Weapon
Let's talk about the most underutilized resource in your security arsenal. While you're dropping six figures on fancy security tools and consultants, there's a government agency quietly publishing intelligence that could save your company millions – and most CTOs I meet are barely tapping into it.
Why CISA Is Not Just Another Government Acronym
The Cybersecurity and Infrastructure Security Agency (CISA) isn't some bureaucratic backwater pushing outdated advisories.
It's become a cybersecurity powerhouse that deserves your attention:
- They see what you don't: CISA has visibility across critical infrastructure, government systems, and thousands of private sector breaches. When I implemented CISA's recommendations after the SolarWinds attack, we identified compromise indicators in our environment that none of our commercial tools flagged – three weeks before our security vendor released detection rules.
- They're faster than your vendors: After a major zero-day hit last year, CISA published actionable mitigation guidance within 48 hours, while most security vendors were still crafting their marketing emails about the threat. Time is your most precious commodity during an attack, and CISA consistently delivers when it matters.
- They speak CEO and technical languages: Their advisories balance technical depth with business impact, perfect for translating threats to your executive team without diluting critical technical details your security team needs.
That said, according to Jeff Le, the managing principal at 100 Mile Strategies and a Visiting Fellow at the National Security Institute, leveraging best CISA practices by working with companies and solutions that adhere to Secure by Design principles helps reduce some wild cards. However, he goes on to say that he has seen organizations do more to prioritize security configuration for Microsoft 365 and Google Workspace.
"Both adopt resources that emphasize extensible visibility, which is more pressing in cloud environments and helps fill gaps and mitigate risk," he continues.
Le goes on to say that "a clear rubric that connects operations to the NIST Cybersecurity Framework 2.0 allows everyone to have a road map and reminders to get back to basic hygiene and reduce unneeded complexity, especially with a focus on govern and identify facets."
Responding to Cybersecurity Incidents
Okay, you've gotten set up with some excellent security tools, and everybody is paranoid about the company's confidential information. Despite this, there's still a breach, and it's happening right now. What do you do?
Incident Response Planning
Ideally, you'll already have a plan that you can consult in the inevitable emergency. Different types of attacks call for different strategies, and you might need several response plans. That means before you can start responding to the threat, you have to identify it and kick-start your response.
Once you've identified the threat (in this case, a DDoS attack), you must isolate it as quickly as possible. Data compartmentalization is your friend here, like the bulkheads on a sailing ship. With internal firewalls and a quick response, you can generally limit an attacker's access and how long they can play on your systems.
The next move is eradication. For a DDoS attack, you might initiate an IP ban. You could shift to reserve servers, alert your cloud services provider, and call law enforcement to initiate their investigation. Wait until the attack is over to start recovery efforts.
Cybersecurity Threat Crisis Communication: Internal and External
Communication across stakeholders is crucial here. You might need many people working together in different places to stop the threat effectively. As with the initial detection and response, you should have a plan to set up communications channels ASAP and include several options with diverse routes so no single pathway can be compromised.
For example, if your internal memo and email systems are under attack, everybody should have a way of identifying that fact and know that you'll be sending text messages instead. In extreme cases, you could even DM your team leaders over social media.
Post-Incident Analysis and Recovery
When it's over, it's time to recover. Restore any lost data, and try to get your website back online. Review logs to see where the harm was done and restore your backups. Set up an after-action briefing on the incident to establish what happened, where the weakness was, and how to improve going forward.
CISA's Intelligence Engine: How to Use It
Stop treating CISA alerts like another security newsletter cluttering your inbox. Here's how successful CTOs leverage this resource:
- The Known Exploited Vulnerabilities (KEV) Catalog is gold: CISA's KEV doesn't waste your time with theoretical vulnerabilities – it focuses exclusively on those actively exploited in the wild. I've helped companies build automated patching workflows triggered directly from KEV updates, slashing their mean time to remediate from 27 days to 4 days.
- Their alerts should drive your response playbooks: One healthcare organization I advised built response templates based on CISA alert categories, with pre-approved actions for each severity level. This eliminated decision paralysis during incidents and accelerated their average response time by 64%.
- Sector-specific intelligence you can't get elsewhere: CISA's sector risk management teams provide industry-specific threat intelligence that commercial vendors can't match. This intelligence is invaluable for regulated industries in understanding their unique threat landscape.
Beyond Cybersecurity Threat Alerts: CISA's Overlooked Services That Deliver Real Value
CISA offers free services that rival what you're paying vendors for:
- Protective DNS is a no-brainer: Their Protective DNS Resolver service blocks malicious domains based on federal intelligence, and it's available at no cost to public and private critical infrastructure. When one energy company I worked with implemented this, they saw a 72% reduction in successful phishing attempts within 90 days.
- The SCuBA project for cloud security: CISA's Secure Cloud Business Applications project provides cloud security guidance that cuts through vendor marketing hype. Their baseline recommendations have helped multiple clients close critical cloud security gaps that commercial tools missed entirely.
- Free pen testing you're not using: Through its Risk and Vulnerability Assessment program, CISA offers critical infrastructure organizations free penetration testing. These aren't junior analysts—they're seasoned professionals who have seen the worst attacks across industries.
Making CISA Work in Your Security Program
Here's how to operationalize CISA intelligence without creating more work:
- Automate CISA alerts into your security workflow: Set up direct integration of their feeds into your ticketing system or SOAR platform. One manufacturing client reduced vulnerability triage time by 40% by automating CISA KEV entries directly to prioritized patch tickets.
- Establish a regular CISA review cadence: Assign a team member to spend 30 minutes weekly reviewing new CISA publications and reporting relevant findings in your security meetings. This small investment pays enormous dividends.
- Leverage their incident response resources before you need them: Contact your regional CISA team before a crisis hits. One retailer I advised had CISA experts on-site within hours of a significant breach because they'd established this relationship months earlier.
The most effective security leaders I know don't just consume CISA's intelligence—they actively participate in their information-sharing programs, providing feedback that strengthens the entire ecosystem.
Don't be the CTO scrambling to implement CISA's guidance after a breach. Make them an integral part of your security strategy today, and you'll gain an invaluable ally in defending your organization against threats that most commercial tools won't catch until it's too late.
Industry Regulations
Governments worldwide love to regulate tech-heavy industries, and a good old-fashioned security incident will get them interested like nobody's business. Be ready to answer some hard questions after a breach.
Understanding GDPR, CCPA, and Other Regulations
California’s Consumer Privacy Act (CCPA) and the European Union’s General Data Protection Regulation (GDPR) are the gold standard for data security regulations. Both are relevant to companies handling information across borders since you will likely be held to both.
GDPR is probably the most restrictive, as it sets six specific legal bases for a company to handle consumer data. The CCPA doesn't do this, but it requires all data handling to be lawful and not fraudulent. The EU's rule is regulatory only, while California has regulators and a statutory code from which to work.
Then there's HIPAA. If your enterprise touches medical records in the United States, the Health Insurance Portability and Accountability Act imposes standards and sanctions for healthcare information held by private entities.
Stay Safe
The landscape of cybersecurity threats poses new challenges to organizations daily. To deepen your understanding of how to counter these threats, exploring a range of insightful cybersecurity books can provide foundational knowledge and advanced strategies essential for any tech leader's arsenal.
Staying ahead of these threats requires up-to-date knowledge and a community of informed leaders sharing insights and strategies. There are many noteworthy cybersecurity resources available for you to learn more. For CTOs and tech leaders at the forefront of cybersecurity innovation and defense, join our newsletter for expert advice and cutting-edge solutions in cybersecurity.
FAQs: Enhancing Your Cybersecurity Threat Strategy
What Are the First Steps to Take After Identifying a Cybersecurity Threat?
You can’t fight what you haven’t found. Start by identifying the fact that an attack is ongoing or imminent, then isolate it to limit the damage it can do. Implement your emergency containment plan and try to stop the attack. Finally, schedule a debrief for the security team to work out what happened, what went wrong, and what went right.
How Can I Convince Stakeholders to Invest Against Cybersecurity Threats?
Stakeholders have an interest in the continued profitability and functionality of your enterprise. Simply reeling off the stats about how common attacks are and how expensive they can be is enough for most people. If you’re still not all the way there, try to come up with a few relatively affordable upgrades, such as installing MFA on your Wi-Fi networks, then reporting on how successful they’ve been.
What is a Common Cybersecurity Threat Myth?
By far the most common cybersecurity myth is that cybercriminals have no reason to attack your network. Even if you don’t handle credit cards or national security information, it’s pretty likely you have at least some sensitive information that’s worth a few dollars. Hackers looking for financial gain will always be motivated to crack your systems.