Best Data Security Software Shortlist
In today's digital landscape, data security is more than just a priority—it's a necessity. You're likely facing challenges in protecting sensitive information from threats and ensuring compliance with regulations. That's where data security software comes in, offering solutions to safeguard your data.
I've tested and reviewed various software independently. My goal? To give you a clear, unbiased look at the best options out there. In this listicle, I'll share top picks tailored for different needs, industries, and team sizes.
You'll find insights into features, user-friendliness, and what sets each tool apart. Let's make your data security decisions easier and more informed.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Data Security Software Summary
This comparison chart summarizes pricing details for my top data security software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for secure network access with scalability | 14-day free trial + free demo available | From $7/user/month (billed annually) | Website | |
| 2 | Best for data security compliance | Free plan available | From $150/month (billed annually) | Website | |
| 3 | Best for multi-layered malware protection | 30-day free trial | From $49.99/device/year | Website | |
| 4 | Best for secrets management and data protection | Not available | Pricing upon request | Website | |
| 5 | Best for Oracle database risk assessment | Not available | Pricing upon request | Website | |
| 6 | Best for data redaction and cloning | Not available | Pricing upon request | Website | |
| 7 | Best for robust embedded database management | Not available | Pricing upon request | Website | |
| 8 | Best for pinpointing data vulnerabilities | Not available | Pricing upon request | Website | |
| 9 | Best for cryptographic protection of database records | Not available | Pricing upon request | Website | |
| 10 | Best for personal data discovery and privacy | Free demo available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Data Security Software Reviews
Below are my detailed summaries of the best data security software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
NordLayer, by the renowned NordVPN team, delivers a secure network solution tailored for businesses. With an emphasis on combining security with scalability, NordLayer ensures that companies can grow while maintaining a robust protective barrier for their networks.
Why I Picked NordLayer:
When choosing the right tools, I had to judge based on efficacy, utility, and overall capability. In comparing various service providers, NordLayer consistently emerged as a top contender. Its unique blend of security features, coupled with the scalability it offers, led me to determine that it stands head and shoulders above its peers. Given these attributes, NordLayer is optimal for businesses needing secure network access that can scale as they grow.
Standout Features & Integrations:
NordLayer boasts a solid replication mechanism ensuring network settings consistency across various locations. Its support for multiple repositories aids in data organization, and its advanced web application security measures are commendable. Integration-wise, NordLayer seamlessly fits into an organization's infrastructure, supporting significant platforms and devices without hitches.
Pros and Cons
Pros:
- High-grade web application security provisions
- Supports diverse repositories aiding in better data management
- Offers advanced replication mechanisms for network consistency
Cons:
- Depending on the business size, some features might be overkill and underutilized
- Some users might prefer a standalone application rather than a suite
- Might be perceived as complex for smaller teams without dedicated IT personnel
New Product Updates from NordLayer
NordLayer Enhances Security with Download Protection
NordLayer introduces a Download Protection feature that safeguards files from threats by scanning and blocking malicious downloads in real time. For more information, visit NordLayer's official site.
Ketch is a data privacy management platform designed to help businesses automate privacy compliance and data governance. By leveraging Ketch, your team can responsibly collect and utilize customer data, ensuring adherence to global privacy regulations.
Why I Picked Ketch:
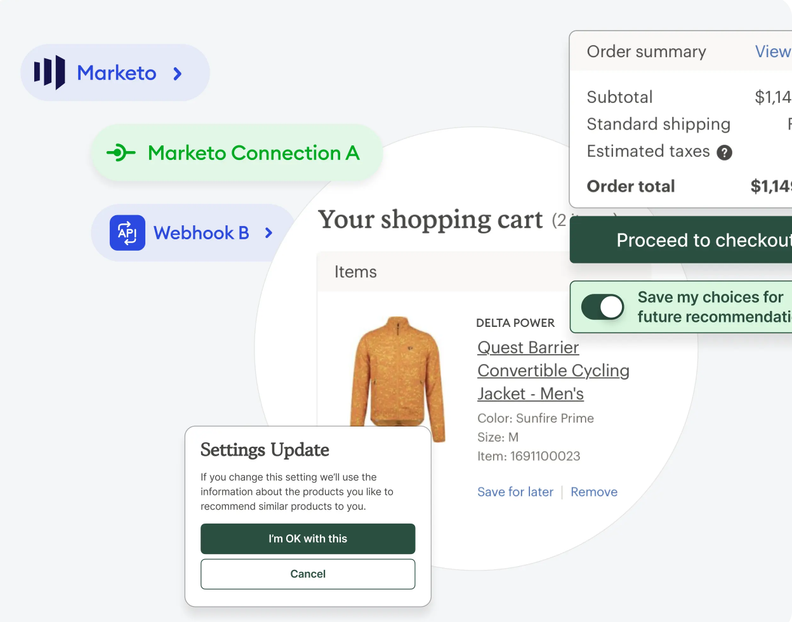
Ketch is unique in that it focuses on data security compliance instead of threat detection. For example, it offers consent management and data subject request automation. These features are crucial for ensuring your organization complies with regulations like GDPR and CCPA for the secure handling of information. Ketch also has data mapping tools that provide instant insights into personal data flowing across your entire business, helping you find and assess data risks with the power of AI.
Standout Features & Integrations:
Additionally, Ketch covers the complete lifecycle of data subject requests, from consumer intake to fulfillment in your data systems. This includes customizable intake forms and a drag-and-drop workflow builder, allowing your team to efficiently manage and respond to data access or deletion requests. Some integrations include Adobe Experience Platform, AdRoll, Google Analytics, HubSpot, Salesforce, Shopify, Snowflake, Facebook Ads, Google Ads, LinkedIn, Mailchimp, and Oracle.
Pros and Cons
Pros:
- Provides clear data mapping for better visibility
- Customizable workflows allow adaptation to specific business needs
- Automates data subject request handling
Cons:
- Doesn't offer data threat prevention and protection
- Potential learning curve during setup
New Product Updates from Ketch
Ketch Expands Marketing Preference Management Capabilities
Ketch expands Marketing Preference Management, introducing capabilities for unifying consent, preferences, and zero-party data across systems. This update enables teams to activate customer data more effectively for personalized and compliant marketing. For more information, visit Ketch’s official site.
ESET offers robust cybersecurity solutions that deliver multi-layered protection against various malware threats. As online threats become more advanced, businesses must have a defense mechanism like ESET that prioritizes comprehensive malware protection.
Why I Picked ESET:
While exploring cybersecurity tools, ESET consistently made its presence felt. After determining its capabilities and comparing it with other contenders, I formed an opinion: ESET truly differentiates itself through its multi-layered approach. Given its dedication to addressing malware threats from multiple angles, it's best for multi-layered malware protection.
Standout Features & Integrations:
ESET has advanced features like network security that monitors inbound and outbound traffic, ensuring any malicious activity is thwarted. The password manager is also a boon for users, centralizing and securing password-related operations. As for integrations, ESET can be integrated into various operating systems and platforms, ensuring wide-ranging device protection.
Pros and Cons
Pros:
- Flexible integration options ensure protection across diverse platforms
- Integrated password manager promotes secure password practices
- Advanced network security capabilities protect against both known and emerging threats
Cons:
- Though comprehensive, it might be feature-rich for smaller teams with basic needs
- Frequent updates may disrupt workflows for some users
- Interface might be intimidating for non-tech savvy users
HashiCorp Vault is an advanced solution that manages secrets and protects sensitive data. Recognizing the increasing threats in today's digital environment, Vault's unique approach to secrets management makes it pivotal for businesses aiming for top-tier data protection.
Why I Picked HashiCorp Vault:
In the landscape of cybersecurity tools, Vault emerged as a clear standout when I was selecting the best. It wasn't just a snap judgment; rather, after comparing various options, assessing user testimonials, and relying on my experience, I chose Vault. It's unique, not just in its capability but also in its design. Vault is undeniably the best choice for businesses that prioritize secrets management and seek formidable data protection, Vault is undeniably the best choice.
Standout Features & Integrations:
HashiCorp Vault excels in dynamic secrets management, allowing temporary access, and reducing the risks associated with static passwords. It also integrates with numerous firewall systems, enhancing the protection against potential cyberattacks. Regarding integrations, Vault integrates well with various cloud-based providers, ensuring that secrets are consistently managed regardless of where your infrastructure resides.
Pros and Cons
Pros:
- Enhanced protection against cyberattacks
- Strong integrations with major cloud providers
- Dynamic secrets management reduces risks
Cons:
- Documentation may be challenging for some to navigate
- Requires consistent monitoring and management
- Setup can be complex for beginners
Oracle Data Safe is a robust solution dedicated to the risk assessment of Oracle databases. With an all-in-one approach, it provides end-to-end security features, compliance reporting, and disaster recovery capabilities, making it essential for any business relying on Oracle's database ecosystem.
Why I Picked Oracle Data Safe:
In my quest for the most adept Oracle-specific database risk assessment tool, Oracle Data Safe surfaced as a top contender. I judged its capabilities against others and found its all-in-one, end-to-end approach distinctive. Given its specialized focus on Oracle databases and its vast features, it's no surprise that I see it as the best for Oracle database risk assessment.
Standout Features & Integrations:
Oracle Data Safe boasts a comprehensive suite of security and risk management tools. Its compliance reporting tools are particularly noteworthy, simplifying the often complex task of maintaining database compliance. Furthermore, its integrations within the Oracle ecosystem, including Oracle Cloud Infrastructure and Oracle Autonomous Database, ensure a smooth and connected operational environment.
Pros and Cons
Pros:
- Tightly integrated with other Oracle services for a unified experience
- Strong emphasis on compliance reporting, ensuring adherence to regulations
- All-in-one platform that provides end to end risk assessment solutions
Cons:
- As a specialized tool, it might be seen as an added expense on top of other Oracle services
- The depth of its features may present a machine learning curve for some users
- Might be too Oracle-specific for businesses using a mix of database providers
Oracle Data Masking and Subsetting specializes in safeguarding sensitive data by utilizing data redaction and cloning techniques. This ensures that real data is shielded even in test environments, positioning it as an instrumental solution for organizations prioritizing data protection and efficient data management.
Why I Picked Oracle Data Masking and Subsetting:
In selecting tools for a definitive list, I meticulously compared various contenders. I chose Oracle Data Masking and Subsetting for its consistent reputation and robust capabilities in data redaction. Its proficiency in redaction and cloning makes it an obvious choice for organizations looking for these specific functionalities.
Standout Features & Integrations:
The strength of Oracle Data Masking and Subsetting lies in its comprehensive features for data protection. It offers ransomware protection that safeguards your data from potential threats and a permissions system that provides granular control over data access. Furthermore, it's designed with integrations that cater to a variety of mobile devices, expanding its utility and adaptability.
Pros and Cons
Pros:
- Compatibility with a range of mobile devices broadens its applicability
- Granular permissions system allows controlled data access
- Advanced ransomware protection ensures data remains uncompromised
Cons:
- Some organizations might find its features excessive for simple tasks
- Integration with existing infrastructure might require expert assistance
- Potential complexity for new users due to its extensive feature set
Databases are essential in today's complex technology environments, especially regarding strong embedded database management. This makes them an invaluable choice.
Why I Picked SAP SQL Anywhere:
Based on my research and analysis, SAP SQL Anywhere is the best solution for data management. It excels in embedded database management and has a reliable and efficient infrastructure. It's an ideal choice for businesses needing dependable data management.
Standout Features & Integrations:
SAP SQL Anywhere is designed to keep your data synchronized and consistent across different applications and platforms. It has advanced security features to protect your databases and an automation function that simplifies database tasks while maintaining high performance. SAP SQL Anywhere also integrates seamlessly with other SAP solutions, which makes it an essential component of a complete enterprise technology stack.
Pros and Cons
Pros:
- Efficient automation of database tasks
- Advanced authentication measures
- Strong synchronization with multiple apps
Cons:
- The complexity might be overkill for smaller projects
- Limited native integrations outside the SAP ecosystem
- Might have a steeper learning curve for new users
Best for pinpointing data vulnerabilities
IBM Security Guardium Vulnerability Assessment offers a meticulous examination of your data environment to identify, classify, and prioritize vulnerabilities. With data breaches becoming more sophisticated, this tool's expertise in pinpointing exposures is pivotal for proactive protection.
Why I Picked IBM Security Guardium Vulnerability Assessment:
The journey of selecting the ideal vulnerability assessment tool was not trivial. Among numerous contenders, IBM Security Guardium set itself apart. I chose it for its reputable track record and IBM's history of consistent innovation. This tool is the best choice when it comes to precision in identifying vulnerabilities, especially in large-scale on-premises environments vulnerabilities, especially in large-scale on-premises environments, this tool stands as the best choice.
Standout Features & Integrations:
IBM's solution boasts advanced anti-malware integration, ensuring the detection and prevention of malicious intrusions. With support for multiple operating systems, it offers versatility in scanning different IT environments. Furthermore, its integrations extend to various data sources, from traditional databases to big data environments, covering a broad spectrum of potential vulnerabilities.
Pros and Cons
Pros:
- Advanced anti-malware capabilities
- Comprehensive support for multiple operating systems
- Precision in vulnerability detection
Cons:
- Initial configuration can be intensive
- Requires regular updates to stay current with threats
- Might be overwhelming for small businesses
Acra offers specialized tools that prioritize the cryptographic protection of database records, ensuring that sensitive data remains confidential and unaltered. Recognizing the increasing threats to data integrity and the value of cryptographic safeguards, Acra emerges as a pertinent solution for organizations keen on enhanced data encryption.
Why I Picked Acra:
Choosing the right tools for a list requires an in-depth examination of the landscape. After deliberating, I decided Acra for its unique approach to data encryption. Its unwavering focus on cryptographic protection differentiates it from many other tools. This specific dedication convinced me that it is best suited for protecting database records.
Standout Features & Integrations:
Acra has a range of features aimed at robust data encryption and data loss prevention. Its data privacy measures are thorough, ensuring organizations can trust their records’ sanctity. Acra's integrations with popular databases also underline its versatility and applicability in various database environments.
Pros and Cons
Pros:
- Wide-ranging integrations with popular databases
- Effective data loss prevention (DLP) capabilities
- In-depth cryptographic measures for database records
Cons:
- Might not be suitable for small-scale projects with minimal encryption needs
- Integration might be complex depending on the existing infrastructure
- Might require a learning curve for those unfamiliar with cryptographic tools
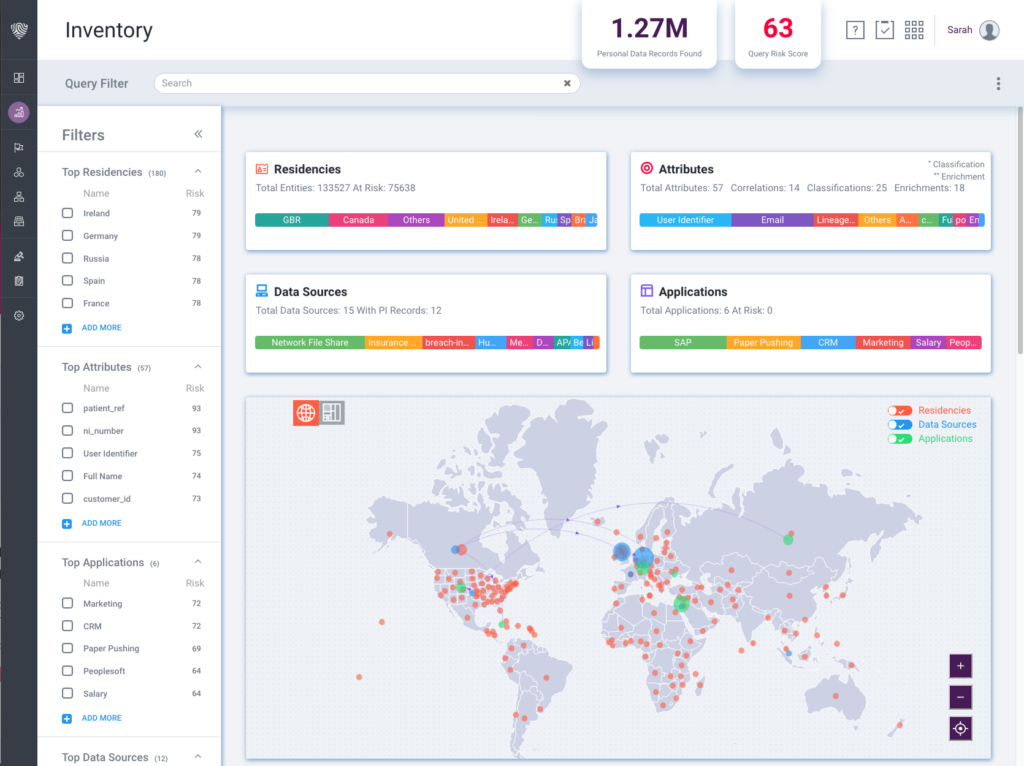
BigID specializes in helping organizations find and protect their most sensitive personal data across their entire data ecosystem. Its focus on personal data discovery and the increasing demand for privacy in today's GDPR-driven world make it an essential tool for businesses concerned about information security.
Why I Picked BigID:
During my exploration of data protection tools, BigID consistently stood out. I judged it against many tools and determined that its approach to personal data discovery was unparalleled. My opinion, formed through comparing its capabilities, is that it's unequivocally best for personal data discovery and privacy.
Standout Features & Integrations:
BigID's prowess lies in its advanced data discovery capabilities, which go beyond typical endpoint protection to offer a granular view of personal data. It also incorporates proactive measures to ensure information security and GDPR compliance. Integration-wise, BigID seamlessly connects with various data sources and platforms, ensuring comprehensive data oversight.
Pros and Cons
Pros:
- Wide-ranging integrations ensure extensive data ecosystem coverage
- Proactively addresses information security and GDPR concerns
- Advanced data discovery capabilities cater to a detailed view of personal data
Cons:
- While comprehensive, its features may be overwhelming for small businesses
- Depending on the scale, the implementation process might be time-consuming
- Might have a learning curve for users new to data protection tools
Other Data Security Software
Here are some additional data security software options that didn’t make it onto my shortlist, but are still worth checking out:
- SQL Secure
For SQL server security monitoring
- Satori Data Security Platform
For real-time data flow visibility
- McAfee Vulnerability Manager for Database
For comprehensive database threat insights
- Protegrity
Good for enterprise-wide data protection solutions
- DBHawk
Good for intuitive web-based database management
- Immuta
Good for dynamic data access and control
- IBM Security Guardium Insights
Good for comprehensive data activity auditing
- DataSunrise Database Security
Good for real-time data masking and monitoring
- Oracle Advanced Security
Good for advanced encryption and redaction solutions
- Aryson SQL Password Recovery
Good for swift SQL database password retrieval
- Assure Security
Good for multi-layered IBM i system protection
- Imperva Database Risk & Compliance
Good for insightful risk assessment and compliance
- Covax Polymer
Good for data-driven AI and BI solutions
- MyDiamo
Good for column-level encryption in databases
- Trustwave AppDetectivePRO
Good for vulnerability assessment and database discovery
- ASNA DataGate
Good for IBM i data-centric solutions
- iSecurity Safe-Update
Good for controlled data file editing on IBM i
Data Security Software Selection Criteria
When selecting the best data security software to include in this list, I considered common buyer needs and pain points like protecting sensitive information and ensuring compliance with data regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Protecting sensitive data
- Ensuring data encryption
- Monitoring data access
- Managing user permissions
- Detecting data breaches
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat intelligence
- Automated compliance reporting
- Advanced data analytics
- Cross-platform integration
- User behavior analytics
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Ease of navigation
- Customizable dashboards
- Minimal learning curve
- Responsive performance
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Live chat support during setup
- Webinars for new users
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multi-channel communication options
- Knowledgeable support staff
- Fast response times
- Comprehensive help center
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Pricing transparency
- Competitive pricing
- Flexible subscription plans
- Free trial availability
- Discounts for long-term commitments
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Commonly reported issues
- Praise for specific features
- Feedback on customer support
- User recommendations
How to Choose Data Security Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your business? Check if it can handle increased data volumes and user counts without degrading performance. |
| Integrations | Does it work well with your existing systems? Look for compatibility with your current tools to avoid costly and time-consuming workarounds. |
| Customizability | Can you tailor the software to your specific needs? Flexibility in settings and features ensures it meets your unique requirements. |
| Ease of use | Is the interface intuitive for your team? A simple design reduces training time and increases user adoption. |
| Implementation and onboarding | How quickly can you get up and running? Consider the complexity of setup and the support provided during the transition. |
| Cost | Does the price fit your budget? Compare upfront costs and long-term expenses, including hidden fees or required add-ons. |
| Security safeguards | Are there robust protections for your data? Ensure the software meets industry standards for encryption and access controls. |
| Compliance requirements | Does it support your regulatory needs? Verify that it aligns with legal obligations like GDPR or HIPAA to avoid compliance issues. |
What Is Data Security Software?
Data security software is designed to protect sensitive information from unauthorized access and breaches. IT professionals, security analysts, and compliance officers typically use these tools to safeguard data integrity and privacy. Encryption, data masking software, access controls, and real-time monitoring help with compliance, protecting data, and ensuring ease of use. Overall, these tools provide peace of mind by keeping your data secure.
Features
When selecting data security software, keep an eye out for the following key features:
- Encryption: Protects data by converting it into a secure code, ensuring only authorized users can access it. PKI software can help manage encryption keys and digital certificates once active.
- Access controls: Manages who can view or modify data, helping maintain privacy and security.
- Real-time monitoring: Continuously checks for suspicious activity, alerting you to potential threats immediately.
- Compliance reporting: Simplifies adherence to regulations by generating necessary audit trails and reports.
- User behavior analytics: Tracks and analyzes user actions to detect unusual activity that might indicate a security risk.
- Automated backups: Regularly saves data copies to prevent loss from hardware failure or cyber attacks.
- Threat intelligence: Provides insights into potential security risks by analyzing data from various sources.
- Cross-platform integration: Ensures compatibility with existing systems, reducing disruptions and enhancing functionality.
- Customizable dashboards: Allows you to tailor views and reports to fit specific needs, improving data management.
- Training resources: Offers guides, videos, and interactive tools to help users understand and utilize the software effectively.
Benefits
Implementing data security software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced data protection: Encryption and access controls ensure sensitive information stays secure from unauthorized access.
- Regulatory compliance: Compliance reporting helps your business meet legal requirements and avoid penalties.
- Threat detection: Real-time monitoring and threat intelligence alert you to potential risks before they become issues.
- Operational continuity: Automated backups ensure data recovery in case of hardware failures or cyber attacks.
- Informed decision-making: User behavior analytics provide insights into user activities, helping to identify and address security gaps.
- Improved efficiency: Cross-platform integration ensures smooth operation with existing systems, minimizing disruptions.
- User empowerment: Training resources help your team effectively use the software, increasing overall security awareness.
Costs & Pricing
Selecting data security software is similar to choosing internet security software, as it requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in data security software solutions:
Plan Comparison Table for Data Security Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic encryption, limited data protection, and access controls. |
| Personal Plan | $5-$25/user/month | Enhanced encryption, real-time monitoring, and basic compliance reporting. |
| Business Plan | $25-$50/user/month | Advanced threat detection, user behavior analytics, and automated backups. |
| Enterprise Plan | $50-$100/user/month | Customizable dashboards, cross-platform integration, and dedicated support. |
Data Security Software FAQs
Here are some answers to common questions about data security software:
How do I know if a data security software is compatible with my existing systems?
Check for integration capabilities with your current software and systems. Most providers list compatible platforms on their website. You might also consider reaching out to their support team for confirmation. Compatibility ensures the software works seamlessly with your existing tools, saving time and reducing potential headaches.
Can data security software help with compliance requirements?
Yes, many data security software solutions offer features that assist with compliance requirements. These tools often include automated compliance reporting and audit trails, which help you meet regulations like GDPR or HIPAA. By using these features, you can ensure your organization adheres to necessary legal standards and avoid potential fines.
How often should data security software be updated?
Regular updates are crucial for maintaining security. Most software providers offer automatic updates to ensure you have the latest protections against new threats. I recommend setting your software to update automatically or scheduling regular checks to see if updates are available. Staying up-to-date minimizes vulnerabilities and enhances security.
What’s Next:
If you're in the process of researching data security software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.