Best Vulnerability Management Tools Shortlist
The best vulnerability management tools help teams identify exposures early, reduce security risks, and maintain safer, more compliant systems across their infrastructure. When weaknesses go undetected, when patching cycles rely on manual tasks, or when alerts generate more noise than useful insight, threats can grow quickly and create unnecessary gaps in security operations.
The right vulnerability management platform gives security and IT teams clear visibility, automated scanning, and accurate prioritization so they can understand which issues require immediate action and resolve them before they impact the business. As a Chief Technology Officer with over 20 years of experience testing and implementing security tools in real production environments, I’ve evaluated the top solutions based on detection accuracy, automation quality, and ease of use during ongoing security work.
Each review covers features, pros and cons, and ideal use cases to help your team choose the best vulnerability management tool for reliable, efficient risk reduction.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Vulnerability Management Tools Summary
This comparison chart summarizes pricing details for my top Vulnerability Management Tools selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for third-party vendor risk assessments | Free demo available | Pricing upon request | Website | |
| 2 | Best for real-time external threat monitoring | Not available | Pricing upon request | Website | |
| 3 | Best for continuous vulnerability monitoring | 14-day free trial + free demo available | From $149/month | Website | |
| 4 | Best for comprehensive code-to-cloud security | Free plan available + free demo | From $350/month | Website | |
| 5 | Best for zero-configuration security insights | Free trial + free demo available | Pricing upon request | Website | |
| 6 | Best for comprehensive threat intelligence | Not available | Pricing upon request | Website | |
| 7 | Best for extensive device and protocol coverage | Not available | Pricing upon request | Website | |
| 8 | Best for integration with Microsoft ecosystem | Not available | From $10/user/month (billed annually) | Website | |
| 9 | Best for active directory and infrastructure security | Not available | From $3/user/month (billed annually) | Website | |
| 10 | Best for comprehensive IT asset management | Not available | Pricing upon request | Website |
-

QA Wolf
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

NordLayer
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.3 -

Intruder
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Vulnerability Management Tool Reviews
Below are my detailed summaries of the best Vulnerability Management Tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Prevalent is a third-party risk management platform that helps organizations assess and monitor the risks associated with their vendors and suppliers. By automating the collection and analysis of vendor data, Prevalent enables you to focus on reducing risk and ensuring compliance throughout your vendor ecosystem.
Why I Picked Prevalent: As a vulnerability management tool, Prevalent offers cyber intelligence to help you identify and address potential security issues within your vendor network. It monitors over 550,000 companies for cyber incidents by tracking more than 1,500 criminal forums, numerous dark web pages, and various threat feeds. This extensive monitoring allows you to stay informed about vulnerabilities and take proactive measures to protect your organization.
Standout features & integrations:
Features include automated onboarding and offboarding processes, simplifying the management of vendor relationships. The platform also includes a vendor dashboard that centralizes security, performance, and compliance reporting, making it easier for your team to monitor and address risks. Furthermore, Prevalent provides built-in remediation guidance.
Integrations include Active Directory, BitSight, ServiceNow, SecZetta, and Source Defense.
Pros and Cons
Pros:
- Strong security protocols to protect data
- Users can tailor reports according to specific needs
- Extensive functionalities for managing vendor risk
Cons:
- Challenges in migrating data can complicate the initial setup
- The platform is complex and comes with a learning curve
NordStellar is a platform designed to help you manage vulnerabilities with a focus on external threat intelligence and security. It provides tools to identify and mitigate potential security threats in real-time, ensuring your organization stays protected from cyber threats.
Why I Picked NordStellar: I chose NordStellar for its real-time alerts, advanced threat detection, and automated attack surface management that keep you ahead of cyber risks. With instant data breach and dark web monitoring, it alerts your team to compromised data or emerging threats, enabling swift action. By centralizing intelligence from over 36,000 sources and prioritizing risks, NordStellar helps both executives and security teams maintain proactive, comprehensive protection.
Standout features & integrations:
Features include brand protection, which helps in detecting and preventing unauthorized use of your brand online. The platform also offers real-time monitoring, allowing you to keep a constant watch on security threats. Lastly, its integration capabilities with SIEM and SOAR platforms mean you can easily incorporate NordStellar into your existing security infrastructure, enhancing your overall security posture.
Integrations include Splunk, SIEM platforms, SOAR platforms, Email, Slack, Webhooks, and API.
Pros and Cons
Pros:
- Integrates with SIEM and SOAR
- Automated asset discovery and mapping
- Real-time alerts for cyber threats
Cons:
- Limited mobile application support
- Pricing not publicly disclosed
Intruder is a cloud-based vulnerability management tool that helps you identify and address security weaknesses in your digital infrastructure.
Why I Picked Intruder: Intruder's continuous vulnerability management ensures your systems are regularly scanned for new threats. This feature automatically initiates scans when changes are detected, helping you stay ahead of potential security risks. Additionally, Intruder's attack surface management discovers unknown assets like subdomains and untracked APIs, providing a comprehensive view of your organization's exposure. It also offers exposure management, which combines multiple scanning engines to identify over a thousand attack surface issues that other scanners might miss.
Standout features & integrations:
Features include prioritization that leverages the latest threat intelligence, such as CISA's Known Exploited Vulnerabilities list and machine learning-driven exploitation predictions. It also offers private bug bounty access, allowing your team to collaborate with elite hackers to uncover vulnerabilities that automated scanners might overlook.
Integrations include AWS, Azure, Google Cloud, Drata, Jira, Azure DevOps, GitHub, GitLab, ServiceNow, Cloudflare, Microsoft Sentinel, and Okta.
Pros and Cons
Pros:
- Compliance reporting capabilities
- Automated scanning and monitoring
- Comprehensive vulnerability detection
Cons:
- Attack surface feature limited to premium plan
- Occasional false positives
New Product Updates from Intruder
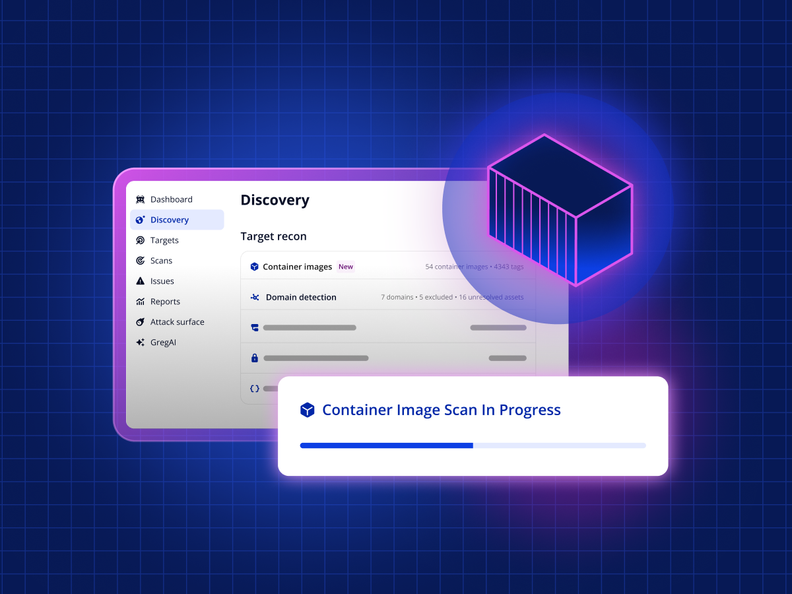
Intruder Unveils Agentless Container Image Scanning
Intruder introduces agentless container image scanning across cloud platforms. This update helps teams detect vulnerabilities before deployment with less setup. For more information, visit Intruder’s official site.
Aikido Security is an all-in-one platform that helps you identify and fix vulnerabilities in your code and cloud environments. It offers a range of tools to detect security risks, from static code analysis to cloud posture management.
Why I Picked Aikido Security: Aikido's static code analysis (SAST) scans your source code to spot vulnerabilities like SQL injection and cross-site scripting before they become issues. This proactive approach lets your team address potential threats early, enhancing your application's security. Additionally, Aikido's secret detection feature checks your code for exposed API keys, passwords, and other sensitive information, preventing accidental leaks that could be exploited.
Standout features & integrations:
Features include its cloud posture management (CSPM) capabilities that detect risks in your cloud infrastructure across major providers, helping you maintain a secure cloud environment. Aikido also offers infrastructure as code (IaC) scanning, open-source dependency scanning, container image scanning, surface monitoring, and malware detection in dependencies.
Integrations include Amazon Web Services (AWS), Google Cloud, Microsoft Azure Cloud, Drata, Vanta, AWS Elastic Container Registry, Docker Hub, Jira, Asana, and GitHub.
Pros and Cons
Pros:
- Scalable for growing teams
- Offers actionable insights
- Has a comprehensive dashboard and customizable reports
Cons:
- Only available in English
- Ignores vulnerabilities if no fix is available
New Product Updates from Aikido Security
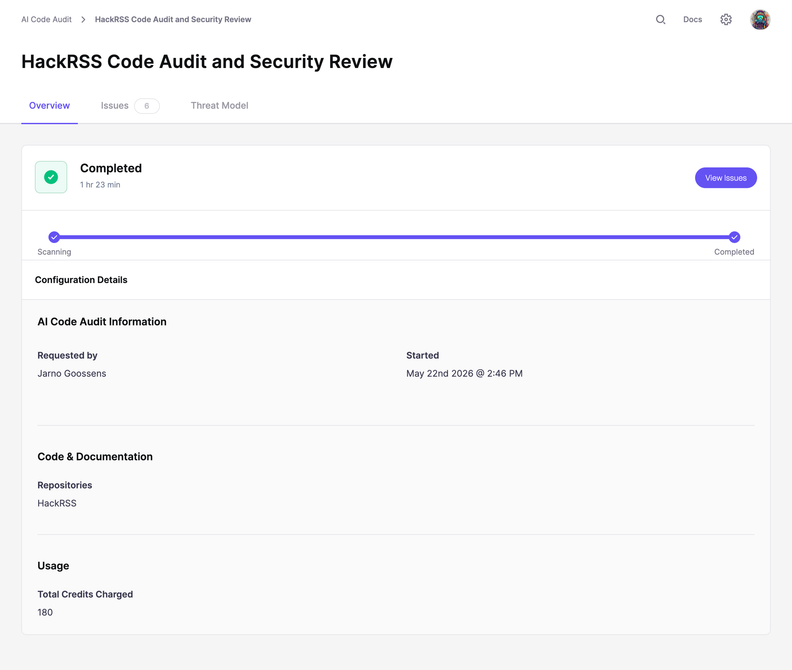
Aikido Security Adds Code Audit for Source Code Analysis
Aikido Security introduces Code Audit, bringing pentest-grade security reasoning directly to your source code to uncover logic flaws and vulnerabilities missed by pattern scanners. For more information, visit Aikido Security's official site.
New Relic is an all-in-one observability platform designed to help you monitor, debug, and improve your entire software stack. It offers a range of tools to ensure your applications run smoothly and securely.
Why I Picked New Relic: I chose New Relic for its ability to provide continuous runtime software composition analysis (SCA) and vulnerability assessment without requiring additional configuration. This means you can instantly detect common vulnerabilities and exposures (CVEs) across your application's dependencies, helping you identify potential security risks early in the development process.
Standout features & integrations:
Features include enhanced prioritization analytics that help you prioritize which risks need immediate attention by incorporating data like the Exploit Prediction Scoring System (EPSS). It is also an open ecosystem that enables easy integration with your existing security assessment tools.
Integrations include AWS, Google Cloud Platform, Microsoft Azure, Slack, Atlassian Jira, AWS EventBridge, Email Notifications, Mobile Push Notifications, Opsgenie, PagerDuty, ServiceNow, and Prometheus.
Pros and Cons
Pros:
- Wide range of integrations with cloud platforms and development tools
- Offers real-time tracking and detailed error logging
- Provides comprehensive monitoring and alerting capabilities
Cons:
- Dashboards may require customization for specific use cases
- Learning curve for new users
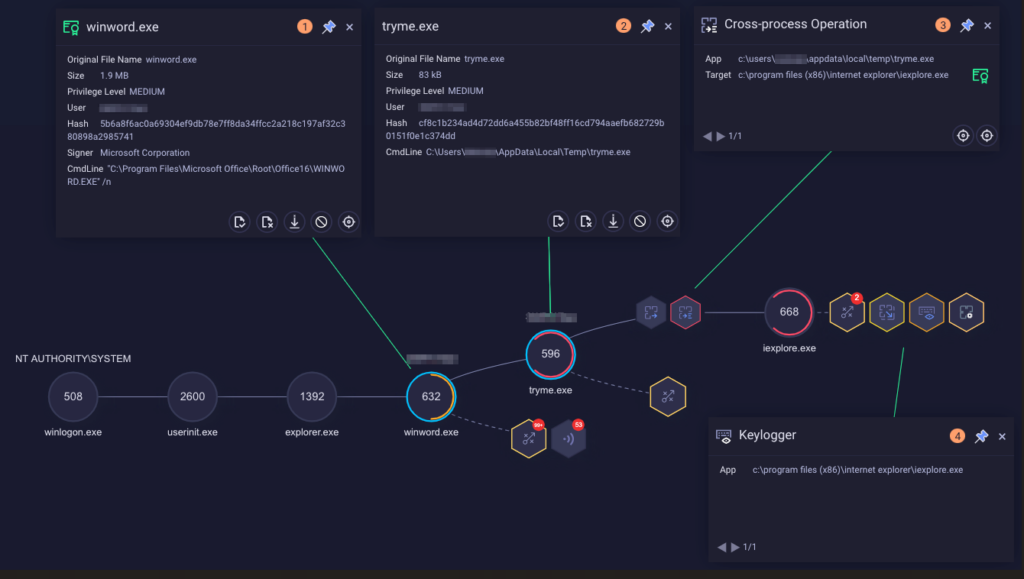
The IBM Security QRadar EDR tool is an advanced threat protection platform that provides companies with critical insight into potential security risks. Its capabilities are uniquely designed for comprehensive threat intelligence, providing a holistic view of a firm's threat landscape.
Why I Picked IBM Security QRadar EDR: In the realm of cybersecurity tools, IBM Security QRadar EDR emerged as a top pick for me because of its capability to offer end-to-end threat detection and response. This tool has top-notch threat intelligence that goes beyond others. It gathers and analyzes data from multiple sources for a complete view of security risks.
Standout features & integrations:
IBM Security QRadar EDR shines with features like artificial intelligence (AI) integration, which supports advanced threat detection and automated response actions. Furthermore, it’s User Behavior Analytics (UBA) helps identify insider threats by analyzing patterns.
Notably, QRadar EDR integrates well with other security and IT management platforms, allowing for streamlined threat management.
Pros and Cons
Pros:
- Facilitates robust user behavior analysis
- Provides advanced threat detection with AI
- Offers comprehensive threat intelligence
Cons:
- Advanced features may require dedicated personnel to manage
- May be complex for new users
- Pricing not readily available
Cisco Vulnerability Management is a robust security solution that offers an expansive range of device and protocol coverage. The tool scans your network to identify and manage vulnerabilities, making it an excellent choice for those seeking to secure diverse device environments and protocols.
Why I Picked Cisco Vulnerability Management: I chose Cisco Vulnerability Management primarily because of its wide device and protocol coverage, which is critical for businesses operating in a mixed environment. I determined this tool to be unique in its capability to cover many devices and protocols, making it best for organizations that utilize the diverse technological infrastructure.
Standout features & integrations:
Key features of Cisco Vulnerability Management include robust scanning capabilities, extensive device and protocol support, and advanced reporting.
Its integrations are also impressive, with connectivity to other Cisco security products and third-party security systems, broadening its utility and effectiveness within your security ecosystem.
Pros and Cons
Pros:
- Integration with Cisco and third-party security systems
- Advanced reporting capabilities
- Extensive device and protocol coverage
Cons:
- Limited customization features for reporting and dashboards
- May have a steep learning curve for new users
- Pricing details are not readily available
Best for integration with Microsoft ecosystem
Microsoft Defender Vulnerability Management is a comprehensive security tool designed to identify, assess, and mitigate vulnerabilities. It fits into the Microsoft ecosystem, providing an integrated solution for businesses heavily invested in Microsoft products.
Why I Picked Microsoft Defender Vulnerability Management: I selected Microsoft Defender Vulnerability Management because it integrates with the Microsoft ecosystem. Given its native integration with products like Windows, Office 365, and Azure, it provides a unified security solution that stands apart from many competitors. It also supports macOS, Linux, Android and iOS, and some network devices. Therefore, this tool is best for businesses that have a strong reliance on Microsoft products.
Standout features & integrations:
Microsoft Defender Vulnerability Management offers advanced threat analytics, vulnerability assessment, and threat & vulnerability management.
Its most notable aspect is its integration with the Microsoft ecosystem, including Microsoft 365 Defender, Microsoft Defender for Endpoint, and Azure Security Center, contributing to a more consolidated and effective security posture.
Pros and Cons
Pros:
- Effective vulnerability assessment and management
- Advanced threat analytics feature
- Integration with Microsoft ecosystem
Cons:
- Limited customization options for reports and dashboards
- Pricing can be high for smaller organizations
- Less effective for non-Microsoft systems
Best for active directory and infrastructure security
Tenable Vulnerability Management is a comprehensive security platform that provides a thorough active directory and infrastructure security. It allows organizations to continuously monitor their IT infrastructure, ensuring security weaknesses are promptly identified and addressed, which aligns perfectly with its 'best for' statement.
Why I Picked Tenable Vulnerability Management: I picked Tenable for its strong emphasis on active directory and infrastructure security. Its robustness in these areas sets it apart from many other tools. If active directory and infrastructure security are your priority, then Tenable Vulnerability Management is the right choice.
Standout features & integrations:
Tenable Vulnerability Management offers predictive prioritization, continuous visibility, and in-depth analytics among its most essential features.
Regarding integrations, it connects with a wide range of systems, including Active Directory, cloud-based infrastructures, and a variety of networking equipment, adding to its value in managing infrastructure security.
Pros and Cons
Pros:
- Provides continuous visibility and in-depth analytics
- Offers predictive prioritization of vulnerabilities
- Excellent for Active Directory and infrastructure security
Cons:
- Depending on the scale, deployment might require significant resources
- Interface can be complex for new users
- Pricing details are not readily available
Qualys VMDR (Vulnerability Management, Detection, and Response) is a cloud-based solution offering a unified IT security and compliance approach. Combining asset discovery and inventory with vulnerability assessment tools is perfect for complete IT asset management.
Why I Picked Qualys VMDR: I selected Qualys VMDR because it offers a full-featured platform, merging IT asset management with vulnerability detection. This tool combines inventory and vulnerability assessment to offer a thorough approach to asset management. It detects all IoT, OT, and IT assets for a complete inventory. This includes your on-premises device and application, certificate, cloud, container, and mobile device inventory. This makes Qualys VMDR best for comprehensive IT asset management.
Standout features & integrations:
Qualys VMDR's core features include IT asset discovery, inventory management, patch management, continuous monitoring, and vulnerability assessment.
Furthermore, the tool provides robust integrations with common enterprise platforms such as ServiceNow, Splunk, JIRA, and Microsoft Cloud solutions.
Pros and Cons
Pros:
- Continuous monitoring and risk assessment
- Wide range of integrations with enterprise platforms
- Comprehensive approach to asset management and vulnerability assessment
Cons:
- The tool's broad scope may introduce complexity for some users
- Pricing could be high for smaller organizations
- Annual pricing model may not suit all businesses
Other Vulnerability Management Tools
Here are some additional vulnerability management tools options that didn’t make it onto my shortlist, but are still worth checking out:
- InsightVM (Nexpose)
For real-time end-to-end visibility
- Wiz Vulnerability Management
For multi-cloud environment security
- CyCognito
For attack surface management
- Arctic Wolf
For managed detection and response services
- Frontline Vulnerability Manager
For cloud and network security integration
- Adlumin
For financial sector-focused security
- Nucleus
For multi-framework compliance management
- CYRISMA
For intuitive user interface and automated patching
- Astra Pentest
For comprehensive vulnerability scanning
- NowSecure
For mobile app security
- Resolver
Good for integrating risk management across business operations
- SanerNow
Good for combined vulnerability management and patch remediation
- ManageEngine Vulnerability Manager Plus
Good for unified vulnerability management and patching
- HostedScan
Good for providing quick and easy external vulnerability scans
- Aqua Security
Good for cloud-native application protection
- Syxsense
Good for real-time endpoint management and security
- SecOps Solution
Good for cloud-based cybersecurity and risk management
Vulnerability Management Tool Selection Criteria
When selecting the best Vulnerability Management Tools to include in this list, I considered common buyer needs and pain points like integration with existing IT infrastructure and real-time threat detection. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Identify vulnerabilities
- Prioritize threats
- Provide remediation guidance
- Offer compliance reporting
- Conduct continuous monitoring
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Cloud-native security
- Automated patch management
- Threat intelligence integration
- Real-time analytics
- Customizable dashboards
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Easy navigation
- Minimal learning curve
- Customizable user settings
- Efficient workflow integration
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Webinars and workshops
- Responsive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple support channels
- Knowledgeable support staff
- Comprehensive documentation
- Fast response times
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Feature set versus cost
- Flexible pricing plans
- Discounts for annual subscriptions
- Transparent pricing structure
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on feature effectiveness
- Comments on ease of use
- Opinions on customer support
- Value-for-money perceptions
How to Choose a Vulnerability Management Tool
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
| Scalability | Ensure the tool can grow with your business. Consider if it can handle increased data loads and more users without compromising performance. |
| Integrations | Check if the tool integrates with your existing software, such as SIEM systems, ticketing tools, and cloud services, to streamline workflows. |
| Customizability | Look for customization options that let you tailor dashboards, reports, and alerts to fit your team’s specific needs and preferences. |
| Ease of Use | Choose a tool with an intuitive interface and minimal learning curve to ensure quick adoption by your team. |
| Budget | Evaluate the cost against the features offered. Consider flexible pricing plans that fit your financial constraints and provide value for money. |
| Security Safeguards | Assess the tool's ability to protect sensitive data and comply with industry regulations, ensuring robust security measures are in place. |
| Vendor Support | Consider the vendor's reputation for customer support, including availability, response time, and the resources they provide for troubleshooting. |
| Reporting Features | Look for comprehensive reporting capabilities that provide insights into vulnerabilities and compliance, helping you make informed security decisions. |
Trends in Vulnerability Management Tool
In my research, I sourced countless product updates, press releases, and release logs from different Vulnerability Management Tools vendors. Here are some of the emerging trends I’m keeping an eye on:
- AI-Powered Threat Detection: Vendors are using artificial intelligence to enhance threat detection capabilities. AI can identify patterns and anomalies faster than traditional methods, helping teams respond to threats more quickly. Some tools are incorporating machine learning to predict potential vulnerabilities.
- Cloud-Native Security: As more businesses move to the cloud, tools are evolving to provide better cloud-native security features. This trend is crucial for companies relying heavily on cloud infrastructure, offering deeper insights into cloud-specific vulnerabilities.
- Zero Trust Security Models: More tools are adopting zero trust models, which require verification for every user and device. This approach enhances security by assuming threats could be internal or external. Vendors like Cisco are integrating zero trust principles into their platforms.
- Enhanced Reporting Capabilities: Detailed and customizable reporting is becoming more important. Users need insights into vulnerabilities and compliance status. Tools are offering more advanced reporting features to meet these demands, allowing for better risk management.
- User Behavior Analytics: Some vendors are incorporating user behavior analytics to monitor and identify unusual activities. This trend helps detect insider threats and compromised accounts, adding another layer of security for businesses.
What Are Vulnerability Management Tools?
Vulnerability management tools find, track, and help fix security weaknesses across an organization’s assets. They’re used by security teams, IT administrators, and operations staff who need to reduce risk and keep systems up to date without relying on manual checks.
Automated scanning, risk scoring, and reporting features help with spotting issues earlier, choosing what to fix first, and keeping teams informed. Overall, these tools help organizations maintain safer and more reliable systems with less manual effort.
Features of Vulnerability Management Tools
When selecting Vulnerability Management Tools, keep an eye out for the following key features:
- AI-powered threat detection: Uses artificial intelligence to quickly identify patterns and anomalies, helping teams respond to threats faster.
- Cloud-native security: Provides specialized security features for cloud environments, offering insights into cloud-specific vulnerabilities.
- Zero trust security models: Requires verification for every user and device, enhancing security by assuming all access could be a threat.
- Enhanced reporting capabilities: Offers customizable and detailed reports that provide insights into vulnerabilities and compliance status.
- User behavior analytics: Monitors and identifies unusual user activities to detect insider threats and compromised accounts.
- Risk prioritization: Helps teams focus on the most critical vulnerabilities by assessing and ranking potential threats.
- Automated patch management: Streamlines the process of applying security patches, reducing manual workload and minimizing vulnerabilities.
- Continuous monitoring: Provides ongoing assessment of the network to detect new vulnerabilities as they arise.
- Compliance reporting: Ensures that security measures meet industry standards and regulations, simplifying the compliance process.
- Customizable dashboards: Allows users to tailor their view of data and metrics to fit specific needs and preferences.
Benefits of Vulnerability Management Tools
Implementing Vulnerability Management Tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security posture: By identifying and managing vulnerabilities, these tools help protect your systems from potential threats and reduce security risks.
- Efficient risk management: Risk prioritization features allow your team to focus on the most critical vulnerabilities, ensuring resources are used effectively.
- Enhanced compliance: Compliance reporting helps you meet industry standards and regulations, simplifying audits and reducing compliance-related stress.
- Time savings: Automated patch management and continuous monitoring reduce manual tasks, freeing up your team to focus on other important activities.
- Informed decision-making: Detailed reporting and analytics provide insights that support better security decisions and strategies.
- Increased visibility: Features like cloud-native security and user behavior analytics give you a clearer view of your network and potential threats.
- Proactive threat detection: AI-powered threat detection enables faster identification and response to vulnerabilities, keeping your systems secure.
Costs and Pricing of Vulnerability Management Tools
Selecting Vulnerability Management Tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in Vulnerability Management Tools solutions:
Plan Comparison Table for Vulnerability Management Tools
| Plan Type | Average Price | Common Features |
| Free Plan | $0 | Basic vulnerability scanning, limited reporting, and community support. |
| Personal Plan | $5-$25/user/month | Standard scanning capabilities, risk prioritization, and basic compliance checks. |
| Business Plan | $30-$60/ user/month | Advanced analytics, automated patch management, and customizable dashboards. |
| Enterprise Plan | $70-$150/ user/month | Comprehensive reporting, AI-powered threat detection, and dedicated support. |
Vulnerability Management Tools (FAQs)
Here are some answers to common questions about Vulnerability Management Tools:
How do vulnerability management tools work?
Vulnerability management tools assess your network using IP scanners, network and port scanners, and more. They prioritize issues to ensure the most critical weaknesses are fixed first and suggest practical remediation steps. This process helps secure your systems by addressing vulnerabilities promptly.
What is common with most vulnerability assessment tools?
A key feature of vulnerability assessment tools is their ability to scan your systems. They run automated scans across your network, analyzing every device, application, and system for potential vulnerabilities. This automation ensures comprehensive coverage and efficient vulnerability detection.
What are the typical pricing models for vulnerability management tools?
A key feature of vulnerability assessment tools is their ability to scan your systems. They run automated scans across your network, analyzing every device, application, and system for potential vulnerabilities. This automation ensures comprehensive coverage and efficient vulnerability detection.
What is the disadvantage of an automated vulnerability tool scan?
Automated vulnerability tool scans have some drawbacks. They might not detect newly discovered vulnerabilities or complex ones that are hard to automate. This limitation means you might need manual checks to ensure comprehensive security coverage.
How often should vulnerability scans be performed?
The frequency of vulnerability scans depends on your organization’s needs and risk tolerance. Generally, it’s best to perform scans regularly, such as weekly or monthly, to ensure continuous protection against emerging threats. Regular scans help maintain a strong security posture.
Can vulnerability management tools integrate with existing security systems?
Yes, many vulnerability management tools can integrate with existing security systems. This integration allows for seamless data sharing and improved threat management. By working with your current infrastructure, these tools enhance your overall security strategy.
What's Next?
If you're in the process of researching vulnerability management tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.