10 Best Intrusion Detection and Prevention Systems Shortlist
In the fast-paced world of IT, keeping your network secure is a top priority. Intrusion detection and prevention systems (IDPS) are your first line of defense against unauthorized access and cyber threats. They help you spot vulnerabilities and act swiftly.
I've tested and reviewed a range of IDPS solutions to help you find the best fit for your team. My experience in the SaaS development industry ensures that I bring you unbiased and well-researched insights.
In this article, you'll discover top picks for intrusion detection and prevention systems, each offering unique features to address your specific needs. Let's dive into how these tools can enhance your network security and give you peace of mind.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Intrusion Detection and Prevention Systems Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for real-time monitoring and auditing | Free demo available | Pricing upon request | Website | |
| 2 | Best for advanced threat detection | Free trial + free demo available | Pricing upon request | Website | |
| 3 | Best for granular control over security policies | Not available | From $10/user/month | Website | |
| 4 | Best for integrating with existing Cisco infrastructures | Not available | From $38/user/month (billed annually) | Website | |
| 5 | Best for advanced threat protection | Not available | Pricing upon request | Website | |
| 6 | Best for integrating threat intelligence feeds | Not available | From $14/user/month | Website | |
| 7 | Best for providing a proactive security posture | Not available | Pricing upon request | Website | |
| 8 | Best for customizable intrusion detection rules | Free demo available | From $29.99/year (billed annually) | Website | |
| 9 | Best for continuous security monitoring | Not available | From $2500/user/month | Website | |
| 10 | Best for open-source network threat detection | Free | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Intrusion Detection and Prevention Systems Reviews
ManageEngine Log360 is a comprehensive security information and event management (SIEM) solution designed to provide extensive visibility and control over an organization's IT infrastructure. It integrates log management and auditing capabilities across various platforms, including Windows servers, AWS, and Azure cloud services.
Why I Picked ManageEngine Log360:
I like its real-time monitoring and auditing capabilities for Active Directory, file systems, and Windows servers. This ensures that any unauthorized access or suspicious activity is detected and addressed promptly. The platform also integrates Data Loss Prevention (DLP) and Cloud Access Security Broker (CASB) functionalities, which are crucial for monitoring data access and managing cloud security.
Another significant advantage of Log360 is its use of advanced technologies such as machine learning and user and entity behavior analytics (UEBA). These technologies enable behavior-based detection, which is essential for identifying insider threats.
Standout Features and Integrations:
The platform's integration with the MITRE ATT&CK Framework helps prioritize threats based on their position in the attack chain, enhancing threat response strategies. Additionally, the Vigil IQ engine offers advanced threat detection, investigation, and response capabilities, providing real-time visibility into security threats through correlation, adaptive alerts, and intuitive analytics.
Integrations include Microsoft Exchange, Amazon Web Services (AWS), Microsoft Entra ID, Microsoft Azure, and Active Directory.
Pros and Cons
Pros:
- User-friendly interface
- Customizable reporting options
- Comprehensive visibility across systems
Cons:
- Potential performance issues when handling large volumes of data
- Initial setup and configuration can be complex
New Product Updates from ManageEngine Log360
ManageEngine Log360 Adds New Log Source Integrations
ManageEngine Log360 introduced new integration support for NetFlow Analyzer and Firewall Analyzer, along with enhanced audit log parsing for OpManager products. The updates help teams centralize log collection and improve monitoring and analysis workflows. For more information, visit ManageEngine Log360's official site.
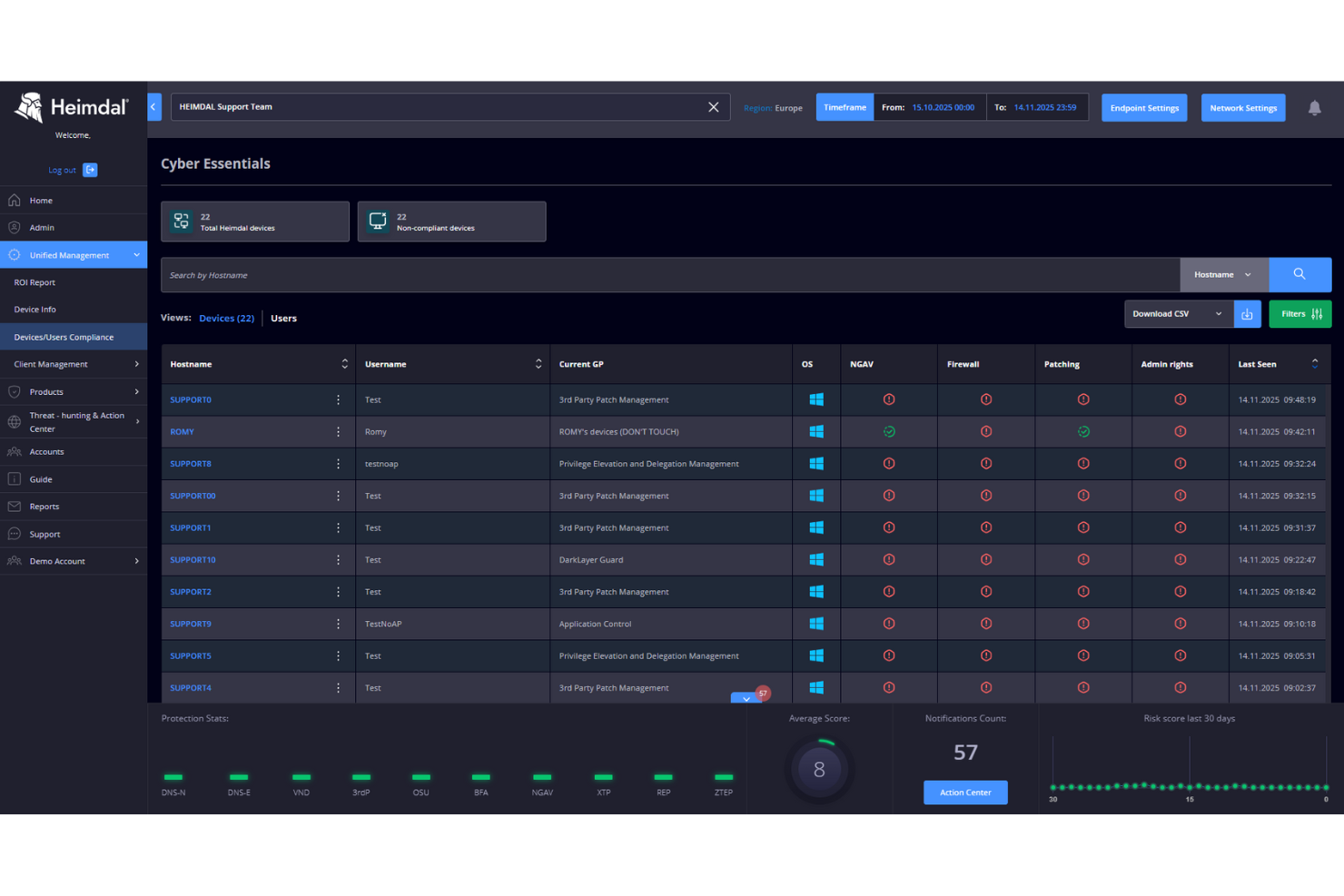
Heimdal is a cybersecurity platform designed for businesses seeking to bolster their security posture against cyber threats. It appeals to industries like healthcare, education, and SMBs, offering solutions that address compliance and data governance challenges. By integrating intrusion detection and prevention systems, Heimdal helps streamline threat detection, vulnerability management, and overall cybersecurity measures for organizations facing complex security requirements.
Why I Picked Heimdal
I picked Heimdal for its focus on advanced threat detection and response capabilities. The platform’s Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) features provide comprehensive monitoring and protection against cyber threats. Heimdal’s ability to integrate managed services and automate security processes addresses the common challenge of alert fatigue, making it a reliable choice for businesses looking to enhance their cybersecurity framework.
Heimdal Key Features
In addition to its robust detection and response capabilities, Heimdal offers a suite of additional features:
- DNS Security: Protects against DNS hijacking and ensures safe web browsing by blocking malicious sites.
- Automated Patch Management: Streamlines the patching process for software vulnerabilities, reducing the risk of exploitation.
- Ransomware Protection: Provides multi-layered defense against ransomware attacks, safeguarding critical data and systems.
- Privileged Account and Session Management: Ensures secure access control and monitoring of privileged accounts to prevent unauthorized access.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
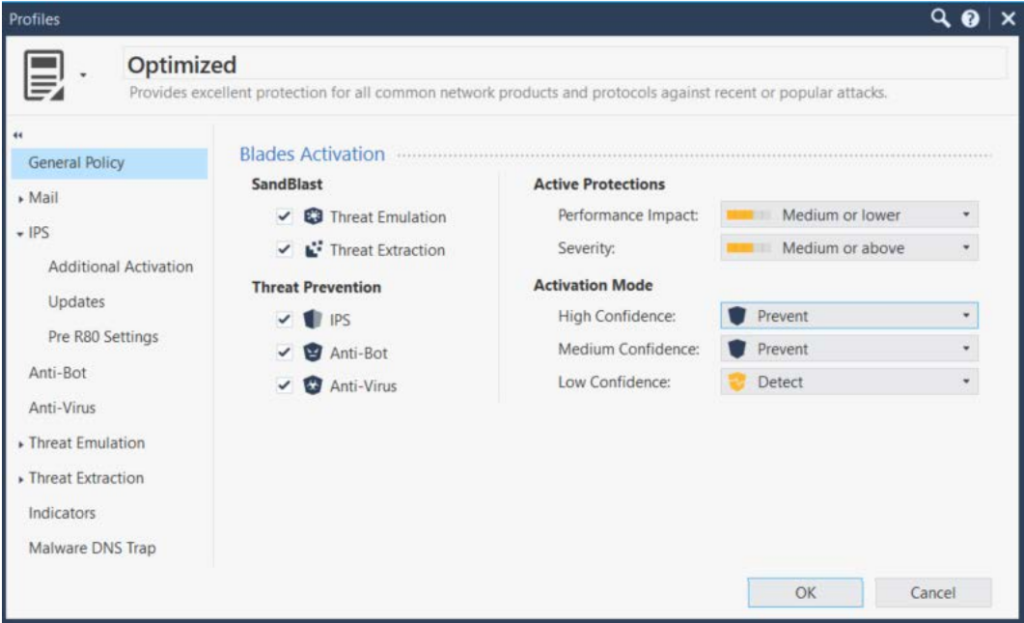
Check Point IPS acts as a vigilant sentinel, providing robust security solutions to protect your digital landscape. The tool's ability to offer granular control over security policies is a critical strength that sets it apart from the competition.
Why I Picked Check Point IPS:
In my quest for top-tier intrusion detection and prevention systems, Check Point IPS caught my eye for its impressive policy control features. It shines for its ability to offer precise, granular control over security policies, effectively mitigating potential vulnerabilities.
This granular control allows businesses to finely tune their security posture, making it the best choice for organizations requiring a customizable security policy.
Standout Features and Integrations:
Check Point IPS comes loaded with several potent features, including comprehensive threat intelligence, built-in antivirus, anti-bot, and sandboxing. It’s also an intuitive management console and an automated policy tuner. The threat intelligence feature provides in-depth information on possible threats, while the automated policy tuner streamlines policy management, ensuring efficient operation.
Check Point IPS also integrates smoothly with several prominent platforms. Notably, it connects with existing Check Point security solutions, allowing for unified threat management and streamlined operations.
Pros and Cons
Pros:
- Efficient integrations with other Check Point security solutions
- Granular control over security policies
- Detailed threat intelligence
Cons:
- Could be complex for smaller organizations or those new to cybersecurity
- Requires a minimum of 5 seats
- High starting price point
Cisco Secure Firewall provides robust threat defense and high visibility, effectively safeguarding network infrastructures from potential security breaches. Given its deep integration capabilities with existing Cisco infrastructures, it serves as an invaluable addition to the cybersecurity toolkit for companies already leveraging Cisco's broad range of products.
Why I Picked Cisco Secure Firewall:
In the process of selecting the right tools, the integration capabilities of Cisco Secure Firewall with existing Cisco infrastructures stood out. It provides a compelling advantage for businesses that rely heavily on Cisco's ecosystem.
Thus, I determined it to be the "best for integrating with existing Cisco infrastructures" based on its compatibility and the operational ease it brings to an already familiar environment.
Standout Features and Integrations:
Cisco Secure Firewall incorporates features such as next-generation intrusion preventions system (NGIPS), advanced malware protection, and URL filtering to protect the network. The most notable feature is its threat intelligence supported by Cisco Talos, one of the largest commercial threat intelligence teams in the world.
Cisco Secure Firewall integrates seamlessly with other Cisco security products, including SecureX platform, Cisco Secure Endpoint, SolarWinds security event manager, and Cisco Secure Email gateways, providing a comprehensive security solution.
Pros and Cons
Pros:
- Comprehensive security features such as intrusion prevention and malware protection
- Access to robust threat intelligence from Cisco Talos
- Excellent integration with existing Cisco infrastructures
Cons:
- Limited integration with non-Cisco products
- Complexity may require IT expertise to manage effectively
- Pricing can be high, especially for small businesses
Trend Micro TippingPoint is a network security solution providing robust protection against advanced threats. It brings real-time network protection and operational simplicity to your diversified network environment, making it particularly adept at advanced threat protection.
Why I Picked Trend Micro TippingPoint:
TippingPoint earned a spot on this list because of its specialized capabilities for protecting networks against advanced threats. The combination of threat intelligence and network-level protection sets it apart from other cybersecurity tools.
When considering the tool's best use case, advanced threat protection is a standout due to its comprehensive approach to managing both known and unknown vulnerabilities.
Standout Features and Integrations:
TippingPoint offers several notable features including high-performance inspection, ThreatLinQ Security Intelligence, and customizable dashboards for network visibility. Furthermore, its Advanced Threat Protection Framework ensures a proactive security stance.
As for integrations, TippingPoint fits seamlessly into Trend Micro's security ecosystem. It integrates with other Trend Micro solutions, providing a unified approach to security. Additionally, it supports integrations with third-party vendors like SIEM systems for centralized security management.
Pros and Cons
Pros:
- Seamless integration with other Trend Micro solutions
- High-performance network inspection
- Comprehensive advanced threat protection framework
Cons:
- Might be overkill for smaller organizations with less complex network infrastructures
- May require technical expertise to manage effectively
- Pricing information is not readily available
Best for integrating threat intelligence feeds
Palo Alto Networks Next-Generation Firewall (NGFW) sets the benchmark in securing your digital domain name system (DNS), boasting powerful intrusion detection and prevention capabilities. Its standout feature is its ability to seamlessly integrate threat intelligence feeds, a unique capability that makes it a strong contender in the cybersecurity realm.
Why I Picked Palo Alto Networks NGFW:
When I first evaluated Palo Alto Networks NGFW, I was drawn to its unrivaled ability to integrate threat intelligence feeds. This feature, in my opinion, sets it apart from the crowd, offering a distinct advantage for organizations that heavily rely on threat intelligence for proactive defense.
Given the escalating cybersecurity threat landscape, the capacity to integrate threat intelligence feeds is invaluable, which is why Palo Alto Networks NGFW stands as the best option for this purpose.
Standout Features and Integrations:
Palo Alto Networks NGFW boasts a suite of impressive features, including application identification, user-based policy enforcement, and multi-factor authentication. Its application identification feature offers an in-depth view of network traffic, while the multi-factor authentication feature adds an extra layer of security.
In terms of integrations, Palo Alto Networks NGFW smoothly integrates with a wide variety of platforms, including popular cloud service providers. These integrations help organizations extend their security posture beyond the traditional network boundary and into the cloud.
Pros and Cons
Pros:
- Provides excellent cloud integrations
- Comes with a suite of impressive features
- Integrates well with threat intelligence feeds
Cons:
- Interface may be complex for newcomers to cybersecurity
- Requires a minimum of 10 seats
- High starting price point
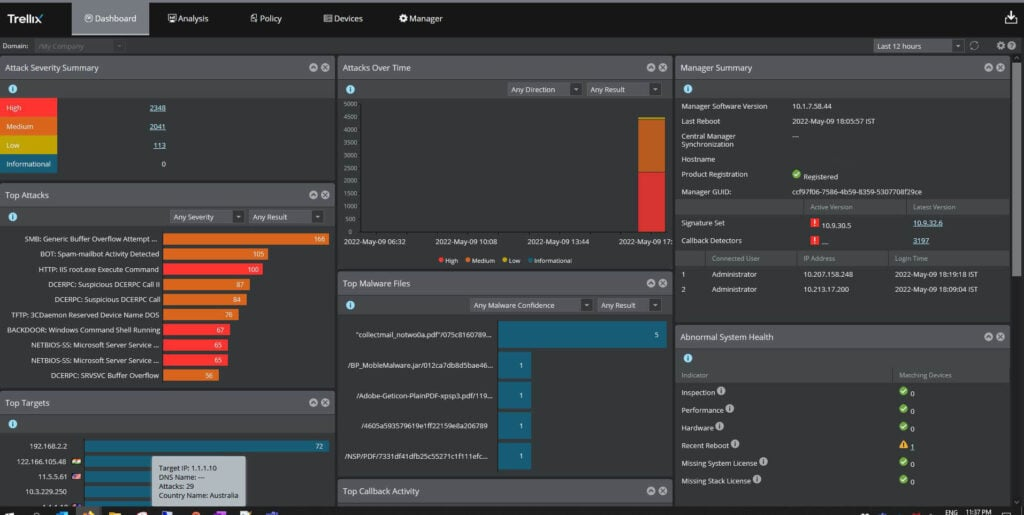
Trellix Intrusion Prevention System (IPS) is a cybersecurity tool that aims to protect enterprise networks from various threats. By detecting and preventing intrusions, it helps organizations maintain a proactive security posture.
Why I Picked Trellix Intrusion Prevention System:
I selected Trellix IPS for this list because of its strong emphasis on proactive protection. Its unique approach to threat detection and prevention helps set it apart from many other cybersecurity tools.
With its ability to maintain a proactive security posture, it's best suited for organizations looking to take a preemptive approach to cybersecurity, thwarting potential threats before they cause harm.
Standout Features and Integrations:
Trellix IPS is built with several key features that help establish a proactive security stance. Its in-depth traffic analysis, advanced threat detection algorithms, and real-time response capabilities enable comprehensive protection.
For integrations, the Trellix IPS solution works well with the broader Trellix platform, ensuring organizations can leverage a unified, layered security strategy. It can also integrate with third-party tools such as McAfee ePO for an expanded, tailored security environment.
Pros and Cons
Pros:
- Easy integration with Trellix platform and third-party tools
- Real-time response capabilities
- Proactive security approach
Cons:
- Reliance on other Trellix products for full functionality
- The learning curve may be steep for those unfamiliar with intrusion prevention systems
- Lack of transparent pricing information
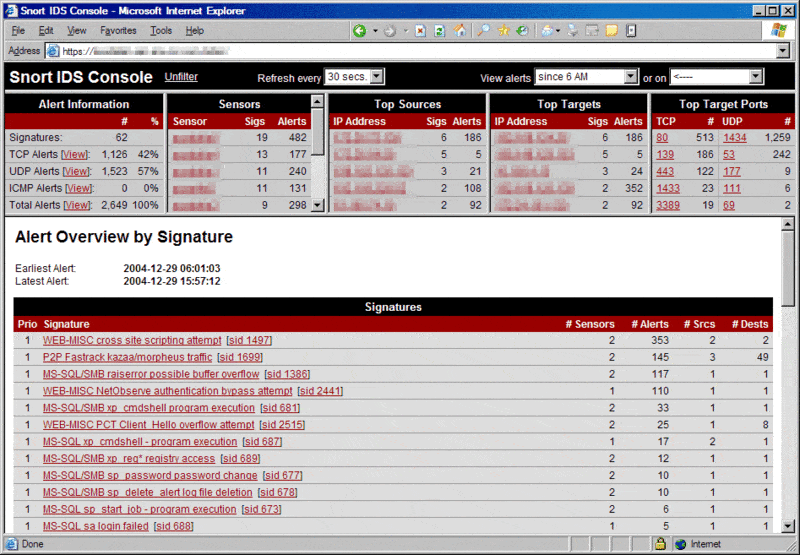
Snort is an open-source network intrusion detection system (IDS) designed to identify and prevent network intrusions. It allows users to create and customize rules for detecting suspicious activities, making it excellent for organizations that require adaptable and tailored intrusion detection solutions.
Why I Picked Snort:
I chose Snort because of its high degree of customization. The ability to set specific detection rules differentiates Snort from many intrusion detection tools, allowing organizations to refine their network security based on their unique requirements.
Therefore, it stands out as the best tool for customizable intrusion detection rules.
Standout Features and Integrations:
Snort's key feature is its rule-based detection system, which allows users to define unique rules for detecting suspicious network activity. In addition, its real-time traffic analysis and packet logging functionality contribute to a comprehensive intrusion detection solution.
Integration-wise, Snort has been built to function smoothly with other security and networking tools. It is often used in combination with other network monitoring tools to provide an integrated security solution.
Pros and Cons
Pros:
- Can integrate with other network monitoring tools
- Real-time traffic analysis
- Highly customizable intrusion detection rules
Cons:
- Might be overwhelming for small networks due to extensive features
- Free version lacks commercial support
- Might require advanced technical knowledge to fully utilize
Best for continuous security monitoring
Alert Logic MDR offers an integrated solution that pairs advanced technology with human expertise to deliver continuous security monitoring. It provides real-time threat detection and incident response services, offering businesses peace of mind in their cybersecurity operations.
Why I Picked Alert Logic MDR:
Alert Logic MDR grabbed my attention due to its unique blend of technology and human expertise. I believe the value of human involvement in identifying complex threats complements the speed and precision of automated systems, which makes Alert Logic MDR stand out.
Considering its strength in providing continuous, round-the-clock security monitoring, I determined it to be the "best for continuous security monitoring".
Standout Features and Integrations:
Alert Logic MDR includes features such as asset discovery, vulnerability assessment, intrusion detection, log management, and incident management. The most impressive part is its threat intelligence backed by a global team of security experts who actively monitor and respond to threats.
Integrations play a key role in Alert Logic MDR's functionality. It works well with popular cloud platforms like AWS, Azure, and Google Cloud, ensuring smooth operations and high security in these environments.
Pros and Cons
Pros:
- Integrates well with popular cloud platforms
- Provides a blend of technology and human expertise
- Offers continuous, round-the-clock security monitoring
Cons:
- Requires a minimum commitment period for contracts
- Does not offer a free trial or free plan
- High starting price may be a barrier for small businesses
Suricata takes a robust stand in the realm of intrusion detection and prevention systems with its open-source capabilities. It's specially crafted to provide state-of-the-art network threat detection, ensuring security teams get the insights they need.
Why I Picked Suricata:
Among the reasons why Suricata made it to my list, the first that stands out is its open-source nature. This means that it provides a platform for continuous updates and improvements driven by an active community of security experts.
I identified Suricata as "best for open-source network-based threat detection" because it combines affordability with an ever-evolving set of features to stay ahead of security threats.
Standout Features and Integrations:
Suricata comes with key features such as real-time intrusion detection, network security monitoring, and offline PCAP processing. Its inline intrusion prevention ability can halt malicious activity at the network level before it impacts the systems.
Suricata boasts a high degree of compatibility with a range of log management and SIEM systems like ELK Stack, OSSEC HIDS, and Splunk, allowing for easier assimilation of data for security teams.
Pros and Cons
Pros:
- Compatible with multiple SIEM systems
- Real-time intrusion detection capability
- Open-source with an active community for continuous updates
Cons:
- Being open-source, it requires community input for new features, which may take time
- Might require some technical know-how to set up and configure
- Professional support comes at an additional cost
Other Intrusion Detection and Prevention Systems
Below is a list of additional intrusion detection and prevention systems that I shortlisted, but did not make it to the top 10. Definitely worth checking them out.
- Zeek
For extensive network visibility and diagnostics
- Apiiro
For providing a risk-based approach to security
- Nanitor
For network vulnerability scanning
- Quantum Armor
For predictive breach detection capabilities
- GFI Languard
Good for network security, patch management, and vulnerability scanning
- Corelight
Good for providing network visibility with the help of the Zeek framework
- Security Onion
Good for open-source intrusion detection, network security monitoring, and log management
- Sophos Firewall
Good for integrating network protection with endpoint security
- Fidelis Network
Good for deep visibility into network activities for threat hunting
- IBM Security QRadar Suite
Good for detecting unusual network behavior through advanced analytics
- Dell Security
Good for enterprise-level protection against cybersecurity threats
- FortiGate
Good for combined firewall, VPN, and security services in a single device
- SonicWall Network Security Appliance (NSA)
Good for mid-range network security and intrusion prevention
- Juniper Networks® SRX Series Firewalls
Good for scalable, high-performance network security
- Trustwave IDS/IPS
Good for organizations looking for data privacy compliance solutions
Related Reviews
Intrusion Detection and Prevention System Selection Criteria
When selecting the best intrusion detection and prevention systems to include in this list, I considered common buyer needs and pain points like real-time threat detection and ease of integration with existing infrastructure. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect unauthorized access
- Monitor network traffic
- Alert on suspicious activity
- Log security events
- Prevent known threats
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Integration with other security tools
- Machine learning capabilities
- Cloud-based deployment options
- Customizable alert settings
- Compliance reporting tools
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Ease of navigation
- Customizable dashboards
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Webinars for new users
- Chatbot assistance
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple support channels
- Knowledge base resources
- Response time to queries
- Availability of dedicated account managers
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Licensing flexibility
- Feature-to-price ratio
- Availability of free trials
- Discounts for long-term contracts
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Ease of setup feedback
- Performance satisfaction
- Customer service experiences
- Long-term user feedback
- Comparisons to competitors
How to Choose an Intrusion Detection and Prevention System
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the system grow with your business? Consider future expansion and user limits. |
| Integrations | Does it work with your current tools? Check compatibility for seamless operations. |
| Customizability | Can you tailor the system to fit your needs? Look for flexible settings and options. |
| Ease of use | Is the system intuitive for your team? Consider the learning curve and interface. |
| Implementation and onboarding | How quickly can you get started? Evaluate setup time and available support. |
| Cost | Does it fit your budget? Compare pricing models and hidden fees. |
| Security safeguards | Are there strong security measures? Ensure compliance with industry standards. |
What Is an Intrusion Detection and Prevention System?
Intrusion detection and prevention systems are tools designed to monitor network traffic for suspicious activities and unauthorized access. IT professionals and security teams use these tools to enhance network security and protect sensitive data.
Real-time threat detection, integration with existing security tools, and customizable alerts help with identifying threats and responding quickly. Overall, these tools provide essential protection for maintaining secure and reliable network operations.
Features
When selecting intrusion detection and prevention systems, keep an eye out for the following key features:
- Real-time threat detection: Monitors network traffic continuously to identify and alert on suspicious activities immediately.
- Integration capabilities: Works seamlessly with existing security tools to provide a unified security strategy.
- Customizable alerts: Allows users to set specific triggers and notifications for different types of threats.
- Scalability: Supports business growth by accommodating increased network size and user demands without performance loss.
- User-friendly interface: Offers an intuitive layout that simplifies navigation and reduces the learning curve for new users.
- Compliance reporting: Generates reports to help meet industry standards and regulatory requirements.
- Machine learning capabilities: Uses advanced algorithms to adapt and improve threat detection over time.
- Cloud-based deployment: Provides flexible access and management of security features from anywhere.
- 24/7 customer support: Ensures assistance is available whenever issues or questions arise.
- Training resources: Offers tutorials, webinars, and other educational materials to help users maximize the tool's potential.
Benefits
Implementing intrusion detection and prevention systems provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: By detecting threats in real time, these systems help prevent unauthorized access and data breaches.
- Operational efficiency: Integration capabilities allow your team to manage security within existing workflows, saving time and effort.
- Regulatory compliance: Compliance reporting features assist in meeting industry regulations and standards.
- Scalability: As your business grows, these systems can scale to meet increased demands without compromising performance.
- Cost savings: By preventing breaches and minimizing downtime, these tools help reduce potential financial losses.
- Informed decision-making: Customizable alerts and detailed reports provide valuable insights to guide your security strategy.
- User empowerment: Training resources and user-friendly interfaces make it easier for your team to effectively use the system.
Costs & Pricing
Selecting intrusion detection and prevention systems requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in intrusion detection and prevention systems solutions:
Plan Comparison Table for Intrusion Detection and Prevention Systems
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited alerts, and community support. |
| Personal Plan | $5-$25/user/month | Real-time monitoring, customizable alerts, and basic reporting. |
| Business Plan | $30-$60/user/month | Advanced analytics, integration capabilities, and compliance reporting. |
| Enterprise Plan | $70-$150/user/month | Full customization, dedicated account support, and machine learning capabilities. |
Intrusion Detection and Prevention Systems FAQs
How do intrusion detection systems handle encrypted traffic?
Encrypted traffic can be challenging for IDS to analyze, as encryption hides the content of data packets. Some systems may decrypt traffic for inspection, but this can impact performance. Consider solutions that balance security and speed for encrypted data.
Can intrusion detection systems prevent attacks?
IDS itself doesn’t prevent attacks; it alerts you to potential threats. To block attacks, integrate IDS with an intrusion prevention system (IPS), which actively takes measures to stop threats based on IDS alerts.
What detection methods do most IDPS platforms use?
Most IDPS platforms use signature-based, anomaly-based, or hybrid detection methods. Signature-based detection matches known attack patterns, while anomaly-based models flag behavior outside normal baselines. The combination of both often determines how effective and flexible the system will be in a real-world network.
Are these systems deployed inline or out-of-band?
Some platforms offer inline deployment, where they can actively block traffic, while others are out-of-band and focus on detection only. Many support both modes, but performance and complexity may differ. Inline systems often require more careful configuration to avoid latency or disruption.
How do these platforms log and store data?
IDPS tools typically log all detected events, including source IPs, timestamps, payloads, and attack types. Storage options vary—some tools store logs locally, while others integrate with centralized SIEMs. Retention policies and log formats can impact how easily data can be analyzed or audited.
What’s Next:
If you're in the process of researching intrusion detection and prevention systems, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.