10 Best Network Intrusion Detection Systems Shortlist
Here's my pick of the 10 best software from the 18 tools reviewed.
A network intrusion detection system (NIDS) helps security teams spot suspicious network activity and quickly respond before an attack can spread.
Many teams look for a NIDS when they face challenges like too many false positives, limited visibility into east-west traffic, or slow detection of advanced threats. Without clear, timely alerts, it’s easy to miss real attacks or waste time chasing harmless events.
I’ve worked with security teams to deploy and fine-tune NIDS solutions that actually balance detection with practicality, making sure they fit into real workflows without adding noise. This guide is built on those experiences to help you choose a system that strengthens your defenses and supports how your team works.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Network Intrusion Detection Systems Summary
This comparison chart summarizes pricing details for my top network intrusion detection system selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for cloud-native cybersecurity protection | Free trial available | From $59.99/device (billed annually) | Website | |
| 2 | Best for broad-based cybersecurity protection | Not available | Pricing upon request | Website | |
| 3 | Best for threat intelligence and response | Not available | Pricing upon request | Website | |
| 4 | Best for firewall policy management | Free demo available | From $33/user/month | Website | |
| 5 | Best for DDoS attack mitigation | Not available | Pricing upon request | Website | |
| 6 | Best for AI-driven threat detection | Free 30-day trial | Pricing upon request | Website | |
| 7 | Best for open-source enthusiasts | Free demo available | From $29.99/year (billed annually) | Website | |
| 8 | Best for unified security management | Not available | Open source project and available for free | Website | |
| 9 | Best for automated real-time attack detection | Free demo available | Pricing upon request | Website | |
| 10 | Best for comprehensive network analysis | Free plan available | From $9/user/month (billed annually) | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Network Intrusion Detection Systems Reviews
Below are my detailed summaries of the best network intrusion detection systems that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
CrowdStrike Falcon is a cybersecurity platform designed to provide comprehensive cloud-native protection. With the ability to safeguard cloud-based infrastructures from various cyber threats, CrowdStrike Falcon is the ideal choice for organizations prioritizing robust, cloud-native cybersecurity defenses.
Why I Picked CrowdStrike Falcon:
I selected CrowdStrike Falcon because it demonstrates a strong focus on cloud-native protection. The tool's ability to leverage the power of AI to detect and respond to threats in real-time places it in a unique position compared to other cybersecurity solutions. Hence, it is my determined opinion that CrowdStrike Falcon is the "Best for..." cloud-native cybersecurity protection.
Standout features and integrations:
Among the most significant features of CrowdStrike Falcon are its artificial intelligence-based threat detection, real-time threat response, and comprehensive visibility across cloud networks. It also boasts a cloud-based architecture, making it scalable and easy to deploy. In terms of integrations, CrowdStrike Falcon can connect with a variety of platforms and tools, including major cloud providers like AWS, GCP, and Azure, as well as SIEM solutions and IT operations tools.
Pros and Cons
Pros:
- Integrates with a wide variety of platforms and tools
- AI-powered real-time threat detection and response
- Comprehensive cloud-native protection
Cons:
- May require advanced technical knowledge for effective use
- Requires annual commitment for pricing
- Pricing can be high for small to mid-size organizations
Symantec Network Security, a product by Broadcom, delivers a comprehensive set of cybersecurity solutions that secure the entirety of an enterprise's network. It offers a holistic approach to network security, making it optimal for organizations seeking broad-based cybersecurity protection.
Why I Picked Symantec Network Security:
During my evaluation, Symantec Network Security stood out due to its expansive, all-encompassing approach to cybersecurity. Unlike other solutions that may focus on specific aspects of security, Symantec provides a wide-ranging suite of tools for robust protection. With this comprehensive perspective in mind, I determined that Symantec Network Security is "Best for..." broad-based cybersecurity protection.
Standout features and integrations:
Symantec Network Security offers a broad array of features, including intrusion prevention, web filtering, and malware analysis. It's known for its integration capabilities with a wide variety of systems, enabling businesses to protect their existing infrastructure without major changes.
Pros and Cons
Pros:
- Strong focus on both detection and prevention of threats
- Seamless integration with a variety of systems
- Offers a comprehensive set of cybersecurity solutions
Cons:
- Integration with non-Broadcom products may require additional configuration
- May be overly complex for smaller organizations
- No public pricing information available
TippingPoint is a network security solution that focuses on providing a proactive approach to threat intelligence and response. With its advanced threat protection system, TippingPoint can identify, analyze, and react to potential threats in real time, making it an excellent choice for organizations prioritizing threat intelligence and response.
Why I Picked TippingPoint:
In my selection process, I was impressed by TippingPoint's robust capabilities in threat intelligence and response. Its proactive approach and real-time analysis stand out in the realm of network security. Considering these aspects, I firmly believe TippingPoint is the "Best for..." threat intelligence and response.
Standout Features and Integrations:
TippingPoint offers robust features like the Threat Protection System and the Digital Vaccine service for real-time threat intelligence. It integrates well with other security products from TrendMicro, providing an interconnected defense system.
Pros and Cons
Pros:
- Real-time threat analysis and protection
- Integrates well with other TrendMicro products
- Proactive approach to threat intelligence and response
Cons:
- Lack of integrations with non-TrendMicro products
- Could have a steep learning curve for beginners
- Pricing information isn't publicly available
ManageEngine Firewall Analyzer is a firewall log management tool that helps you audit rules, monitor VPN and proxy activity, and run compliance checks—all without needing extra hardware. While it’s not a traditional intrusion detection system (NIDS), it gives you visibility into traffic behaviour and rule usage that can help you spot suspicious patterns and tighten your firewall configurations accordingly.
Why I Picked ManageEngine Firewall Analyzer:
I picked this tool for teams that want deeper insight into how their firewall policies actually function. If you're tasked with managing a multi-vendor firewall setup and need to make sure outdated or overly permissive rules don’t slip through, this tool gives you the visibility to do just that. It’s also helpful if you’re under pressure to produce compliance reports or track changes across multiple devices. Just keep in mind: while it supports real-time alerts for config changes and usage trends, it doesn't analyze raw network packets the way a NIDS does.
Standout features & integrations:
Firewall Analyzer lets you group internet activity by user category (like streaming or file sharing), flagging higher-risk behaviour for review. You can drill into VPN session logs by user or group and get bandwidth data for proxies too. For audits, it generates reports based on standards like PCI-DSS and ISO 27001. It integrates with other ManageEngine tools like Log360, Endpoint Central, Patch Manager Plus, and M365 Security Plus, giving you a broader security stack if needed.
Pros and Cons
Pros:
- Provides detailed insights into firewall traffic and user activity
- VPN tracking and bandwidth management
- Real-time monitoring capabilities help identify unusual traffic patterns
Cons:
- Requires regular updates and maintenance
- Slower patch responses for third-party software vulnerabilities
Radware DefensePro is a renowned cybersecurity solution that specializes in mitigating Distributed Denial of Service (DDoS) attacks. With its focus on ensuring uninterrupted service availability even under severe DDoS attacks, it earns its place as an optimal choice for organizations seeking dedicated DDoS protection.
Why I Picked Radware DefensePro:
I selected Radware DefensePro for its dedicated and robust approach to combating DDoS attacks. It has the ability to detect and mitigate multi-vector DDoS attacks in real time, which makes it distinct in the cybersecurity landscape. Therefore, based on my judgment, Radware DefensePro is the "Best for..." organization looking to ensure service availability during DDoS attacks.
Standout features and integrations:
Key features of Radware DefensePro include real-time DDoS attack detection, multi-layered protection, and machine-learning-powered threat analysis. The system’s ability to protect against a wide variety of attacks, from volumetric to encrypted attacks, is impressive. As for integrations, Radware DefensePro can be incorporated into a broader Radware security ecosystem, interfacing with tools such as Radware's Alteon and AppWall for a comprehensive security setup.
Pros and Cons
Pros:
- Can integrate with other Radware security tools for a holistic data security approach
- Real-time detection and mitigation of attacks
- Dedicated protection against multi-vector DDoS attacks
Cons:
- Its comprehensive features may present a steep learning curve for users
- Could be over-specialized for organizations seeking a more general security solution
- Pricing information is not transparently provided
Darktrace delivers enterprise-wide cyber defense through AI technology and machine learning. Its focus on providing organizations with self-learning AI allows for the detection of unusual network behavior and emerging threats, making it an ideal choice for proactive and AI-driven threat detection.
Why I Picked Darktrace:
In selecting Darktrace for this list, I considered its unique approach to threat detection, leveraging self-learning AI that adapts and learns from your network behavior. This autonomous response technology allows it to react to threats in seconds, making it a stand-out choice. In my opinion, Darktrace is "Best for..." AI-driven threat detection due to this focus on machine learning and quick response.
Standout Features and Integrations:
Darktrace's key features include its Enterprise Immune System, which learns normal 'patterns of life' to detect deviations indicative of a threat, and Darktrace Antigena, an AI response solution that reacts to in-progress cyber threats. Regarding integrations, Darktrace can work alongside your existing security tools, enhancing your defenses by integrating its AI-powered insight into other parts of your security ecosystem.
Pros and Cons
Pros:
- Can integrate with existing security tools
- Autonomous response technology reacts to threats in real-time
- Leverages self-learning AI for adaptive threat detection
Cons:
- Could be overkill for smaller organizations
- May have a steep learning curve for non-technical users
- Pricing isn't transparent
Snort is a robust open-source network intrusion detection system that inspects network traffic in real-time to detect potential threats. As an open-source tool, Snort offers flexible, customizable features that cater well to tech-savvy users who prefer hands-on control over their network security.
Why I Picked Snort:
I chose Snort because of its rich heritage and strong community support, making it a tried-and-true solution in the realm of open-source network security. Its openness means users have the freedom to tweak the system as they see fit, providing a level of customization that is hard to match. That's why I believe it is best for open-source enthusiasts who appreciate control and flexibility.
Standout Features and Integrations:
Snort boasts a rich array of features, including real-time traffic analysis and packet logging. It utilizes a variety of detection methods, such as signature, anomaly-based detection, and policy-based techniques, to provide comprehensive security. As for integrations, Snort benefits from its open-source nature, boasting compatibility with a wide range of other security tools. Its flexibility allows it to work well with systems like Security Onion and various SIEM systems for enhanced threat detection and response.
Pros and Cons
Pros:
- Comprehensive detection methods
- High level of customization
- Strong community support
Cons:
- Up-to-date rule sets come at a cost
- Requires manual setup and configuration
- Steep learning curve for newcomers
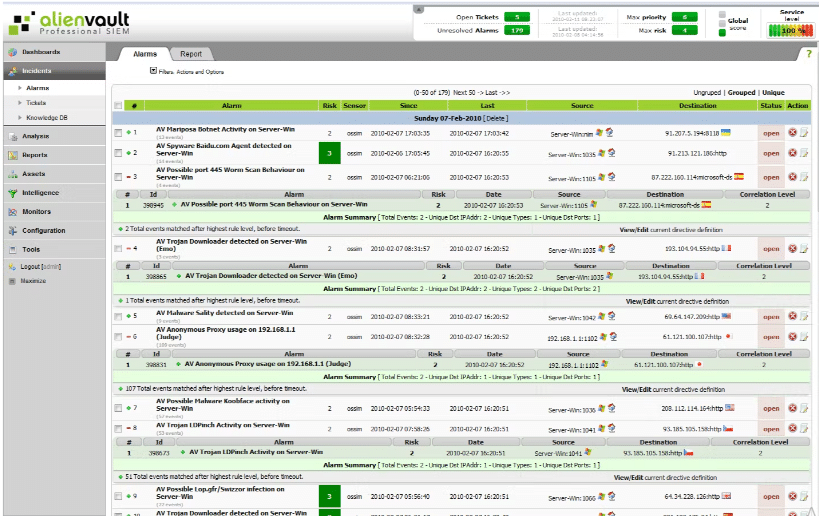
AlienVault OSSIM is an open-source security information and event management (SIEM) system that combines network visibility, log management, intrusion detection, and compliance into one unified platform. It's perfect for those seeking a centralized security platform to manage various security tasks simultaneously.
Why I Picked AlienVault OSSIM:
AlienVault OSSIM made my list because of its ability to merge diverse security technologies into a single, unified platform. It sets itself apart with a broad range of integrated security functionalities, including asset discovery, vulnerability assessment, and intrusion detection. Thus, it's best for organizations in need of unified security management.
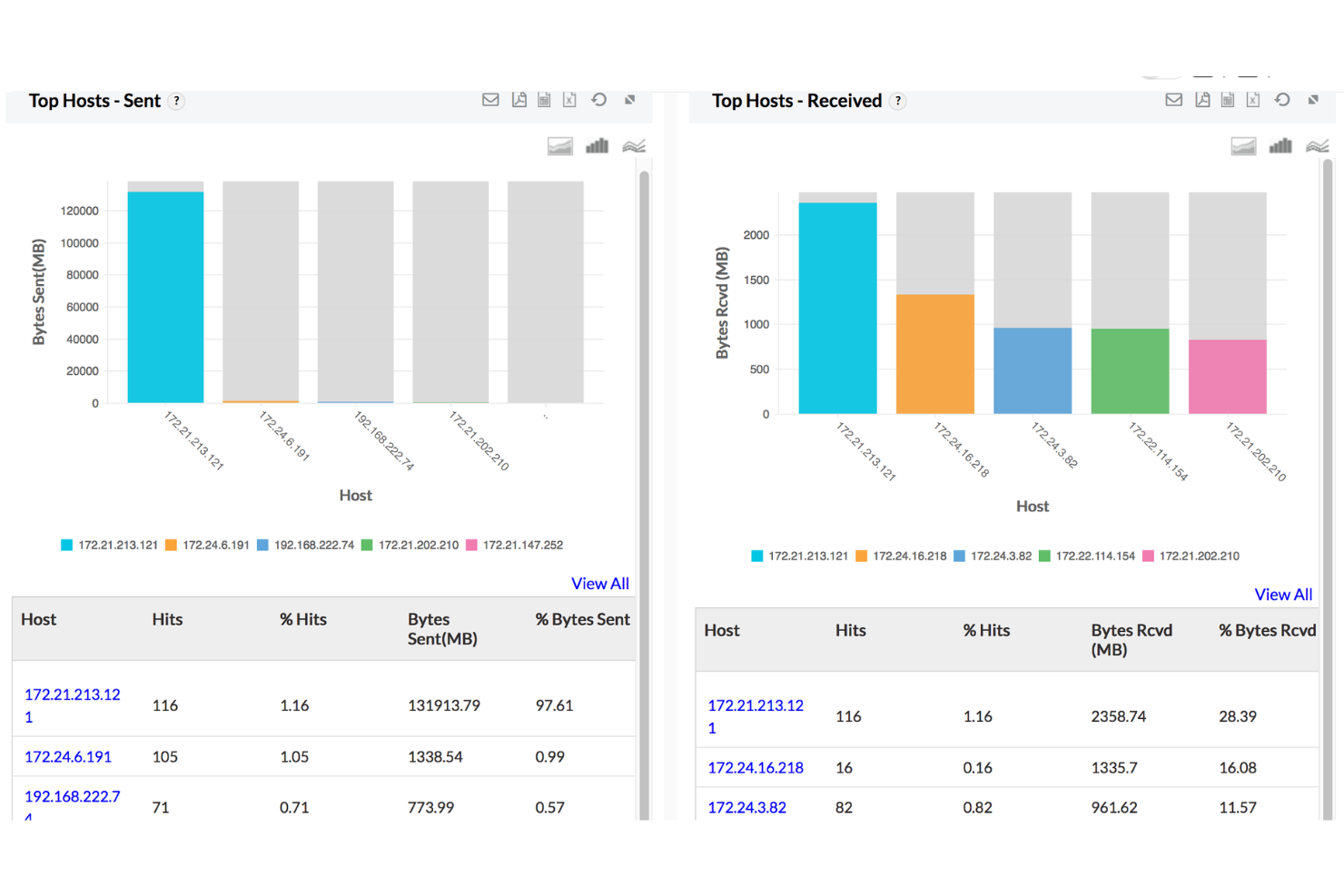
Standout Features and Integrations:
AlienVault OSSIM stands out with its features, such as asset discovery, vulnerability assessment, and behavioral monitoring. Its integrated threat intelligence from AlienVault Labs and the AlienVault Open Threat Exchange (OTX) provides real-time information on emerging threats. As for integrations, it allows you to centralize data from existing security tools for better visibility and control.
Pros and Cons
Pros:
- Centralizes data from multiple sources for better visibility
- Provides real-time threat intelligence
- Integrates multiple security functionalities into a single platform
Cons:
- Commercial support costs extra
- Some advanced features only available in the paid version
- May require technical expertise to fully utilize
Vectra AI is a network detection and response (NDR) solution that harnesses artificial intelligence to identify and combat threats in real-time. Given its emphasis on automation and immediate threat identification, it stands as a prime choice for organizations seeking effective real-time attack detection.
Why I Picked Vectra AI:
I chose Vectra AI due to its strong focus on real-time, automated threat detection. The tool applies AI to detect anomalous network behavior promptly and automatically, which sets it apart in the field of network security tools. Thus, in my opinion, Vectra AI is "Best for..." organizations that prioritize swift, automated detection of potential threats.
Standout features and integrations:
Vectra AI's standout features include its real-time threat detection, AI-driven threat hunting, and its capability for automated response. It provides network-based detection, enriches security incidents with unique context, and offers robust reporting.
Importantly, Vectra AI integrates well with security information and event management (SIEM) solutions like Splunk, QRadar, and Chronicle, as well as endpoint detection and response (EDR) systems such as Crowdstrike and Carbon Black.
Pros and Cons
Pros:
- Provides valuable integrations with SIEM and EDR solutions
- Utilizes AI for efficient threat hunting and response
- Robust real-time threat detection
Cons:
- Its comprehensive functionality may be overwhelming for small organizations
- The tool's high level of automation might limit manual control
- Pricing is not directly disclosed, which can be unclear for potential customers
Zeek, formerly known as Bro, is an open-source network intrusion detection system that provides a high-powered platform for network traffic analysis. Its ability to transform raw network traffic into high-fidelity logs, files, and custom insights makes it an excellent choice for those looking for an in-depth understanding of their network.
Why I Picked Zeek:
When I was selecting tools, Zeek caught my eye due to its unique focus on transforming network traffic data into comprehensive, actionable information. This thorough analysis is the cornerstone of Zeek's capability, providing users with rich insights about their networks that many other NIDS don't offer. Therefore, I deem Zeek as best for comprehensive network analysis, given its superior data transformation capabilities.
Standout Features and Integrations:
Zeek's script interpreter is one of its most distinguishing features. It allows users to write scripts that guide the analysis of network traffic, providing unparalleled control over the process. Additionally, Zeek offers file extraction capabilities, further enhancing its analysis. As an open-source platform, Zeek can integrate with a variety of other tools. Most notably, it often pairs with ELK Stack for log management, enhancing its capabilities for thorough network analysis.
Pros and Cons
Pros:
- Extracts files from network traffic for in-depth review
- High flexibility through its scripting language
- Rich, comprehensive network traffic analysis
Cons:
- Commercial support and training come at an additional cost
- No built-in GUI, relies on third-party tools
- Requires technical expertise to use effectively
Other Network Intrusion Detection System Tools
Here are some additional network intrusion detection system options that didn’t make it onto my shortlist, but are still worth checking out:
- Corelight
For enterprises seeking scalability
- Security Onion
For integrated defense toolkit
- RSA NetWitness
For forensic investigation capabilities
- PRTG Network Monitor
Good for comprehensive network monitoring and fault detection
- Cynet 360
Good for advanced threat detection and response
- WatchGuard Firebox
Good for unified security platform management
- Network Detective Pro
Good for network risk assessment and management
- VM-Ware NXS
Good for multi-cloud networking and security
Selection Criteria
When selecting the best network intrusion detection system to include in this list, I considered common buyer needs and pain points like scalability and ease of integration. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect unauthorized access
- Monitor network traffic
- Alert on suspicious activities
- Log and report security incidents
- Identify malware threats
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- AI-driven threat analysis
- Integration with third-party security tools
- Real-time data visualization
- Customizable detection rules
- Cloud-based deployment options
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Ease of navigation
- Customizable dashboards
- Responsive design for mobile access
- Clear and concise alert notifications
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Comprehensive user manuals
- Access to live webinars
- On-demand chat support
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multi-channel support options
- Dedicated account managers
- Response time to queries
- Access to a knowledge base
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Pricing transparency
- Tiered pricing options
- Cost against feature set
- Discounts for long-term contracts
- Comparison with industry standards
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall user satisfaction
- Frequency of updates and improvements
- Ease of integration with existing systems
- Feedback on customer service experiences
- Reported ROI and cost-effectiveness
How to Choose a Network Intrusion Detection System
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the tool grow with your business? Think about future needs and whether the system can handle increased network traffic without slowing down. |
| Integrations | Check if it connects with your existing security tools. Seamless integration saves time and reduces errors. |
| Customizability | Can you tailor the system to fit your specific security policies and workflows? Flexibility is key for unique business needs. |
| Ease of use | Is the interface intuitive for your team? A complicated system can slow down response times and frustrate users. |
| Implementation and onboarding | How long does it take to get up and running? Consider the learning curve and the resources needed for a smooth transition. |
| Cost | Evaluate the pricing structure. Are there hidden fees or costs for additional features? Ensure it fits your budget. |
| Security safeguards | Does it have strong encryption and regular security updates? Ensure it meets your security standards to protect sensitive data. |
| Compliance requirements | Does it comply with industry regulations like GDPR or HIPAA? Non-compliance can lead to fines and legal issues. |
What Are Network Intrusion Detection Systems?
Network intrusion detection systems are software tools that watch network traffic to find and alert on suspicious or harmful activity. They are used by security analysts, IT admins, and network teams who need to catch threats early and protect data. Features like packet inspection, signature matching, and alert logging help with spotting unusual behavior, reducing false alarms, and giving teams a clear picture of what’s happening on the network. These tools help people stay ahead of attacks without having to sift through endless traffic by hand.
Features
When selecting a network intrusion detection system, keep an eye out for the following key features:
- Real-time monitoring: Continuously observes network traffic to detect and alert on suspicious activities instantly.
- Customizable alerts: Allows you to set specific conditions for alerts, ensuring you’re notified about the most relevant threats.
- Integration capabilities: Connects seamlessly with existing security tools to enhance overall network protection.
- Threat intelligence: Utilizes data from past incidents to recognize and respond to new threats more effectively.
- User-friendly interface: Offers an intuitive design that makes it easy for teams to navigate and manage security tasks.
- Scalability: Adapts to growing network demands, ensuring performance remains consistent as your business expands.
- Log and report generation: Provides detailed records of detected incidents, aiding in analysis and compliance.
- Customizable detection rules: Enable tailoring of detection protocols to meet specific organizational security policies.
- Encryption support: Ensures that data is securely transmitted and stored, protecting sensitive information from unauthorized access.
- Compliance support: Assists in meeting industry regulations such as GDPR or HIPAA, reducing legal risks.
Benefits
Implementing a network intrusion detection system provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Real-time monitoring and threat intelligence help protect your network from unauthorized access and potential breaches.
- Improved compliance: Compliance support ensures your business meets industry regulations, reducing the risk of legal issues.
- Cost savings: Early detection of threats prevents costly data breaches, saving your business money in the long run.
- Better resource allocation: Customizable alerts allow your team to focus on genuine threats, optimizing resource use.
- Scalability: The system grows with your business, maintaining performance as network demands increase.
- Informed decision-making: Detailed log and report generation provides insights for future security strategies and improvements.
- Increased efficiency: A user-friendly interface and integration capabilities streamline security management tasks.
Costs and Pricing
Selecting a network intrusion detection system requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in network intrusion detection system solutions:
Plan Comparison Table for Network Intrusion Detection System
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited alerts, and community support. |
| Personal Plan | $10-$30/user/month | Real-time monitoring, customizable alerts, and basic integration options. |
| Business Plan | $50-$100/user/month | Advanced threat detection, detailed reporting, and multi-user support. |
| Enterprise Plan | $150-$300/user/month | Comprehensive security features, compliance support, and dedicated account management. |
Network Intrusion Detection System FAQs
Here are some answers to common questions about network intrusion detection systems:
Can network intrusion detection systems prevent attacks?
What are the limitations of network intrusion detection systems?
How often should you update your network intrusion detection system?
Is it necessary to have a dedicated team for managing network intrusion detection systems?
What’s Next:
If you're in the process of researching network intrusion detection systems, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.