10 Best Multi Factor Authentication Software Shortlist
Navigating the complex world of user authentication, I've come to value multi factor authentication software. With rising data breaches, it's essential to secure online accounts beyond just passwords. This goes beyond the traditional username and password combination and can include something the user knows, something the user has, or something inherent to the user.
These tools not only ensure end-users receive secure access via passcodes and self-service provisioning but also enhance remote access, connecting web-based user identities more securely. The pain points? Managing multiple user authentications, identity and access management (IAM), and ensuring remote access without compromising security. But with the right software, these are addressed, fortifying your accounts against breaches.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Multi Factor Authentication Software Summary
This comparison chart summarizes pricing details for my top MFA software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for adaptive MFA with multiple authentication factors | Free version available (up to 50 domain users) | From $595 (500 domain users) | Website | |
| 2 | Best for combining password management and MFA | 30-day free trial + free plan available | From $3/user/month (billed annually) | Website | |
| 3 | Best for SaaS companies needing rapid integration | 30 Days Free Trial | From $99/month for up to 10 multi-user accounts and 1,000 users. | Website | |
| 4 | Best for adaptive multi-factor authentication | 30-day free trial available | From $2/user/month | Website | |
| 5 | Best for achieving passwordless authentication | Free 14-Day Trial | From $8/user/month (billed annually) | Website | |
| 6 | Best for SMS and call verification | Not available | From $15/user/month | Website | |
| 7 | Best for scalable enterprise authentication | Free trial available | From $35/month | Website | |
| 8 | Best for those already in the Salesforce environment | Free plan available | From $25/user/month (billed annually) | Website | |
| 9 | Best for businesses in hybrid cloud scenarios | Not available | Pricing upon request | Website | |
| 10 | Best for users within the Microsoft ecosystem | Not available | From $6/user/month (billed annually) | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Multi Factor Authentication Software Reviews
Below are my detailed summaries of the best multi factor authentication software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
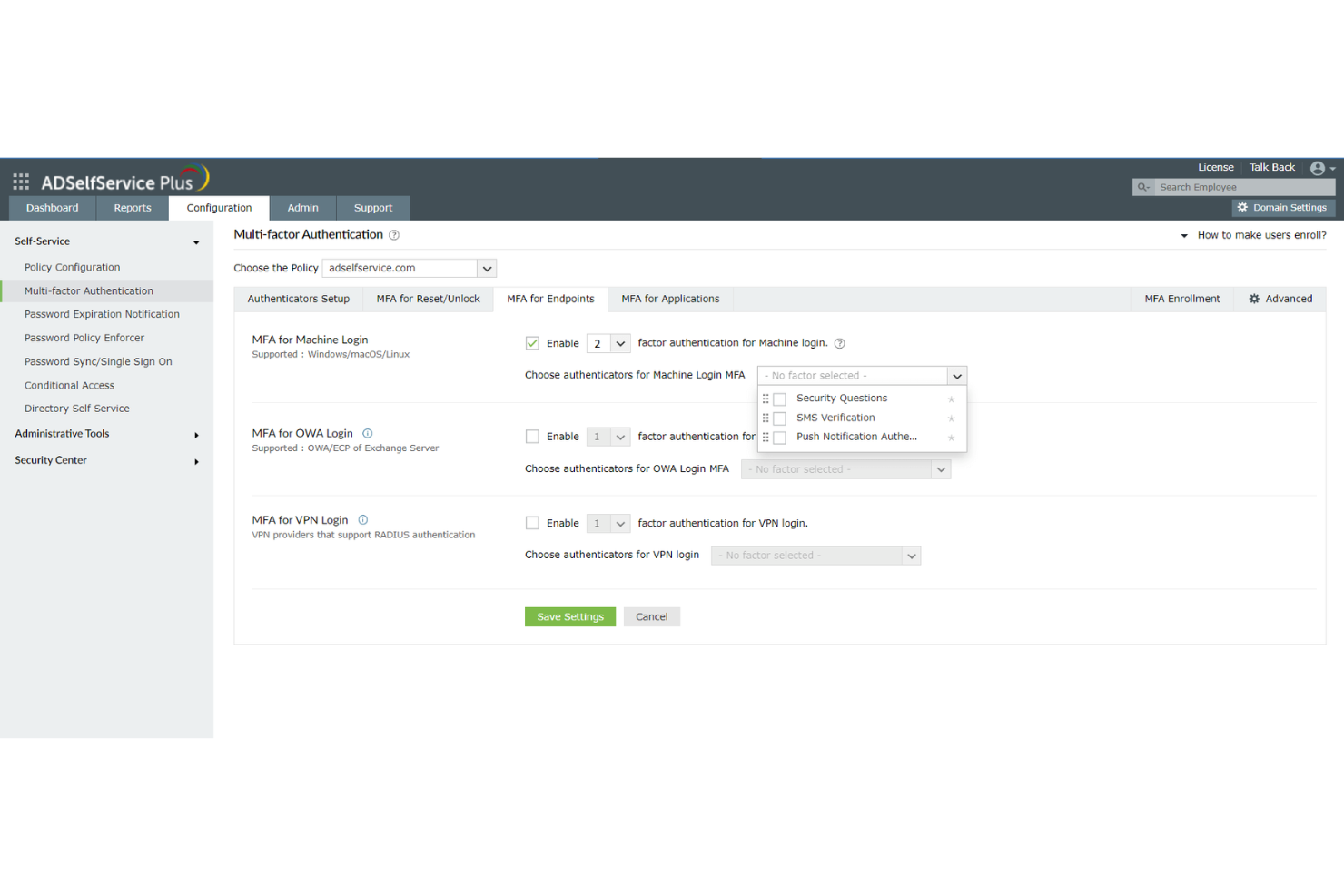
Best for adaptive MFA with multiple authentication factors
ManageEngine ADSelfService Plus is a comprehensive self-service password management and single sign-on (SSO) solution designed to streamline IT operations and enhance security. It caters to IT admins and end-users by providing functionalities such as password self-service, multi-factor authentication (MFA), and endpoint security.
Why I Picked ManageEngine ADSelfService Plus: ADSelfService Plus supports various authentication techniques such as biometrics, TOTP codes, push notifications, and security keys, which enhance the security landscape by adding multiple layers of verification beyond the traditional username and password. This adaptability in authentication methods ensures that organizations can tailor their security protocols to meet specific needs and compliance requirements. Furthermore, its adaptive MFA feature dynamically adjusts authentication requirements based on risk factors like user location and device type, providing a nuanced and context-aware security measure.
Standout features & integrations:
Other features include Single Sign-On (SSO), which integrates seamlessly with both on-premises and cloud-based applications, offering a unified and secure login experience across different environments. The tool also has self-service password management capabilities to allow users to reset passwords and unlock accounts independently. Integrations include Zendesk, Freshdesk, Splunk, syslog, and other ManageEngine applications like ManageEngine ADManager Plus and AD360.
Pros and Cons
Pros:
- Extensive reporting features for audits and compliance
- Various MFA options
- Self-service password reset
Cons:
- Free version has limited features
- Can be expensive for smaller organizations
LastPass functions as a comprehensive tool designed to both manage passwords securely and offer multi-factor authentication (MFA). It has cleverly combined these two essential features, making it an ideal choice for those who prioritize both password management and improved authentication.
Why I Picked LastPass: During my selection process, LastPass distinctly stood out because of its dual capability: managing passwords while also offering MFA. Comparing it with other tools, its comprehensive approach to security is what I found to be unique. My judgment is that for individuals or businesses that see the value in uniting password management with MFA, LastPass is a fitting choice.
Standout features & integrations:
LastPass provides a secure vault for storing passwords, notes, and other credentials, all of which are encrypted locally on the user's device. Additionally, its MFA functionality is robust, integrating biometric and contextual factors for improved security. Integration-wise, LastPass can be coupled with numerous web browsers, and platforms, and has extensions that ensure its functionality is easily accessible across devices.
Pros and Cons
Pros:
- Wide range of browser and platform integrations
- Local encryption ensures user data remains private
- Combines password management and MFA in one platform
Cons:
- Some advanced features are only available in higher-priced tiers
- The user interface might be challenging for non-tech-savvy individuals
- Annual billing may not appeal to all users
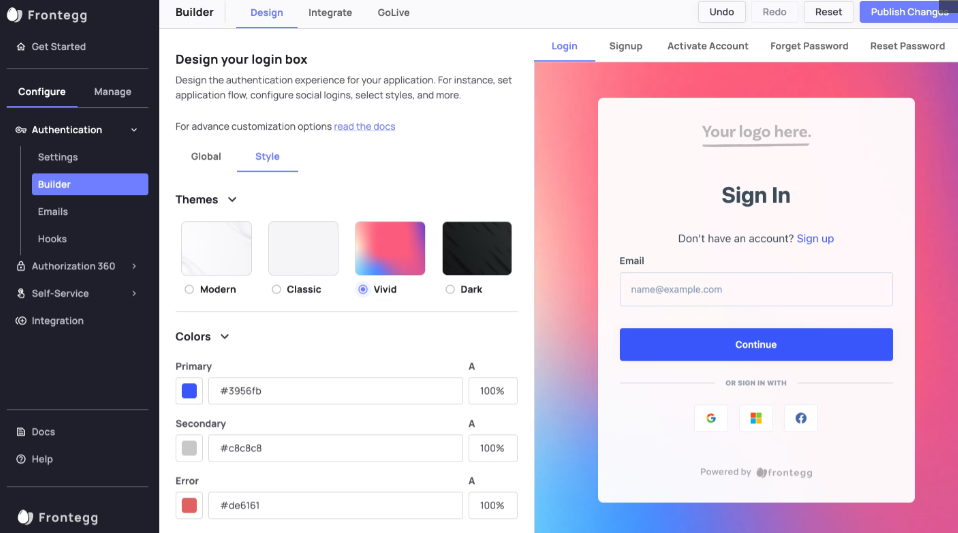
Frontegg is a platform designed to empower SaaS companies with pre-built, fully customizable functionalities to enhance their applications. This approach significantly accelerates integration processes, making it particularly advantageous for SaaS firms aiming for swift incorporation of essential features.
Why I Picked Frontegg: In the process of determining the most valuable tools for this list, Frontegg caught my attention due to its targeted approach to serving SaaS companies. Its capability to provide rapid integration truly differentiates it from other platforms. I judged that Frontegg is indeed the top choice for SaaS entities requiring quick feature integration.
Standout features & integrations:
Frontegg offers a suite of pre-built SaaS functionalities, ranging from user management, and notifications, to security and auditing capabilities. Their approach allows companies to skip lengthy development processes and immediately tap into proven features. Furthermore, Frontegg's integrations with popular platforms like Slack, Azure, and AWS ensure its functionalities can easily complement existing tech stacks.
Pros and Cons
Pros:
- Extensive integration options with major platforms
- Pre-built functionalities eliminate lengthy development times
- Tailored solutions specifically for SaaS companies
Cons:
- Pricing transparency could be improved
- Customizability could come with a learning curve for some
- Might not be suitable for non-SaaS companies
For those seeking a multi-factor authentication solution that combines security with ease of use, miniOrange IDP offers a compelling choice. It caters to businesses across various industries looking to enhance their security measures without complicating user access. By integrating additional verification methods, miniOrange IDP helps organizations safeguard sensitive information while maintaining a user-friendly login experience.
Why I Picked miniOrange IDP
I picked miniOrange IDP for its adaptive multi-factor authentication, which intelligently adjusts security measures based on user behaviour and risk levels. This feature ensures that your team remains secure without unnecessary interruptions. Additionally, the platform's extensive integration capabilities with over 6000 applications make it a versatile choice for businesses looking to streamline their access management. miniOrange IDP's centralized dashboard allows administrators to efficiently manage user access and monitor security policies, addressing common concerns around managing diverse user environments.
miniOrange IDP Key Features
In addition to its adaptive multi-factor authentication and integration capabilities, I also found the following useful:
- Multiple MFA Methods: Supports push notifications, OTP via SMS and email, Google Authenticator, hardware tokens, biometrics, and security questions.
- Passwordless Authentication: Enables passwordless login using FIDO2, biometrics, and push-based authentication methods.
- Conditional Access Policies: Applies authentication requirements based on user behaviour, device, location, and risk level.
- Self-Service Options: Allows users to reset passwords and configure their own MFA methods, which can help reduce IT support requests.
- Endpoint & VPN Protection: Secures VPN access as well as Windows, macOS, and Linux logins.
miniOrange IDP Integrations
Integrations include Microsoft 365, Google Workspace, AWS, Salesforce, Slack, Zoom, ServiceNow, Atlassian, GitHub, Dropbox, and WordPress. The platform supports integration with over 6,000 cloud, on-prem, and legacy applications. An API is also available for custom or proprietary application integrations.
Pros and Cons
Pros:
- Supports branded, customizable logins
- Centralized dashboard for user and policy management
- Robust adaptive MFA and security features
Cons:
- Initial setup can be complex, especially for small organizations
- Restrictive refund policies
Uniqkey is a robust authentication solution designed to offer users the convenience and security of passwordless authentication. Uniqkey stands as a formidable option to bridge this transition, particularly for those who prioritize passwordless solutions.
Why I Picked Uniqkey: In the process of determining the best tools for this list, Uniqkey grabbed my attention because of its dedication to a passwordless environment. Its focus on such a specific and critical area of cybersecurity made it different from many others I compared. I judged it as the best tool for those who are looking to achieve passwordless authentication, given its specialized approach and effectiveness in this domain.
Standout features & integrations:
Uniqkey's primary strength is its adaptive authentication which analyzes risk factors in real-time to determine the necessary level of verification. Moreover, it offers biometric verification options and a secure password vault for users who might still have some passwords to manage. For integrations, Uniqkey is compatible with a range of enterprise systems, ensuring businesses can incorporate it without causing disruptions to existing workflows.
Pros and Cons
Pros:
- Secure vault for residual passwords
- Adaptive authentication based on real-time risks
- Dedicated to a passwordless environment
Cons:
- Relatively new in the market, which might concern some users seeking established brands
- Limited to certain platforms and devices
- Might have a learning curve for those new to passwordless systems
RingCaptcha stands as a specialized tool geared towards ensuring reliable user verification via SMS and voice calls. As businesses today seek tighter security measures, especially during user onboarding, RingCaptcha emerges as a frontrunner with its focus on mobile verification, aligning it perfectly with the title of being the best in SMS and call verification.
Why I Picked RingCaptcha: In the process of choosing the right tools for this list, RingCaptcha caught my attention due to its sheer specificity and prowess in mobile-based verification. RingCaptcha's specialization in SMS and call verification made it distinct. This dedication to mobile verification is why I determined it's the best for businesses relying heavily on these methods.
Standout features & integrations:
RingCaptcha's core strength lies in its rapid SMS delivery, robust voice call verification, and user-friendly dashboard to track and manage verifications. Regarding integration, RingCaptcha is versatile, integrating smoothly with platforms like Shopify, WordPress, and WooCommerce, ensuring a wider reach and applicability across different business models.
Pros and Cons
Pros:
- User-centric dashboard for tracking
- Rapid SMS delivery mechanism
- Specializes in SMS and voice call verifications
Cons:
- Limited features beyond mobile verification
- Higher price point compared to some competitors
- Might be over-specific for businesses needing varied verification methods
Auth0 is a leading identity management platform designed to simplify authentication and authorization for businesses of all sizes. Tailored especially for enterprises, it ensures that as businesses grow, their security measures scale with them, making it a top pick for scalable enterprise authentication.
Why I Picked Auth0: When I was selecting an authentication tool, Auth0 consistently emerged at the forefront of the options. Its reputation for robustness and adaptability in the identity management space set it apart from its peers. In comparing it to other tools, its scalability especially for larger corporations cemented its position as the best for scalable enterprise authentication in my opinion.
Standout features & integrations:
Among its myriad of features, Auth0's Single Sign-On, Adaptive Multifactor Authentication, and user-friendly administration dashboard are particularly noteworthy. When considering integrations, Auth0 shines with its compatibility across a range of platforms such as AWS, Slack, Salesforce, and Zendesk, ensuring businesses have a cohesive and integrated workflow.
Pros and Cons
Pros:
- Comprehensive security tools
- Wide range of third-party integrations
- Adaptable for various business sizes
Cons:
- Starting price might be steep for some budgets
- Some customizations can demand technical know-how
- Potential complexity for smaller businesses
The Salesforce Platform provides an extensive suite of tools and services designed to enable businesses to build and scale applications quickly. It is tailored especially for companies and teams that are already immersed in the Salesforce ecosystem.
Why I Picked Salesforce Platform: Selecting tools for this list, I was drawn to the Salesforce Platform because of its deep integration capabilities and the comprehensive solutions it offers. This platform provides the most aligned and synergistic approach. That's why I believe it's best for those already in the Salesforce environment.
Standout features & integrations:
The Salesforce Platform is notable for its low-code development capabilities, allowing businesses to create applications swiftly. It also boasts AI-powered analytics and a robust security model to protect sensitive data. When it comes to integrations, the platform naturally works well with other Salesforce offerings like Sales Cloud, Service Cloud, and Marketing Cloud, ensuring a cohesive experience for users.
Pros and Cons
Pros:
- Strong security features
- Low-code development accelerates application creation
- Deep integration with other Salesforce products
Cons:
- Requires investment in learning and training for optimal use
- Pricing can become high as more features are added
- Might be overwhelming for those new to Salesforce
IBM Security Verify offers an identity and access management solution that is designed to provide a secure user experience across various platforms and applications. This tool stands out especially for businesses operating in hybrid cloud environments, given its robust integration capabilities and security features tailored for such scenarios.
Why I Picked IBM Security Verify: In the process of selecting tools, IBM Security Verify caught my eye because of its distinct focus on hybrid cloud situations. Judging from its features and the feedback from users, it became evident that its strengths lie in addressing the unique challenges posed by hybrid cloud setups. This makes me believe it's ideally suited for businesses navigating such complex environments.
Standout features & integrations:
IBM Security Verify boasts a comprehensive suite of features, including adaptive access policies, AI-driven insights, and a user behavior analytics engine. It's also equipped with single sign-on (SSO) and multi-factor authentication (MFA) to bolster security. As for integrations, the tool supports a wide array of applications, databases, and platforms, making it adaptable to diverse IT ecosystems.
Pros and Cons
Pros:
- Broad spectrum of integrations
- Comprehensive security measures, including SSO and MFA
- Tailored features for hybrid cloud environments
Cons:
- Some businesses might find it feature-dense for simpler use cases
- Initial setup can be complex for some users
- Pricing transparency could be improved
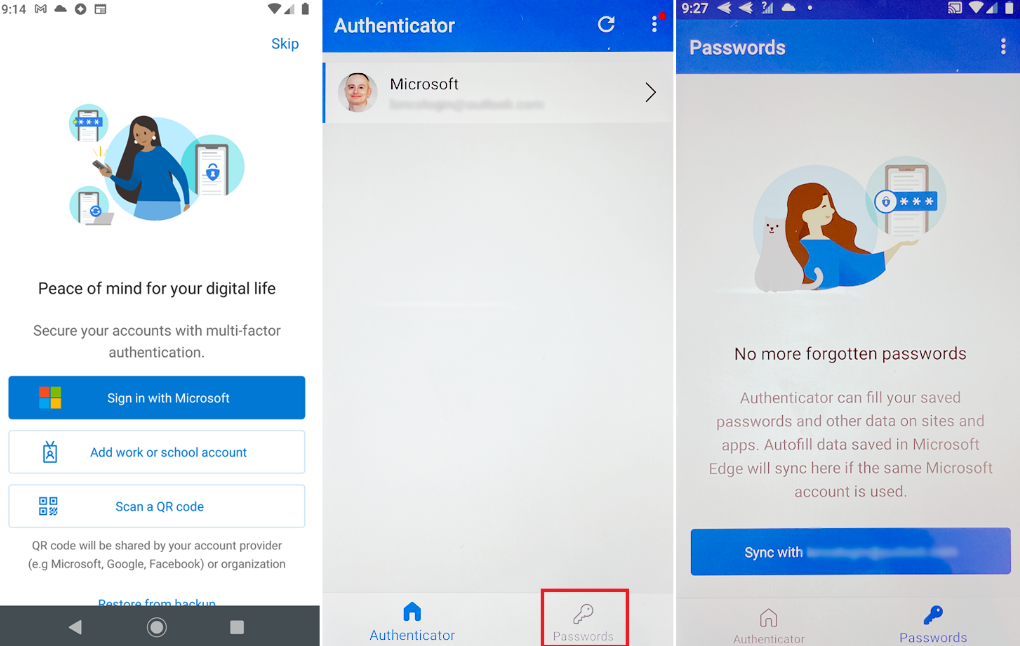
Microsoft Authenticator streamlines the multi-factor authentication process for those immersed in the Microsoft ecosystem. By integrating deeply with Microsoft services, it provides a smooth and efficient authentication experience, making it an ideal choice for users heavily reliant on Microsoft products.
Why I Picked Microsoft Authenticator: When selecting tools for this list, Microsoft Authenticator stood out due to its natural integration with the vast array of Microsoft services. From my perspective, the tool's compatibility and synchronicity within the Microsoft environment differentiate it from many other authenticators. Based on these observations, I judged it as the best fit for users who are deeply enmeshed in the Microsoft ecosystem.
Standout features & integrations:
One of Microsoft Authenticator's prime features is its passwordless login capability, which enhances security while simplifying the user experience. The tool also boasts biometric verification, allowing users to authenticate using their fingerprint or face recognition. Regarding integrations, it flawlessly meshes with Microsoft services such as Office 365, Outlook, and OneDrive, providing a unified and secure experience across all platforms.
Pros and Cons
Pros:
- Biometric verification options
- Passwordless login feature
- Deep integration with Microsoft services
Cons:
- Limited customization options compared to other tools on the market
- Requires regular updates for optimal functionality
- Might be less appealing to non-Microsoft users
Other Multi Factor Authentication Software
Below is a list of additional multi factor authentication software that I shortlisted but did not make it to the top 12. Definitely worth checking them out.
- Google Authenticator
For users of Google's suite of services
- Twilio Verify API
For developers needing customizable verification
- WatchGuard AuthPoint
For ensuring mobile-based security
- ManageEngine ADManager Plus
For diverse authentication methods
- OneLogin
Good for streamlined cloud identity management
- Duo Security
For comprehensive endpoint protection
- CyberArk Identity
Good for privileged access management integration
- Yubico
Good for hardware-based authentication keys
- Thales SafeNet Trusted Access
Good for cloud and on-premises integrations
- Prove
Good for phone-centric identity verification
- SecureID
Good for risk-based dynamic access decisions
- Silverfort
Good for adaptive authentication across environments
- Azure Multi-Factor Authentication
Good for Azure users needing native MFA
- PingID
Good for mobile biometric verification
- AuthN by IDEE
Good for passwordless multi-factor authentication
- Instasafe ZTAA
Good for Zero Trust network access
- GateKeeper Proximity Authentication
Good for hands-free, proximity-based access
Multi Factor Authentication Software Selection Criteria
When selecting the best MFA software to include in this list, I considered common buyer needs and pain points like ease of integration and user experience. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Provide two-factor authentication
- Support for multiple authentication methods
- Integration with existing systems
- Real-time monitoring and alerts
- Secure access to applications
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Biometric authentication options
- Risk-based authentication
- Customizable user policies
- Passwordless authentication
- Geo-location tracking
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Ease of setup and configuration
- Clear navigation and layout
- User-friendly experience
- Accessibility features
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates and guides
- Responsive chat support and chatbots
- Webinars and live demonstrations
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of 24/7 support
- Multiple support channels
- Response time to inquiries
- Quality of documentation
- Access to a dedicated account manager
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing options
- Transparent pricing structure
- Flexibility of subscription plans
- Cost-benefit ratio
- Discounts for larger teams
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Frequency of positive feedback
- Commonly mentioned pain points
- Feedback on customer support
- User-reported ease of use
How to Choose a Multi Factor Authentication Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your team? Consider user limits and expansion capabilities. Ensure it accommodates future growth without needing a complete overhaul or costly upgrades. |
| Integrations | Does it work with your existing tools? Check compatibility with your current systems, such as CRM, email clients, or cloud services, to prevent workflow disruptions. |
| Customizability | Can you tailor it to your needs? Look for options to adjust settings, policies, and user interfaces to fit your specific requirements. Avoid rigid solutions that force you into a one-size-fits-all approach. |
| Ease of use | Will your team pick it up quickly? Assess the interface design and user experience. A complicated system could slow down adoption and frustrate users. |
| Implementation and onboarding | How smooth is the transition? Examine the support for setup, such as guides, training resources, and dedicated onboarding assistance, to ensure a smooth switch from your current system. |
| Cost | Is it within your budget? Evaluate the pricing model, including hidden fees, add-ons, and long-term costs. Compare against your budget constraints to find the right balance between cost and functionality. |
| Security safeguards | Are your data and user identities protected? Verify encryption standards, data storage practices, and compliance with security protocols like GDPR or HIPAA. |
| Compliance requirements | Does it meet industry standards? Ensure the software aligns with legal and regulatory requirements relevant to your sector, such as PCI-DSS for payment processing. |
What is Multi Factor Authentication Software?
Multi factor authentication software provides an added layer of security by requiring users to provide two or more verification methods before granting access to an account or system. This software offers multiple authentication factors – from OTPs for Windows, Linux, and MAC/macOS to biometric authentication for mobile apps on Android and Apple iOS. With tools, you get push notifications, authenticator apps, and software tokens that work easily with the active directory.
Organizations and individuals leverage these tools to bolster security, particularly in an era where cyber threats are rampant. This approach minimizes the risk of unauthorized access, even if malicious actors obtain a user's password, ensuring that sensitive data and systems remain protected.
Features
When selecting MFA software, keep an eye out for the following key features:
- Two-factor authentication: Provides an additional security layer by requiring a second form of verification, such as a text message or email code.
- Integration capabilities: Allows seamless connection with existing systems like CRM and email clients to prevent workflow disruptions.
- Biometric authentication: Uses fingerprints or facial recognition to verify identity, offering a more secure and convenient user experience.
- Risk-based authentication: Adapts security measures based on user behavior and location to enhance protection without compromising usability.
- Passwordless authentication: Eliminates the need for passwords, reducing the risk of breaches due to weak or stolen credentials.
- Customizable user policies: Enable the creation of tailored security protocols to meet specific organizational needs and compliance requirements.
- Real-time monitoring: Provides instant alerts and insights into unauthorized access attempts, allowing for quick response to potential threats.
- Geo-location tracking: Monitors user locations to prevent access from suspicious or unauthorized regions.
- User-friendly interface: Ensures ease of use with an intuitive design, reducing training time and improving user adoption.
- Compliance support: Aligns with industry standards like GDPR and HIPAA, ensuring legal and regulatory adherence.
Benefits
Implementing MFA software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Provides additional layers of protection through features like two-factor and biometric authentication to reduce unauthorized access.
- Reduced risk of breaches: Minimizes the chances of data breaches by using passwordless authentication and real-time monitoring to detect suspicious activities.
- Improved compliance: Helps meet industry regulations with compliance support, ensuring your organization adheres to legal standards.
- Increased user confidence: Builds trust among users by securing sensitive information and protecting personal data.
- Flexible access management: Offers customizable user policies, allowing you to tailor security measures to fit your specific needs.
- Efficient threat response: Enables quick action on potential threats with instant alerts and geo-location tracking.
- Simplified user experience: Ensures ease of use with a user-friendly interface, making it easier for your team to adopt and utilize the software effectively.
Costs and Pricing
Selecting multi factor authentication software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in MFA solutions:
Plan Comparison Table for Multi Factor Authentication Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic two-factor authentication, limited integrations, and community support. |
| Personal Plan | $5-$10/user/month | Two-factor authentication, email support, and basic app integrations. |
| Business Plan | $15-$25/user/month | Multi-device support, advanced integrations, risk-based authentication, and priority support. |
| Enterprise Plan | $30-$50/user/month | Customizable policies, biometric authentication, a dedicated account manager, and compliance support. |
Multi Factor Authentication Software FAQs
Here are some answers to common questions about MFA software:
Can multi factor authentication software be used with hardware tokens?
Yes, many multi factor authentication solutions support hardware tokens as an additional layer of security. This feature is useful if your team prefers physical devices over digital methods. Ensure the software you’re considering is compatible with the tokens you intend to use.
What should I do if I’m not receiving verification codes?
If you’re not receiving verification codes via text, it could be due to carrier issues or security apps. Switching to an authenticator app can improve reliability. Check if your software provides alternative verification methods to avoid interruptions in access.
Is user data stored in the cloud?
User data handling varies by provider. Some solutions store data on-premises, while others use the cloud. It’s important to understand where your data is stored and how it’s protected. Look for software that offers secure communication for authentication requests.
What support options are available for troubleshooting?
Most providers offer a range of support options, including troubleshooting steps for common issues and direct assistance. Look for software that provides detailed documentation, user forums, and direct support channels like chat or phone for quick help.
Which software is known to be the most affordable?
While exact prices can change, OneLogin and Azure Multi-Factor Authentication have historically been among the more affordable options on the market.
Which software tends to be the most expensive?
Premium solutions like CyberArk Identity and Thales SafeNet Trusted Access often come at a higher price point due to their advanced features and enterprise-level capabilities.
What’s Next:
If you're in the process of researching multi factor authentication software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.