10 Best Digital Forensics Software
Navigating the intricate world of computer forensics, I've come to realize the invaluable role digital forensics software plays. By sifting through digital evidence, it becomes a formidable shield against malware, ensuring the integrity of operating systems and bolstering our overall cybersecurity posture. Imagine a tool that extracts and analyzes digital data, presenting a clearer picture amidst the chaos.
This software not only safeguards your digital assets but alleviates the daunting challenges of uncovering malicious activities and securing sensitive data. It's essential gear for anyone venturing into the vast realm of digital investigations.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Digital Forensics Software Summary
This comparison chart summarizes pricing details for my top digital forensics software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for cross-platform data correlations | 15-day free trial | Pricing upon request | Website | |
| 2 | Best for real-time network activity insights | Not available | Pricing upon request | Website | |
| 3 | Best for security event and log management | Free demo available | Pricing upon request | Website | |
| 4 | Best for domain and DNS-based research | Not available | Pricing upon request | Website | |
| 5 | Best for comprehensive digital investigations | Not available | Pricing upon request | Website | |
| 6 | Best for identifying large-scale attack campaigns | Not available | Pricing upon request | Website | |
| 7 | Best for advanced data recovery | Not available | Pricing upon request | Website | |
| 8 | Best for on-site mobile data extraction | Not available | Pricing upon request | Website | |
| 9 | Best for mobile and cloud evidence recovery | Not available | Pricing upon request | Website | |
| 10 | Best for extracting digital artifacts | Not available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Digital Forensics Software Reviews
Below are my detailed summaries of the best digital forensics software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Oxygen Forensics is a digital forensics platform that handles data collection, extraction, and analysis across mobile devices, computers, cloud services, and IoT sources, with tools for timeline analysis, malware detection, password recovery, and eDiscovery.
Who Is Oxygen Forensics Best For?
Oxygen Forensics is a strong fit for law enforcement agencies, government investigators, and enterprise security teams that need deep forensic analysis across a wide range of devices and data sources.
Why I Picked Oxygen Forensics
I picked Oxygen Forensics as one of the best because of how well it handles cross-platform data correlations in a single investigation. My team can pull data from mobile devices, computers, cloud services, and IoT sources, then run timeline and link analysis across all of it together. That means when a suspect's phone activity, cloud storage, and laptop artifacts all need to connect into a single narrative, I'm not stitching together separate exports. The ability to parse over 900 apps and import third-party extractions into that same unified view is what makes the correlation work at scale.
Oxygen Forensics Key Features
- Mapping and location services: Plot and analyze location data from devices on dynamic maps, with exports available for reporting.
- Media review: Review and categorize photos, videos, and other media types extracted during an investigation in a dedicated review interface.
- eDiscovery export: Export electronically stored information (ESI) in industry-standard formats for use in legal proceedings or downstream review platforms.
- Key evidence tagging: Mark, tag, and annotate specific pieces of evidence within a case to flag items for review or collaboration.
Oxygen Forensics Integrations
Oxygen Forensics imports and parses extractions from third-party forensic tools, including Cellebrite UFED and MSAB XRY file formats, and has a direct connector with Relativity for exporting extracted data into eDiscovery review workflows. API and Zapier support are not clearly documented.
Pros and Cons
Pros:
- Parses cryptocurrency and AI chat artifacts
- Supports multiple simultaneous device extractions
- Decrypts encrypted messaging apps like Signal
Cons:
- Licensing costs are quite high
- Limited computer forensics compared to mobile
ExtraHop earns its spot for the way it gives you real-time insight into network activity, not just logs. I go to ExtraHop when teams outgrow packet capture tools and need instant visibility into lateral movements or advanced threats as traffic flows.
What stands out for me is how it correlates packets into readable workflows, helping security teams reconstruct incidents and spot suspicious behavior quickly. I appreciate how you can dig right into encrypted traffic analytics without waiting on processing or sifting through raw data.
ExtraHop’s Best For
- Security teams monitoring real-time east-west network traffic
- Incident response units needing instant packet-level forensics
ExtraHop’s Not Great For
- Teams focused on endpoint or disk-level forensics
- Small IT teams with limited network complexity
What sets ExtraHop apart
ExtraHop centers its workflow around real-time network observation rather than retroactive deep dives. Instead of the log-driven approaches you get with tools like Splunk, ExtraHop expects you to monitor live traffic and spot abnormal activity as it happens. This approach works best when you want to understand network behaviors in the moment instead of sifting through logs after the fact.
Tradeoffs with ExtraHop
ExtraHop optimizes for velocity and instant network insights, but as a result, it falls short on detailed endpoint investigation. If you need in-depth analysis beyond the network layer, you end up missing context.
Pros and Cons
Pros:
- Robust integrations with IoT platforms and utility for law enforcement agencies.
- Broad compatibility including support for macOS.
- The intuitive graphical interface simplifies malware analysis.
Cons:
- Some custom integrations might necessitate additional configurations.
- Advanced features require a steeper learning curve.
- The initial setup might be intricate for some users.
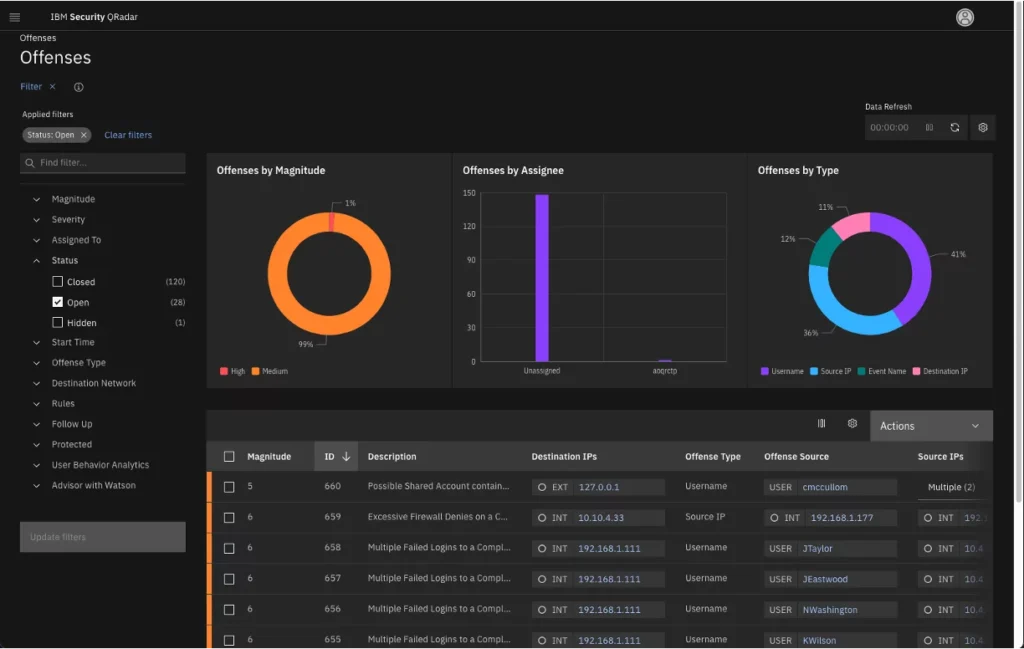
IBM Security QRadar SIEM earns its spot because it pulls together security event, log, and network data into one place for deep forensic analysis. I recommend it to teams that need to triage incidents quickly, trace activity across sources, and visualize attack paths after something suspicious happens.
What I appreciate is how you can reconstruct events from diverse logs and get clear, actionable context through QRadar’s correlation and timeline features. This works best when you deal with high volumes of alerts and require audit trails that will hold up to scrutiny.
QRadar’s Best For
- Security operations centers handling large-scale incident investigations
- IT teams needing unified log and event forensic analysis
QRadar’s Not Great For
- Small organizations with basic forensics needs
- Teams wanting built-in file or memory analysis tools
What Sets QRadar Apart
QRadar stands out because it assumes you’ll bring together huge volumes of security data from diverse sources and need a way to reconstruct incidents step by step. Unlike tools like Splunk that emphasize custom visualization and search above all, QRadar is organized around correlation and event timelines. This works well when you need a security forensics backbone that fits into large, operational security environments.
Tradeoffs with QRadar
QRadar optimizes for end-to-end event correlation at scale, but speedy setup and lightweight deployment suffer as a result, making it a tough fit for smaller or very lean teams.
Pros and Cons
Pros:
- A broad range of integrations with third-party security tools.
- Advanced analytics capabilities for pinpointing threats.
- Comprehensive correlation of security data from various sources.
Cons:
- Requires periodic tuning to remain optimally effective.
- The sheer amount of data may require significant storage solutions.
- Can be complex to set up initially.
DomainTools makes my shortlist because it's the resource I count on when domain and DNS connections are central to an investigation. I like how it traces domain ownership, uncovers domain infrastructure, and tracks DNS changes to spot malicious activity or ties between threat actors.
For anyone dealing with attack surface expansion or suspicious domains, its Whois and passive DNS intelligence give you data you can act on—fast.
DomainTools’s Best For
- Security teams tracing domain and DNS relationships
- Investigators mapping threat actor infrastructure across the web
DomainTools’s Not Great For
- Digital forensics focused on endpoint or disk analysis
- Teams needing all-in-one incident response with data capture
What sets DomainTools apart
DomainTools takes a domain-centric approach to digital forensics by mapping domain ownership, infrastructure, and DNS relationships in detail. Unlike network forensics tools that analyze packets or logs, it assumes that your investigation needs to surface connections between web properties, attackers, or malicious assets. In practice, this stands out when you need to connect seemingly unrelated domains or spot infrastructure shifts.
Tradeoffs with DomainTools
DomainTools optimizes for domain and DNS intelligence, so you lose the ability to dig into hosts, endpoints, or file-level artifacts, and will need a second tool to cover those areas.
Pros and Cons
Pros:
- Wide integration, including with Android platforms.
- Strong network forensic features to detect vulnerabilities.
- Deep domain metadata extraction capabilities.
Cons:
- Real-time updates or alerts might not be instantaneous.
- The user interface may seem complex for beginners.
- Might require some time to familiarize yourself with its plethora of features.
OpenText EnCase Forensic earns a spot on my list because of how thoroughly it handles complex digital investigations across diverse environments. I see teams rely on EnCase when they need to collect, analyze, and report on evidence from Windows, Mac, mobile devices, and cloud sources without gaps.
I appreciate its depth in evidence acquisition and validation—being able to create repeatable, defensible workflows saves a lot of headaches in high-stakes cases.
EnCase Forensic’s Best For
- Investigators handling multi-platform, large-scale digital evidence
- Legal and law enforcement teams requiring defensible workflows
EnCase Forensic’s Not Great For
- Small organizations with basic forensic needs only
- Users wanting a lightweight or quick-start forensics tool
What sets EnCase Forensic apart
EnCase Forensic focuses on enabling digital investigators to pull evidence from a variety of sources and environments with consistency. Unlike lighter tools like FTK Imager that handle one device at a time, EnCase expects you to methodically process entire drives, servers, or cloud storage. In practice, this fits organizations where evidence integrity and repeatability really matter.
Tradeoffs with EnCase Forensic
EnCase optimizes for detailed, large-scale investigations, but this means slower setup and a steeper learning curve for people who just need fast answers.
Pros and Cons
Pros:
- Extensive integrations with popular operating systems.
- Can navigate both open-source and proprietary platforms.
- Broad device compatibility, including hard drives and mobile devices.
Cons:
- Could be considered pricey compared to more niche forensic tools.
- Initial setup may require expert knowledge.
- Might be overwhelming for beginners given its range of features.
Imperva Attack Analytics makes my list for its ability to pinpoint coordinated attack campaigns across your infrastructure, even at huge scale. I’ve worked with security teams who rely on its automated incident correlation to quickly connect data from multiple sources—logs, events, and behavioral analytics. What I really appreciate is how it surfaces attack patterns that would otherwise slip through if you just watched incidents in isolation.
For teams tasked with digital forensics on high-traffic environments, this is the tool I’d turn to when the main concern is distinguishing organized threats from routine noise.
Imperva Attack Analytics’ Best For
- Security teams monitoring for coordinated, large-scale attack campaigns
- Organizations with high event volumes needing automated incident correlation
Imperva Attack Analytics’ Not Great For
- Small environments with limited security event data
- Teams seeking in-depth malware or endpoint-level investigation
What sets Imperva Attack Analytics apart
Imperva Attack Analytics is designed to help you see coordinated attack patterns by tying together logs and incidents from multiple systems. Instead of the granular, endpoint focus you get with tools like CrowdStrike, Imperva aims to surface the big picture. This works best when you want to understand how complex attack campaigns unfold across different layers of your stack.
Tradeoffs with Imperva Attack Analytics
It optimizes for campaign-level correlation, so you lose granularity on device or file-level forensics. This means you often need a second tool for root cause or detailed endpoint analysis.
Pros and Cons
Pros:
- Versatile file format processing capabilities.
- Efficient management and interpretation of dumps.
- Comprehensive ability to create and analyze disk images.
Cons:
- Integration with some tools might require manual configuration.
- Requires significant storage for large-scale analysis.
- The interface might be complex for beginners.
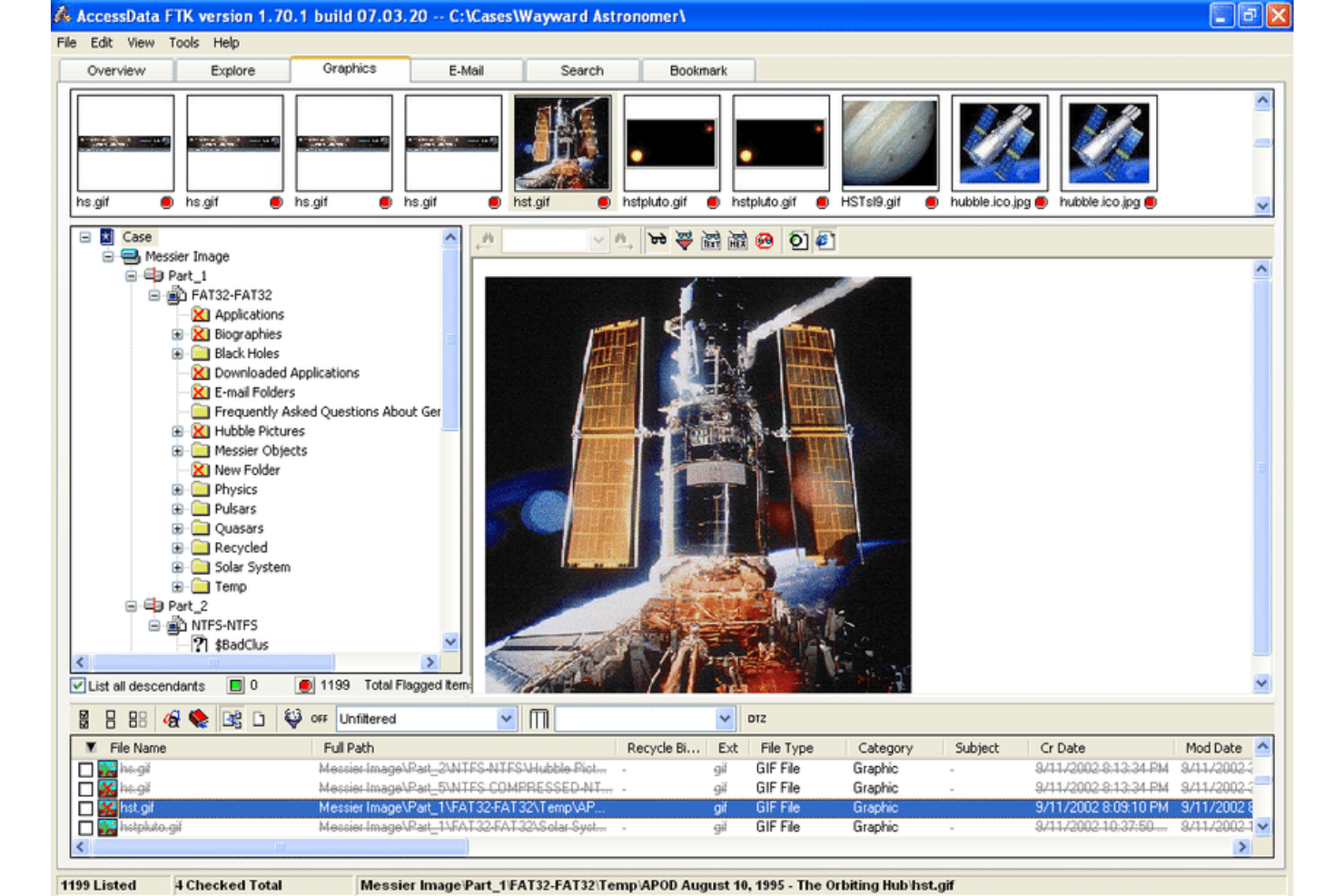
FTK Forensic Toolkit is on my list because its advanced data recovery consistently helps teams handle tough investigations. I like how well it digs into encrypted, deleted, or hidden files at scale, especially for complex environments. When you need to reconstruct timelines from fragmented evidence or recover data from formatted drives, I’ve found FTK’s automation and processing speed save hours.
FTK Forensic Toolkit’s Best For
- Digital forensics labs handling complex investigations
- Legal teams recovering hard-to-access or encrypted data
FTK Forensic Toolkit’s Not Great For
- Small organizations with basic evidence collection needs
- Teams looking for lightweight or budget-friendly tools
What sets FTK Forensic Toolkit apart
FTK Forensic Toolkit is purposely designed for in-depth digital investigations rather than simple evidence imaging, so it suits teams that need layered data review and recovery. Unlike EnCase, which leans toward broader evidence management, FTK expects you to work with large volumes of raw data, combing through deleted files, encrypted partitions, and system artifacts for hidden evidence.
This works well when you need to dig into difficult cases that require reconstructing a story from scattered data fragments.
Tradeoffs with FTK Forensic Toolkit
FTK optimizes for advanced discovery and processing scale, but that means you deal with heavier setup, steep learning, and more overhead if you only need basic evidence capture.
Pros and Cons
Pros:
- Comprehensive tool integrations conducive to digital forensic investigations.
- Strong defensive mechanisms against cyber attacks.
- Rigorous cloning capabilities ensuring accurate replications.
Cons:
- Data processing speed might vary based on the volume of evidence.
- The sheer number of features could be overwhelming.
- The initial setup might be intricate for some users.
Cellebrite earns its place on my list because it solves onsite mobile data extraction where remote or cloud-based tools aren't a fit. When I meet teams that need access to locked or encrypted devices quickly, this is the tool I trust.
I've seen Cellebrite Premium reliably pull data from the latest iOS and Android devices in field scenarios where time and access are tight. I appreciate how focused it is on bypassing security hurdles while preserving evidence integrity right on site.
Cellebrite’s Best For
- Law enforcement needing rapid onsite device extraction
- Investigators accessing locked or encrypted mobile devices
Cellebrite’s Not Great For
- Teams focusing on remote or cloud data collection
- Investigators without physical access to mobile devices
What sets Cellebrite apart
Cellebrite expects you to work directly with the device in hand, prioritizing on-the-spot data extraction instead of remote access. Unlike platforms like Magnet AXIOM, which focus on pulling evidence from cloud sources, Cellebrite Premium is designed for scenarios where every minute counts and the device is physically present.
Field teams tend to rely on it for quick, targeted collections from locked or encrypted phones in time-sensitive investigations.
Tradeoffs with Cellebrite
Cellebrite optimizes for physical access to devices, which means you lose practical options for collecting data from cloud accounts or remote endpoints. If you need off-site or ongoing monitoring, you’ll need to pair it with a different tool.
Pros and Cons
Pros:
- Effective integrations with other investigative platforms.
- High compatibility with a vast range of mobile devices.
- Robust computer-aided investigative environment.
Cons:
- Initial setup and calibration can be time-consuming.
- Hardware components might need frequent updates for newer devices.
- Requires specialized training for optimal usage.
Magnet AXIOM makes my list for its strength in collecting and analyzing evidence from mobile devices and cloud platforms like iOS, Android, and services such as Google, iCloud, and social apps. I reach for it when organizations need to recover chat histories, app data, or account activity across multiple sources. From using it, one thing that stands out is its ability to surface hidden or encrypted data and connect artifacts across devices and accounts. This saves time when correlating evidence from things like mobile chats and cloud backups during complex investigations.
Magnet AXIOM's Best For
- Investigators handling mobile and cloud data sources
- Teams focused on recovering encrypted or hidden evidence
Magnet AXIOM's Not Great For
- Cases limited to traditional desktop forensics
- Organizations with low technical expertise or minimal training resources
What sets Magnet AXIOM apart
Magnet AXIOM stands out by focusing on mobile devices and cloud sources instead of building around desktop imaging like EnCase. It’s designed for cases where data extraction from chat apps, social media, and cloud accounts is essential, not just a bonus. In practice, teams use it when traditional forensics tools can’t access data in apps or encrypted cloud storage.
Tradeoffs with Magnet AXIOM
AXIOM optimizes for mobile and cloud recovery, but its workflows can overwhelm those who want quick, surface-level analysis. You trade simplicity for broader evidence access and deeper extraction.
Pros and Cons
Pros:
- Noteworthy integrations with cloud platforms and mobile OS.
- Proficient in retrieving internet history from various devices, especially mobile phones.
- Detailed timeline analysis ensures comprehensive insight.
Cons:
- Reliance on continuous updates to support the latest mobile OS versions.
- Some advanced features could be overwhelming.
- Might have a steeper learning curve for beginners.
Belkasoft Evidence Center earns its spot for how quickly it pulls data from a huge array of sources—browser history, chats, emails, and device images. Whenever you need to dig deep into mobile or computer artifacts, its automatic extraction and timeline building helps paint a complete picture, even from encrypted sources.
What I really like is how the artifact overview gives you instant access to the most relevant evidence, especially when your investigation demands fast answers under tight timelines.
Belkasoft Evidence Center’s Best For
- Forensics teams extracting artifacts from computers, mobile, and cloud
- Investigators who need fast evidence analysis from diverse sources
Belkasoft Evidence Center’s Not Great For
- Teams needing live remote acquisition from endpoints
- Users focusing on incident response or network forensics
What sets Belkasoft Evidence Center apart
Belkasoft Evidence Center is built for investigators who need to extract and correlate artifacts from a huge range of sources very quickly. Unlike tools that require manual searching, Belkasoft automates the process, surfacing evidence from encrypted images, mobile devices, and cloud sources with minimal input.
In practice, this works best if you’re juggling many data types and want to get hands-on with disk, memory, or app artifacts without heavy manual setup.
Tradeoffs with Belkasoft Evidence Center
It optimizes for artifact extraction and correlation, but you lose out on live endpoint acquisition and active monitoring—meaning you’ll need another tool if you depend on network-based or real-time response work.
Pros and Cons
Pros:
- Efficient forensic imaging feature for evidence preservation.
- Advanced memory forensics capabilities.
- Comprehensive focus on digital artifact extraction.
Cons:
- Potential hidden costs for additional modules or advanced training.
- The breadth of features might seem daunting initially.
- A learning curve may be present for newcomers.
Other Digital Forensics Software
Below is a list of additional digital forensics software that I shortlisted, but did not make it to the top 10. They are definitely worth checking out.
- Detego Global
For unified digital forensics operations
- Cyber Triage
For rapid incident response
- MailXaminer
For email analysis and recovery
- Wireshark
Good for network protocol analysis
- Sandblast Threat Extraction
Good for advanced threat defense
- Parrot Security
Good for ethical hacking and pen testing
- Autopsy Digital Forensics
Good for detailed digital investigations
- CYREBRO
Good for cybersecurity and forensic analysis
- Oxygen Forensic Detective
Good for mobile data extractions
- PALADIN
Good for OS-based forensic acquisition
- Binalyze AIR
Good for automated incident response
- Aware
Good for forensic research and compliance
- Sleuth Kit
Good for open-source forensic investigations
- OSForensics
Good for rapid digital forensic discovery
Digital Forensics Software Selection Criteria
When selecting the best digital forensics software to include in this list, I considered common buyer needs and pain points like data accuracy and compliance with data regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Data recovery
- Evidence collection
- File analysis
- Incident response
- Report generation
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Cloud integration
- Real-time monitoring
- Cross-platform compatibility
- Advanced encryption
- Automated reporting
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Easy navigation
- Customizable dashboards
- Quick setup
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Step-by-step guides
- Access to webinars
- Chatbot assistance
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple contact channels
- Response time
- Knowledgeable staff
- Comprehensive FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Free trial availability
- Feature-to-cost ratio
- Discounts for long-term plans
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- User satisfaction
- Highlighted strengths
- Reported weaknesses
- Frequency of updates
- Community engagement
How to Choose Digital Forensics Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your team? Consider if it supports more users or increased data volume as your needs expand. Avoid tools that limit growth with high upgrade costs. |
| Integrations | Does it work with your existing tools? Check if it connects easily with systems you already use to avoid workflow disruptions. Look for APIs or pre-built connectors. |
| Customizability | Can you tailor it to fit your processes? Evaluate if you can adjust settings or workflows to match your team's needs without extra costs or complications. |
| Ease of use | Is it user-friendly for your team? Ensure that non-technical staff can navigate it without extensive training. Look for intuitive interfaces and straightforward navigation. |
| Implementation and onboarding | How quickly can you get started? Assess the time and resources needed to implement the software and train your team. Look for tools that offer guided setups and training resources. |
| Cost | Does it fit your budget? Compare the total cost of ownership, including hidden fees or charges for essential features. Seek transparent pricing models. |
| Security safeguards | Are your data and investigations protected? Verify if the software meets your security standards, including encryption and access controls. Check for compliance with relevant regulations. |
What Is Digital Forensics Software?
Digital forensics software is a tool used to collect, analyze, and report on digital data for investigative purposes. These tools are commonly used by law enforcement, cybersecurity professionals, and IT teams to uncover and understand digital evidence. Data recovery, evidence collection, and file analysis capabilities help with accurate investigations and compliance with regulations. Overall, these tools provide essential support for uncovering digital truths and maintaining data integrity.
Features
When selecting digital forensics software, keep an eye out for the following key features:
- Data recovery: Retrieves lost or deleted data to aid investigations and ensure nothing is overlooked.
- Evidence collection: Gathers digital evidence systematically, maintaining integrity for legal proceedings.
- File analysis: Examines files for hidden information or anomalies that may indicate tampering or malicious activity.
- Incident response: Offers tools to quickly react to security incidents, minimizing potential damage.
- Report generation: Creates detailed reports to present findings clearly and professionally.
- Cloud integration: Connects with cloud services to extend data access and storage capabilities.
- Real-time monitoring: Provides continuous oversight to detect and respond to threats as they occur.
- Cross-platform compatibility: Ensures the software works across different operating systems and devices.
- Advanced encryption: Protects sensitive data with encryption to prevent unauthorized access.
- Automated reporting: Saves time by generating reports automatically, ensuring consistency and accuracy.
Benefits
Implementing digital forensics software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved accuracy: Data recovery and evidence collection features ensure that investigations are thorough and precise.
- Efficient investigations: Automated reporting and real-time monitoring save time, allowing your team to focus on analysis.
- Enhanced security: Advanced encryption and incident response tools help protect sensitive information from unauthorized access.
- Legal compliance: Report generation and file analysis support adherence to legal standards and regulations in investigations.
- Cross-platform access: Compatibility across devices and operating systems provides flexibility in various environments.
- Scalability: Cloud integration ensures your tools can grow with your data and team needs.
- Quick response: Incident response capabilities allow for immediate action, reducing the impact of security breaches.
Costs & Pricing
Selecting digital forensics software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in digital forensics software solutions:
Plan Comparison Table for Digital Forensics Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic data recovery, limited file analysis, and standard reporting. |
| Personal Plan | $10-$30/user/month | Advanced data recovery, evidence collection, and basic incident response. |
| Business Plan | $50-$100/user/month | Comprehensive file analysis, automated reporting, and cross-platform compatibility. |
| Enterprise Plan | $150-$300/user/month | Real-time monitoring, advanced encryption, customizable dashboards, and priority customer support. |
Digital Forensics Software FAQs
Here are some answers to common questions about digital forensics software:
How do I assess the reliability of digital forensics software?
Evaluate the software’s reputation through references, reviews, and trial versions. Look for feedback on its stability, accuracy, and ease of use. Reliable software should have a strong track record in handling data accurately and providing consistent performance during investigations.
What types of data can digital forensics software collect and analyze?
Digital forensics software can handle various data types, including computer files, mobile data, and cloud-based information. It’s crucial for you to ensure the software supports the specific data sources you work with to maximize its effectiveness in investigations.
Can digital forensics software integrate with existing systems or tools?
Yes, most digital forensics software offers integration capabilities with other tools and systems. Check if it supports seamless connections with your current software ecosystem to enhance workflow efficiency and data management.
What’s Next:
If you're in the process of researching digital forensics software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.