Critical Role of Network Monitoring: Proactive monitoring ensures smooth network operations.
Network as Cardiovascular System: Highlighting the vital role of network health.
Analogous Network Health Practices: Comparing network monitoring to personal health habits.
Essential Network Monitoring: Underscoring the significance of network monitoring.
Boosting Network Security: Emphasizing the crucial link between monitoring and security.
Network monitoring is the continual practice of tracking a computer network's health and performance to guarantee the smooth operation of network services. The primary goal of network monitoring is to detect and address issues as soon as they occur, minimizing downtime and maintaining optimal network performance.
"CTOs should think about network monitoring as the blood vessels and arterial system for their entire organization," says Shankar Somasundaram, CEO at Asimily, a risk management platform for IoT device security. "The productivity of knowledge workers and business processes depend on networks functioning properly for devices, employees, partners, and customers."
Comparing an IT network to the human cardiovascular system might sound dramatic. But the modern network must connect the entire organization – its people, processes, applications, data, devices, infrastructure, and more. In that light, the comparison isn’t dramatic – it’s spot-on.
We can extend the metaphor for a bit: Just as we take measures to ensure our cardiovascular health, network administrators must proactively monitor their network’s health, from performance to security to costs and other requirements. Network performance monitoring tools help IT teams proactively root out potential bottlenecks, outages, and other issues before they impact the bottom line.
In this article, we’ll examine the benefits of network monitoring and the evolving best practices for CTOs to prevent costly disruptions.
What is Network Monitoring?
The discipline of network monitoring aims to achieve exactly what we just laid out: Discovering and observing the entirety of an organization’s network to maximize performance and minimize risks. Not monitoring your network is like operating in the dark – unaware of a potential intrusion, a latency problem, or other network performance issues that cause a service to sag under heavy traffic; the list goes on.
Network monitoring is the practice of keeping your network and everything on it in its desired state rather than its failed state: uptime (not downtime), secure (not breached), fast (not lagging), connected (not disjointed), cost-effective (not costly), and so forth.
A considerable menu of network monitoring tools can help network administrators map and monitor their assets. Network management software can help create a network map and capture the network data vital to ongoing performance monitoring and other needs.
Network Monitoring Best Practices for 2026
Now that we’ve established the why behind network monitoring, it’s time to discuss how.
Network monitoring can essentially be boiled down to three phases: planning, implementation, and response. It all starts with developing an informed, sensible strategy.
Once you’ve done that, it’s also important to recognize that network management – like network devices, users, and IT infrastructure more broadly – is a continuously evolving discipline. With that in mind, we asked Somasundaram to share best practices to keep top of mind in 2026 and beyond. Here’s what he had to say:
1. Ensure Enforcement of Identity
Identity is the new perimeter. Somasundaram posits that identity management and enforcement will receive renewed attention in 2026: “[Ensure] that there’s more specific enforcement of identity before anything can get onto the network.” As network devices have become more diverse and distributed, traditional approaches to network security—things like firewalls and endpoint protection—are no longer enough.
2. Embrace Zero-Trust Architectures
Zero trust principles and architectures aren’t new, but according to Somasundaram, they’ll continue to evolve and mature in 2026. For example, “UEBA (User and Entity Behavior Analytics) will become more functionally useful for allowing short-term authentication and authorization before granting access to resources.”
3. Solidify Your SaaS Security Posture
SaaS security posture management is getting ready for primetime. There are “a thousand flowers blooming right now," says Somasundaram, adding that 2025 appears likely to be an important year in determining which approaches and tools become the dominant ones. Regardless, the continued proliferation of SaaS in the enterprise has added another layer to network monitoring. "Businesses will understand that they must use more SaaS applications and push some authorization to people lower in their organization while maintaining top-level control."
4. IoT will continue to proliferate and drive network traffic
It’s early days yet for IoT in the enterprise. Somasundaram anticipates massive growth of high-end smart devices and low-end “dumb” devices to hit networks in the years ahead. No matter what that mix looks like in your organization, it has one common implication for network monitoring: These devices will increase network traffic, period. "The one thing that any IoT device will give you, high-end or low-end, is network traffic. Monitoring network traffic will become even more valuable for cybersecurity and operational purposes.
There’ll be a whole set of developments to watch in AI. I think we’ll go from a flurry of activity to a smaller set that’s more useful and mainstream over time.
5. Yes, AI is coming for network monitoring
We know, we know – you’ve got some AI hype fatigue. But given the existing relationship between network management and automation – they go hand in hand these days, and practitioners generally advise automating as much of your network monitoring overhead as possible – it follows that AI will eventually impact network monitoring tools and best practices. We’re not quite there yet, but it’s worth keeping tabs on because the momentum behind AI tools in the enterprise doesn’t seem to have any limits.
-

NinjaOne
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Auvik
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

Atera
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
4 Reasons Why Network Monitoring is Important
Before we dig into some of the current best practices and tips, it’s essential to understand the key advantages of network monitoring.
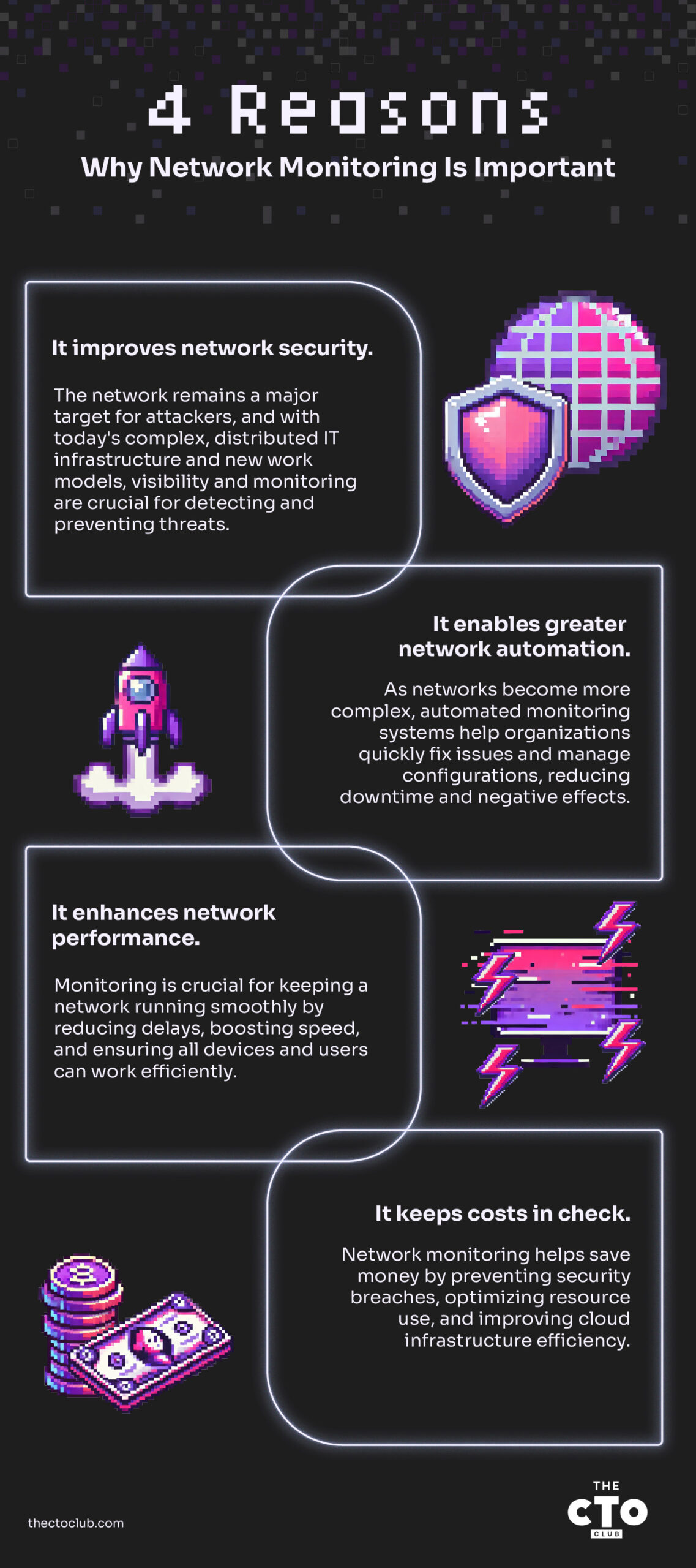
1. It improves network security. The network has long been a primary threat surface for attackers and other bad actors who want to compromise an organization. That’s as true as ever. What has changed regarding network security is that the network – and IT infrastructure more broadly – is as complex and distributed as ever.
Sea changes in IT operating models (think cloud computing and ubiquitous mobile devices, for example) and approaches to work (think remote and hybrid offices, for example) make network visibility and monitoring all the more crucial. Holistic network performance data allows IT teams to define what “normal behavior” looks like on their network – and then be alerted, often with automated responses already set up, when the network deviates from that baseline.
There's a fundamental truth in network security: you can't protect what you don't know or see. Network visibility and monitoring are foundational for minimizing vulnerabilities and keeping threats at bay. Effective network monitoring practices go beyond basic metrics. Techniques like anomaly detection can identify suspicious activity that might evade traditional rule-based monitoring. Anomaly detection works by establishing baselines for network behavior and flagging significant deviations as potential threats.
Furthermore, threat hunting takes a proactive approach to uncovering hidden threats within the network. By analyzing network data for anomalies and suspicious patterns, IT teams can identify and neutralize potential security breaches before they escalate into major incidents.
“It’s knowing this part of the network is not beleaguered,” Somasundaram says. “It’s knowing that very wise attackers with automation don’t sniff something out about your organization as a weakness that directs their attention and resources to your network.
2. It enables greater network automation. As network infrastructure has become more diverse, distributed, and complex, one of the most significant monitoring challenges is that most organizations can’t keep tabs on everything manually.
Modern network monitoring systems enable far more automation, both in terms of alerts and how those alerts are handled and remediated, as well as critical functions such as configuration management. When network issues occur – and they will – automation can reduce response times and get the network back to its desired state faster, minimizing negative impacts.
3. It enhances network performance. Monitoring is also vital for ensuring effective network performance. Comprehensive network performance data helps identify opportunities to reduce latency, increase bandwidth, and ensure that everything and everyone that connects to a network to perform its job—from devices to people—can do so optimally.
4. It keeps costs in check. Revisiting #1 for a moment: network security breaches are costly, both in financial and reputational terms. Minimizing them is itself a cost-saving measure. However, network monitoring offers other potential cost savings. For example, it can identify underutilized or overutilized IT infrastructure, such as CPU and other resources, so network administrators can reduce waste and boost productivity. Collecting performance data and metrics and analyzing them for untapped opportunities is just good business – and it’s made possible by a smart network monitoring strategy.
Going Beyond Uptime: Key Network Metrics to Consider
While ensuring basic network functionality is crucial, effective network monitoring in 2026 goes even deeper. Simply knowing if your network is up or down isn't enough to optimize performance and proactively identify potential issues. This is where monitoring specific network metrics becomes essential. These metrics provide valuable insights into the health and efficiency of your network, allowing you to make data-driven decisions and avoid costly disruptions.
- Bandwidth Usage: The amount of data traffic flowing across your network at any given time. Monitoring bandwidth usage allows you to identify potential bottlenecks, crucial information for optimizing resource allocation and ensuring your network has sufficient capacity to handle future growth. While typical usage varies depending on your organization's size and activity, sudden spikes can indicate unauthorized access, application issues, or overloaded network segments.
- Why this matters: By setting thresholds and alerts for bandwidth usage, you can be notified of potential problems before they disrupt user experience or critical applications.
- Latency: The time it takes for data to travel from one point on your network to another. High latency can significantly impact user experience, especially for applications that require real-time responsiveness. Acceptable latency thresholds depend on the type of application, but generally, lower latency is preferable. Monitoring latency allows you to identify potential issues that might be causing delays, such as overloaded network segments, hardware limitations, or even geographic distance between users and resources.
- Why this matters: By proactively addressing these issues, you can ensure optimal performance for your users and applications.
- Error Rates: Not every packet of data makes it to its destination flawlessly. Network errors can occur due to various reasons, such as hardware malfunctions, signal interference, or even software bugs. Monitoring error rates helps you identify trends and potential problems in your network infrastructure. Different types of errors exist, each with its own implications. For instance, high packet loss rates could indicate failing network hardware or congested links.
- Why this matters: By understanding the different types of errors and monitoring their occurrence, you can pinpoint potential issues and take corrective action before they escalate into major outages
Real-World Examples of Effective Network Monitoring
Network monitoring isn't just theoretical; it has tangible benefits for businesses across various industries. Here are a couple of real-world examples showcasing the impact of effective network monitoring:
- Retail Giant Avoids Black Friday Meltdown
Imagine the potential disaster for a major online retailer experiencing a network outage on Black Friday, one of the busiest shopping days of the year. This scenario almost became a reality for a large retail company. However, thanks to their robust network monitoring system, they were able to avert a potential catastrophe.
The monitoring system detected a gradual increase in bandwidth usage throughout the day. By analyzing historical data and setting custom thresholds, the network team identified this surge as unusual for their typical Black Friday traffic patterns. This early warning allowed them to quickly investigate and discover a faulty network switch that was nearing capacity. The switch was promptly replaced before it could overload and cause a widespread outage.
This proactive approach, made possible by effective network monitoring, saved the company from millions in lost sales and a significant blow to its customer reputation.
- Hospital Ensures Patient Care Continuity
Maintaining a reliable network is critical for hospitals to provide uninterrupted patient care. A healthcare facility implemented a network monitoring solution that provided real-time insights into network performance.
One evening, the monitoring system identified an anomaly in latency – the response time for data traveling across the network. Further investigation revealed a failing router on a critical network segment responsible for connecting medical devices and electronic health records. The IT team was able to isolate the issue and reroute traffic before it impacted patient care or medical staff access to vital information.
This swift action, enabled by network monitoring, ensured the continued smooth operation of the hospital's IT infrastructure, potentially saving lives and preventing delays in critical medical procedures.
Setting Up Network Monitoring Systems and Configuring Alerts
So, now you know everything about network monitoring best practices, and you want to set up and configure your system. Network monitoring systems come in various flavors, from on-premises software to cloud-based solutions. The specific setup process will differ depending on the chosen platform. However, I'll share a general step-by-step guide to get you started:
1. Choose Your Network Monitoring Solution:
- Consider your needs and budget. Cloud-based solutions offer ease of use but might have limitations on customization. On-premises solutions provide greater control but require more technical expertise for setup and maintenance.
2. Install or Access Your Monitoring Software:
- Follow the vendor's instructions for installation if using an on-premises solution. Cloud-based platforms typically require account creation and login.
3. Add Devices to Monitor:
- Most solutions offer methods for automatically discovering devices on your network. You can also manually add specific devices by IP address or hostname.
4. Configure Monitoring Parameters:
- Define the metrics you want to monitor for each device (e.g., bandwidth usage, latency, packet loss).
- Set thresholds for alerts. These are trigger points for notifications when a specific metric exceeds or falls below a defined value.
Here's where a one-size-fits-all approach becomes difficult.
The ideal metrics and thresholds will vary depending on your network configuration, device types, and business needs. For instance, acceptable latency for a web server might be different from a real-time video-conferencing application.
Here are some general best practices for configuring alerts:
- Start with a Focused Set: Don't overwhelm yourself with excessive alerts. Begin by monitoring critical metrics and devices, then gradually expand.
- Set Realistic Thresholds: Avoid overly sensitive thresholds that trigger constant alerts for minor fluctuations.
- Prioritize Alerts: Distinguish between critical, warning, and informational alerts based on their potential impact.
- Define Alert Actions: Determine what happens when an alert is triggered (e.g., email notification, SMS message, automated troubleshooting scripts).
5. Test Your Monitoring System:
- Simulate potential network issues (e.g., artificial bandwidth overload) to ensure alerts function as expected.
Build a Strong Foundation
The nature of enterprise IT networks has undoubtedly evolved over the years, but the fundamental need to monitor and manage those networks has not—it’s crucial to effective IT management and an organization's overall success.
Effective network monitoring is the foundation for better performance, stronger security, and reduced costs. Subscribe to The CTO Club newsletter for more industry news and discussions.