Liste des meilleurs outils SIEM
Choisir les bons outils de gestion des informations et des événements de sécurité (SIEM) peut faire la différence entre détecter une menace en quelques minutes ou la rater complètement.
Avec près de dix ans d'expérience en cybersécurité et en supervision d'infrastructures, j’ai évalué des dizaines de plateformes SIEM en entreprise, SaaS et environnements hybrides. Les meilleurs outils ne se contentent pas de centraliser les journaux : ils corrèlent les événements, automatisent la détection des incidents et aident les équipes de sécurité à réagir plus vite sous pression.
Dans ce guide, je partage les outils SIEM qui ont prouvé à plusieurs reprises leur fiabilité, leur scalabilité et leur capacité d’intégration dans des opérations de sécurité réelles. Chaque recommandation s’appuie sur une expérience concrète d’utilisation de ces plateformes pour renforcer la visibilité, la conformité et le temps de réaction des équipes d’ingénierie en croissance.
Pourquoi faire confiance à nos avis sur les logiciels ?
Nous testons et évaluons des logiciels depuis 2023. En tant que spécialistes IT et data, nous savons combien il est crucial et complexe de prendre la bonne décision lors du choix d’un logiciel.
Nous investissons dans des recherches approfondies pour aider notre audience à prendre de meilleures décisions d’achat logiciel. Nous avons testé plus de 2 000 outils pour différents cas d’utilisation IT et rédigé plus de 1 000 analyses logicielles détaillées. Découvrez comment nous restons transparents & notre méthodologie de test.
Résumé des meilleurs outils SIEM
Ce tableau comparatif résume les détails tarifaires de mes principales sélections de logiciels SIEM pour vous aider à trouver le plus adapté à votre budget et à vos besoins métier.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Idéal pour l'intelligence sur les menaces | Démo gratuite disponible | Tarification sur demande | Website | |
| 2 | Idéal pour les petites et moyennes entreprises | Démo gratuite disponible | À partir de $0.09/GB/mois | Website | |
| 3 | Idéal pour une surveillance continue et une réponse rapide | Essai gratuit + démo gratuite disponible | Tarification sur demande | Website | |
| 4 | Am besten geeignet für Workflow-Automatisierung | Preise auf Anfrage | Website | ||
| 5 | Idéal pour les fournisseurs de solutions informatiques | Essai gratuit sur demande | Tarification sur demande | Website | |
| 6 | Idéal pour la détection avancée des menaces | Démo gratuite disponible | Tarification sur demande | Website | |
| 7 | Idéal pour les entreprises multi-cloud | Essai gratuit de 31 jours | À partir de 2,46 $/Go (paiement à l'utilisation) | Website | |
| 8 | Idéal pour un large éventail d'intégrations | Essai gratuit de 14 jours | À partir de 95 $/mois | Website | |
| 9 | Idéal pour les visualisations SIEM | Essai gratuit de 14 jours | À partir de $15/hôte/mois | Website | |
| 10 | Idéal pour la détection des menaces en temps réel | Démo gratuite disponible. | Les tarifs varient selon le modèle de licence, le type de déploiement et l'ensemble des fonctionnalités. | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Avis détaillés sur les meilleurs logiciels SIEM
Vous trouverez ci-dessous mes analyses détaillées des meilleurs logiciels SIEM ayant rejoint ma sélection. Mes avis offrent un aperçu complet de leurs fonctionnalités clés, avantages & inconvénients, intégrations et cas d’utilisation idéaux pour vous aider à choisir l’outil qui vous convient.
ManageEngine Log360 est une solution de gestion des informations et des événements de sécurité (SIEM) conçue pour aider les organisations à surveiller et à gérer leur infrastructure informatique.
Pourquoi j'ai choisi ManageEngine Log360 : J'ai sélectionné ManageEngine Log360 en raison de son approche globale de la gestion de la sécurité. Il intègre diverses fonctionnalités telles que le renseignement sur les menaces, la détection d'anomalies basée sur l'apprentissage automatique et la détection d'attaques basée sur des règles pour offrir un cadre de sécurité robuste. La capacité du logiciel à fournir des analyses et des informations en temps réel sur les environnements locaux, cloud et hybrides garantit une approche complète et dynamique de la détection et de la réponse aux menaces.
Fonctionnalités et intégrations phares de ManageEngine Log360 :
Fonctionnalités : on retrouve notamment l’analyse du comportement des utilisateurs et des entités (UEBA). Cette fonctionnalité utilise des algorithmes avancés d'apprentissage automatique pour établir des références d'activité normale, puis détecter toute déviation pouvant indiquer des menaces potentielles. Une autre fonctionnalité remarquable est la réponse automatisée aux menaces, qui permet de réduire le délai entre la détection d'une menace et sa neutralisation en automatisant le processus de réponse.
Intégrations : Microsoft Active Directory, Office 365, Google Workspace, AWS, Azure, Salesforce, Box, ServiceNow, Jira, Slack, IBM QRadar, Splunk, SolarWinds, Palo Alto Networks, Fortinet, Cisco et Sophos.
Pros and Cons
Pros:
- Gestion centralisée des journaux et des événements de sécurité
- Alertes en temps réel
- Fonctionnalités d'intelligence sur les menaces
Cons:
- Le déploiement peut être complexe
- Nécessite une maintenance et des mises à jour régulières
New Product Updates from ManageEngine Log360
ManageEngine Log360 Adds New Log Source Integrations
ManageEngine Log360 introduced new integration support for NetFlow Analyzer and Firewall Analyzer, along with enhanced audit log parsing for OpManager products. The updates help teams centralize log collection and improve monitoring and analysis workflows. For more information, visit ManageEngine Log360's official site.
Logmanager offre aux petites et moyennes entreprises un SIEM facile à déployer et à maintenir, sans avoir à recruter un ingénieur sécurité dédié. Il aide votre équipe à détecter les menaces plus rapidement en unifiant les journaux provenant de l'ensemble de votre environnement et en fournissant un contexte clair pour enquêter sur les incidents.
Pourquoi j'ai choisi Logmanager
J'ai choisi Logmanager car il permet de gérer des fonctionnalités SIEM sans devoir jongler avec de nombreuses étapes de configuration complexes, grâce à ses parseurs, alertes et tableaux de bord prêts à l'emploi. Vous pouvez obtenir une visibilité sur l'ensemble de votre infrastructure en centralisant les journaux de plus de 140 sources compatibles, ce qui vous aide à détecter des événements suspects avec un contexte fiable. Ses outils d'automatisation sans code permettent à votre équipe d'adapter les règles, alertes et flux de travail sans avoir à écrire de script. J'apprécie également qu'il soutienne les initiatives de conformité en vous donnant rapidement accès à l'historique des journaux et à des rapports prêts pour l'audit.
Fonctionnalités clés de Logmanager
Ces fonctionnalités renforcent la valeur de Logmanager pour les équipes qui ont besoin d'une analyse des journaux évolutive sans la complexité des solutions d'entreprise :
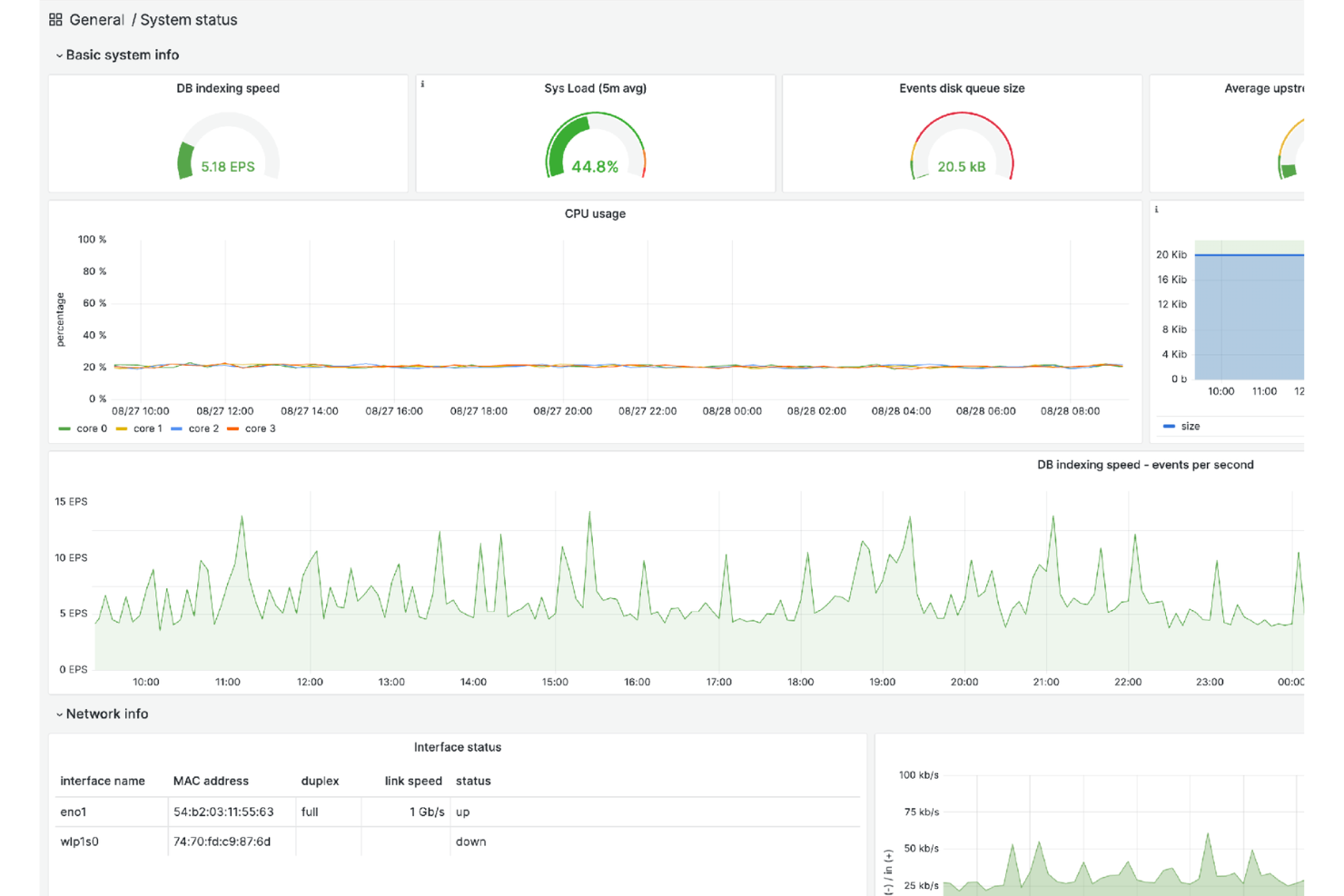
- Tableaux de bord prédéfinis : Affichez en un coup d'œil les performances système, les événements de sécurité et le statut de conformité.
- Rapports de conformité : Génère des analyses prêtes pour l'audit en conformité avec des normes telles que le RGPD, l'ISO 27001 et la directive NIS2.
- Recherche haute vitesse : Permet un filtrage et une récupération des journaux rapides lors des investigations.
- Alertes personnalisées : Laisse les équipes définir des conditions qui déclenchent des notifications pour des activités à haut risque.
Intégrations Logmanager
Les intégrations incluent Apache Tomcat, Aruba Networks, CheckPoint Firewall, équipements Cisco, Dell iDRAC, ESET Remote Administrator, produits Fortinet, IBM AIX Syslog, produits Microsoft et MySQL.
Pros and Cons
Pros:
- Tableaux de bord personnalisables offrant une visibilité complète sur l'infrastructure
- Recherche rapide qui accélère les temps d'investigation sur les incidents
- S'adapte à la croissance du volume de journaux dans les environnements hybrides
Cons:
- Certains flux de personnalisation nécessitent une connaissance approfondie des SIEM
- Le prix peut être élevé pour les très petites équipes
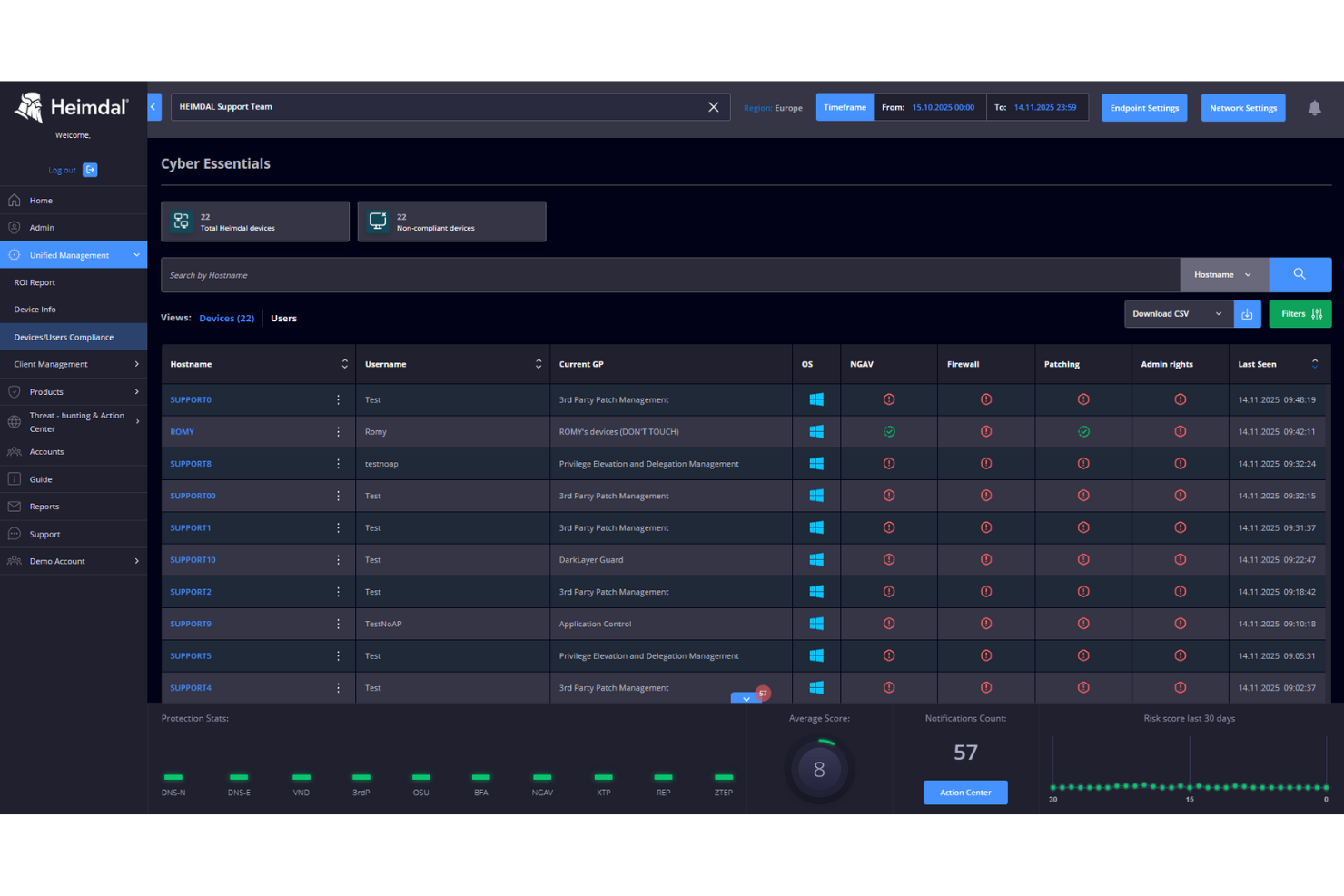
Dans un monde où les menaces informatiques évoluent chaque jour, Heimdal se distingue comme une solution polyvalente pour ceux qui recherchent un outil de gestion des informations et des événements de sécurité (SIEM). Adapté à des secteurs tels que la santé, le gouvernement et les infrastructures critiques, il répond aux défis liés à la conformité et à la gouvernance des données. Grâce à des fonctionnalités comme la chasse aux menaces et la sécurité des endpoints, Heimdal permet à votre organisation d’anticiper les violations de sécurité potentielles, assurant ainsi la tranquillité d’esprit des professionnels de l’informatique et des dirigeants d’entreprise.
Pourquoi j’ai choisi Heimdal
J’ai choisi Heimdal pour sa combinaison unique de Détection et Réponse Managées Étendues (MXDR) et de support d’un centre d’opérations de sécurité (SOC) disponible 24/7. Ces fonctionnalités sont essentielles pour les entreprises nécessitant une surveillance constante et une réponse rapide aux incidents. La capacité de Heimdal à s’intégrer aux applications tierces renforce sa flexibilité, et son accent mis sur la conformité avec des normes telles qu’ISO 27001 et HIPAA assure à votre organisation de respecter les réglementations du secteur. Les capacités complètes de détection des menaces de la plateforme répondent au besoin crucial de mesures de sécurité proactives, en faisant un choix judicieux pour toute structure.
Principales fonctionnalités de Heimdal
En plus de ses solides capacités MXDR et SOC, j’ai également constaté que Heimdal propose plusieurs autres fonctionnalités intéressantes :
- Chasse aux menaces : Cette fonctionnalité permet de rechercher activement les menaces potentielles au sein de votre réseau, apportant une couche de sécurité supplémentaire.
- Gestion des vulnérabilités : Heimdal aide à identifier et corriger les vulnérabilités de vos systèmes pour prévenir d’éventuelles failles.
- Sécurité des endpoints : Il offre une protection avancée pour les appareils endpoints, garantissant que tous les points d’accès sont sécurisés.
- Sécurité des e-mails : Cette fonctionnalité protège contre les menaces par e-mail, y compris le phishing et les tentatives de fraude, assurant la sécurité des canaux de communication de votre organisation.
Intégrations de Heimdal
Les intégrations natives ne sont actuellement pas listées par Heimdal ; cependant, la plateforme prend en charge des intégrations personnalisées via API.
Pros and Cons
Pros:
- Automatise le déploiement des correctifs sur les endpoints
- Détection poussée des vulnérabilités et menaces
- Visibilité détaillée des actifs et licences
Cons:
- Aucune intégration native disponible
- L’interface nécessite une phase d’onboarding
Am besten geeignet für Workflow-Automatisierung
ArcSight Enterprise Security Manager bietet Echtzeit-Bedrohungserkennung und -analysen. Es unterstützt Unternehmen dabei, ihre Bedrohungsexponierung zu reduzieren und gesetzliche Anforderungen einzuhalten.
Warum ich mich für ArcSight Enterprise Security Manager entschieden habe: Was mir an ArcSight Enterprise Security Manager besonders gefallen hat, sind die leistungsstarken Funktionen zur Workflow-Automatisierung. Sobald eine Bedrohung erkannt wird, erfolgt eine Klassifizierung und automatische Fallzuweisung an einen Analysten. Sie können diese Workflows oder 'Playbooks' je nach Bedarf manuell einrichten.
Herausragende Funktionen und Integrationen von ArcSight Enterprise Security Manager:
Funktionen, die ArcSight Enterprise Security Manager auszeichnen, sind die Ereigniskorrelations-Engine, die Tausende von Ereignissen pro Sekunde verfolgen und bei verdächtigen Aktivitäten Alarme auslösen kann. Ich fand die Anpassung dieser Regelsets für verschiedene SIEM-Anwendungsfälle unkompliziert.
Integrationen sind nativ mit ArcSight Intelligence verfügbar, um die Bedrohungserkennung zu verbessern, und mit ArcSight Recon, um das Log-Management zu optimieren. ArcSight Enterprise Security Manager lässt sich außerdem nativ mit SOC-Tools wie Qualys, AhnLab und Satrix integrieren.
Pros and Cons
Pros:
- Echtzeit-Korrelations-Engine hilft, Bedrohungen präzise zu erkennen
- Intelligente Risikobewertung hilft bei der Priorisierung von Sicherheitsbedrohungen
- Dashboards und Berichte sind hochgradig anpassbar
Cons:
- Verzögerte Antwortzeiten bei Datenbankabfragen
- Keine Preisinformationen verfügbar
Idéal pour les fournisseurs de solutions informatiques
ConnectWise SIEM, anciennement Perch, est une plateforme SIEM qui permet aux fournisseurs de solutions informatiques d’aider leurs clients à protéger leurs réseaux contre les cyberattaques.
Pourquoi j’ai choisi ConnectWise SIEM : À mon avis, ConnectWise SIEM mérite sa place dans cette liste car il est spécifiquement conçu pour les prestataires de services informatiques. Il propose des déploiements flexibles sur site et dans le cloud, ainsi que des évaluations complètes des risques qui vous aident à comprendre l’état de l’infrastructure informatique de vos clients. Ce que j’apprécie, c’est que ConnectWise SIEM effectue des analyses réseau automatisées et hiérarchise les menaces potentielles en fonction de leur impact.
Fonctionnalités et intégrations remarquables de ConnectWise SIEM :
Les fonctionnalités qui rendent ConnectWise SIEM adapté aux fournisseurs de solutions informatiques sont ses objectifs de niveau de service (SLO) que vous pouvez définir pour vos clients. Je pense que les SLO sont un excellent moyen de fixer des attentes claires et d’aider les clients à percevoir la valeur d’une plateforme SIEM. ConnectWise SIEM vous permet également d’aider les entreprises à répondre aux exigences de conformité et de réglementation.
Les intégrations sont accessibles nativement via le ConnectWise Marketplace. Parmi les partenaires notables figurent Fortinet, Perimeter 81, Orbitera, SonicWall et Trend Micro.
Pros and Cons
Pros:
- Propose des déploiements flexibles sur site et dans le cloud
- S’intègre avec d’autres produits ConnectWise
- Permet de créer des rapports à destination des clients
Cons:
- Certains utilisateurs signalent des problèmes d'évolutivité
- Certaines intégrations peuvent ne pas être disponibles
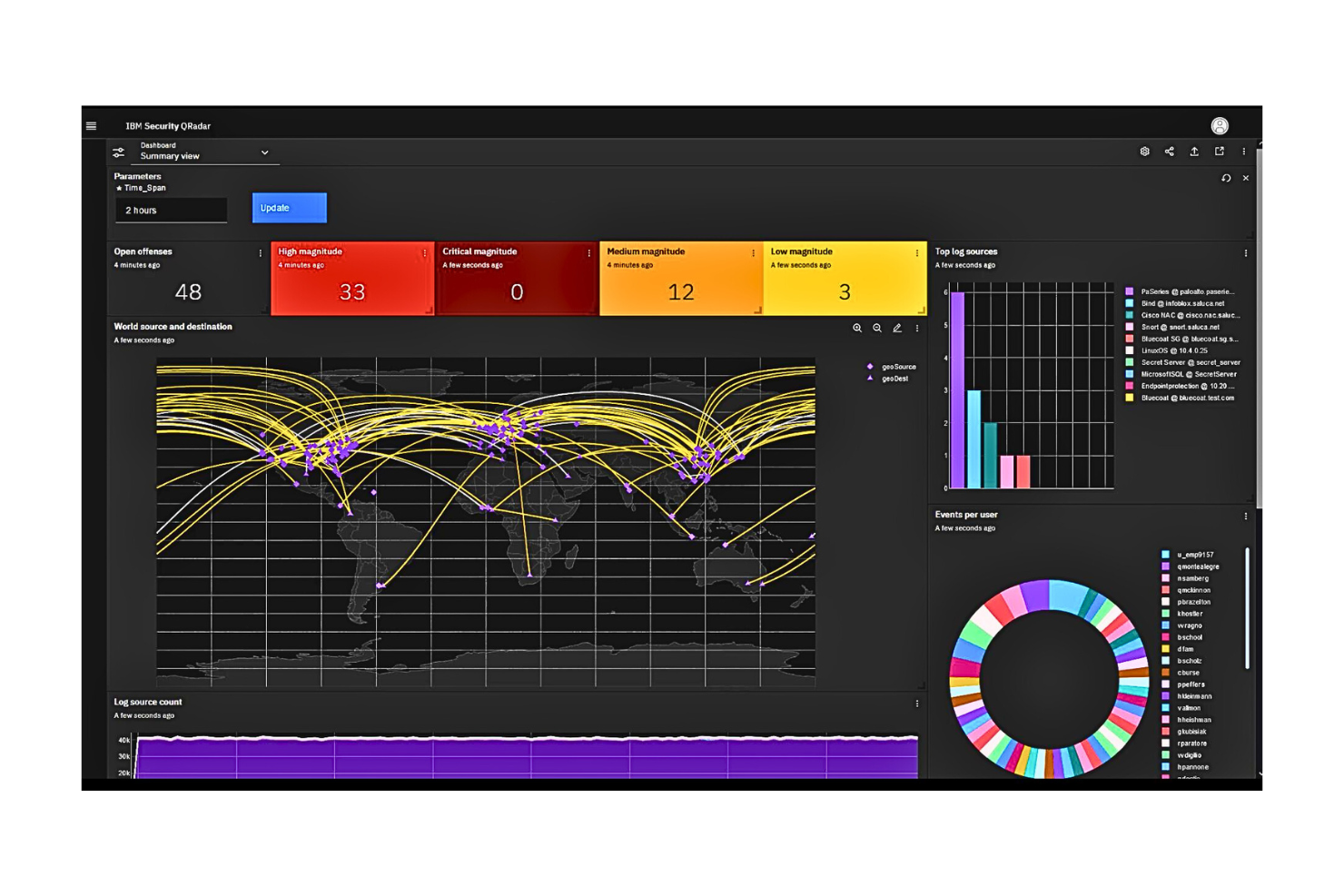
IBM Security QRadar SIEM est une plateforme SIEM évolutive qui collecte les données liées à la sécurité provenant des appareils d'extrémité et des applications sur l'ensemble d'un réseau. Elle permet aux équipes de sécurité de surveiller leur infrastructure informatique depuis un seul endroit.
Pourquoi j'ai choisi IBM Security QRadar : J'ai choisi IBM Security QRadar SIEM pour ses capacités avancées de détection des menaces. Il utilise l'IA ainsi que l'analyse du comportement réseau et utilisateur pour détecter les menaces de sécurité en quasi temps réel. J'ai également apprécié que la plateforme assigne à chaque infraction un score de gravité, ce qui m'a permis de prioriser plus facilement les problèmes les plus critiques.
Caractéristiques et intégrations remarquables d'IBM Security QRadar SIEM :
Les fonctionnalités qui distinguent IBM Security QRadar SIEM, selon moi, incluent ses intégrations natives avec plus de 700 produits de sécurité, offrant ainsi une visibilité étendue du réseau. Une autre fonctionnalité qui m'a marqué est le centre des opérations de sécurité (SOC) de la plateforme. Je pouvais facilement examiner chaque menace en détail et obtenir davantage d'informations sur chacune.
Les intégrations sont disponibles nativement avec plus de 370 applications et 450 modules de support d'appareils (DSM) comme Amazon AWS Network Firewall, Cisco ACE Firewall, et Google Cloud Audit Logs. Vous pouvez également utiliser l’API REST cloud universelle d’IBM pour créer des intégrations personnalisées.
Pros and Cons
Pros:
- Prend en charge un large éventail de sources de logs d'événements
- Compatible avec des cadres de sécurité et de confidentialité comme ISO 27001
- Propose des déploiements sur site et dans le cloud
Cons:
- Les déploiements à grande échelle peuvent être difficiles à mettre en œuvre
- Les performances peuvent diminuer lors du traitement de gros volumes de données
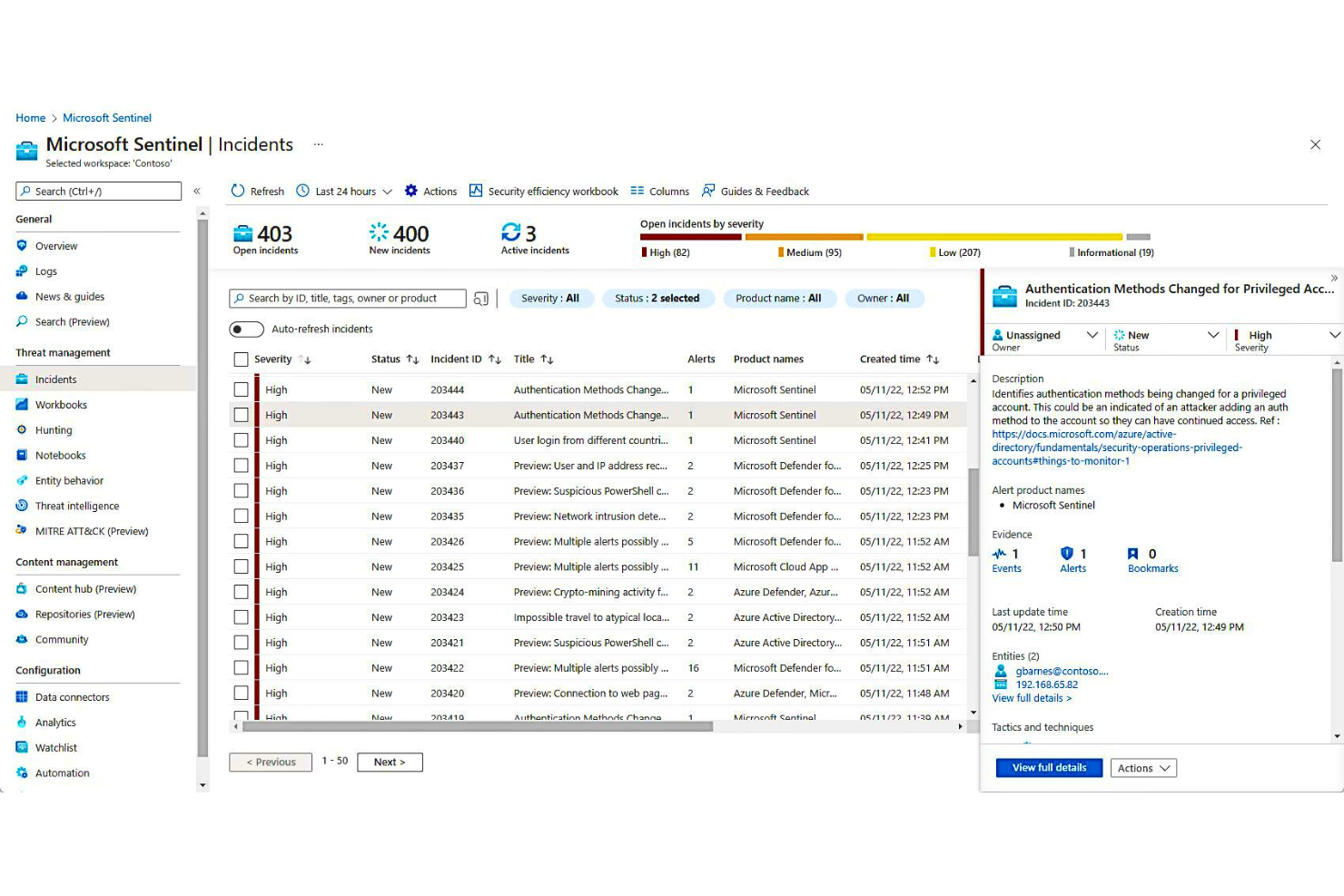
Microsoft Azure Sentinel est une solution SIEM basée sur le cloud capable d'ingérer des données provenant de diverses sources et de détecter les menaces avant qu'elles ne s'aggravent. Elle est construite sur la plateforme Azure, qui offre flexibilité et évolutivité.
Pourquoi j'ai choisi Microsoft Azure Sentinel : Ce qui rend Microsoft Azure Sentinel remarquable en tant qu'outil SIEM, à mon avis, c'est sa capacité à collecter et analyser les données à l'échelle du cloud — un aspect important à considérer, surtout si votre entreprise utilise plusieurs fournisseurs cloud. J'apprécie également son intégration native avec la plateforme de cloud computing Azure, car cela signifie qu'il peut automatiquement s'adapter à tous les besoins de sécurité.
Fonctionnalités et intégrations remarquables de Microsoft Azure Sentinel :
Fonctionnalités : je trouve que Microsoft Azure Sentinel se distingue notamment par ses analyses de sécurité avancées, qui utilisent l'IA pour détecter les menaces et réduire le nombre de faux positifs. Cela facilite la priorisation des incidents représentant de véritables risques. La plateforme propose également un système de gestion des workflows avec des règles prédéfinies pour automatiser les tâches de sécurité à grande échelle.
Intégrations : plus de 130 connecteurs de données préconfigurés avec des sources comme AWS, Citrix, Elastic, Ivanti et Juniper. Vous pouvez également utiliser les API REST de la plateforme pour l'intégration avec d'autres connecteurs de données.
Pros and Cons
Pros:
- S'intègre avec les autres produits de sécurité Microsoft
- Propose une tarification flexible à l'utilisation
- Peut automatiquement s'adapter à vos besoins en sécurité
Cons:
- Non adapté aux petites entreprises
- Nécessite un investissement initial important pour la mise en place de la solution
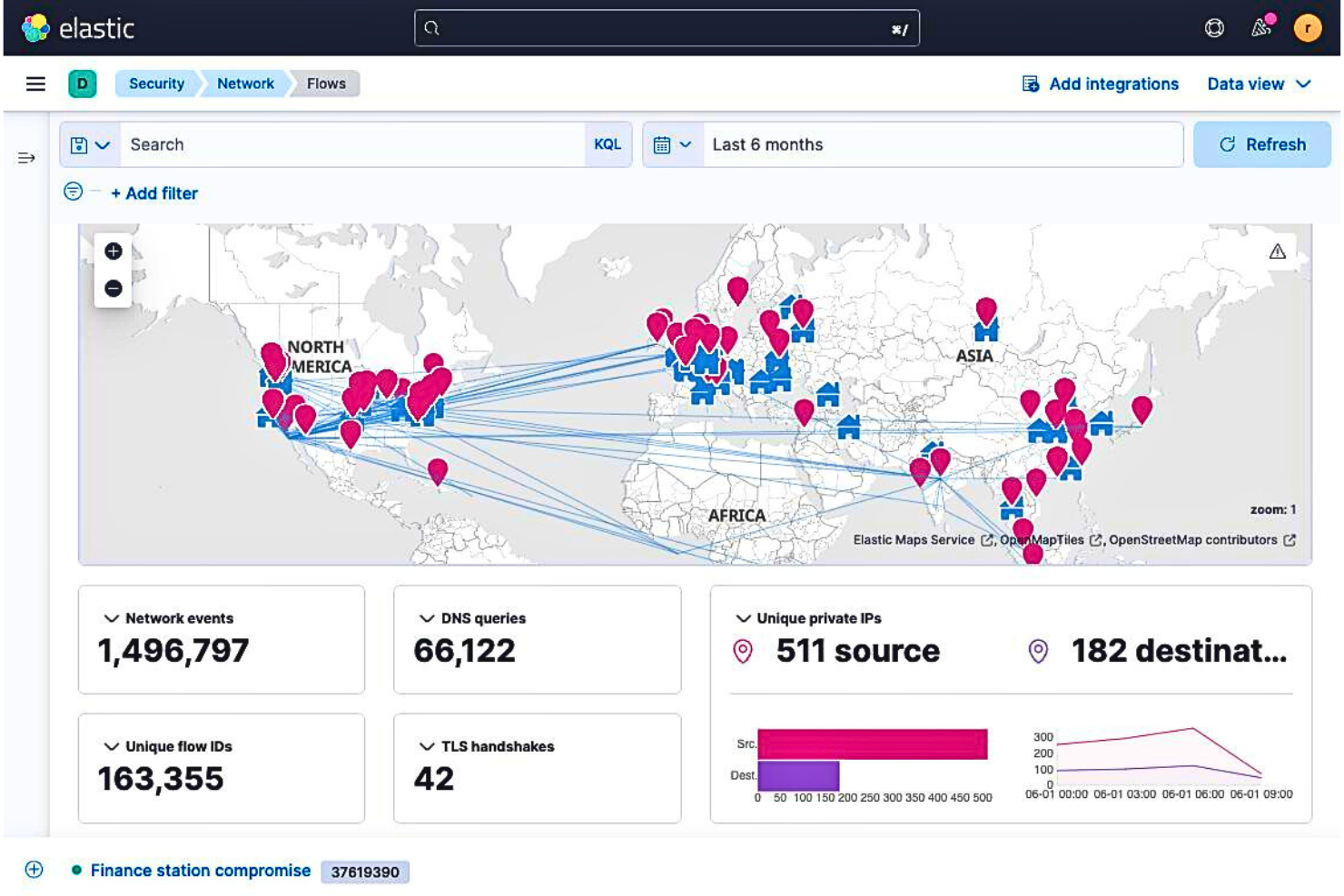
Elastic Security vous offre une vue holistique de vos données, où qu'elles se trouvent. Il fournit une gestion centralisée des journaux et des capacités d'intervention rapide afin de renforcer la sécurité du réseau.
Pourquoi j'ai choisi Elastic Security : J'ai sélectionné Elastic Security dans cette liste en raison de son large éventail d'intégrations natives impressionnantes. Il peut ingérer des métriques, des journaux et des événements provenant de diverses sources de données, offrant ainsi une vue plus complète de votre posture de sécurité. Les intégrations en un clic m'ont permis d'ajouter facilement de nouvelles sources et d'étendre la visibilité du SIEM.
Fonctionnalités et intégrations remarquables d’Elastic Security :
Fonctionnalités qui, selon moi, méritent d'être mentionnées concernant Elastic Security incluent ses outils interactifs qui vous aident à effectuer une analyse des causes profondes d’un incident et à mettre en œuvre de nouvelles règles pour éviter de futurs incidents. Vous pouvez également utiliser des règles créées par des chercheurs en menaces Elastic et des membres de la communauté afin d'améliorer la détection des menaces.
Intégrations disponibles nativement avec des applications, bases de données, équipements réseau et outils de travail collaboratif. Les intégrations notables incluent AWS, Apache Spark, Microsoft Azure, Cisco Umbrella et Jira. Vous pouvez également utiliser les API REST de la plateforme pour connecter davantage de sources.
Pros and Cons
Pros:
- Capacité à ingérer et analyser des données à l’échelle du cloud
- Les intégrations en un clic facilitent l’ajout de nouvelles sources de données
- Propose des options tarifaires flexibles
Cons:
- Moins robuste que d'autres solutions SIEM sur le marché
- Peut ne pas convenir aux organisations avec des besoins de sécurité complexes
Datadog Cloud SIEM est une solution SIEM native du cloud qui analyse les journaux opérationnels et de sécurité à travers l'ensemble de votre pile technologique, offrant aux équipes opérationnelles une vue d'ensemble du niveau de sécurité de l'entreprise.
Pourquoi j'ai choisi Datadog Cloud SIEM : Lors de mes tests, j'ai été impressionné par les visualisations offertes par la plateforme. L'interface facilitait la visualisation des activités des utilisateurs et des services. Ce niveau de visibilité a grandement amélioré la collaboration, car mon équipe et moi avons pu approfondir les incidents et identifier la cause racine des menaces de sécurité.
Fonctionnalités marquantes et intégrations de Datadog Cloud SIEM :
Fonctionnalités : ce qui distingue Datadog Cloud SIEM à mes yeux, ce sont ses règles de détection des menaces prêtes à l'emploi qui permettent aux entreprises d'améliorer la sécurité de leur réseau sans passer beaucoup de temps à les configurer. Pour les entreprises aux besoins spécifiques, Datadog Cloud SIEM inclut un éditeur sans code qui permet de créer vos propres règles.
Intégrations : disponibles nativement avec plus de 600 applications, fournisseurs d'identité et endpoints. Parmi les intégrations principales, on retrouve AWS, Azure DevOps, Redis et Jira.
Pros and Cons
Pros:
- Solution cloud-native permettant une plus grande évolutivité
- Propose des filtres de recherche avancés pour affiner vos résultats
- L'ingestion de données est rapide et fiable
Cons:
- L'offre gratuite est limitée en fonctionnalités
- L'analyse des journaux pourrait être améliorée
Introduction
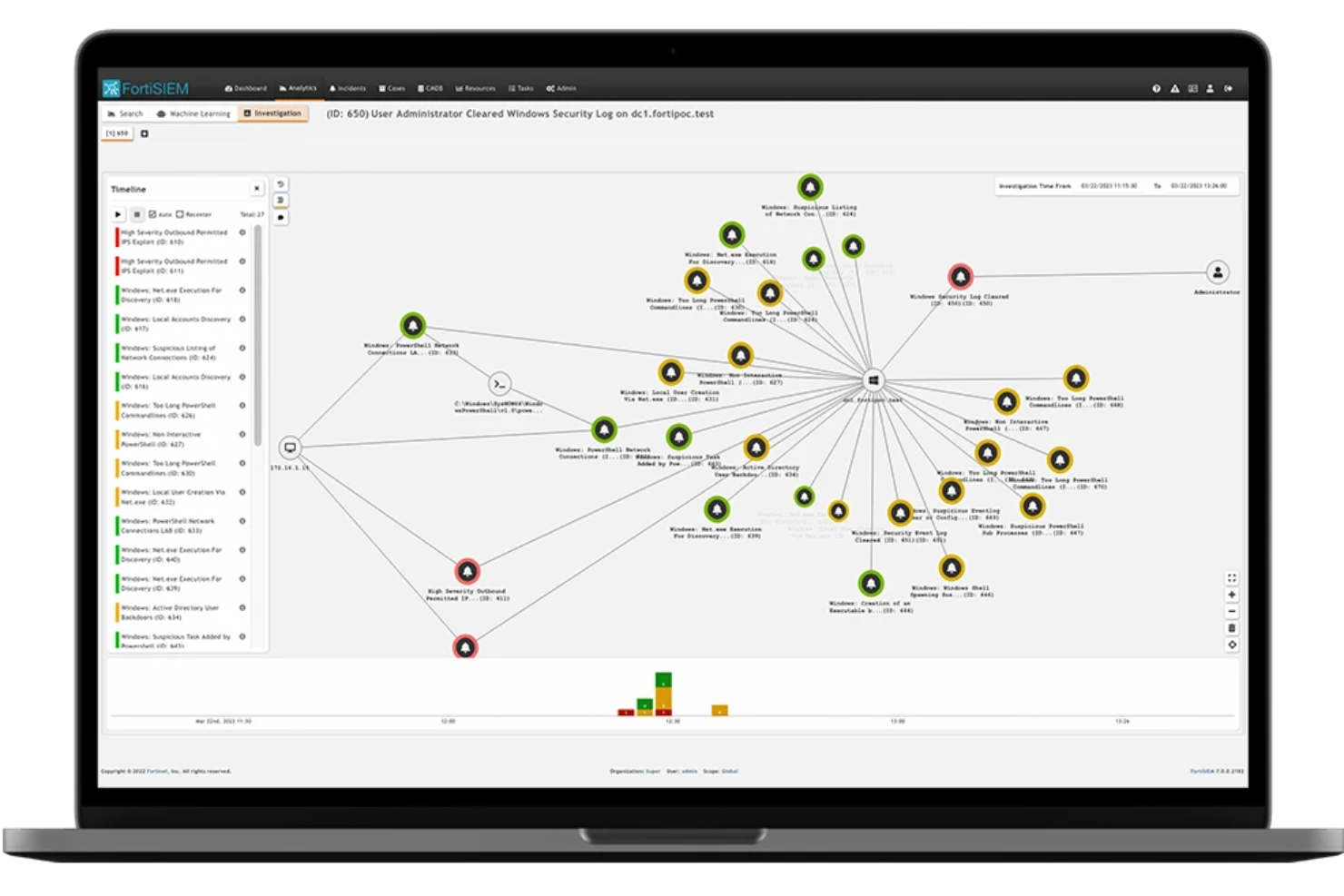
Fortinet FortiSIEM est un outil sophistiqué de gestion des informations et des événements de sécurité (SIEM) conçu pour renforcer vos opérations de sécurité. Il offre une suite complète de fonctionnalités qui vous aident à détecter les menaces en temps réel et à automatiser les réponses aux incidents, garantissant ainsi la sécurité et la conformité de votre réseau.
Pourquoi j'ai choisi
J'ai choisi Fortinet FortiSIEM pour sa capacité exceptionnelle à détecter les menaces en temps réel. Cette fonctionnalité vous permet d'identifier les menaces potentielles au fur et à mesure qu'elles surviennent, vous donnant ainsi l'occasion de réagir rapidement et de minimiser les risques. De plus, les analyses avancées de FortiSIEM offrent des aperçus approfondis sur la sécurité, permettant à votre équipe de comprendre et de remédier plus efficacement aux vulnérabilités.
Un autre point fort de FortiSIEM est sa réponse automatisée aux incidents. Cette fonctionnalité simplifie le traitement des incidents de sécurité, réduisant la charge de travail de votre équipe et lui permettant de se concentrer sur des tâches plus stratégiques. Avec FortiSIEM, vous pouvez garantir une gestion rapide et efficace des incidents, minimisant ainsi les interruptions et les éventuels dégâts.
Fonctionnalités remarquables
Les fonctionnalités incluent une base de données de gestion de la configuration (CMDB) qui permet une surveillance complète des actifs, assurant une visibilité sur l'ensemble de votre réseau. L'outil prend en charge plus de 2800 règles de corrélation qui aident à identifier les schémas révélateurs de menaces potentielles. De plus, FortiSIEM propose une automatisation SOAR intégrée, simplifiant les opérations de sécurité en automatisant les tâches répétitives afin que votre équipe puisse se concentrer sur les enjeux les plus critiques.
Intégrations
Les intégrations incluent AWS, Microsoft Azure, Google Cloud, Oracle Cloud, Cisco, ServiceNow, Salesforce, Jira, Bitdefender, Citrix, Claroty et Acronis.
Autres logiciels SIEM
Voici une sélection de quelques outils SIEM supplémentaires qui n’ont pas intégré mon top mais qui méritent quand même d’être considérés :
- AT&T USM Anywhere
Idéal pour une réponse rapide aux menaces
- ArcSight Enterprise Security Manager
Idéal pour l'automatisation des workflows
- Rapid7 InsightIDR
Meilleure protection des terminaux
- Splunk Enterprise Security
Idéal pour les alertes basées sur les risques
- ManageEngine EventLog Analyzer
Idéal pour la surveillance de l'intégrité des fichiers
- Exabeam SIEM
Idéal pour faire évoluer la gestion des journaux
- Graylog
Idéal pour la gestion des journaux en temps réel
- LogRhythm SIEM
Idéal pour les déploiements sur site
- Securonix
Idéal pour la détection avancée des menaces
- Logpoint Converged SIEM
Idéal pour l’ingestion centralisée des données
- RSA NetWitness
Idéal pour la surveillance avec capture complète de paquets
- Paessler PRTG
Idéal pour les organisations de petite à moyenne taille
- Trellix Security Operations and Analytics
Idéal pour unifier les outils de sécurité
Autres tests de logiciels similaires
Si vous n'avez pas encore trouvé ce que vous cherchez ici, consultez ces outils alternatifs que nous avons également testés et évalués.
- Logiciel de supervision réseau
- Logiciel de surveillance de serveurs
- Solutions SD-Wan
- Outils de supervision d’infrastructures
- Analyseurs de paquets
- Logiciels de supervision applicative
Critères de sélection des outils SIEM
Pour sélectionner les meilleurs outils SIEM de cette liste, j’ai pris en compte les besoins communs des acheteurs et les points douloureux tels que la simplification de la détection des menaces et l’amélioration du reporting conformité. J’ai également utilisé le cadre suivant pour assurer une évaluation structurée et équitable :
Fonctionnalités de base (25 % de la note globale)
Pour intégrer cette sélection, chaque solution devait couvrir ces cas d’usage courants :
- Détection des menaces en temps réel
- Gestion et analyse des journaux
- Logiciel de réponse aux incidents
- Rapports de conformité
- Alerte et notification
Fonctionnalités supplémentaires remarquables (25 % du score total)
Pour affiner davantage la sélection, j'ai également recherché des fonctionnalités uniques, telles que :
- Analyses comportementales avancées
- Intégration de renseignements sur les menaces
- Actions de réponse automatisées
- Analyses du comportement des utilisateurs et des entités (UEBA)
- Outils de sécurité cloud
Ergonomie (10 % du score total)
Pour évaluer la convivialité de chaque système, j'ai pris en compte les éléments suivants :
- Tableaux de bord conviviaux
- Interface facile à naviguer
- Génération de rapports simplifiée
- Visualisations claires des événements de sécurité
- Formation minimale requise
Intégration des utilisateurs (Onboarding) (10 % du score total)
Pour évaluer l'expérience d'intégration pour chaque plateforme, j'ai pris en compte les éléments suivants :
- Matériel de formation complet
- Guides d'installation étape par étape
- Disponibilité de webinaires d'intégration
- Tutoriels et démonstrations interactives
- Facilité de migration à partir de solutions précédentes
Support client (10 % du score total)
Pour évaluer les services de support client de chaque éditeur de logiciel, j'ai pris en compte les éléments suivants :
- Temps de réponse rapides
- Multiples canaux de support (email, chat, téléphone)
- Disponibilité d'une assistance 24h/24 et 7j/7
- Représentants dédiés d'assistance
- Documentation et base de connaissances utiles
Rapport qualité/prix (10 % du score total)
Pour évaluer le rapport qualité/prix de chaque plateforme, j'ai pris en compte les éléments suivants :
- Tarification compétitive
- Structures tarifaires claires
- Modèles de licences flexibles
- Disponibilité d'une tarification évolutive
- Coûts transparents sans frais cachés
Avis clients (10 % du score total)
Pour évaluer la satisfaction générale des clients, j'ai pris en compte les points suivants lors de la lecture des avis :
- Recommandations globales des utilisateurs actuels
- Avis positifs sur la précision de détection
- Satisfaction des utilisateurs sur la facilité d'utilisation
- Fiabilité et stabilité de l'outil
- Expériences avec le support client
Comment choisir un outil SIEM
Il est facile de se perdre dans des listes de fonctionnalités interminables et des structures tarifaires complexes. Pour vous aider à rester concentré pendant votre processus de sélection logicielle, voici une liste de critères à garder à l’esprit :
| Critère | Ce qu’il faut considérer |
|---|---|
| Évolutivité | Vérifiez si l’outil peut gérer des volumes de données croissants et l’ajout de nouveaux appareils sans difficulté, à mesure que votre organisation grandit. Privilégiez les déploiements cloud ou hybrides pour une meilleure évolutivité. |
| Intégrations | Assurez-vous que le SIEM s’intègre à vos systèmes existants, y compris aux points de terminaison, pare-feu et services cloud, pour un suivi unifié et une détection plus rapide des incidents. |
| Personnalisation | Vérifiez si le logiciel vous permet d’adapter les alertes, tableaux de bord et rapports selon vos exigences de sécurité, afin de réduire les faux positifs et d’améliorer l’efficacité. |
| Facilité d'utilisation | Choisissez un outil offrant une interface intuitive, des tableaux de bord clairs et des workflows simples pour que votre équipe puisse réagir rapidement aux incidents de sécurité, sans formation intensive. |
| Budget | Examinez attentivement les modèles de tarification—par événement, par appareil, ou forfaitaire—et choisissez celui qui correspond le mieux à votre budget et à la croissance anticipée de vos données. |
| Mesures de sécurité | Assurez-vous que l’outil dispose de mesures robustes, notamment le chiffrement des données, la gestion des accès selon les rôles et la conformité aux normes réglementaires telles que le RGPD ou l’HIPAA. |
| Renseignement sur les menaces | Optez pour un outil disposant de renseignements intégrés sur les menaces ou d’options d’intégration, pour détecter et répondre plus rapidement aux menaces émergentes. |
| Qualité du support | Vérifiez la disponibilité d’un service client fiable, idéalement 24h/24 et 7j/7, afin d’aider votre équipe à résoudre rapidement tout incident ou problème. |
Qu'est-ce qu'un outil SIEM ?
Un outil SIEM est une plateforme logicielle qui collecte, analyse et corrèle les données de sécurité provenant de l’ensemble de votre écosystème informatique afin d’identifier les menaces potentielles et les risques de conformité.
En agrégeant les journaux et les événements des serveurs, applications, pare-feux et terminaux, les outils SIEM offrent une vue centralisée de l’activité de sécurité. Ils permettent la surveillance en temps réel, la détection des incidents et l’automatisation des réponses—aidant ainsi les équipes à renforcer les capacités de détection des menaces tout en simplifiant la génération de rapports réglementaires et la préparation aux audits.
Des fonctionnalités comme le logiciel de gestion des journaux, la surveillance en temps réel et les rapports de conformité aident les organisations à sécuriser leur infrastructure informatique et à atténuer les cyberattaques.
Fonctionnalités des outils SIEM
Lors du choix d’un outil SIEM, vérifiez la présence de ces fonctionnalités clés :
- Gestion des journaux : Collecte, stocke et organise les données des journaux provenant de divers appareils et applications, afin que vous puissiez facilement repérer des schémas, détecter des problèmes et rester en conformité avec la réglementation.
- Surveillance en temps réel : Surveille continuellement l’activité réseau et les événements du système pour vous aider à détecter immédiatement tout accès non autorisé ou menace potentielle.
- Détection des menaces : Utilise des règles de corrélation et des analyses pour signaler automatiquement tout comportement suspect ou anomalie, vous permettant de garder une longueur d’avance sur les cyberattaquants.
- Réponse aux incidents : Rationalise l’investigation des alertes, l’attribution des tâches et la documentation de vos actions afin d’assurer une réaction rapide et efficace en cas d’incident de sécurité.
- Alerte et notification : Vous informe instantanément lorsque des activités à haut risque ou des violations de politiques surviennent, pour que vous ne soyez jamais pris au dépourvu face à un problème urgent.
- Rapports de conformité : Génère des rapports prêts à l’emploi et personnalisables pour démontrer que votre organisation respecte les normes sectorielles et les exigences réglementaires.
- Visualisation des données : Transforme les données techniques en graphiques et tableaux de bord clairs, permettant à votre équipe d’identifier les schémas et tendances sans être submergée par les détails.
- Capacités d’intégration : S’intègre facilement à d’autres solutions de sécurité et à l’infrastructure informatique, afin de bâtir un écosystème de sécurité adapté aux besoins spécifiques de votre organisation.
- Analyse du comportement des utilisateurs et des entités : Suit les actions des utilisateurs et le comportement des appareils pour révéler des activités inhabituelles, vous aidant à détecter des menaces internes ou des comptes compromis.
- Analyse médico-légale : Vous permet de remonter dans le temps en examinant les données historiques, afin d’approfondir l’analyse d’événements de sécurité passés et d’améliorer vos défenses futures.
Fonctionnalités courantes de l’IA dans les outils SIEM
Au-delà des fonctionnalités SIEM standards mentionnées ci-dessus, nombre de ces solutions intègrent désormais l’intelligence artificielle avec des fonctionnalités telles que :
- Renseignement automatisé sur les menaces : Utilise l’IA pour collecter, traiter et intégrer des données externes sur les menaces, vous fournissant ainsi un contexte en temps réel sur l’évolution des cybermenaces.
- Détection d’anomalies : Apprend les schémas d’activité habituels de votre organisation grâce à l’IA, puis signale tout écart susceptible d’indiquer une attaque furtive ou une nouvelle vulnérabilité.
- Analyses prédictives : Utilise des modèles d’IA pour anticiper les risques de sécurité sur la base des tendances observées dans votre réseau, de sorte que vous puissiez vous préparer proactivement avant toute attaque.
- Traitement automatisé des alertes : Emploie l’IA pour hiérarchiser, investiguer et même résoudre certains types d’alertes, vous aidant ainsi à mieux gérer la surcharge d’alertes et à vous concentrer sur les enjeux critiques.
- Traitement du langage naturel (NLP) : Permet à l’outil SIEM d’interpréter et de corréler les messages de journaux et données de sécurité, même issus de sources non structurées, grâce à des modèles linguistiques pilotés par IA.
Avantages des outils SIEM
L’implémentation d’outils SIEM procure plusieurs avantages à votre équipe et à votre entreprise. En voici quelques-uns dont vous pourrez bénéficier :
- Réponse plus rapide : Les alertes en temps réel permettent à votre équipe de traiter rapidement les incidents de sécurité avant qu’ils ne prennent de l’ampleur.
- Conformité facilitée : Les rapports intégrés simplifient le respect des exigences réglementaires telles que le RGPD ou la HIPAA.
- Meilleure visibilité : La gestion centralisée des journaux permet à votre équipe de sécurité d’avoir une vision claire de l’activité réseau.
- Risque de menace réduit : L’analyse du comportement des utilisateurs identifie rapidement les activités suspectes, réduisant ainsi le risque de compromission.
- Productivité améliorée : L’automatisation des tâches répétitives libère votre équipe sécurité pour qu’elle se concentre sur les enjeux majeurs.
- Prise de décision renforcée : Les tableaux de bord visuels offrent une vision claire des tendances en matière de sécurité, facilitant des décisions plus éclairées.
- Coûts de sécurité réduits : La détection et la réponse précoces diminuent l’impact financier des incidents de sécurité.
Coûts et tarification des outils SIEM
Choisir des outils SIEM nécessite de comprendre les différents modèles et formules tarifaires disponibles. Les coûts varient en fonction des fonctionnalités, de la taille de l’équipe, des modules complémentaires et plus encore. Le tableau ci-dessous résume les formules courantes, leurs prix moyens et les fonctionnalités généralement incluses dans les solutions d’outils SIEM :
Tableau comparatif des formules pour les outils SIEM
| Type de formule | Prix moyen | Fonctionnalités courantes |
|---|---|---|
| Formule gratuite | $0 | Collecte de logs basique, surveillance limitée et alertes simples. |
| Formule personnelle | $50-$100/utilisateur/mois | Détection de menaces en temps réel, rapports de conformité de base et notifications par e-mail. |
| Formule entreprise | $100-$500/utilisateur/mois | Analyses avancées, surveillance du comportement des utilisateurs, tableaux de bord personnalisables et rapports de conformité détaillés. |
| Formule grande entreprise | $500-$1500+/utilisateur/mois | Analyses pilotées par l’IA, automatisation des incidents, renseignement avancé sur les menaces, support dédié et intégrations complètes. |
FAQ sur les outils SIEM
Voici des réponses aux questions courantes concernant les outils SIEM :
Quelles sont les trois fonctions principales d’un outil SIEM ?
Comment les outils SIEM détectent-ils les menaces ?
Que faut-il rechercher lors de l’évaluation des intégrations SIEM avec les solutions existantes ?
Comment un système SIEM peut-il aider à réduire la fatigue liée aux alertes dans mon équipe sécurité ?
Quelles erreurs faut-il éviter lors du déploiement d’un SIEM ?
Comment mesurer le ROI d’un outil SIEM ?
Les plateformes SIEM peuvent-elles faciliter les audits de conformité et les rapports associés ?
Réflexions finales
Les cyberattaques contre les réseaux d’entreprise ont augmenté de 38 % en 2022 par rapport à 2021, et cette tendance devrait se poursuivre à mesure que les cybercriminels exploitent les failles pour leur profit. Les outils SIEM sont des solutions puissantes capables de détecter, voire d’arrêter, toute menace potentielle dès son apparition. Si votre entreprise n’a pas encore adopté de solution SIEM, servez-vous de cette liste pour lancer vos recherches.
Abonnez-vous à la newsletter The CTO Club pour plus d’analyses.