Best Web Application Firewall Software Shortlist
In the ever-evolving landscape of cybersecurity, dealing with challenges like false positives, zero-day threats, and application-layer attacks is common. Web Application Firewall Software (WAF) is a critical tool for both on-premise and cloud-based security, offering robust protection for web apps and API security. WAF protects against data breaches and hackers by controlling IP addresses, profiling user behavior, applying rulesets, and employing virtual patching. It's more than just a security measure; it's an advanced system offering application protection and customization to combat malicious traffic, file inclusion, and threats to virtual machines.
The best WAF not only offers vital deployment options but also minimizes downtime, ensuring uninterrupted service. It helps in solving major pain points such as vulnerabilities and unauthorized access, providing advanced WAF features and API protection. Auditing, virtual patching, and robust responsiveness to emerging threats are key aspects of WAF that contribute to a secure digital environment. Whether you're new to cybersecurity or looking to enhance your existing measures, understanding the multifaceted role of WAF will guide you in making an informed decision to safeguard your online presence.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Web Application Firewall Software Summary
This comparison chart summarizes pricing details for my top web application firewall software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for AI-driven threat analytics | 30-day free trial + free demo available | Pricing upon request | Website | |
| 2 | Best for customizable traffic control | 14-day free trial + free demo available | From $7/user/month (billed annually) | Website | |
| 3 | Best for blocking real-time attacks | Free plan available + free demo | From $350/month | Website | |
| 4 | Best for high-speed performance and caching | 30-day free trial + free plan available | Pay-as-you-go model | Website | |
| 5 | Best for compliance management | Not available | Pricing upon request | Website | |
| 6 | Best for advanced threat protection | No | From $20/user/month (min 5 seats) | Website | |
| 7 | Best for malware removal and cleanup | No | From $9.99/user/month (billed annually) | Website | |
| 8 | Best for Azure native applications | No | From $10/user/month (billed annually) | Website | |
| 9 | Best for Amazon Web Services integration | No | From $5/user/month + $1 per million web requests | Website | |
| 10 | Best for scalable DDoS defense | No | From $15/user/month (billed annually) | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Web Application Firewall Software Review
Below are my detailed summaries of the best web application firewall software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Radware provides a full suite of web application and API protection tools designed to safeguard digital environments against automated and evolving threats. Its Cloud WAF and Bot Manager work together to defend against OWASP Top 10 vulnerabilities, API abuse, and malicious bot traffic. As a web application firewall solution, Radware emphasizes adaptive detection and mitigation that scale with complex online environments.
Why I Picked Radware: I picked Radware because it combines comprehensive cloud-based WAF protection with advanced bot and API security, powered by real-time behavioral analysis. If you need to protect your applications from both human and automated threats, Radware can help you identify malicious intent using AI-driven analytics. I also like that it provides application-layer DDoS defense and supports flexible deployment across cloud, on-premises, and hybrid environments.
Radware standout features and integrations:
Features include AI-based bot management, application-layer DDoS protection, and API security with real-time behavioral analysis.
Integrations include Akamai API, ESI Caching, and Manual Blacklisting options for custom traffic control.
Pros and Cons
Pros:
- Scalable hybrid deployment options
- Strong API and bot protection
- AI-based behavioral threat detection
Cons:
- Some integrations require manual setup
- Pricing available upon request
NordLayer is a network security platform tailored for businesses, aimed at enhancing cybersecurity for remote workforces. It offers secure VPN services, access management, and network protection to safeguard sensitive data while maintaining employee connectivity.
Why I Picked NordLayer: One of the standout features of NordLayer's cloud firewall is its ability to define default actions for network traffic. You can set the firewall to either 'Allow' or 'Deny' all traffic by default, and then customize rules to permit or block certain connections. Additionally, NordLayer's cloud firewall supports detailed rule creation based on traffic source, destination, and services. For instance, you can specify which team members or groups have access to particular IP addresses or subnets and define which services or ports they can use.
Standout Features & Integrations:
Features include the ability to manage firewall rules through a user-friendly control panel, allowing for quick adjustments as your security needs evolve. NordLayer also offers two-factor authentication, single sign-on integration, device posture security, dedicated IP addresses, site-to-site connections, smart remote access, and threat intelligence. Some integrations include Entra ID, Okta, OneLogin, JumpCloud, Google Workspace, Google Cloud, IBM Cloud, and AWS.
Pros and Cons
Pros:
- Utilizes a zero-trust framework
- Security measures like AES-256 encryption and multi-factor authentication
- NordLayer supports multiple operating systems
Cons:
- Number of available server locations could be expanded
- Server setup can be complex
New Product Updates from NordLayer
NordLayer Enhances Security with Download Protection
NordLayer introduces a Download Protection feature that safeguards files from threats by scanning and blocking malicious downloads in real time. For more information, visit NordLayer's official site.
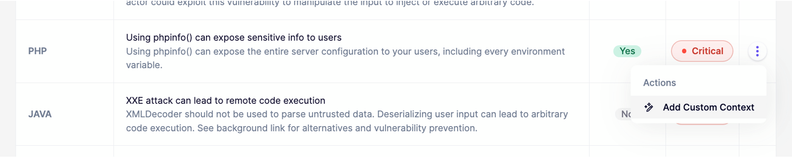
Aikido Security is a DevSecOps platform that provides comprehensive security coverage from code to cloud. It offers a variety of security scans and features to protect applications at runtime, including vulnerability management, Software Bill of Materials (SBOM) generation, and protection against threats like malware, outdated software, and license risks.
Why I Picked Aikido Security: Aikido Security stands out as web application firewall software with its robust feature set tailored for modern web applications, particularly those built on Node.js. It offers the ability to autonomously protect applications against common and critical attacks such as SQL injection, NoSQL injection, command injection, and path traversal. This is achieved through an embedded JavaScript library that operates directly within the application, ensuring high accuracy and minimal false positives or negatives.
Standout Features & Integrations:
Features include cloud posture management, which detects cloud infrastructure risks. The platform also excels in open source dependency scanning, continuously monitoring code for known vulnerabilities and generating SBOMs for better dependency management. Integrations include Amazon Web Services (AWS), Google Cloud, Microsoft Azure Cloud, Drata, Vanta, AWS Elastic Container Registry, Docker Hub, Jira, Asana, and GitHub.
Pros and Cons
Pros:
- User-friendly interface
- Helps in compliance tracking and reporting
- Provides actionable insights and recommendations
Cons:
- Setup may be complex for some users
- Can be expensive for some users
New Product Updates from Aikido Security
Aikido Security Enhances AI Pentest and AutoTriage Accuracy
Aikido Security introduces AI Pentest vulnerability escalation and custom context for AutoTriage to enhance exploitability assessment and reduce false positives. For more information, visit Aikido Security's official site.
Fastly is a real-time caching content delivery network (CDN) designed to provide high-speed performance and caching solutions for web applications. It uses globally distributed networks and edge computing to ensure low-latency responses, making it best for high-speed performance and caching.
Why I Picked Fastly: I chose Fastly after carefully comparing various CDN solutions, selecting it for its distinctive high-speed delivery and caching abilities. What makes it stand out is its robust infrastructure that leverages strategically positioned servers to minimize latency. I determined it's best for high-speed performance and caching due to its real-time cache controls and unique instant purging feature.
Standout Features & Integrations:
Fastly's standout features include instant purging, real-time analytics, and flexible edge scripting that enable custom logic at the network's edge. These functionalities are not only useful but are core to its high-speed performance. The integrations with popular web platforms, such as WordPress and Drupal, allow for streamlined content delivery and caching management.
Pros and Cons
Pros:
- Integrates easily with many web platforms
- Optimized for low-latency performance
- Provides real-time caching controls
Cons:
- Base fee might be a barrier for entry-level users
- Custom scripting might require a learning curve
- Starting price may be higher for some small businesses
Imperva WAF is a cloud-based web application firewall designed to protect websites and applications from security breaches while also aiding in meeting regulatory compliance requirements. Its strong focus on ensuring compliance with various standards like GDPR, HIPAA, and PCI DSS makes Imperva WAF the best for compliance management.
Why I Picked Imperva WAF: I chose Imperva WAF for this list after carefully judging its unique approach to compliance management. Among the numerous tools I compared, Imperva stood out due to its commitment to not only providing robust security but also simplifying compliance reporting and adherence to legal regulations. I determined that it's the best for compliance management, given its vast library of predefined compliance templates and guided setup.
Standout Features & Integrations:
Imperva WAF offers features like data masking, threat analytics, and automated compliance reporting that are essential for modern regulatory needs. Integrations with leading SIEM systems, DLP solutions, and authentication providers further enhance its capabilities in managing and maintaining compliance across different platforms.
Pros and Cons
Pros:
- Comprehensive reporting capabilities for various standards
- Integrates well with existing compliance and security tools
- Specialized focus on compliance management
Cons:
- Some users might find the interface complex or overwhelming
- Cost could be prohibitive for smaller organizations
- Might be too focused on compliance for some users' needs
Fortinet FortiWeb is renowned for providing top-tier protection against sophisticated web threats. This advanced layer of security aligns perfectly with its positioning as the best tool for advanced threat protection, especially for organizations requiring intense security measures.
Why I Picked Fortinet FortiWeb: I chose Fortinet FortiWeb for its commitment to tackling complex and evolving threats. After careful comparison and judging its performance against other options, it's clear that Fortinet stands apart in offering advanced threat protection. The decision to label it as the best for this specific use case was backed by its well-designed architecture aimed at protecting against the most advanced and targeted attacks.
Standout Features & Integrations:
Fortinet FortiWeb offers behavior-based threat detection, providing an intelligent response to attacks. It also includes proactive bot defense and inbuilt fraud detection. Key integrations include compatibility with SIEM systems and connectors to various third-party reporting tools, enhancing its utility and collaborative security measures.
Pros and Cons
Pros:
- Useful integration with third-party tools
- Strong bot defense mechanism
- Behavior-based threat analysis
Cons:
- Higher starting price point
- Potential complexity in setup
- Minimum seat requirement
Sucuri WAF excels in providing security against malware, with a specific focus on efficient removal and cleanup. This tool brings together robust detection methods and precise remediation to make it the best for malware removal and cleanup, a crucial aspect of maintaining web application integrity.
Why I Picked Sucuri WAF: I chose Sucuri WAF after assessing its capacity to identify, remove, and clean malware effectively. In my judgment, its distinct emphasis on malware handling sets it apart from the rest. The ability to not just detect but also swiftly clean malware makes it best for those facing consistent malware threats or looking for thorough post-attack cleanup.
Standout Features & Integrations:
Sucuri WAF’s malware removal tool is paired with constant monitoring to detect and clean malware as quickly as possible. It integrates threat intelligence to refine detection methods continually. Important integrations include compatibility with popular content management systems (CMS) like WordPress and Joomla, making it easily implementable in various web environments.
Pros and Cons
Pros:
- Continuous monitoring for swift action
- Integration with popular CMS
- Comprehensive malware detection and cleanup
Cons:
- Specificity on malware may overlook other threat vectors
- May not suit businesses focused solely on preventive measures
- Annual billing only
Microsoft Azure Web Application Firewall (WAF) is designed to protect web applications from various online threats such as SQL injection, cross-site scripting, and other web vulnerabilities. Tailored specifically for Azure native applications, it ensures optimized protection and easy integration within the Azure environment. This specificity in design makes it the best choice for those running applications natively within Azure.
Why I Picked Microsoft Azure Web Application Firewall (WAF): I chose Microsoft Azure WAF because of its robust security features and native integration with the Azure platform. By comparing its capabilities with other tools, I determined that its strength lies in the integration with Azure, providing a tailored security solution. It stands out for its ability to protect applications within the Azure ecosystem, and I believe it's best for Azure native applications because of its specific focus on those deployments.
Standout Features & Integrations:
Microsoft Azure WAF offers comprehensive protection against common web vulnerabilities. Features such as custom rules, bot protection, and geo-filtering enable a wide range of security options. The most important integrations it provides include connection with other Azure services, such as Azure Active Directory and Azure Monitor, ensuring an integrated and efficient workflow within the Azure environment.
Pros and Cons
Pros:
- Integrates effortlessly with other Azure services
- Offers custom rules for specialized protection needs
- Designed specifically for Azure, ensuring optimized protection for native applications
Cons:
- May be considered expensive for smaller applications or businesses
- Custom configurations might require specialized knowledge
- Limited appeal to those not using the Azure platform
AWS WAF (Web Application Firewall) is a security service designed to protect web applications hosted on the Amazon Web Services (AWS) platform from common online threats. By integrating tightly with AWS services, it provides specific protections tailored to the unique infrastructure and service offerings within AWS. This strong integration with the AWS ecosystem makes it the best option for those relying on Amazon's cloud services.
Why I Picked AWS WAF: I chose AWS WAF for this list after carefully comparing its features and integrations specifically for the AWS platform. It's evident that its design is strongly focused on serving applications hosted within AWS, which makes it stand out from other web application firewalls. I judged it to be best for Amazon Web Services integration due to its dedicated alignment with AWS's unique architecture and service offerings.
Standout Features & Integrations:
AWS WAF's most important features include real-time visibility into attacks, customizable web security rules, and bot control. The tool is capable of responding quickly to changing threat landscapes. As for integrations, it links easily with other AWS services such as AWS CloudTrail, Amazon CloudWatch, and AWS Lambda, enabling streamlined security management within the AWS environment.
Pros and Cons
Pros:
- Customizable security rules provide flexibility for various use cases
- Real-time visibility into attacks, allowing for quick response
- Designed specifically for AWS, providing tailored protection for applications hosted there
Cons:
- Complexity in configuration may require specialized expertise
- Additional cost per web request can become significant with high traffic
- May not be suitable for non-AWS environments
Akamai Kona Site Defender is designed to offer robust protection against Distributed Denial of Service (DDoS) attacks. It stands out for its scalability, making it a suitable option for organizations that require a flexible defense mechanism and thus justifying its position as the best for scalable DDoS defense.
Why I Picked Akamai Kona Site Defender: I chose Akamai Kona Site Defender after evaluating its ability to handle DDoS attacks at varying scales. In the process of comparing it to other options, it became evident that its scalable architecture is unique and vital. This scalability makes it best for businesses that need to adapt to changing threat landscapes and can grow with the organization's needs.
Standout Features & Integrations:
Akamai Kona Site Defender offers a multi-layered approach to security, blending attack detection and mitigation. It also features adaptive rate controls to manage suspicious traffic efficiently. Among its integrations, Akamai connects well with cloud providers and existing security information and event management (SIEM) systems, facilitating a comprehensive defense strategy.
Pros and Cons
Pros:
- Cloud and SIEM integrations
- Multi-layered security approach
- Scalable DDoS protection
Cons:
- Not tailored for small-scale users
- May require technical expertise for full utilization
- Annual billing might be limiting
Other Web Application Firewall Software
Here are some additional web application firewall software options that didn’t make it onto my shortlist, but are still worth checking out:
- Cloudflare WAF
For integrated content delivery network
- Wallarm
For AI-driven security automation
- Signal Sciences WAF
For real-time data monitoring
- Reblaze WAF
For comprehensive bot mitigation
- Symantec Web Application Firewall and Reverse Proxy
For content inspection and protection
- Prophaze WAF
Good for Kubernetes environments and container security
- AppTrana Cloud WAAP (WAF)
Good for managed security and continuous risk assessment
- HAProxy
Good for load balancing and performance optimization
- Microsoft Application Gateway
Good for Azure integration and application delivery control
- NSFOCUS Web Application Firewall
Good for comprehensive threat analysis and customizable security
- Sophos XG Firewall with Web Application Firewall
Good for unified threat management and synchronized security
- Penta Security WAPPLES
Good for heuristic-based web attack detection
Web Application Firewall Software Selection Criteria
When selecting the best web application firewall software to include in this list, I considered common buyer needs and pain points like protection against DDoS attacks and ease of integration with existing systems. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Protect against SQL injection
- Defend against cross-site scripting
- Block DDoS attacks
- Monitor traffic in real-time
- Provide detailed security reports
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Machine learning for threat detection
- Automated incident response
- API security management
- Multi-cloud support
- Customizable security rules
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Clear documentation
- Customizable dashboards
- Responsive design for mobile access
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive onboarding guides
- 24/7 chat support
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of live chat
- 24/7 technical support
- Access to a dedicated account manager
- Comprehensive knowledge base
- Fast response times
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Free trial availability
- Discounts for long-term commitments
- Transparent pricing structure
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall rating consistency
- Feedback on ease of use
- Comments on customer support quality
- User satisfaction with core features
- Frequency of software updates and improvements
How to Choose Web Application Firewall Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your business? Consider future traffic loads and if the tool can handle increased demand without extra costs or performance hits. |
| Integrations | Does it work with your existing systems? Check compatibility with your current tech stack to avoid additional expenses or complex workarounds. |
| Customizability | Can you tailor the security rules to your needs? Look for tools that allow flexibility in setting up rules and policies specific to your business. |
| Ease of use | Is the interface user-friendly? Ensure your team can navigate the software without extensive training or reliance on technical support. |
| Implementation and onboarding | How quickly can you get started? Evaluate the setup process, available resources like tutorials or support, and the time it takes to go live. |
| Cost | Does the price fit your budget? Compare subscription models, hidden fees, and any additional costs for scaling or extra features. |
| Security safeguards | What protections are in place? Ensure the tool offers robust defenses against common threats like SQL injection and DDoS attacks. |
| Compliance requirements | Does it meet industry standards? Verify the software complies with regulations relevant to your industry, such as GDPR or PCI-DSS. |
What Is Web Application Firewall Software?
Web application firewall software is a specialized barrier designed to secure web applications by monitoring and filtering HTTP traffic between a web application and the Internet. It serves as a shield against common web-based threats such as cross-site scripting (XSS), SQL injection, and other OWASP (Open Web Application Security Project) threats.
Typically used by businesses, e-commerce sites, and any organization with an online presence, web application firewall software inspects incoming traffic and uses established rules to identify and block anything malicious.
Features
When selecting web application firewall software, keep an eye out for the following key features:
- Real-time traffic analysis: Monitors incoming and outgoing traffic instantly to detect and respond to potential threats.
- Threat detection: Identifies and flags malicious activities to prevent breaches and data loss.
- Customizable security rules: Allows users to set specific rules tailored to their unique security needs and business requirements.
- DDoS protection: Provides safeguards against distributed denial-of-service attacks to maintain application availability.
- API security management: Secures API endpoints to prevent unauthorized access and data breaches.
- Integration capabilities: Works seamlessly with existing systems and applications to enhance security without complicating workflows.
- Compliance support: Ensures adherence to industry regulations such as GDPR and PCI-DSS, reducing the risk of penalties.
- Automated incident response: Quickly reacts to threats, minimizing damage and ensuring continuity.
- User-friendly interface: Offers an intuitive design that makes it easy for teams to manage and configure security settings.
- Scalability: Adapts to growing business needs, handling increased traffic and new applications without degradation in performance.
Benefits
Implementing web application firewall software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Protects your applications from threats like SQL injection and cross-site scripting, ensuring data integrity and confidentiality.
- Regulatory compliance: Helps meet industry standards such as GDPR and PCI-DSS, reducing the risk of fines and legal issues.
- Improved application performance: Mitigates DDoS attacks to keep your applications running smoothly and consistently.
- Customization flexibility: Allows you to tailor security settings to fit your specific business needs, enhancing overall security posture.
- Quick threat response: Automates responses to potential threats, minimizing the impact of security incidents.
- User-friendly management: Simplifies the setup and monitoring of security protocols, making it accessible for teams without deep technical expertise.
- Scalability: Grows with your business, handling increased traffic and new applications without compromising security or performance.
Costs & Pricing
Selecting web application firewall software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in web application firewall software solutions:
Plan Comparison Table for Web Application Firewall Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited traffic analysis, and community support. |
| Personal Plan | $10-$30/month | Enhanced security rules, basic DDoS protection, and email support. |
| Business Plan | $50-$150/month | Advanced threat detection, API security, and 24/7 customer support. |
| Enterprise Plan | $200-$500/month | Full customization, compliance support, dedicated account manager, and SLA guarantees. |
Web Application Firewall Software FAQs
Here are some answers to common questions about web application firewall software:
How do I know if my business needs a web application firewall?
If your business relies on web applications or handles sensitive data online, a web application firewall is essential. A WAF protects against common web-based threats and helps maintain customer trust by safeguarding their information. Even small businesses can benefit, as cyber threats don’t discriminate by size. Evaluate your web presence and data sensitivity to determine the necessity of a WAF.
What is the difference between a web application firewall and a traditional firewall?
A web application firewall (WAF) specifically protects web applications by filtering and monitoring HTTP traffic, whereas a traditional firewall acts as a barrier between a trusted network and untrusted networks. WAFs focus on application-level attacks, such as SQL injection and cross-site scripting, while traditional firewalls manage network-level threats. For businesses with web applications, a WAF provides specialized protection that a traditional firewall can’t offer.
How do I know which deployment model fits my setup?
Check if your apps run on-prem, in the cloud, or both. Cloud WAFs are easier to deploy but offer less control. On-prem options need more management but give you full visibility and customization.
What metrics should I track after deployment?
Monitor blocked threats, false positives, and page load times. Watch for latency issues or user complaints that may show over-filtering. Compare before-and-after attack data to gauge value.
What’s Next:
If you're in the process of researching web application firewall software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.