Best Application Security Software Shortlist
In today's digital landscape, securing your applications is more important than ever. You face countless threats that can compromise your data and disrupt your operations. That's where application security software comes in. It helps protect your systems from vulnerabilities and keeps your data safe.
I've spent time testing and reviewing these tools, aiming to give you an unbiased look at the best options available. In this article, I'll share my top picks, focusing on what makes each one stand out. You'll find insights into features, user experiences, and how they can fit into your team's workflow.
Let's dive in and find the right solution for your needs.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Application Security Software Summary
This comparison chart summarizes pricing details for my top application security software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for automated threat mitigation | 30-day free trial + free demo available | Pricing upon request | Website | |
| 2 | Best for catching context-aware vulnerabilities | Free plan available | From $200/month | Website | |
| 3 | Best for web code integrity | Free trial available | Pricing upon request | Website | |
| 4 | Best for locking application execution environments | Not available | Pricing upon request | Website | |
| 5 | Best for integrated DevSecOps | Not available | Pricing upon request | Website | |
| 6 | Best for comprehensive mobile security | Not available | From $12/user/month (billed annually) | Website | |
| 7 | Best for JavaScript-focused protection | Not available | From $10/user/month (billed annually) | Website | |
| 8 | Best for .NET code protection | Not available | Pricing upon request | Website | |
| 9 | Best for Android and Java app fortification | Not available | Pricing upon request | Website | |
| 10 | Best for real-time app security monitoring | Not available | Pricing upon request | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Application Security Software Review
Below are my detailed summaries of the best application security software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Radware lands on this shortlist because of how well it intercepts and manages automated threats that target enterprise applications. When I'm working with IT teams facing bot attacks, credential stuffing, or scraping, Radware's behavioral analysis and real-time API protection hold up in production. What I appreciate most is its dedicated machine learning engine for detecting evolving threats before they impact your environment.
Radware’s Best For
- Enterprises facing high volumes of automated threats and bots
- Security teams needing real-time behavioral threat detection
Radware’s Not Great For
- Small organizations with basic bot mitigation needs
- Teams focused on manual vulnerability scanning and audits
What sets Radware apart
Radware stands out by focusing heavily on automated threat mitigation through behavioral analytics and machine learning. It expects you to treat bot detection as a continuous, adaptive process rather than something you configure and leave alone. Compared to something like Imperva, which often covers broader application security, Radware zeroes in on evolving automated threats and changing traffic patterns.
This tends to work well if your environment faces many bot-driven risks and you want fine-tuned control over mitigation strategies.
Tradeoffs with Radware
Radware optimizes for automated threat defense, but you give up breadth in coverage for manual assessment or broader application security. You might need other tools if you want unified dashboards across vulnerability scanning and WAF management.
Pros and Cons
Pros:
- Comprehensive web and mobile coverage
- Strong defense against account takeover
- Real-time automated threat detection
Cons:
- Limited third-party integrations available
- Interface could be more intuitive
Zeropath lands on my list for its sharp focus on context-aware vulnerability detection. I see teams benefit from how it analyses code in production-like environments, catching risks that static scanning tends to miss. What I really appreciate is Zeropath's ability to surface issues linked to actual application logic and workflows, not just surface-level code flaws.
If you need application security that goes beyond generic signature-based tests, Zeropath delivers.
Zeropath’s Best For
- Dev and security teams tackling context-driven vulnerabilities
- Organizations simulating real-world conditions for code analysis
Zeropath’s Not Great For
- Projects needing only basic or signature-based scanning
- Teams with limited technical resources for dynamic testing
What sets Zeropath apart
Zeropath approaches application security by focusing on runtime context and how code behaves during real execution, not just static analysis. Unlike tools like SonarQube, which scan for code quality issues, Zeropath emphasizes vulnerabilities that can actually be exploited in production—such as insecure data flows, exposed endpoints, or authorization gaps. I see its value when you want detection that maps to business logic and real data movement, instead of flagging low-impact issues that never surface in runtime.
Tradeoffs with Zeropath
Zeropath optimizes for dynamic, context-driven analysis, but you lose the ease and speed of lightweight, static scans. This means investing more resources to simulate real application environments before you can act on the results.
Pros and Cons
Pros:
- It catches logic flaws and hidden risks you might miss in normal scans.
- Cuts down noisy findings so your team can focus on real issues.
- Gives you clear fixes that speed up your security reviews.
Cons:
- You may need time to adjust your workflow around its automation.
- Integration options may not be extensive enough for complex enterprise environments.
Jscrambler is on my shortlist because it addresses real risks around web app code exposure and tampering. I picked it for this list after seeing how well it protects JavaScript source code through obfuscation and real-time monitoring. What tends to stand out is its ability to detect packaging or runtime changes, block debugger tools, and alert you if there’s a tampering attempt.
I especially like how Jscrambler lets you enforce code integrity checks, so you can catch and act on malicious modifications before they impact customers.
Jscrambler’s Best For
- Security teams protecting front-end code from tampering
- Organizations that require code integrity and obfuscation
Jscrambler’s Not Great For
- Back-end application security and vulnerability scanning
- Teams with no JavaScript or client-side web assets
What sets Jscrambler apart
Jscrambler is designed around the idea that protecting code at the client side is just as important as traditional network or server-layer security. Instead of treating JavaScript as something you can’t lock down, it expects you to actively defend your source code and real-time app experience from tampering or reverse engineering. Compared to security suites like Snyk or Veracode, Jscrambler targets web code integrity at the browser level—not just static vulnerabilities.
This works best when you have sensitive business logic or intellectual property inside your front-end assets.
Tradeoffs with Jscrambler
Jscrambler optimizes for browser-side code protection, but it doesn’t address core app vulnerabilities or back-end risks. You need other tools for end-to-end coverage.
Pros and Cons
Pros:
- Integrates smoothly with popular development tools and platforms
- Real-time monitoring offers insights into potential threats
- Specialized techniques for robust code protection
Cons:
- Depending on configuration, there might be minor impacts on code performance
- Premium features can be pricey
- Might come off as complex for beginners
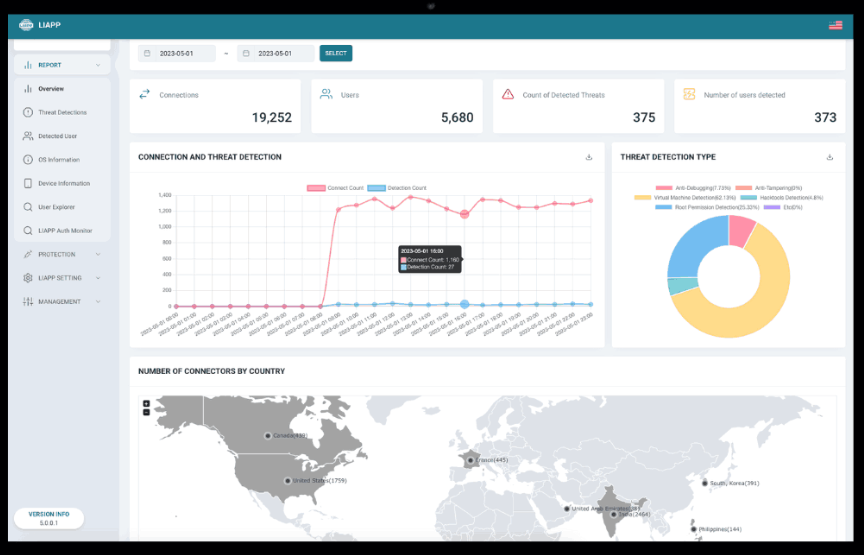
LIAPP makes my list because it gives you fine-grained control to lock down application execution environments—something most app security platforms barely touch. I picked it after seeing how quickly you can restrict code execution to known, trusted devices or containers.
I especially appreciate that it covers both static binary protection and runtime checks, which helps prevent issues like repackaged apps, injected code at runtime, or apps running outside approved environments.
LIAPP’s Best For
- Mobile app developers needing to lock execution environments
- Security teams preventing unauthorized distribution or code tampering
LIAPP’s Not Great For
- Organizations seeking source code-level application security
- Teams focused on desktop or web app protection
What sets LIAPP apart
LIAPP stands out by focusing entirely on controlling where and how your app runs, rather than just protecting code from reverse engineering like AppSealing or DexGuard. It expects you to take a lockdown-first approach, locking execution to known, managed environments. In practice, this works well for regulated industries that can’t risk apps running on untrusted devices or want tight container-level control.
Tradeoffs with LIAPP
LIAPP optimizes for strict runtime control, but you lose out on broader security tooling like source code obfuscation or web app coverage. This means anyone looking for a single tool for all app types or broad application hardening will need another solution.
Pros and Cons
Pros:
- Compatible with various mobile management platforms
- Efficient tamper-detection mechanisms
- Strong environment validation system
Cons:
- Limited to mobile application protection, not for desktop or web apps
- Might require a learning curve for those unfamiliar with application execution controls
- More geared toward large-scale deployments than individual use
Digital.ai Application Protection lands on my list because it addresses the challenge of embedding security directly into your DevSecOps processes. This isn’t just about runtime protection—I’ve seen teams use its obfuscation and anti-tampering to secure both mobile and server-side code right from the CI/CD pipeline.
What I like is how you can automate threat response and threat analytics within your delivery workflow, without siloing security away from development. I’d suggest this to teams consolidating security and release management so application security isn’t an afterthought.
Digital.ai Application Protection’s Best For
- DevSecOps teams automating security in CI/CD pipelines
- Organizations needing advanced code obfuscation and anti-tampering
Digital.ai Application Protection’s Not Great For
- Small teams needing basic application security only
- Organizations focused solely on web app firewall protection
What sets Digital.ai Application Protection apart
Digital.ai Application Protection takes a direct approach by embedding security measures and protections into your build and release process. Unlike application firewalls or scanners that bolt on after the fact, it expects you to treat security as integral to the software lifecycle. I find this works best in organizations looking to automate obfuscation and runtime protection side by side with DevOps practices.
Tradeoffs with Digital.ai Application Protection
Optimizing for early, automated protection means you get less value if you only want reactive security. Teams focused on manual, ad-hoc responses may find it too process-centric.
Pros and Cons
Pros:
- Easy integrations with CI/CD tools and cloud platforms
- Detailed vulnerability assessments
- Comprehensive real-time threat analysis
Cons:
- The documentation could benefit from more detailed use-case scenarios
- Advanced features might be overkill for smaller applications
- Might have a steeper learning curve for newcomers
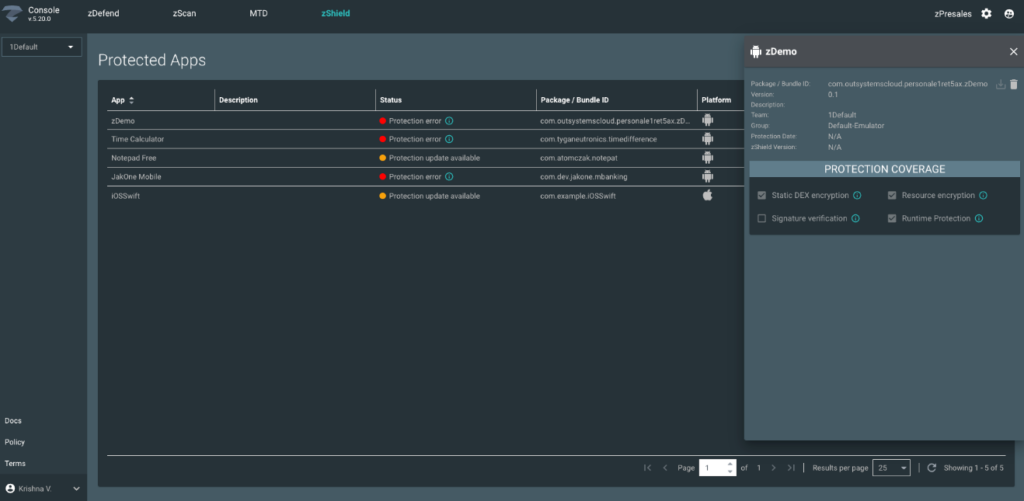
Best for comprehensive mobile security
Zimperium Mobile Application Protection Suite makes my list for how thoroughly it secures mobile apps against advanced threats. I see teams use it when compliance or brand risk is a concern and standard app scanning isn’t enough.
I appreciate its runtime application self-protection and machine learning-based threat detection that flag real-world attack attempts while apps are in use. You get ongoing monitoring across devices, not just at build or deployment.
Zimperium MAPS's Best For
- Security teams protecting apps against mobile-specific threats
- Organizations with strict compliance or mobile threat detection needs
Zimperium MAPS's Not Great For
- Developers needing basic, one-off code vulnerability scans
- Teams focused mainly on non-mobile (web or desktop) apps
What sets Zimperium MAPS apart
Zimperium MAPS is built around the idea that protecting apps doesn’t stop at scanning the code before release. Unlike Checkmarx or even Black Duck, it focuses on active monitoring and in-app defenses once your software is on real user devices. This approach works best when you want to know what’s hitting your production mobile app over time, not just at the pipeline’s gate.
Tradeoffs with Zimperium MAPS
MAPS optimizes for ongoing runtime protection, which means you won’t get the same static code depth or control as you’d see in classic SAST tools.
Pros and Cons
Pros:
- Rich insights into mobile application vulnerabilities
- Integrates with major app development platforms
- Comprehensive mobile threat detection and response
Cons:
- Requires understanding of mobile security to maximize benefits
- Some advanced features come at a premium cost
- May be perceived as a bit overwhelming for small app developers
JSDefender is explicitly designed to fortify JavaScript applications against potential threats. Recognizing JavaScript's ubiquitous presence and significance in web development, this tool offers a niche protection mechanism tailored for JavaScript environments.
Why I Picked JSDefender App Protection for JavaScript:
JSDefender is specialized in JavaScript, making it a great choice for organizations heavily reliant on it. It's ideally suited for JavaScript-focused protection due to the unique challenges posed by JavaScript vulnerabilities.
Standout Features & Integrations:
The tool brings advanced code obfuscation techniques that hinder reverse-engineering attempts. Furthermore, its runtime protection capabilities monitor the application's behavior, ensuring it doesn't deviate due to external manipulations. Its integrations, significant among them integrations with major JavaScript frameworks and popular build tools, cement its position in the JavaScript development lifecycle.
Pros and Cons
Pros:
- Integrates well with popular JavaScript frameworks
- Advanced obfuscation techniques deter code tampering
- Tailored protection mechanisms for JavaScript environments
Cons:
- Some obfuscation settings might cause compatibility issues with certain JavaScript libraries
- Initial configuration can be intricate
- Might be over-specialized for some broader application needs
Dotfuscator earns its place on my list for how thoroughly it protects .NET applications with code obfuscation and anti-tamper controls. I like using this tool in scenarios where teams need serious code confidentiality, especially when deploying desktop or mobile apps that could be reverse engineered.
What sets Dotfuscator apart is its trusted .NET-specific protection and its runtime checks that help guard against debugging and tampering attempts. I appreciate how you can apply strong encryption and injection protections without breaking app functionality or continuous delivery pipelines.
Dotfuscator’s Best For
- .NET developers deploying commercial apps with IP concerns
- Teams prioritizing runtime protection against tampering and reverse engineering
Dotfuscator’s Not Great For
- Projects outside the .NET ecosystem
- Developers needing basic code obfuscation without advanced anti-tamper features
What sets Dotfuscator apart
Dotfuscator is designed squarely for the .NET world and expects developers to treat code protection as an integral, repeatable step before release. Unlike multi-language security suites that patch in .NET support, I find Dotfuscator prefers you work within its specific obfuscation and anti-tamper workflow. In practice, this works well when your process relies on Visual Studio and continuous deployment and you want code security handled automatically as part of build routines.
Tradeoffs with Dotfuscator
Because it’s optimized for .NET protection, you lose flexibility with non-.NET code and must use other tools for mixed-language projects.
Pros and Cons
Pros:
- Tamper detection ensures post-deployment safety
- Integrates with leading CI/CD tools
- Comprehensive .NET protection including Xamarin apps
Cons:
- The focus is primarily on .NET, limiting its versatility for multi-platform projects
- The initial setup could be complex for some users
- Might be overkill for smaller .NET projects
DashO App Protection for Android & Java makes the cut because it covers the security gaps I see in Android and Java apps, especially when compliance or IP protection is in play. I like its mix of advanced obfuscation, runtime checks, and anti-tamper—most tools don't go nearly as deep with bytecode-level defenses.
I've worked with teams who have to harden their mobile apps for the enterprise, and this is where DashO’s focus on real, adaptive protection makes a difference. You can set up defenses specifically for your app’s threat model, not just generic protections.
DashO’s Best For
- Android and Java apps needing advanced code protection
- Developers building for regulated or high-risk industries
DashO’s Not Great For
- Teams working outside Android or Java environments
- Small apps without IP or compliance concerns
What sets DashO apart
DashO expects you to take a hands-on approach to code protection, not just check a box for compliance. It lets you design custom defense strategies, so your app’s security is tailored instead of generic. Unlike out-of-the-box “app wrapping” tools, DashO invites you to think about where your code is most exposed and lets you fine-tune obfuscation, anti-tamper, and runtime checks to match that.
This works best when you need protections specific to your IP or compliance environment, instead of broad security coverage.
Tradeoffs with DashO
DashO optimizes for granular controls and custom defenses, but setup and ongoing adjustments take more time. For low-risk or short lifecycle apps, you end up spending more effort than you might need.
Pros and Cons
Pros:
- Easy integration with popular development environments like Android Studio and Eclipse
- Efficient code obfuscation mechanisms
- Dedicated protection for Android and Java applications
Cons:
- Potential performance impact due to rigorous security checks
- Requires developers to be familiar with its configuration for maximum efficacy
- Might not cater to languages outside of Java and Android
AppSealing earns a spot here for its focus on real-time security monitoring for mobile applications. I recommend it when organizations want 24/7 in-app threat detection without relying on device-level controls. You get live alerts for suspicious activity and automated app shielding, which I like because it helps plug security gaps in fast-release mobile development cycles. AppSealing’s runtime protection stands out for teams working on consumer-facing apps with heightened visibility and exposure.
AppSealing’s Best For
- Mobile app developers needing real-time threat monitoring
- Teams releasing consumer apps with frequent updates
AppSealing’s Not Great For
- Organizations focused on web or desktop application security
- Security teams needing detailed vulnerability management tools
What sets AppSealing apart
AppSealing is built for mobile teams that want security features running live inside their apps, not just at the network or server level. Unlike tools like Veracode (which focus more on code scanning and static analysis), AppSealing expects you to watch for active threats in real time as users interact with your app. I see this work best when you care about runtime attack detection and automated response on actual devices.
Tradeoffs with AppSealing
AppSealing optimizes for real-time mobile app defense, but you give up deeper code analysis and manual control over remediation steps. This can limit how much insight you get into the root cause of security issues.
Pros and Cons
Pros:
- Compatible with leading app development platforms
- Comprehensive dashboard for a unified view of app security
- Real-time vulnerability alerts and responses
Cons:
- Limited documentation available for some features
- While it offers real-time insights, historical data might not be as detailed
- The user interface might be challenging for beginners
Other Application Security Software
Here are some additional application security software options that didn’t make it onto my shortlist, but are still worth checking out:
- Data Theorem
For data-centric app security
- RedShield
For active web vulnerability shielding
- Forces Unseen
For deep threat analysis
- Endcrypt
For end-to-end encryption needs
- Promon SHIELD
Good for in-depth runtime protection
- Quarks AppShield
Good for multi-layered app defense
- StarForce ProActive for Business
Good for comprehensive software licensing management
- ThreatCast
Good for dynamic application behavior analysis
- Trusted Software
Good for mainframe-based security enhancements
- Verimatrix App Shield
Good for scalable mobile app shielding
Application Security Software Selection Criteria
When selecting the best application security software to include in this list, I considered common buyer needs and pain points like data protection and vulnerability management. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detecting vulnerabilities
- Threat assessment
- Compliance reporting
- Application scanning
- Security alerts
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Machine learning integration
- Real-time threat intelligence
- Automated patch management
- Customizable dashboards
- Cross-platform compatibility
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive navigation
- User-friendly interface
- Customization options
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Comprehensive documentation
- Access to webinars
- Supportive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multichannel communication
- Response time efficiency
- Knowledgeable staff
- Availability of FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Free trial availability
- Discounts for long-term use
- Cost vs. features offered
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on support services
- User experience insights
- Comments on reliability
- Feature effectiveness feedback
How to Choose Application Security Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your business? Consider if it supports increased users or data without additional costs. |
| Integrations | Does it work with your current tech stack? Check compatibility with existing tools to ensure smooth workflow integration. |
| Customizability | Can you tailor it to your specific needs? Look for options to adjust settings and features to fit your unique processes. |
| Ease of use | Is it user-friendly for your team? Consider if the interface is intuitive and requires minimal training for new users. |
| Implementation and onboarding | How quickly can you get started? Evaluate the setup time and the resources needed for a successful launch, like training or support materials. |
| Cost | Does it fit your budget? Compare pricing plans and watch for hidden fees or costs that might add up over time. |
| Security safeguards | Are the security measures strong enough? Ensure the software includes encryption, access controls, and regular updates to protect your data. |
| Compliance requirements | Does it meet industry standards? Verify if the software complies with necessary regulations relevant to your sector, such as GDPR or HIPAA. |
What Is Application Security Software?
Application security software is designed to protect applications from external threats and vulnerabilities. IT professionals, developers, and security teams generally use these tools to ensure their applications are secure. Features like vulnerability scanning, compliance reporting, and threat assessment help with identifying and mitigating risks. These tools provide essential protection, keeping applications safe and secure.
Features
When selecting application security software, keep an eye out for the following key features:
- Vulnerability scanning: Automatically identifies weaknesses in applications to prevent potential breaches.
- Threat assessment: Evaluates potential threats to help prioritize security efforts.
- Compliance reporting: Generates reports to ensure adherence to industry standards and regulations.
- Security alerts: Notifies users of any suspicious activity or threats in real-time.
- Application scanning: Continuously scans applications to detect and fix vulnerabilities.
- Customizable dashboards: Allows users to tailor the interface to meet specific monitoring needs.
- Automated patch management: Ensures applications are up-to-date with the latest security patches.
- Real-time threat intelligence: Provides current data on threats to enhance security measures.
- Cross-platform compatibility: Works seamlessly with various operating systems and environments.
- Machine learning integration: Utilizes AI to improve threat detection and response over time.
Benefits
Implementing application security software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved data protection: By identifying and fixing vulnerabilities, it helps safeguard sensitive information.
- Risk reduction: Real-time threat intelligence and assessments minimize the chances of security breaches.
- Regulatory compliance: Compliance reporting ensures your business meets industry standards and regulations.
- Operational efficiency: Automated patch management saves time by keeping applications up-to-date without manual intervention.
- Informed decision-making: Customizable dashboards provide insights that help teams make better security decisions.
- Enhanced threat detection: Machine learning integration improves the ability to identify and respond to new threats.
- Cross-platform support: Compatibility with various systems ensures consistent security across your tech environment.
Costs & Pricing
Selecting application security software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in application security software solutions:
Plan Comparison Table for Application Security Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic vulnerability scanning, limited threat alerts, and community support. |
| Personal Plan | $10-$30/user/month | Vulnerability scanning, basic database security software, compliance reporting, and email support. |
| Business Plan | $50-$100/user/month | Advanced threat assessment, real-time alerts, automated patch management, and phone support. |
| Enterprise Plan | $150-$300/user/month | All features in lower plans, machine learning integration, customizable dashboards, and dedicated account manager. |
Application Security Software FAQs
Here are some answers to common questions about application security software:
How does application security software detect vulnerabilities?
Application security software continuously monitors your applications to identify vulnerabilities in real-time. It uses techniques like static code analysis and dynamic testing to pinpoint weaknesses. You can set it up to scan both third-party libraries and your custom code for comprehensive coverage.
What impact does enabling application security have on system performance?
Enabling application security might introduce some overhead, depending on the software you choose and your licensing model. Evaluate your system’s capacity to handle additional resource demands to ensure performance remains optimal while maintaining security.
Can application security software automatically resolve vulnerabilities?
Most application security solutions identify and monitor vulnerabilities but don’t automatically fix them. You’ll receive insights and recommendations to address these issues manually. It’s crucial to have a plan in place for your team to act on these insights promptly.
How often does application security software perform scans?
Many application security tools provide continuous monitoring rather than scheduled scans. This ensures vulnerabilities are detected as soon as they arise, giving your team the chance to respond quickly to new threats.
Is it necessary to restart applications after addressing vulnerabilities?
In some cases, resolving vulnerabilities requires restarting the affected application processes. This is especially true for updates related to third-party libraries or code-level vulnerabilities. Ensure your team is prepared to handle such restarts without disrupting your operations.
What’s Next:
If you're in the process of researching application security software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.