Best User Provisioning Software Shortlist
Managing user access can be a headache for any tech team. You’ve got to ensure everyone has the right permissions without compromising security. That’s where user provisioning software comes in. It helps you automate and simplify user management, saving your team time and reducing errors.
In my experience testing and reviewing these tools, I’ve found some standout options that can make your life easier. I’ve done the research, so you don’t have to. This listicle will guide you through the best user provisioning software available, highlighting features, pros, and cons.
You’ll get an unbiased look at each tool, helping you make the best choice for your team’s needs. Let’s dive into the world of user provisioning software and find the right fit for you.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best User Provisioning Software Summary
This comparison chart summarizes pricing details for my top user provisioning software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for global user provisioning for physical assets | Free demo available | from $5/person/month | Website | |
| 2 | Best for automated user provisioning | Free trial available | From $8/user/month (billed annually) | Website | |
| 3 | Best for streamlined Active Directory management | 30-day free trial | From $7/user/month (min 5 seats) | Website | |
| 4 | Best for integrated HR and IT automation | Free demo + free trial available | Pricing upon request | Website | |
| 5 | Best for directory-as-a-service capabilities | 30-day free trial + free demo available | Pricing upon request | Website | |
| 6 | Best for risk-based authentication | Not available | Pricing upon request | Website | |
| 7 | Best for secure enterprise identity verification | 30-day free trial available | From $6/user/month (billed annually) | Website | |
| 8 | Best for adaptive workforce authentication | 30-day free trial + free demo available | From $6/user/month (billed annually) | Website | |
| 9 | Best for open-source identity and access management | Not available | From $20/user/month (billed annually) | Website | |
| 10 | Best for SaaS operations management | 21-day free trial + free demo available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best User Provisioning Software Review
Below are my detailed summaries of the best user provisioning software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
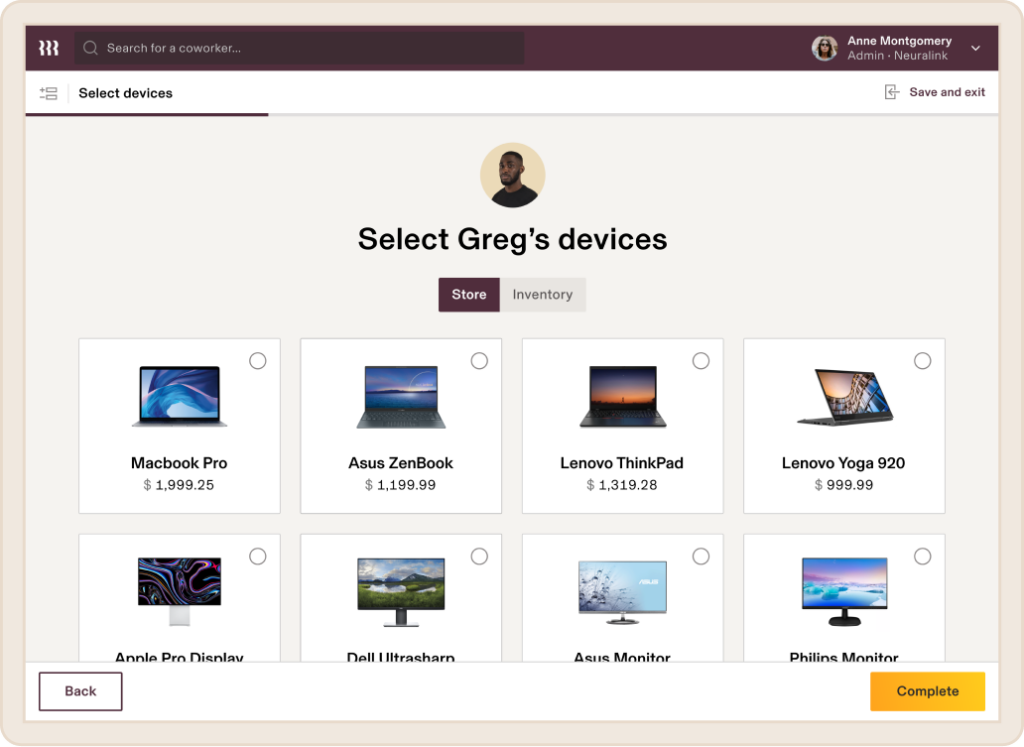
Deel is a global leader in payroll, HR, and IT management, offering a wide range of solutions that empower businesses to manage distributed teams in over 130 countries. With a strong focus on supporting global operations, Deel provides tools for handling everything from equipment delivery to workforce management, ensuring compliance.
Why I Picked Deel: Deel IT automates key workflows, such as onboarding and offboarding, enabling businesses to set up new hires with pre-configured devices, complete with all necessary apps and security settings. The platform’s global reach ensures that the provisioning of physical assets is not limited by geographic barriers—equipment and user accounts can be activated quickly, no matter where your employee is located.
Standout features & integrations:
Other standout features include its 24/7 global support and real-time visibility into all IT assets, enabling businesses to track, update, and manage devices across different regions efficiently. The platform also supports device recovery and reuse, ensuring optimal use of physical resources. Deel integrates with systems like Apple Business Manager, Windows Autopilot, Okta, BambooHR, Rippling, and Workday.
Pros and Cons
Pros:
- Can combine HR and IT asset management in one
- Helps automate asset workflows
- Supports equipment deployment in over 130 countries
Cons:
- Doesn't offer features beyond device management, like network and server management
- May not be ideal for teams with very complex IT asset needs
Rippling IT is a comprehensive platform designed to help businesses manage their IT infrastructure efficiently, with tools for device management, identity and access management, and inventory management. Amy Mortlock, VP of Marketing at ShadowDragon, shared: “The automated device management is impressive. When someone joins, leaves, or changes jobs, Rippling handles device setup, software installation, and security settings automatically—no manual IT work required.”
Why I Picked Rippling IT: It offers automated user provisioning. When you hire a new employee, the system automatically sets up their user accounts across all necessary applications based on predefined roles and departments. For instance, if you onboard a new sales representative, Rippling will create their accounts and grant them access to all sales-designated apps without manual intervention.
Standout features & integrations:
Other features include app-specific configuration, which allows you to set provisioning rules tailored to each application. This means that different roles within your company can have customized access to the tools they need. The platform also offers detailed audit trails and reporting, providing visibility into user activities and aiding in compliance efforts. Some integrations include Slack, Microsoft Teams, Zoom, Asana, Jira, Salesforce, Hubspot, Google Workspace, Microsoft 365, GitHub, Datadog, and Checkr.
Pros and Cons
Pros:
- Remote device lock and wipe capabilities
- Support for onboarding and offboarding employees and their devices
- Customizable workflow automation
Cons:
- Can be complex to set up initially
- Not all features may be necessary for smaller operations
Best for streamlined Active Directory management
ManageEngine ADManager Plus provides an extensive platform designed to manage and maintain Active Directory domains efficiently. Focusing on making Active Directory operations more intuitive, it ties directly into our rationale for being the best tool for streamlined Active Directory management.
Why I Picked ManageEngine ADManager Plus: I chose ManageEngine ADManager Plus after comparing various tools for Active Directory management. Its focus on providing a streamlined user experience and rich features made it stand out. When judging its ability to simplify complex AD tasks, it became evident that it truly was the best for those looking for a tool that offers a straightforward approach to Active Directory management.
Standout features & integrations:
ManageEngine ADManager Plus boasts an array of features catering to novice and expert administrators. Its bulk user management capabilities, combined with the detailed reports, make day-to-day operations efficient. Furthermore, it has vital integrations with various apps and on-premises systems, allowing for a more unified IT management experience.
Pros and Cons
Pros:
- Provides a self-service portal for end-users
- Integrated reporting system
- Comprehensive Active Directory management capabilities
Cons:
- Lacks some advanced automation features
- User interface could be more modern
- Steeper learning curve for beginners
Rippling is a platform that effortlessly merges HR and IT functions, providing businesses with a unified solution for employee data and system access. The tool's innate capability to combine HR processes with IT entitlements is the cornerstone of its integrated HR and IT automation prowess.
Why I Picked Rippling: In my journey of selecting and comparing platforms, Rippling stood out significantly. What captured my attention was its holistic approach to bridging HR tasks with IT functions. This unique blend, along with its adeptness in IAM (Identity Access Management) and identity governance, made me determine it's truly the best for those seeking integrated HR and IT automation solutions.
Standout features & integrations:
Rippling boasts features that facilitate effective identity governance, ensuring the right entitlements are provided to the right personnel. Its robust IAM capabilities also make managing user access structured and systematic. For integrations, Rippling is compatible with key business platforms like G Suite, Slack, and a myriad of HR applications, further bolstering its unified approach.
Pros and Cons
Pros:
- Allows for precise control over entitlements
- Strong emphasis on IAM and identity governance
- Holistic HR and IT automation in one platform
Cons:
- Needs more out-of-the-box integrations
- Some features may require training for optimal use
- Interface might seem overwhelming initially
JumpCloud provides a centralized platform to manage user identities across various IT resources. Businesses can achieve unified identity management through their directory-as-a-service capabilities, thus fulfilling complex access requests in today's heterogeneous IT environments.
Why I Picked JumpCloud: In the vast landscape of IT tools, selecting the right one often boils down to specific needs and standout features. When determining the best fit for directory services, JumpCloud immediately surfaced as a top contender due to its robust capabilities in handling user identities. I chose this tool because it effectively blends automated user processes with intricate directory functionalities, marking it as the best for directory-as-a-service capabilities.
Standout features & integrations:
JumpCloud excels in managing and automating user identities, ensuring that access requests are processed efficiently. The platform's comprehensive API further augments its directory functionalities, facilitating intricate integrations and custom workflows. As for integrations, JumpCloud has built partnerships with various IT platforms, allowing businesses to maintain cohesion in identity management across diverse ecosystems.
Pros and Cons
Pros:
- Efficient handling of access requests
- Advanced API for custom integrations and workflows
- Comprehensive management of user identities
Cons:
- Integrations, while vast, may not cover niche industry tools
- Some advanced features could require technical expertise
- Might be overwhelming for smaller organizations
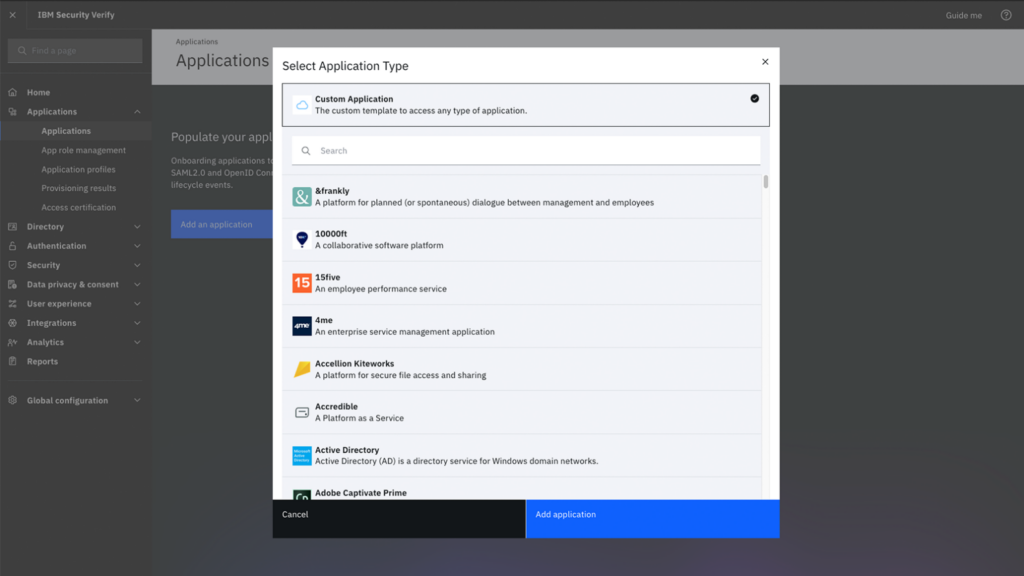
IBM Security Verify is a comprehensive access management solution emphasizing risk-based authentication, ensuring users are granted access based on contextual risks. This approach balances security and user convenience, aligning perfectly with the rising demands of modern digital businesses.
Why I Picked IBM Security Verify: In choosing and comparing various tools, IBM Security Verify particularly caught my attention due to its unique approach to authentication. The tool's emphasis on a risk-based method, which is different from traditional authentication strategies, piqued my interest. Hence, I am of the opinion that for organizations looking to pivot towards a more contextual and dynamic authentication system, IBM Security Verify is best for risk-based authentication.
Standout features & integrations:
IBM Security Verify is an account provisioning tool and a complete identity solution. Its risk-based authentication mechanism evaluates numerous parameters before granting access, adding an extra layer of security. Integration-wise, IBM Security Verify is compatible with various enterprise applications and systems, ensuring consistent identity practices regardless of the underlying platform.
Pros and Cons
Pros:
- Wide compatibility with numerous enterprise applications and systems.
- Comprehensive user provisioning tool ensuring efficient account management.
- Advanced risk-based authentication for improved security.
Cons:
- As with many IBM solutions, it may come with a steeper learning curve for some users
- Integration with certain legacy systems might require additional effort
- Might be perceived as complex for smaller organizations
Microsoft Entra ID is a tool designed to provide businesses with a robust mechanism for identity verification. As enterprises grow and navigate through complex hybrid environments, a secure and reliable identity verification becomes indispensable. Microsoft Entra ID squarely focuses on this, ensuring that enterprise identities are verified with utmost security.
Why I Picked Microsoft Entra ID: I picked Microsoft Entra ID as my top choice for identity verification tools. It's great for the enterprise sector, especially those in hybrid environments. After comparing it to other options, I found that it excels at providing secure identity verification. This makes it easy for the IT department to handle and authenticate users with confidence.
Standout features & integrations:
Microsoft Entra ID boasts of features that are tailored for today's complex business infrastructures. It's highly adaptive to hybrid environments, ensuring absolute identity verifications across both on-premise and cloud platforms. Furthermore, its deep integration with Microsoft 365 means that businesses can maintain a consistent identity verification method across the suite of Microsoft applications.
Pros and Cons
Pros:
- Deep integration with Microsoft 365 ensures a streamlined experience for the IT department.
- Extensive function in hybrid environments, balancing both on-premise and cloud.
- Tailored for enterprises, addressing specific challenges they face in identity verification.
Cons:
- The complexity may require dedicated IT personnel for setup and maintenance
- Businesses not invested in the Microsoft ecosystem might find some features redundant
- May be perceived as intricate for small businesses without hybrid infrastructures
Okta Workforce Identity is a renowned tool in the cybersecurity realm that focuses on providing robust identity solutions for the modern workforce. Its main thrust is adaptive authentication, tailoring access requirements based on varying user contexts and scenarios, which is essential for today's diverse and dynamic work environment.
Why I Picked Okta Workforce Identity: I have found that Okta Workforce Identity is a top choice for adaptive authentication. This tool stands out due to its ability to adjust access protocols based on user behavior and context. After comparing various options, I am confident that Okta Workforce Identity is the ideal solution for adaptive workforce authentication. It is particularly useful for businesses with constantly changing dynamics and security requirements.
Standout features & integrations:
Okta Workforce Identity is more than just an authentication tool. It offers advanced compliance reporting features, helping businesses meet their compliance requirements without hassles. Furthermore, Okta integrates with a multitude of enterprise applications, enhancing its adaptability and ensuring consistent identity practices across various platforms.
Pros and Cons
Pros:
- Extensive integrations with a myriad of enterprise tools, making it versatile in diverse IT environments.
- In-depth compliance reporting assists businesses in meeting stringent compliance requirements.
- Comprehensive adaptive authentication caters to varying workforce needs.
Cons:
- As a comprehensive tool, setup and initial configuration might be extensive
- Certain advanced features might require a steeper learning curve
- Might be perceived as overkill for very small businesses
WSO2 Identity Server offers a comprehensive solution for identity management, ensuring real-time and secure access to applications and services. As an open-source platform, it caters to organizations prioritizing flexibility, customization, and transparency in their identity and access management strategies.
Why I Picked WSO2 Identity Server: After evaluating various tools, I found that the open-source WSO2 Identity Server was the best option for identity and access management. Its transparency and flexibility make it the top choice.
Standout features & integrations:
WSO2 Identity Server prides itself on an efficient provisioning process, ensuring timely and accurate user data management. The platform supports Single Sign-On (SSO) and Multi-Factor Authentication (MFA) mechanisms, reinforcing its commitment to secure access. In integrations, WSO2 connects with a range of enterprise tools, ensuring consistent identity management across diverse business systems.
Pros and Cons
Pros:
- Wide-ranging integrations support uniform identity practices across tools.
- Efficient provisioning process enhances the user data management experience.
- Open-source nature ensures transparency and customization options.
Cons:
- Potential for complexities when integrating with proprietary systems
- Requires dedicated resources for optimal customization and deployment
- Might pose a steeper learning curve for those unfamiliar with open-source platforms
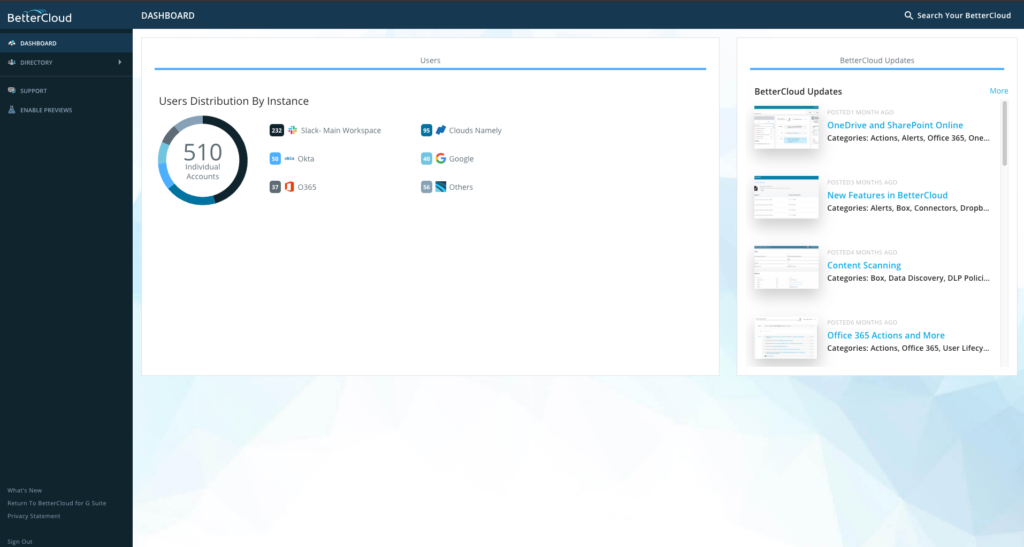
BetterCloud is a cloud-based platform tailor-made for IT professionals, offering extensive SaaS management tools to ensure efficient and secure operations. Its excellence in overseeing multiple SaaS environments ties in directly with our earlier declaration of its prowess in SaaS operations management.
Why I Picked BetterCloud: When selecting tools for the list, BetterCloud caught my attention because of its unique approach to managing diverse SaaS ecosystems. In comparing various platforms, it became evident that BetterCloud had a distinct edge, especially in centralizing the management of SaaS applications. Given its adeptness in offering granular controls over various SaaS apps, it is best for those keen on robust SaaS operations management.
Standout features & integrations:
BetterCloud flourishes with features such as advanced audit trails, multi-factor authentication, and automated deprovisioning to secure and optimize SaaS applications. Furthermore, it provides crucial integrations with prominent SaaS applications like Slack, Google Workspace, and Dropbox, making the management process coherent and integrated.
Pros and Cons
Pros:
- Efficient deprovisioning of user accounts
- Incorporates multi-factor authentication for added security
- Comprehensive cloud-based SaaS management tools
Cons:
- Pricing structure could be more transparent
- Might be overkill for small businesses
- Can be complex for beginners
Other User Provisioning Software
Here are some additional user provisioning software options that didn’t make it onto my shortlist, but are still worth checking out:
- Lumos
For energy-efficient IT solutions
- ConductorOne
For access rights orchestration
- GroupID By Imanami
For group lifecycle and automation
- OneLogin
Good for unified access management across devices
- HelloID
Good for streamlined identity management
- Zluri
Good for SaaS application management
- Uniqkey
Good for advanced password protection in EU
- Jamf connect
For Apple device identity management
- SailPoint
Good for comprehensive identity governance
- Auth0
Good for customizable identity authentication
- CyberArk Identity
Good for secure remote workforce connectivity
- Coreview
Good for Microsoft 365 management and insights
- Fastpath
Good for compliance and audit readiness
- Opal Security
Good for API security and policy enforcement
- Teleport
Good for secure infrastructure access
- PingFederate
Good for scalable enterprise federation and single sign-on
- Avigilon ACM
Good for on-premise access control
User Provisioning Software Selection Criteria
When selecting the best user provisioning software to include in this list, I considered common buyer needs and pain points like security concerns and integration capabilities. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Manage user access
- Automate user provisioning
- Integrate with existing systems
- Provide detailed reporting
- Ensure compliance with regulations
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Advanced security protocols
- Customizable workflows
- Real-time analytics
- Multi-factor authentication
- Self-service portals
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Easy navigation
- Minimal learning curve
- Responsive performance
- Clear documentation
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Supportive chatbots
- Informative webinars
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of 24/7 support
- Responsiveness to inquiries
- Access to a knowledge base
- Personalized assistance
- Community forums
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Features included in basic plans
- Scalability of pricing tiers
- Transparency of costs
- Discounts for annual billing
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on feature effectiveness
- Insights on ease of use
- Comments on customer support
- Reports on reliability and stability
How to Choose User Provisioning Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your organization? Consider future needs and if the tool can handle increased users without extra costs or performance issues. |
| Integrations | Does it connect with your existing systems? Check compatibility with your current tech stack to avoid costly workarounds or limitations. |
| Customizability | Can you tailor the tool to fit your workflows? Evaluate the ease of modifying settings and permissions to match your processes. |
| Ease of use | Is the interface intuitive for your team? Ensure it doesn't require extensive training or slow down daily operations. |
| Implementation and onboarding | How quickly can you get started? Look at the setup process, required resources, and support during onboarding to avoid delays. |
| Cost | How does pricing align with your budget? Compare costs against features and scalability. Watch for hidden fees or inflexible pricing models. |
| Security safeguards | Are data protection measures in place? Assess encryption, access controls, and compliance with industry standards to protect sensitive information. |
| Support availability | What support does the vendor offer? Check for 24/7 availability, response times, and the quality of resources like guides or community forums to help when issues arise. |
What Is User Provisioning Software?
User provisioning software is a tool that helps companies control who can access their systems, apps, and data. It keeps everything organized by making sure each person has the right access for their role.
Instead of manually adding or removing users, the software handles it automatically when someone joins, changes position, or leaves the company. This keeps access up to date and helps prevent mistakes.
Features
When selecting user provisioning software, keep an eye out for the following key features:
- Automated user creation: Automatically sets up new user accounts, saving time and reducing errors in the onboarding process.
- Access management: Controls user permissions and access levels to ensure security and compliance.
- Compliance reporting: Generates reports to help organizations meet regulatory requirements and audit needs.
- Identity federation: Connects multiple identity systems, allowing seamless access across different platforms.
- Single sign-on (SSO): Enables users to access multiple applications with one set of credentials, simplifying login processes.
- Multi-factor authentication: Adds an extra layer of security by requiring additional verification beyond passwords.
- Policy-based management: Enforces rules for user accounts and group memberships to maintain directory hygiene.
- Audit trails: Tracks user activities and changes to provide transparency and assist in troubleshooting.
- Customizable workflows: Allows organizations to tailor the software to fit their specific processes and needs.
- Integration capabilities: Connects with existing systems and applications to enhance functionality and efficiency.
Benefits
Implementing user provisioning software provides several benefits for your team and your business. Here are a few you can look forward to:
- Time savings: Automates user setup and access management, reducing manual work and speeding up the onboarding process.
- Enhanced security: Features like multi-factor authentication and access controls help protect sensitive data from unauthorized access.
- Compliance assurance: Generates compliance reports and audit trails, making it easier to meet regulatory requirements.
- Improved accuracy: Automation reduces errors in user provisioning, ensuring correct access levels and permissions.
- Operational efficiency: Integration capabilities allow the software to work alongside existing systems, enhancing overall workflow.
- Scalability: Supports growing organizations by handling increased user numbers without additional administrative burden.
- Simplified management: Centralizes user management, making it easier to oversee and adjust user roles and permissions.
Costs & Pricing
Selecting user provisioning software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in user provisioning software solutions:
Plan Comparison Table for User Provisioning Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic user management, limited integrations, and community support. |
| Personal Plan | $5-$25/user/month | User provisioning, basic reporting, and email support. |
| Business Plan | $25-$50/user/month | Advanced integrations, compliance reporting, and phone support. |
| Enterprise Plan | $50-$100/user/month | Custom workflows, dedicated account manager, and premium support services. |
User Provisioning Software FAQs
Here are some answers to common questions about user provisioning software:
What is the difference between user provisioning and deprovisioning?
User provisioning involves setting up user accounts and permissions when someone joins your organization. Deprovisioning is the process of removing access when they leave. Both are essential for maintaining security. Automating these tasks saves time and reduces errors, ensuring users have the right access when needed and none when they don’t.
Can user provisioning software integrate with existing IT systems?
Yes, most user provisioning software can integrate with existing IT systems. This includes directories like Active Directory and cloud services like Google Workspace. Integration helps maintain consistency across platforms, reducing the need for manual updates. Check compatibility with your current systems before purchasing to avoid issues.
How does user provisioning software enhance security?
User provisioning software enhances security by automating access controls and ensuring compliance. It helps enforce security policies, like password updates and multi-factor authentication. By maintaining accurate user data and permissions, it minimizes the risk of unauthorized access. Regular audits and reports further support security efforts.
Is training required to use user provisioning software?
Yes, some training is usually required to effectively use user provisioning software. The level of training depends on the complexity of the tool. Many vendors offer training resources like videos, webinars, and documentation. Investing time in training helps you and your team fully utilize the software’s capabilities, ensuring a smoother implementation.
What’s Next:
If you're in the process of researching user provisioning software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.