Best Privileged Access Management Solutions Shortlist
Here’s my shortlist of the best privileged access management solutions:
The best privileged access management solutions help teams control administrative permissions, reduce unauthorized access risks, and protect sensitive systems from internal and external threats. These tools make it easier to enforce least-privilege policies, monitor high-risk activity, and secure credentials across distributed environments.
When misconfigurations expose critical systems, manual approval processes slow urgent work, or privileged accounts go untracked, organizations face increased security gaps and greater operational risk. These issues make it harder for security and IT teams to maintain visibility, support audits, and respond quickly to suspicious behavior.
With over 20 years in the industry as a Chief Technology Officer, I’ve tested and reviewed dozens of privileged access management solutions across real-world environments to evaluate their security controls, audit features, and integration quality. This guide highlights the top privileged access management solutions. Each review covers features, pros and cons, and best-fit use cases to help you choose the right tool.
Why Trust Our Software Reviews
We’ve been testing and reviewing SaaS development software since 2023. As tech experts ourselves, we know how critical and difficult it is to make the right decision when selecting software. We invest in deep research to help our audience make better software purchasing decisions.
We’ve tested more than 2,000 tools for different SaaS development use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & check out our software review methodology.
Table of Contents
Best Privileged Access Management Solutions Summary
This comparison chart summarizes pricing details for my top privileged access management solutions selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for smart privilege elevation | Free trial + free demo available | Pricing upon request | Website | |
| 2 | Best for secure password vault | Free trial + demo available | From $3.33/month (billed annually) | Website | |
| 3 | Best for compliance with data regulations | Free trial + free demo available | Pricing upon request | Website | |
| 4 | Best for agentless PAM approach | 30-day free trial available | From $2/user/month | Website | |
| 5 | Best for enterprise-level integration | Free demo available | Pricing upon request | Website | |
| 6 | Best for privileged access without blind spots | 30-day free trial | From $3/user/month (billed annually) | Website | |
| 7 | Best for small to medium businesses | Free demo available | Pricing upon request | Website | |
| 8 | Best for scalability across industries | Not available | Pricing upon request | Website | |
| 9 | Best for seamless third-party integrations | Free trial available | From $35/month | Website | |
| 10 | Best for identity governance | Free demo available | Pricing upon request | Website |
-

Deel IT
Visit Website -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Cloudflare
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Privileged Access Management Solution Reviews
Below are my detailed summaries of the best privileged access management solutions that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
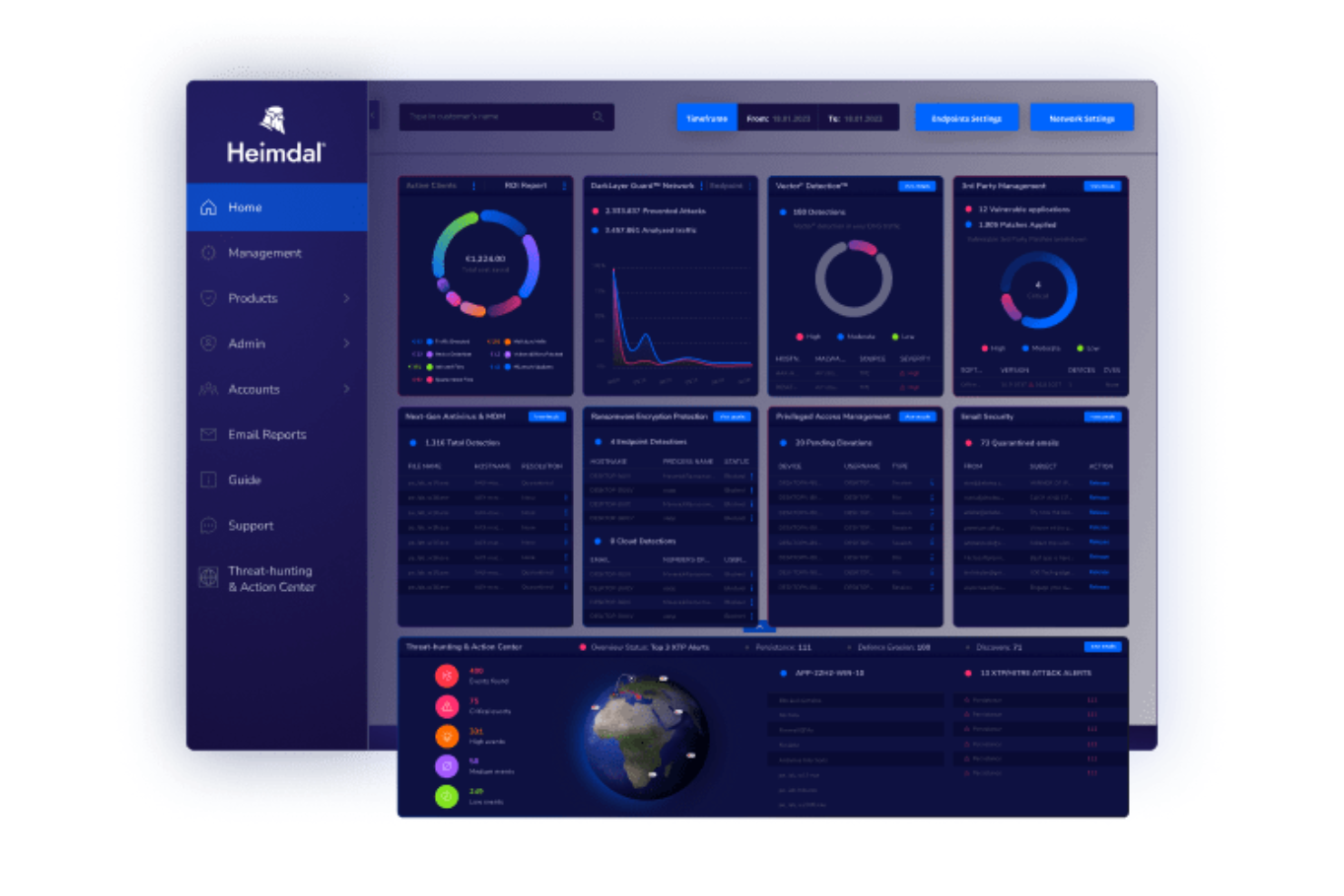
In the realm of privileged access management solutions, Heimdal stands out by addressing the unique security challenges faced by various industries, including healthcare, government, and education. Designed for organizations that prioritize compliance and data governance, it offers a robust framework for managing access to sensitive accounts and systems. By eliminating shared admin passwords and blocking unauthorized software installs, Heimdal provides your team with the tools needed to maintain a secure and compliant IT environment.
Why I Picked Heimdal
I picked Heimdal for its innovative approach to privileged access management, specifically its Smart Privilege Elevation and Delegation Management feature. This tool automates admin requests, allowing you to grant temporary admin rights that automatically expire, reducing the risk of privilege creep. Additionally, Heimdal's Application Control with AppFencing blocks unauthorized software installations, ensuring only approved applications run on your network. These features collectively help your organization maintain security without compromising on efficiency.
Heimdal Key Features
In addition to its standout privilege management tools, I also found several other features that enhance its value:
- Privileged Account & Session Management: This feature records and audits all privileged sessions, providing a clear trail for compliance and security audits.
- Just-in-Time Access: Offers temporary access to critical systems only when necessary, reducing the risk of privilege abuse.
- Mobile Approvals: Allows administrators to approve requests on the go, ensuring that your team maintains control over access even when they're away from their desks.
- Instant Compliance Reporting: Generates detailed reports to help your organization meet various regulatory standards, such as ISO 27001 and HIPAA.
Heimdal Integrations
Integrations include ConnectWise RMM, Autotask PSA, and other third-party cybersecurity tools. Additionally, Heimdal offers an API for custom integrations, allowing you to tailor the solution to fit your specific needs.
Pros and Cons
Pros:
- Comprehensive session monitoring logs
- Smart privilege elevation automation
- Granular role-based access controls
Cons:
- Pricing not publicly disclosed
- Interface may feel complex
Keeper Security is a password management and privileged access management solution designed for businesses and individuals. It focuses on securing passwords and sensitive data, providing features that enhance security and compliance.
Why I picked Keeper Security: Its secure password vault differentiates Keeper Security from other solutions. The platform uses zero-trust and zero-knowledge architecture, ensuring end-to-end encryption for user data. Features like password sharing and secrets management enhance security for your team. Keeper Security is FedRAMP authorized, meeting stringent government standards, making it ideal for high-security environments.
Standout features & integrations:
Features include password sharing, secrets management, and secure file sharing. Your team can benefit from passwordless authentication, reducing the risk of breaches. Keeper Security also offers compliance with certifications like HIPAA, GDPR, and PCI DSS.
Integrations include Microsoft Azure, Active Directory, LDAP, SSO, SAML, Google Workspace, Okta, Duo Security, Slack, and Splunk.
Pros and Cons
Pros:
- Passwordless authentication
- FedRAMP authorized
- Zero-knowledge architecture
Cons:
- Limited customization options
- May be complex for small teams
Cyberark is a leading provider of identity security and privileged access management solutions, serving industries like banking, healthcare, and government. It focuses on securing privileged access and enhancing security through features like single sign-on and multi-factor authentication.
Why I picked Cyberark: It excels in compliance with data regulations, making it a top choice for regulated industries. Cyberark's Identity Security Platform offers intelligent privilege controls and secrets management to meet stringent compliance requirements. It provides robust security measures without compromising productivity. The platform's emphasis on compliance ensures your team can meet regulatory standards effectively.
Standout features & integrations:
Features include single sign-on, multi-factor authentication, and secrets management. Your team can benefit from endpoint identity security to protect devices. Cyberark also offers machine identity security to safeguard automated processes.
Integrations include Splunk, ServiceNow, SailPoint, Okta, Microsoft Azure, AWS, Google Cloud, SAP, Oracle, and IBM.
Pros and Cons
Pros:
- Extensive industry coverage
- Machine identity security
- Strong compliance support
Cons:
- Requires technical expertise
- High resource requirements
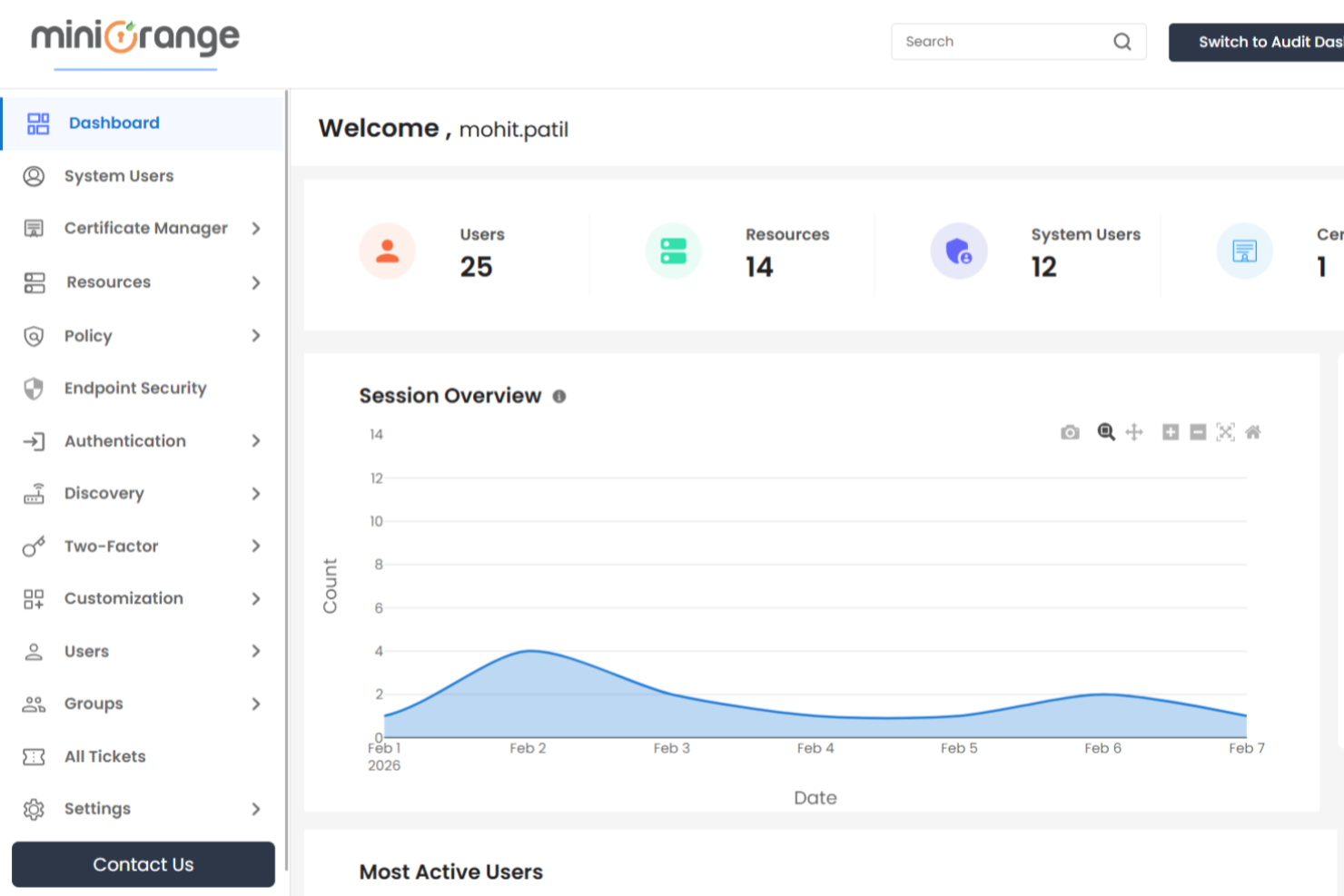
miniOrange PAM is a modern, identity-first privileged access management solution built for organizations that require strong privileged security controls. It is well-suited for regulated industries such as finance, healthcare, manufacturing, and government, where protecting sensitive data and meeting compliance requirements are essential. With capabilities like password vaulting, session monitoring, and just-in-time access, miniOrange PAM helps reduce risk and protect privileged accounts from evolving cyber threats.
Why I Picked miniOrange PAM
I picked miniOrange PAM because it offers modern, mature PAM capabilities with a strong identity-first foundation. It is a cloud-first solution that also supports on-premises and hybrid environments, giving you flexibility across infrastructure models. I value its advanced features such as just-in-time access management, privileged session monitoring and recording, granular access controls, password vaulting, and automated credential rotation. These capabilities support real-time auditing of privileged activity and allow temporary elevation of privileges based on verified needs, aligning with the principle of least privilege. Its agentless PAM architecture also makes deployment simpler and more scalable, which can be especially helpful if you want to strengthen privileged security without managing endpoint agents.
miniOrange PAM Key Features
In addition to its robust privileged access management capabilities, I also found several key features that enhance its value:
- Session Monitoring and Control: Provides real-time tracking and recording of privileged sessions, allowing intervention if unauthorized or risky activity is detected.
- Strong Identity-Based Authentication: Enforces access using native SSO and identity-level MFA, incorporating device trust, location, and risk signals to strengthen verification.
- Just-In-Time Privileged Access and EPM: Grants time-bound privileged access through approval workflows and automatically revokes rights after expiration, while Endpoint Privilege Management removes unnecessary admin rights and enforces least privilege on endpoints.
- AI-Driven Threat Detection: Uses anomaly detection, automated responses, and continuous learning to identify suspicious behaviour and improve privileged account protection.
miniOrange PAM Integrations
Integrations include Salesforce, Google Workspace, Microsoft 365, AWS, Azure, Slack, Jira, ServiceNow, Zoom, Dropbox, SSH, RDP, and VPN and VDI solutions. An API is also available to support custom integrations.
Pros and Cons
Pros:
- Solid endpoint privilege management
- Agentless PAM simplifies deployment
- Cloud-first and hybrid flexibility
Cons:
- Legacy migrations may need planning
- Complex setups may need specialists
BeyondTrust is a privileged access management solution tailored for large enterprises. It focuses on securing and managing access across complex IT environments, providing tools that enhance control and compliance.
Why I picked BeyondTrust: It excels in enterprise-level integration, making it ideal for large organizations with diverse systems. Features like session monitoring and real-time threat analytics help you maintain oversight and security. BeyondTrust's ability to integrate with various enterprise systems ensures smooth operations. The tool offers granular access controls, enhancing security for your team.
Standout features & integrations:
Features include session monitoring, real-time threat analytics, and granular access controls. Your team can use vulnerability management to identify and address potential risks. BeyondTrust also provides detailed audit trails for compliance purposes.
Integrations include Microsoft Active Directory, LDAP, ServiceNow, Splunk, SailPoint, CyberArk, Okta, Duo Security, RSA, and Google Workspace.
Pros and Cons
Pros:
- Strong enterprise-level integration
- Real-time threat analytics
- Detailed audit trails
Cons:
- Complex for small businesses
- Initial setup can be time-consuming
Zygon is a modern identity governance platform that helps IT and security teams control user identities, manage access, and detect shadow IT. It combines identity lifecycle management, access reviews, and governance workflows to strengthen security across SaaS environments.
Why I picked Zygon: I picked Zygon because it gives you fast, automated visibility into all apps and user identities, which is crucial for reducing access sprawl. You can build a consolidated inventory of cloud accounts quickly, even across shadow IT, helping you secure privileged access without blind spots. Zygon also automates deprovisioning, access reviews, and compliance workflows, making it a solid option for teams aiming to save time while staying audit-ready.
Standout features & integrations:
Features include a real-time cloud identity inventory, agentless and SCIM-less deprovisioning, and bulk access reviews. Zygon also offers a browser extension for managing apps without API connections and an Auto-Provisioning Atlas to track authentication methods.
Integrations include Google Workspace, Microsoft 365, Entra ID, Okta, n8n, Make, Slack, and Microsoft Teams.
Pros and Cons
Pros:
- Bulk access reviews
- Browser extension for non-API apps
- Agentless and SCIM-less deprovisioning
Cons:
- Smaller integration library
- Limited advanced reporting
ManageEngine PAM360 is a privileged access management solution designed for small to medium-sized businesses. It provides centralized control over IT infrastructure, helping manage and secure privileged accounts effectively.
Why I picked ManageEngine PAM360: Its suitability for small to medium businesses sets it apart. The tool offers comprehensive password management and session monitoring, making it accessible for teams with limited IT resources. It also provides automated compliance reporting to keep your business aligned with regulations. The intuitive dashboard simplifies management, allowing your team to focus on core tasks without getting bogged down in complex processes.
Standout features & integrations:
Features include automated compliance reporting, session monitoring, and an intuitive dashboard. Your team can benefit from real-time alerts to identify potential security threats. ManageEngine PAM360 also offers audit trails to track user activities and ensure accountability.
Integrations include Microsoft Active Directory, LDAP, ServiceNow, Jira, Azure, AWS, Google Cloud, Oracle, VMware, and SAP.
Pros and Cons
Pros:
- Intuitive user interface
- Automated compliance reporting
- Suitable for small businesses
Cons:
- Limited advanced features
- Basic reporting capabilities
Broadcom is a privileged access management solution catering to enterprises across various industries. It focuses on providing scalable security solutions to manage and protect privileged accounts effectively.
Why I picked Broadcom: Its scalability across industries makes it versatile for different enterprise environments. Broadcom offers centralized policy management and access controls, ensuring consistent security measures. It provides automated threat detection to identify and respond to potential risks. The platform's flexibility allows it to adapt to your organization's specific needs, making it suitable for diverse operational requirements.
Standout features & integrations:
Features include centralized policy management, automated threat detection, and flexible access controls. Your team can use detailed audit logs to track user activities. Broadcom also offers real-time analytics to monitor security events.
Integrations include Microsoft Active Directory, LDAP, ServiceNow, SAP, Oracle, IBM, AWS, Azure, Google Cloud, and Splunk.
Pros and Cons
Pros:
- Centralized policy management
- Automated threat detection
- Flexible access controls
Cons:
- Complex initial setup
- Ongoing maintenance needed
Auth0 is an identity management platform aimed at developers and IT teams. It provides authentication and authorization services, helping businesses secure user access and manage identities efficiently.
Why I picked Auth0: It excels in seamless third-party integrations, making it versatile for various applications. Auth0's extensive integration options allow your team to connect with existing systems effortlessly. The platform supports multiple authentication methods, enhancing security without complicating the user experience. Its comprehensive API support ensures flexibility, allowing you to tailor the solution to your specific needs.
Standout features & integrations:
Features include multiple authentication methods, comprehensive API support, and customizable login screens. Your team can benefit from real-time security monitoring to detect potential threats. Auth0 also provides detailed analytics to track user activity and improve security measures.
Integrations include Microsoft Azure, AWS, Google Cloud Platform, Salesforce, Slack, Twilio, Zendesk, GitHub, Zoom, and Dropbox.
Pros and Cons
Pros:
- Extensive third-party integrations
- Multiple authentication methods
- Comprehensive API support
Cons:
- Can be resource-intensive
- May have a steep learning curve
SailPoint is an identity governance solution tailored for enterprises that need to manage digital identities and secure access. It helps organizations ensure compliance and reduce security risks by providing visibility into who has access to what.
Why I picked SailPoint: Its focus on identity governance sets it apart, providing tools that ensure compliance and security. SailPoint offers features like access certification and policy management to help your team manage identities effectively. The platform's ability to detect and mitigate access risks enhances security for your organization. With SailPoint, you can automate access requests and approvals, streamlining the identity management process.
Standout features & integrations:
Features include access certification, policy management, and automated access requests. Your team can benefit from detailed reporting to monitor compliance. SailPoint also offers role-based access controls to ensure users have the right level of access.
Integrations include Microsoft Azure, AWS, ServiceNow, Workday, SAP, Salesforce, Oracle, Google Workspace, Okta, and Box.
Pros and Cons
Pros:
- Strong identity governance capabilities
- Automated access requests and approvals
- Detailed compliance reporting
Cons:
- Complex for small organizations
- Can be resource-intensive
Other Privileged Access Management Solutions
- One Identity
For cloud-based solutions
- Wallix
For managing remote access
- Cakewalk
For user-friendly interface
- JumpCloud
For comprehensive device management across different operating systems
- Okta
For identity management in large organizations
- Workato
For workflow automation
- Rippling IT
For role-based access control
- Microsoft Entra Verified ID
For verifying digital identities
- StrongDM
For privileged session management
- Delinea
For efficient privilege management
- SafeNet Trusted Access
For managing remote access
- Silverfort
For adaptive multi-factor authentication
- Nokia
For large-scale network environments
- IBM Security Verify Privilege
For hybrid cloud integration
- Azure AD (Microsoft Entra ID)
For seamless integration with Microsoft services
- Ekran
For insider threat detection
- Idency
For on-premise deployments
- PrivX
For cloud-native environments
- Arcon
For enterprise-level security
- Osirium PAM
For task automation capabilities
Privileged Access Management Solution Selection Criteria
When selecting the best privileged access management solutions to include in this list, I considered common buyer needs and pain points like ensuring compliance and managing remote access. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Manage privileged accounts
- Control access to sensitive data
- Monitor user sessions
- Provide audit logs
- Enforce security policies
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Adaptive authentication
- Session recording capabilities
- Real-time threat detection
- Automated compliance reporting
- Role-based access controls
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Ease of navigation
- Clarity of instructions
- Customization options
- Responsiveness of design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Supportive chatbots
- Regular webinars
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of live chat
- Response time to queries
- Quality of help documentation
- Access to a dedicated support team
- Availability of 24/7 support
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Features included in basic plans
- Flexible pricing options
- Discounts for longer commitments
- Cost-effectiveness for small teams
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Consistency of positive feedback
- Commonly reported issues
- Frequency of updates or improvements
- Satisfaction with customer support
- Overall user satisfaction ratings
How to Choose Privileged Access Management Solution
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
| Scalability | Ensure the solution can grow with your organization. Consider if it can handle increased users and data without performance loss. |
| Integrations | Check if it integrates with existing systems like Active Directory, cloud services, and other user provisioning software your team uses. |
| Customizability | Look for options to tailor the solution to fit your specific workflows and security policies. |
| Ease of Use | Evaluate if the interface is intuitive for your team, minimizing training time and user errors. |
| Budget | Assess if the pricing aligns with your financial constraints, including potential hidden costs for add-ons or upgrades. |
| Security Safeguards | Verify the solution offers strong encryption management (PKI software), multi-factor authentication, and compliance with standards like GDPR. |
| Support Services | Consider the availability of customer support, including live chat, phone, and email, to assist when issues arise. |
| Performance Monitoring | Ensure the tool provides real-time insights into system performance and user activities to quickly address potential issues. |
Trends in Privileged Access Management Solution
In my research, I sourced countless product updates, press releases, and release logs from different privileged access management solutions vendors. Here are some of the emerging trends I’m keeping an eye on:
- Zero Trust Architecture: More vendors are adopting zero trust models, which assume that threats could be both external and internal. This approach requires continuous verification of users and devices, enhancing security. Solutions like CyberArk have incorporated this into their offerings.
- Behavioral Analytics: Vendors are integrating behavioral analytics to monitor user actions and detect anomalies. This helps in identifying suspicious activities early. For example, Ekran uses behavioral analytics to enhance security monitoring.
- Cloud-native Solutions: There's a shift towards cloud-native architectures, which offer flexibility and scalability. These solutions are designed to work seamlessly in cloud environments, as seen with providers like PrivX.
- Passwordless Authentication: The move towards passwordless authentication methods is gaining traction. This trend reduces the risk of credential theft and improves user experience. Vendors like BeyondTrust are exploring passwordless options in their solutions.
- Unified Endpoint Management: Vendors are focusing on managing all endpoints through a single platform, which simplifies security management. This trend is evident in the best portal software that offer centralized control and monitoring, such as those provided by One Identity.
What Are Privileged Access Management Solutions?
Privileged access management solutions secure and manage privileged accounts within an organization. IT administrators, security professionals, and compliance officers typically use these tools to protect sensitive information and maintain regulatory compliance.
Features like zero trust architecture, behavioral analytics, and passwordless authentication help with securing access, detecting anomalies, and improving user experience. Overall, these tools ensure that only authorized users have access to critical systems, reducing the risk of data breaches.
Features of Privileged Access Management Solutions
When selecting privileged access management solutions, keep an eye out for the following key features:
- Zero trust architecture: Requires continuous verification of users and devices, enhancing security by assuming threats could be both external and internal.
- Behavioral analytics: Monitors user actions to detect anomalies, helping identify suspicious activities early on.
- Passwordless authentication: Reduces the risk of credential theft and improves user experience by eliminating the need for passwords.
- Role-based access controls: Ensures users have the appropriate access levels, enhancing security and compliance.
- Automated compliance reporting: Streamlines the process of generating reports to ensure your organization meets regulatory standards.
- Session monitoring: Tracks user sessions in real-time to maintain oversight and detect unauthorized activities.
- Cloud-native architecture: Offers flexibility and scalability, making it ideal for environments that rely on cloud services.
- Unified endpoint management: Provides centralized control and monitoring of all endpoints, simplifying security management.
- Access certification: Regularly reviews and certifies access rights to maintain security and compliance.
- Real-time threat detection: Identifies potential security threats as they occur, allowing for swift response and mitigation.
Benefits of Privileged Access Management Solutions
Implementing privileged access management solutions provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: By using zero trust architecture and behavioral analytics, these tools reduce the risk of unauthorized access and data breaches.
- Regulatory compliance: Automated compliance reporting and access certification help ensure your organization meets industry standards and regulations.
- Improved user experience: Passwordless authentication and role-based access controls make it easier for users to access the systems they need without compromising security.
- Operational efficiency: Automated provisioning and session monitoring streamline processes, reducing the workload on IT teams while maintaining oversight.
- Scalability: Cloud-native architectures and unified endpoint management allow your organization to grow without sacrificing security or performance.
- Real-time response: Real-time threat detection enables swift identification and mitigation of potential security threats, minimizing impact on your business.
- Centralized control: Unified management of identities and access across various environments simplifies security management and enhances overall governance.
Costs and Pricing of Privileged Access Management Solutions
Selecting privileged access management solutions requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in privileged access management solutions:
Plan Comparison Table for Privileged Access Management Solutions
| Plan Type | Average Price | Common Features |
| Free Plan | $0 | Basic access control, limited user management, and basic reporting. |
| Personal Plan | $5-$25 /user /month | Single-user access, password management, and basic security features. |
| Business Plan | $25-$50 /user /month | Multi-user support, session monitoring, role-based access, and compliance reporting. |
| Enterprise Plan | $50-$100 /user /month | Advanced security analytics, integration with other systems, unlimited users, and dedicated support. |
Privileged Access Management Solution FAQs
Here are some answers to common questions about privileged access management solutions:
How does a PAM solution work?
PAM solutions secure privileged account credentials by storing them in a secure vault. Administrators must go through the PAM system to access these credentials, ensuring authentication and logging each access. This process helps protect sensitive accounts from unauthorized use.
What is the difference between ZTNA and PAM?
PAM focuses on securing and managing access to critical systems, while ZTNA enforces strict access controls across entire networks. Both are vital for cybersecurity, but they address different security needs. PAM manages privileged access, whereas ZTNA continuously verifies users’ access across networks.
What are the requirements for privileged access management?
Effective PAM requires multifactor authentication, automated security measures, and removal of endpoint user access. Establishing baselines and monitoring deviations are also crucial for maintaining security. These practices help prevent unauthorized access and ensure compliance.
What is the risk of privileged access management?
Neglecting PAM can lead to data breaches, privilege escalation, and insider threats. Attackers may exploit elevated access rights, causing operational and financial damage. Implementing PAM mitigates these risks by securing sensitive accounts and monitoring access.
How does PAM reduce insider threats?
PAM reduces insider threats by limiting access to sensitive accounts and monitoring user activities. It enforces strict controls over who can access what resources, helping prevent misuse of privileges. By recording all access, PAM deters potential malicious actions.
Can PAM solutions integrate with existing security systems?
Yes, PAM solutions often integrate with existing security systems like IAM, SIEM, and other IT tools. This integration enhances overall security by providing a unified approach to managing access and monitoring activities across different platforms.
What's Next?
Boost your SaaS growth and leadership skills. Subscribe to our newsletter for the latest insights from CTOs and aspiring tech leaders. We'll help you scale smarter and lead stronger with guides, resources, and strategies from top experts!