Best IAST Tools Shortlist
Here’s my shortlist of the best IAST tools:
The best IAST tools help development and security teams detect vulnerabilities in real time by analyzing applications as they run. They combine code instrumentation with runtime monitoring to uncover issues like insecure data flows, unvalidated inputs, and weak authentication logic, problems that often slip past static scans or manual reviews.
Many teams turn to IAST because they’re tired of chasing false positives, debugging vague stack traces, or juggling separate security tools that don’t integrate with their development pipelines. These gaps waste time and leave risks unaddressed, especially when applications handle sensitive data across multiple languages and frameworks.
I’ve worked with engineering and security groups migrating from legacy static testing setups and have tested IAST tools in live production and CI/CD environments. That experience has shown me which platforms actually deliver accurate results without slowing down releases.
In this guide, you’ll see which IAST tools provide meaningful visibility into runtime risks, reduce noise in alerts, and help your team prioritize the vulnerabilities that matter most.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best IAST Tool Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for comprehensive code scanning | Free plan available + free demo | From $350/month | Website | |
| 2 | Best for dynamic security scanning flexibility | Free demo available | Pricing upon request | Website | |
| 3 | Best for fast web application scanning | Free demo available | Pricing upon request | Website | |
| 4 | Best for comprehensive software exposure platform | Free demo available | Pricing upon request | Website | |
| 5 | Best for hybrid application security solutions | Not available | From $35/user/month (billed annually) | Website | |
| 6 | Best for holistic software integrity | Not available | From $40/user/month (billed annually) | Website | |
| 7 | Best for cloud-based application defense | Not available | From $65/user/month (billed annually) | Website | |
| 8 | Best for integrated vulnerability management | Free trial + free demo available | From $1.62/asset/month (billed annually) | Website | |
| 9 | Best for automating application vulnerability testing | Free demo available | From $29/user/month (billed annually) | Website | |
| 10 | Best for scalable application security programs | Free demo available | Pricing upon request | Website |
-

QA Wolf
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

NordLayer
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.3 -

Intruder
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best IAST Tools Reviews
Aikido Security is an all-in-one security platform designed to help your development team secure every aspect of your stack, from code to cloud. By centralizing various security scanners into a single platform, Aikido enhances the process of identifying and fixing vulnerabilities.
Why I Picked Aikido Security:
Aikido's Static Application Security Testing (SAST) capabilities are a key reason to consider it among the top IAST tools. Its comprehensive source code scanner can detect vulnerabilities like SQL injection, cross-site scripting (XSS), and buffer overflows before issues can be merged, ensuring that potential threats are addressed early in the development process.
Standout features and integrations:
Aikido also offers AI Autofix, which provides one-click fixes for identified vulnerabilities. Other key features include cloud posture management that detects misconfigurations across major cloud providers, secrets detection to identify exposed API keys and passwords in your code, and container security scanning to ensure your container images are free from vulnerabilities. The platform integrates with GitHub, GitLab, BitBucket, Azure Pipelines, Drata, Vanta, Asana, ClickUp, Monday.com, Microsoft Teams, and Jira.
Pros and Cons
Pros:
- Scalable for growing teams
- Offers actionable insights
- Has a comprehensive dashboard and customizable reports
Cons:
- Does not have endpoint security or intrusion detection capabilities
- Ignores vulnerabilities if no fix is available
New Product Updates from Aikido Security
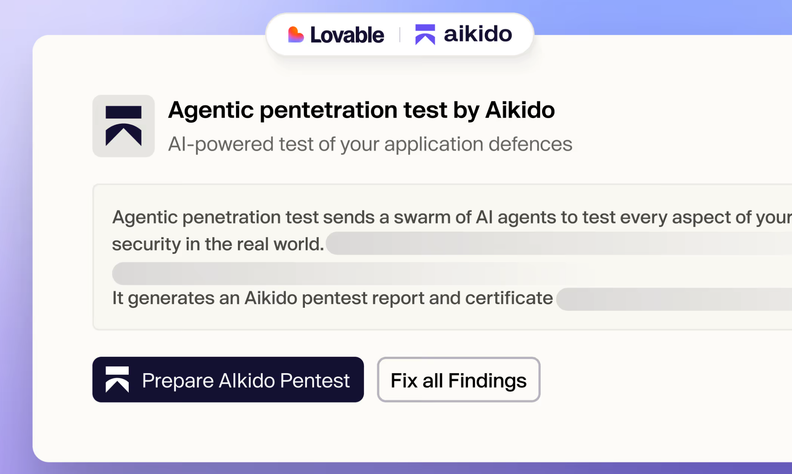
Aikido Adds Lovable Integration for Pentesting
Aikido introduces integration with Lovable and integrated pentesting. This update helps teams detect and fix security issues before deployment. For more information, visit Aikido Security's official site.
Invicti has emerged as a potent tool in the realm of cybersecurity, primarily focusing on dynamic security scanning. Its adaptive scanning approach not only ensures in-depth vulnerability detection but also offers a degree of flexibility that many businesses find invaluable.
Why I Picked Invicti:
When curating a list of security tools, my selection process led me to Invicti, and for good reasons. In evaluating the landscape, Invicti made an impression with its ability to adjust to varying web application structures and environments. This trait of dynamic flexibility is pivotal in today's diverse digital ecosystem, and it is why I hold the opinion that Invicti is unmatched in this aspect.
Standout features and integrations:
Invicti is praised for its tailored scanning capabilities that allow it to adapt to different application landscapes. Its Proof-Based Scanning™ technology provides tangible evidence of identified vulnerabilities, ensuring that threats are real and not false positives. On the integration front, Invicti fits into various IT environments, offering compatibility with leading issue trackers, CI/CD platforms, and security solutions.
Pros and Cons
Pros:
- Broad integration capabilities
- Proof-Based Scanning™ minimizes false positives
- Tailored scanning for diverse applications
Cons:
- Additional features may require separate purchases
- Cost could be prohibitive for smaller businesses
- Might require time to configure for complex environments
New Product Updates from Invicti
Invicti Enterprise Adds WebLogic Support and Security Enhancements
The latest Invicti Enterprise v25.10.0 release introduces WebLogic support for Java Shark sensors and improved secrets management through SEM integrations. It also refines API consistency and strengthens overall platform stability. For more information, visit Invicti's official site.
Acunetix has established itself as a notable cybersecurity solution specifically engineered for web application scanning. With the growing need for swift scanning capabilities, Acunetix's fast processing time aligns with the demand for rapid vulnerability detection in web applications.
Why I Picked Acunetix:
In the realm of security tools focused on web applications, my choice gravitated towards Acunetix because of its pronounced speed in scanning processes. Having compared multiple tools, Acunetix's differentiator lies in its unmatched pace and efficiency in identifying vulnerabilities. This speed-centric approach solidifies its place as the best tool for fast web application scanning.
Standout features and integrations:
Acunetix is equipped with advanced vulnerability detection features, capable of detecting SQL injections, XSS vulnerabilities, and more. Its DeepScan technology allows for the scanning of dynamic web applications, ensuring thorough coverage. Integration-wise, Acunetix offers compatibility with widely-used issue trackers, CI/CD platforms, and popular web application firewalls, which bolsters its utility in diverse IT environments.
Pros and Cons
Pros:
- DeepScan technology for dynamic web apps
- Integration with common IT platforms and tools
- Advanced vulnerability detection capabilities
Cons:
- Premium features might escalate costs
- Might be overkill for very small applications
- Learning curve for new users
Checkmarx delivers a platform designed to identify software vulnerabilities from source code to runtime. Addressing the entire software exposure landscape, this tool offers a comprehensive approach, ensuring that applications remain secure across different stages of the development lifecycle.
Why I Picked Checkmarx:
After evaluating and comparing various tools, I concluded that Checkmarx stands apart due to its all-encompassing approach to software security. My judgment was influenced by its capability to monitor vulnerabilities across both source code and runtime. Recognizing the challenges many businesses face in managing software exposures across a product's lifespan, I believe Checkmarx is best positioned for offering a comprehensive software exposure platform.
Standout features and integrations:
Checkmarx emphasizes its SAST tool, which thoroughly reviews source code for potential risks. Furthermore, its Interactive Application Security Testing (IAST) scrutinizes the application in runtime to detect vulnerabilities that might be missed in the code review stage. On the integrations front, Checkmarx easily integrates with popular CI/CD tools, version control systems, and issue trackers, ensuring smooth workflows and real-time vulnerability management.
Pros and Cons
Pros:
- Comprehensive coverage caters to the entire software development lifecycle
- Easily integrates with popular development and deployment tools.
- Offers both SAST and IAST solutions, ensuring a broad scope of vulnerability detection.
Cons:
- The absence of transparent pricing might deter some potential users
- Could be perceived as complex by teams new to security platforms
- Might be overkill for smaller projects or teams
Micro Focus delivers an extensive range of application security solutions, adept at securing both traditional and modern applications. With its hybrid approach, it caters to enterprises that leverage a mix of on-premises and cloud-based applications, ensuring comprehensive protection.
Why I Picked Micro Focus:
In my quest to find the most versatile and encompassing application security tools, Micro Focus stood out prominently. I chose this solution because it effectively bridges the gap between traditional and modern application security requirements, offering an adaptable platform for diverse enterprise needs. Its prowess in delivering hybrid solutions solidifies its position as the best for businesses seeking to secure a mix of application environments.
Standout features and integrations:
Micro Focus boasts an impressive set of features, including dynamic and static application security testing, which provides insights into potential threats at every stage of the development lifecycle. Additionally, the software's vulnerability management capabilities allow teams to prioritize and tackle security challenges methodically. In terms of integrations, Micro Focus fits snugly into diverse development ecosystems, connecting with popular CI/CD tools and other software development platforms, ensuring a holistic security approach.
Pros and Cons
Pros:
- Integrates smoothly with diverse development tools
- Rich vulnerability management features
- Comprehensive hybrid application protection
Cons:
- Interface could be more intuitive for first-time users
- Some features may be overkill for small teams
- Might have a steeper learning curve
Synopsys is at the forefront of ensuring software integrity throughout the entire development lifecycle. This platform provides comprehensive tools that look beyond just security, diving deep into the very essence of software quality and reliability.
Why I Picked Synopsys:
In the vast landscape of software integrity tools, Synopsys made a distinct impression on me. I selected this tool due to its all-encompassing approach that addresses not just vulnerabilities but also the overall quality and reliability of the software. Such a holistic perspective aligns with its recognition as the best choice for businesses focused on achieving impeccable software integrity.
Standout features and integrations:
Synopsys excels with its suite of dynamic and static application security testing tools, coupled with software composition analysis. These features provide thorough insights into potential threats and the overall health of the software. Integrations-wise, Synopsys plays well with a myriad of development tools and platforms, connecting with popular CI/CD solutions and software development platforms for an integrated software integrity approach.
Pros and Cons
Pros:
- Efficient integrations with key development platforms
- Robust set of testing and analysis tools
- Comprehensive approach to software integrity
Cons:
- Pricing could be a barrier for smaller teams
- Comprehensive features may be overwhelming for beginners
- Initial setup might be complex
Qualys Web App Scanning provides a comprehensive solution for web application security, harnessing the power and accessibility of the cloud. Its primary goal is to defend applications in the cloud environment, making it particularly effective for businesses relying heavily on cloud infrastructures.
Why I Picked Qualys Web App Scanning:
My process of selection naturally directed me to Qualys Web App Scanning after careful comparison and judgment of various tools in the market. The unique blend of its cloud-native nature coupled with robust security scanning functionalities marked it as distinct. Given the increasing adoption of cloud infrastructure, I discerned that Qualys stands out in providing robust defense specifically tailored for cloud-based applications.
Standout features and integrations:
Qualys shines with its Continuous Monitoring feature, which keeps a vigilant eye on an organization's web apps, instantly alerting teams of any vulnerabilities or threats. Furthermore, its Web Application Firewall integration ensures real-time protection against threats, facilitating a proactive defense strategy. In terms of integrations, Qualys supports a range of platforms, including SIEM systems, GRC tools, and bug-tracking platforms, making it versatile for diverse IT setups.
Pros and Cons
Pros:
- Versatile integrations support a wide range of IT environments
- Integrated Web Application Firewall for real-time protection.
- Continuous Monitoring ensures ongoing vulnerability checks.
Cons:
- Licensing model may not fit every organizational size or type
- Some features may seem complex for small-scale applications
- Might present a learning curve for those unfamiliar with cloud-based tools
Rapid7 has positioned itself as a leader in cybersecurity, specializing in vulnerability management and threat detection. By focusing on an integrated approach, the tool streamlines the process of identifying, analyzing, and rectifying potential vulnerabilities in a system.
Why I Picked Rapid7:
From the vast array of vulnerability management tools, Rapid7 resonated with me due to its cohesive integration capabilities. Having judged various tools, I determined that Rapid7's ability to not only pinpoint vulnerabilities but also effectively manage and mitigate them sets it apart. This cohesive, integrated approach makes it the optimal choice for those looking for comprehensive vulnerability management.
Standout features and integrations:
Rapid7 boasts a dynamic range of features, including its InsightVM for real-time vulnerability management and Metasploit for penetration testing. Moreover, its capability to continuously monitor environments ensures a proactive approach to threat detection. When it comes to integrations, Rapid7 meshes with an array of systems, including popular SIEM solutions, cloud providers, and ticketing systems, to ensure a streamlined vulnerability management process.
Pros and Cons
Pros:
- Wide range of integrations for streamlined operations
- Comprehensive penetration testing tools
- Real-time vulnerability monitoring
Cons:
- Some users may find the interface challenging to navigate
- Pricing may not suit smaller enterprises
- Might require skilled personnel for full utilization
HCL AppScan is a robust application security tool that identifies vulnerabilities and assists in their remediation. With an emphasis on automation, the tool streamlines the process of vulnerability testing, enabling businesses to secure applications efficiently.
Why I Picked HCL AppScan:
While evaluating the myriad of application security tools available, HCL AppScan caught my attention for its dedication to automation. I chose this platform because it has made strides in ensuring that vulnerability testing isn't just comprehensive but also automated, thereby reducing manual intervention. Its emphasis on automating the testing process is what positions it as the best choice for those who want efficient and consistent vulnerability scanning without the overhead of manual checks.
Standout features and integrations:
At the heart of HCL AppScan lies its automated scanning engine, capable of detecting a wide range of vulnerabilities from SQL injections to cross-site scripting. Additionally, the tool provides actionable insights and remediation recommendations to bridge security gaps. On the integrations front, HCL AppScan offers compatibility with a variety of development environments and platforms, ensuring that application security testing remains an integral part of the development cycle without causing disruptions.
Pros and Cons
Pros:
- Compatible with diverse development environments
- Actionable remediation insights
- Comprehensive automated vulnerability detection
Cons:
- Limited customization options for reporting
- Advanced configurations require a deeper understanding
- Might be overwhelming for newcomers
Veracode presents itself as a comprehensive application security platform designed to meet the requirements of modern organizations. With a focus on scalability, it assists enterprises in expanding their security measures in tandem with their growth, ensuring no application goes unchecked, irrespective of its scale.
Pros and Cons
Pros:
- Robust integration with popular DevOps tools
- Cloud-based for always-on access and updates
- End-to-end security analysis capabilities
Cons:
- Reliance on cloud might not suit all privacy preferences
- Pricing might be steep for small-scale users
- Learning curve for some advanced features
Other IAST Tools
Below is a list of additional IAST tools that I shortlisted but did not make it to the top 10. Definitely worth checking them out.
- Detectify
For crowdsource-powered vulnerability insights
- Contrast Security
For continuous application protection
- ImmuniWeb
For AI-powered web security testing
- Appknox
Good for mobile application security
- Snyk
Good for developer-first security approach
- Kiuwan
Good for software risk management across lifecycles
- GitLab
Good for integrated CI/CD Pipelines and DevOps practices
- Trustwave
Good for managed security services
- Astra API Security
Good for end-to-end website security solutions
- Tenable.io
Good for comprehensive vulnerability management
- Grammatech
Good for advanced code analysis capabilities
- CAST
Good for in-depth application structure assessment
- ArmorCode
Good for next-gen application security orchestration
- Positive Technology
Good for threat intelligence and prevention
- Pentest
For penetration testing expertise and insights
Other IAST-Related Tool Reviews
IAST Tool Selection Criteria
When selecting the best IAST tools to include in this list, I considered common buyer needs and pain points like detecting vulnerabilities early in the development process and integrating smoothly with existing CI/CD pipelines. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detect security vulnerabilities
- Provide real-time analysis
- Integrate with CI/CD pipelines
- Support multiple programming languages
- Offer detailed reporting
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Customizable dashboards
- Machine learning integration
- Real-time threat intelligence
- Automated remediation suggestions
- User behavior analytics
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Clear documentation
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Supportive chatbots
- Comprehensive webinars
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of 24/7 support
- Access to a knowledge base
- Response time to queries
- Availability of live chat
- Quality of technical assistance
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Availability of free trials
- Cost of additional features
- Discounts for long-term commitments
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Frequency of positive feedback
- Common complaints
- Testimonials on support quality
- Feedback on feature effectiveness
How to Choose IAST Tool
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the tool grow with your needs? Consider future expansion and whether the tool can handle increased load without a hitch. |
| Integrations | Does it easily connect with your existing tools? Check for compatibility with your CI/CD pipelines and other systems you rely on. |
| Customizability | Can you tailor the tool to fit your workflows? Look for options that allow for adjustments to meet your specific requirements. |
| Ease of use | Is the tool user-friendly for your team? Evaluate the interface and how quickly your team can learn to use it effectively. |
| Implementation and onboarding | How long will it take to get up and running? Consider the resources needed for setup and the availability of training materials. |
| Cost | Does the pricing align with your budget? Examine the cost of ownership, including any hidden fees or charges for additional features. |
| Security safeguards | Does it meet your security standards? Ensure it provides robust protection against vulnerabilities and complies with your security protocols. |
| Compliance requirements | Does it adhere to industry regulations? Verify that the tool supports compliance with standards relevant to your business, like GDPR or HIPAA. |
What Are IAST Tools?
IAST tools are interactive application security testing solutions used to identify and address security vulnerabilities in software applications. They are generally used by developers, security analysts, and IT professionals to ensure application security and integrity. Real-time analysis, integration with CI/CD pipelines, and detailed reporting help with identifying issues early and maintaining secure development practices. Overall, these tools provide valuable insights to enhance the security posture of software applications.
Features
When selecting IAST tools, keep an eye out for the following key features:
- Real-time analysis: Identifies vulnerabilities as code is executed, allowing developers to address issues immediately.
- CI/CD integration: Seamlessly works with existing continuous integration and delivery pipelines to maintain security throughout the development lifecycle.
- Multi-language support: Analyzes code written in various programming languages, ensuring broad applicability across projects.
- Detailed reporting: Provides comprehensive reports on identified vulnerabilities, helping teams understand and prioritize fixes.
- Customizable dashboards: Offers tailored views to monitor specific metrics and security concerns relevant to your organization.
- Automated remediation suggestions: Delivers actionable recommendations to quickly address detected vulnerabilities.
- User behavior analytics: Monitors how applications are used to identify unusual patterns that may indicate security risks.
- Interactive product tours: Guides users through the tool's features, enhancing onboarding and ease of use.
- Training resources: Includes videos, webinars, and documentation to support learning and effective tool utilization.
- Security safeguards: Ensures compliance with security protocols to protect sensitive data within applications.
Benefits
Implementing IAST tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security: By identifying vulnerabilities in real-time, IAST tools help you maintain a secure application environment.
- Faster development cycles: Integration with CI/CD pipelines allows for continuous security checks without slowing down the development process.
- Increased efficiency: Automated remediation suggestions save time by providing developers with actionable steps to fix issues quickly.
- Better resource allocation: Detailed reporting helps prioritize vulnerabilities, ensuring your team focuses on the most pressing security issues first.
- Enhanced learning: Training resources and interactive product tours empower your team to use the tool effectively, accelerating the onboarding process.
- Compliance assurance: Security safeguards within the tools help meet industry standards, reducing the risk of non-compliance penalties.
- Adaptability: Multi-language support ensures that IAST tools can be used across various projects, catering to different programming needs.
Costs & Pricing
Selecting IAST tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in IAST tools solutions:
Plan Comparison Table for IAST Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic vulnerability detection, limited language support, and minimal reporting. |
| Personal Plan | $10-$30/user/month | Real-time analysis, CI/CD integration, and basic reporting. |
| Business Plan | $50-$100/user/month | Multi-language support, detailed reporting, customizable dashboards, and support. |
| Enterprise Plan | $150-$300/user/month | Advanced security features, full language support, dedicated account manager, and compliance tools. |
IAST Tools FAQs
Here are some answers to common questions about IAST tools:
What are IAST tools, and why are they important?
IAST (Interactive Application Security Testing) tools are solutions that identify vulnerabilities in software applications in real time during their normal execution. They are crucial because they provide immediate feedback to developers, allowing them to detect and fix vulnerabilities during the development process, thus enhancing software security and reducing post-production fixes.
What are the limitations of IAST?
IAST can increase resource consumption, such as CPU and memory usage, during testing. This might slow down performance, especially in resource-constrained environments. Ensure your infrastructure can handle the additional load to avoid any disruptions in performance.
In which environment is an IAST tool most effective?
IAST works best in a QA environment with automated functional tests running. This setup allows the tool to observe real code execution and provide accurate vulnerability assessments, helping your team address issues before moving to production.
How accurate is IAST?
IAST offers precise findings with fewer false positives by observing real code execution and data paths. This accuracy helps developers quickly identify and fix vulnerabilities, reducing the time spent on false alarms and enhancing overall security.
Does IAST require specific configurations?
Yes, IAST may require specific configurations to integrate with existing development setups. Ensure your team is prepared to make necessary adjustments for optimal tool performance and effectiveness in your unique environment.
How does IAST compare to other testing methods?
IAST provides real-time insights by analyzing running applications, unlike SAST or DAST, which examine static code or external inputs. This approach gives IAST an edge in identifying runtime vulnerabilities, making it a valuable addition to your security strategy.
What’s Next?
If you're in the process of researching IAST tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.