10 Best Data Loss Prevention Software Shortlist
In today's digital world, keeping your data safe is a top priority. Data loss can be a nightmare for you and your team, leading to lost time, money, and trust. That's where data loss prevention software comes in—it helps you protect sensitive information and ensure compliance with regulations.
I test and review software independently, focusing on what truly matters to tech experts like you. In my experience, finding the right data loss prevention tools can make all the difference in safeguarding your business.
In this article, I'll share my top picks for data loss prevention software. You'll get an unbiased look at features, pros and cons, and how these tools can alleviate your challenges. Let's dive in and find the best fit for your needs.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Data Loss Prevention Software Summary
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for insider threat detection | Free trial + free demo available | From $14/seat/month (billed annually) | Website | |
| 2 | Best for threat detection and response | Not available | From $15/user/month (billed annually) | Website | |
| 3 | Best for large-scale enterprise data protection | Not available | Customized price upon request | Website | |
| 4 | Best for holistic data protection across hybrid cloud environments | Not available | Pricing upon request | Website | |
| 5 | Best for database security and compliance | 30-day free trial available | Pricing upon request | Website | |
| 6 | Best for advanced machine learning-based protection | Not available | Pricing upon request | Website | |
| 7 | Best for context-aware data security | Not available | From $10/user/month (billed annually) | Website | |
| 8 | Best for integrated endpoint and network security | Not available | From $15/user/month | Website | |
| 9 | Best for cloud-native environments | Not available | From $10/user/month (billed annually) | Website | |
| 10 | Best for USB and peripheral device control | Not available | From $17.99/user/month (billed annually) | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Data Loss Prevention Software Reviews
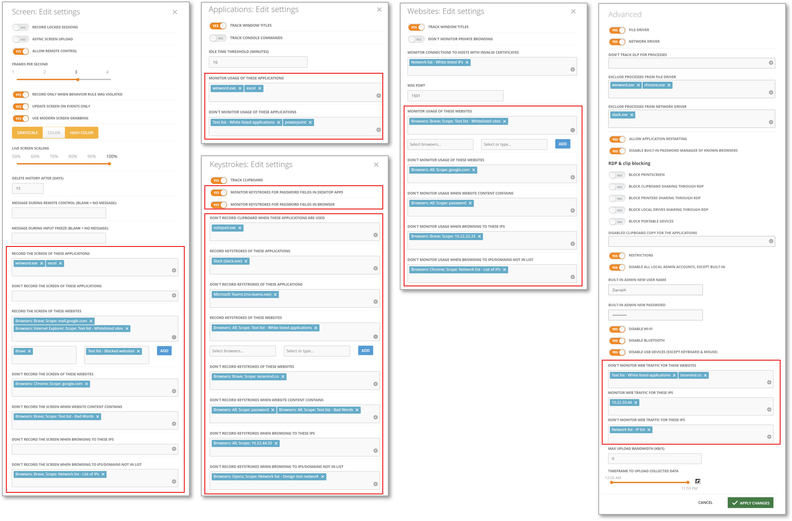
Teramind lands on my shortlist because of how well it covers insider threat detection in real time. I suggest it when you need to monitor risky user behaviors that slip past traditional DLP controls.
What I like is its strong user activity monitoring and automated risk scoring. In practice, teams can pinpoint unusual actions—like mass file movement or unauthorized access—before data actually leaves the environment.
Teramind’s Best For
- Security teams monitoring insider threats and risky users
- Organizations needing granular user activity tracking
Teramind’s Not Great For
- Companies wanting lightweight, hands-off DLP solutions
- Teams focused solely on automated data classification
What Sets Teramind Apart
Teramind focuses on close monitoring of user behavior, treating every action—like file transfers and application usage—as a potential risk indicator you need to track. Unlike most DLP tools that center on content scanning or data tagging, Teramind assumes your biggest threats move through people inside your network. In practice, this works well when you care more about activity patterns than just blocking known data types.
Tradeoffs with Teramind
Teramind optimizes for hands-on monitoring and behavioral data, but this brings more setup, ongoing analysis, and noise. If you want automated DLP with minimal tuning, this approach is a heavier lift.
Pros and Cons
Pros:
- Blocks data leaks proactively, not just detect after
- Granular risk scoring helps reduce false positives
- Catches insider threats missed by rule-only systems
Cons:
- Requires endpoint agent installation on every device
- No database fingerprinting of structured data
New Product Updates from Teramind
Teramind Enhances Tracking Flexibility, Mac Parity, and Security Controls
Teramind introduces flexible monitoring configuration, expanded Mac agent capabilities, and stronger security and data protection controls. These updates give organizations more precise tracking, improved cross-platform monitoring, and tighter privacy-focused security. For more information, visit Teramind’s official site.
Proofpoint Enterprise Data Loss Prevention earns a spot because it consistently catches threats other tools miss, especially across email, cloud, and endpoint channels. I've seen it pinpoint exfiltration attempts and insider risk by combining behavioral analytics and content inspection in one workflow.
What sets it apart for me is the threat correlation engine. You get actionable alerts and a response workflow that covers everything from real-time blocking to incident review in a single dashboard.
Proofpoint DLP’s Best For
- Large enterprises needing threat protection across email, cloud, and endpoints
- Security teams focused on insider and exfiltration risks
Proofpoint DLP’s Not Great For
- Small businesses with minimal IT security resources
- Organizations wanting lightweight or basic DLP solutions
What sets Proofpoint DLP apart
Proofpoint DLP puts threat detection at the center, focusing on behavioral signals before digging into content and policies. Unlike traditional DLP tools that flag based mostly on keywords or patterns, Proofpoint leans into context and real-time activity—flagging risky behavior across email and cloud first. I see this work best in organizations with a mix of insider and external threat concerns, where you want to connect early warning signs with data movement.
Tradeoffs with Proofpoint DLP
By optimizing for advanced detection, Proofpoint adds complexity and a steeper learning curve. For teams wanting something simpler or lighter-touch, that extra depth can translate into more work up front and slower onboarding.
Pros and Cons
Pros:
- Provides comprehensive visibility into data security.
- Integrates with other Proofpoint solutions.
- Exceptional threat detection and response capabilities.
Cons:
- May be complex for small businesses to deploy and manage.
- Extra costs may apply for advanced features.
- Higher starting price compared to other DLP solutions.
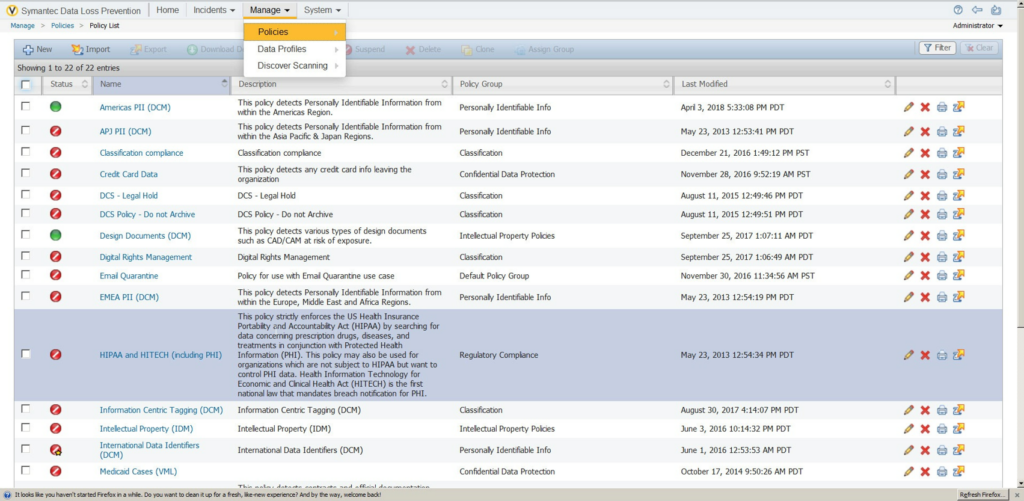
Symantec Data Loss Prevention is on my list because it handles some of the largest, most complex data protection needs I’ve come across. When I’m working with enterprises where confidential data moves across cloud, endpoint, and on-prem systems, Symantec’s unified policy management and automated data discovery really stand out.
What I like most is how you can customize policies to address regional compliance, insider threats, and third-party risk at scale.
Symantec DLP’s Best For
- Large enterprises with diverse and complex data environments
- Organizations needing granular control over sensitive data movement
Symantec DLP’s Not Great For
- Small businesses with simple data protection needs
- Teams looking for fast, lightweight deployments
What sets Symantec DLP apart
Symantec DLP is designed for organizations that need to govern sensitive data moving between endpoints, cloud, and on-prem systems, all under one roof. Unlike simpler tools like Microsoft Purview, which fit smaller or mostly Microsoft-based environments, Symantec expects you to centralize policies and reporting for highly diverse infrastructure.
In practice, this works well for security teams that need to coordinate risk controls across global operations, regulatory obligations, and mixed platforms.
Tradeoffs with Symantec DLP
Symantec DLP optimizes for control over scale and complexity, but onboarding and tuning it takes time and specialized skill. Smaller teams end up with more maintenance than they want.
Pros and Cons
Pros:
- Integrates deeply with other Symantec products.
- Offers unified policy management.
- Can handle large-scale enterprise requirements.
Cons:
- Setup and management could be time-consuming.
- It might be too complex for smaller organizations.
- Pricing information is not readily available.
Best for holistic data protection across hybrid cloud environments
IBM Data Security’s Best For
- Enterprises with complex hybrid or multi-cloud data environments
- Security teams needing centralized policy and compliance automation
IBM Data Security’s Not Great For
- Small organizations with simple, on-premise data storage
- Teams needing lightweight, plug-and-play DLP tools
What Sets IBM Data Security Apart
IBM Data Security stands out by prioritizing unified policy enforcement and monitoring across cloud and on-prem data sources. Instead of layering DLP tools for each environment, you set policies once and apply them everywhere.
This works best for organizations juggling sensitive data in both public cloud and local data centers. Compared to something like Symantec DLP, which often assumes more standardized infrastructure, IBM focuses on cross-environment consistency.
Tradeoffs with IBM Data Security
It optimizes for broad, centralized control, but that can mean slower rollouts and extra configuration when you only need basic, targeted DLP protection for a single system.
Pros and Cons
Pros:
- Wide range of compatible integrations.
- Offers a unified platform for all data security needs.
- Comprehensive solution for data protection in hybrid cloud environments.
Cons:
- Potential learning curve due to its wide array of features.
- It may be too complex for small businesses.
- Pricing information is not readily available.
Imperva’s Best For
- Regulated industries with complex database compliance needs
- Security teams needing real-time monitoring of sensitive data
Imperva’s Not Great For
- Organizations focused on endpoint-based data loss prevention
- Teams with small-scale or file storage-only environments
What sets Imperva apart
Imperva is designed around the idea that database security needs to be granular, continuous, and independent of where your data lives. Unlike traditional DLP solutions that focus on endpoints or network traffic, Imperva assumes your most valuable data lives inside databases and cloud stores—and that’s where it monitors and enforces controls.
I could see how this works well when you need tight policies for regulated workloads or database environments. It takes the view that data-centric controls should drive your security approach, not just network perimeters or endpoints.
Tradeoffs with Imperva
Imperva optimizes for database and cloud data protection, but that focus means you lose full visibility into file and endpoint risks. Teams with data spread across many systems may need another DLP tool for broader coverage.
Pros and Cons
Pros:
- Integrates with other security tools for comprehensive protection.
- Helps in achieving compliance with regulatory standards.
- Strong focus on database security.
Cons:
- Depending on the size of the database, system performance may be affected.
- Customization options may be complex for beginners.
- Pricing might be high for small businesses.
Forcepoint Data Loss Prevention earns its place on my list for its advanced machine learning approach to data loss risks. I’ve seen how the tool identifies nuanced patterns in user behavior that many traditional rules-based systems miss. I like the precision of its automated policy enforcement, especially in complex and heavily regulated environments.
This is a go-to when your team deals with large volumes of sensitive data and you need deeper, contextual insight to stop leaks before they happen.
Forcepoint DLP's Best For
- Enterprises with complex data flows and strict compliance needs
- Security teams demanding contextual, ML-driven data protection
Forcepoint DLP's Not Great For
- Small organizations needing simple, out-of-the-box DLP
- Teams without resources for ongoing tuning and management
What sets Forcepoint DLP apart
Forcepoint DLP is built for organizations that need more than simple content rules. In practice, it expects you to set up policies that consider user context and behavior, not just file types or keywords. Unlike tools such as Symantec DLP, which rely heavily on static patterns, Forcepoint pushes you toward risk-adaptive workflows that change based on what users actually do over time.
You end up working with alerts and controls that adapt to your environment—not just block the same violations over and over.
Tradeoffs with Forcepoint DLP
By focusing on risk-adaptive protection, Forcepoint adds more setup and calibration work upfront, so you give up the easy onboarding you’d get with a basic DLP tool.
Pros and Cons
Pros:
- Provides integrations with other Forcepoint solutions.
- Offers a comprehensive suite of features.
- Utilizes advanced machine learning for protection.
Cons:
- Machine learning models may require time for optimal calibration.
- It might be overly complex for smaller businesses.
- Pricing is not transparent and requires direct contact.
Egress Data Loss Prevention makes my shortlist for the way it applies contextual awareness to email data security. What stands out is how it analyzes message content and recipient context in real time, flagging or blocking risky data events before they happen.
I like how teams can set policy so sensitive information gets handled differently based on content, recipient, or user action—especially in financial or legal settings where context matters most.
Egress’s Best For
- Organizations sending confidential data by email
- Teams needing policy-driven, context-aware data controls
Egress’s Not Great For
- Companies looking for non-email DLP coverage
- Small businesses with straightforward, low-volume email needs
What sets Egress apart
Egress stands out by building email security around context, not just basic content detection. Instead of tagging keywords or blocking attachments like some DLP tools, it analyzes both the message and its recipients before taking action. For organizations where sensitive details might change meaning depending on who sends it, or where mistakes with outbound data are common, this tool is a solid choice.
Tradeoffs with Egress
Egress optimizes for nuanced, policy-driven controls on email, but that comes at the cost of limited coverage for non-email channels. If you need to monitor data in cloud drives or chat, you’ll need a second tool.
Pros and Cons
Pros:
- Utilizes advanced machine learning for threat detection.
- Integrates well with Microsoft 365 and Google Workspace.
- Offers context-aware data security.
Cons:
- The setup might require a learning curve.
- It may be overwhelming for small businesses.
- Advanced features might result in extra costs.
Trellix Data Loss Prevention lands on my list for how it unifies endpoint and network security into a coordinated system. I’ve worked with teams who want to catch both accidental data leaks and serious insider threats without jumping between separate tools, and this fits that use case well.
What I like is the way Trellix combines real-time content inspection with automated policy enforcement across devices and network layers. You can define and apply consistent controls in one place, making gaps between endpoint and network less likely.
Trellix’s Best For
- Organizations needing unified endpoint and network data protection
- Teams with strict regulatory or insider threat monitoring needs
Trellix’s Not Great For
- Small businesses without dedicated security staff
- Teams wanting lightweight or plug-and-play DLP solutions
What sets Trellix apart
Trellix takes a coordinated approach by managing data loss prevention at both endpoints and the network. This is different from tools like Symantec DLP, which often keep those layers siloed. In practice, I see Trellix expecting you to design policies that track sensitive data moving across your whole environment, including endpoints, network traffic, and cloud channels.
This works well if you want consistent controls and unified incident response, but you do need to plan for policy alignment across multiple surfaces.
Tradeoffs with Trellix
Trellix optimizes for deep policy control across endpoints and networks, but that complexity slows down deployment and requires ongoing admin effort. If you want something quick to set up with minimal tuning, this isn’t a good fit.
Pros and Cons
Pros:
- Easy integration with other security and IT platforms.
- Real-time visibility into data movement.
- Provides both endpoint and network security.
Cons:
- The interface may require help to navigate for beginners.
- Requires time for setup and policy configuration.
- It might be pricey for smaller businesses.
Nightfall DLP makes the cut for how thoroughly it addresses cloud-native data protection. When I tested its automated detection, content inspection works right inside tools like Google Drive, Slack, and Jira, flagging sensitive data with minimal setup.
What I appreciate here is the prebuilt detection pack for common data types. It’s a smart way to handle data loss risk without manual tuning, especially as your team scales cloud adoption.
Nightfall DLP's Best For
- Security teams protecting sensitive data in cloud apps
- Organizations needing automated compliance and data classification
Nightfall DLP's Not Great For
- Companies with mostly on-prem or legacy infrastructure
- Small teams that need basic endpoint DLP only
What sets Nightfall DLP apart
Nightfall DLP stands out because it’s built with cloud platforms like Google Workspace, Slack, and Jira in mind, not as an afterthought. While legacy DLP tools lean on endpoint or network controls, Nightfall expects you to work across SaaS apps and APIs directly. In practice, this is a good fit when you need continuous scanning inside the tools your teams already use.
Tradeoffs with Nightfall DLP
Nightfall optimizes for cloud-first environments, but you lose direct support for controlling on-prem data channels, which makes it less helpful if your data still lives mainly on local endpoints or file servers.
Pros and Cons
Pros:
- Extensive cloud platform integrations.
- Machine learning-enhanced detection.
- Excellent cloud-native environment protection.
Cons:
- The user interface may take time to master.
- Some advanced features might come with extra costs.
- It might be over-specialized for non-cloud-native businesses.
Best for USB and peripheral device control
Endpoint Protector Data Loss Prevention (DLP) Software stays top of mind for me when strict control over USBs and peripheral ports is a must. It’s the first tool I think of when organizations need to block, monitor, or allow specific devices across hundreds of endpoints.
Device control works well right out of the box. I appreciate being able to enforce granular policies by user, computer, or group—especially in environments with sensitive data and lots of laptops moving between locations.
Endpoint Protector’s Best For
- Companies needing strict USB and device access control
- Organizations with remote endpoints handling sensitive data
Endpoint Protector’s Not Great For
- Teams focused mainly on email or cloud data loss
- Businesses seeking lightweight or minimal endpoint monitoring
What sets Endpoint Protector apart
Endpoint Protector carves out a space by centering device control right at the endpoint, not just in the cloud or at the network perimeter. Unlike Data Loss Prevention tools like Microsoft Purview, which focus on data moving through cloud platforms, this tool puts the spotlight on physical ports and peripheral access.
In practice, this works well when you need strict oversight over USBs, printers, or storage devices in mixed or highly mobile environments.
Tradeoffs with Endpoint Protector
It optimizes for controlling physical access points, but you lose broad coverage on things like cloud data exfiltration. If your real concern is SaaS or email-based leaks, you’ll have to pair it with another solution.
Pros and Cons
Pros:
- Compatible with Windows, Linux, and Mac.
- Content-aware protection enhances data security.
- Excellent control over USB and peripheral devices.
Cons:
- It could be complex to configure for first-time users.
- Additional costs for more advanced features.
- Higher starting price compared to some competitors.
Other Data Loss Prevention Software
Below is a list of additional data loss prevention software that I shortlisted but did not make it to the top 10. Definitely worth checking them out.
- Safetica ONE
For data leak prevention via behavioral analysis
- 2B Advice PrIME
For privacy and compliance management
- GTT DLP
For comprehensive data visibility
- LastPass
Good for password management in businesses of all sizes
- NordLayer
Good for advanced network security with threat prevention
- Varonis Data Security Platform
Good for extensive data security and threat detection
- Spirion
Good for businesses needing precise personal data discovery and protection
- Tessian
Good for preventing data loss through emails and human interactions
- Cove
Good for reliable data backup and recovery solutions
- GTB Data Loss Prevention
Good for comprehensive data loss protection across various platforms
- Clearswift Data Loss Prevention
Good for adaptable and dynamic data loss prevention
- Digital Guardian DLP
Good for businesses requiring context-aware data loss prevention
- Teramind DLP
Good for user-focused data loss prevention and user behavior analytics
- Fidelis Network
Good for organizations looking for network traffic analysis and data leakage prevention
- Laminar
Good for businesses seeking automated threat detection and response
- Cyberhaven
Good for organizations needing behavioral data loss prevention
Related Reviews
Data Loss Prevention Software Selection Criteria
When selecting the best data loss prevention software to include in this list, I considered common buyer needs and pain points like data security and compliance with regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Protect sensitive data
- Monitor data access
- Control data transfer
- Enforce compliance policies
- Detect data breaches
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat detection
- Advanced analytics
- Customizable alerts
- Integration with cloud services
- Machine learning capabilities
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Easy navigation
- Customizable dashboards
- Minimal learning curve
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive documentation
- Templates for quick setup
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple contact channels
- Response time
- Knowledgeable staff
- Access to a community forum
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Feature set relative to cost
- Discounts for longer commitments
- Cost of add-ons
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction scores
- Frequency of updates
- Ease of implementation
- Support responsiveness
- User feedback on features
How to Choose Data Loss Prevention Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your business? Consider user limits, data capacity, and how easy it is to upgrade or expand features as your needs evolve. |
| Integrations | Does it work with your existing tools? Check compatibility with your current systems and any future tech you plan to implement. |
| Customizability | Can you tailor it to your processes? Look for options to adjust settings, workflows, and reports to fit your team's specific needs. |
| Ease of use | Is the interface user-friendly? Ensure your team can navigate the software without extensive training. Test for intuitive design and functionality. |
| Implementation and onboarding | How quick is setup? Assess the time and resources needed to get started, including training materials and support during the initial phase. |
| Cost | Does it fit your budget? Compare pricing models, such as subscription vs. one-time fees, and consider any hidden costs like add-ons or updates. |
| Security safeguards | How does it protect your data? Evaluate encryption standards, data backup options, and access controls to ensure robust security measures. |
| Compliance requirements | Does it meet industry standards? Verify if the software complies with regulations relevant to your sector, like GDPR or HIPAA. |
What Is Data Loss Prevention Software?
Data loss prevention software is a tool designed to protect sensitive data from being lost, stolen, or accessed by unauthorized users. IT professionals, compliance officers, and data security teams generally use these tools to safeguard information and ensure regulatory compliance.
Monitoring, data encryption, and access control features help with preventing data breaches and maintaining data integrity. When incidents do occur, digital forensics software can help investigate and analyze the breach. Overall, these tools provide peace of mind by securing valuable information and supporting compliance efforts.
Features
When selecting data loss prevention software, keep an eye out for the following key features:
- Data monitoring: Tracks data movement and access to identify unusual activities and prevent unauthorized access.
- Encryption: Protects sensitive information by converting it into unreadable code, ensuring data security even if accessed.
- Access control: Limits who can view or edit data, reducing the risk of internal and external breaches.
- Compliance management: Helps ensure adherence to industry regulations like GDPR or HIPAA, avoiding costly fines and penalties.
- Real-time alerts: Notifies users immediately of potential data breaches or policy violations, allowing for quick response.
- Integration capabilities: Works seamlessly with existing systems and software, enhancing overall security infrastructure.
- Data classification: Categorizes data based on sensitivity, helping prioritize protection efforts effectively.
- Customizable policies: Allows tailoring of security measures to fit specific organizational needs and workflows.
- Audit trails: Provides detailed logs of data access and changes, aiding in forensic analysis and accountability.
- User training support: Offers resources and tools to educate employees on data protection practices, reducing human error.
Benefits
Implementing data loss prevention software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Protects sensitive information with encryption and access controls, reducing the risk of data breaches.
- Regulatory compliance: Helps your organization meet industry standards like GDPR or HIPAA, avoiding costly fines and penalties.
- Real-time response: Sends instant alerts for suspicious activities, allowing your team to act quickly and mitigate potential threats.
- Data visibility: Provides insights into data movement and access, helping you monitor and manage information effectively.
- Cost savings: Prevents data breaches and associated costs by maintaining data integrity and protecting against unauthorized access.
- Tailored protection: Offers customizable policies to fit your specific business needs, ensuring targeted and efficient data security measures.
- User accountability: Tracks data access and changes with audit trails, fostering a culture of responsibility and transparency within your team.
Costs & Pricing
Selecting data loss prevention software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in data loss prevention software solutions:
Plan Comparison Table for Data Loss Prevention Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited data protection, and basic reporting. |
| Personal Plan | $5-$25/user/month | Enhanced encryption, access controls, and standard compliance tools. |
| Business Plan | $30-$75/user/month | Advanced analytics, customizable policies, and integration capabilities. |
| Enterprise Plan | $100-$200/user/month | Real-time alerts, comprehensive audit trails, and dedicated support. |
Most Asked Questions Regarding Data Loss Prevention Software (FAQs)
How do DLP policies work?
DLP policies define rules and actions to protect data from unauthorized access or leaks. They monitor data activity, detect violations, and apply corrective measures like blocking or alerting. These policies are essential for maintaining data security and preventing breaches.
What are the four types of DLP?
The four main types of DLP are network, endpoint, cloud, and application. Network DLP monitors data in transit, endpoint DLP secures data on devices, cloud DLP protects cloud-stored data, and application DLP focuses on securing data within specific applications.
How do you implement DLP software?
Implementing DLP software involves assessing your data protection needs, selecting a suitable solution, and configuring policies to address vulnerabilities. Train your team on usage and monitor the system regularly to ensure it effectively protects sensitive information.
What are DLP guidelines?
DLP guidelines help you identify, monitor, and protect sensitive data at rest, in motion, and in use. They dictate how data is handled across various locations and transmission methods. Implementing these guidelines ensures that sensitive information remains secure and compliant with regulations.
What’s Next:
If you're in the process of researching data loss prevention software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.