10 Best Container Security Solutions Shortlist
Managing container security can feel overwhelming. You're juggling compliance, data protection, and the ever-present threat of breaches. It's not easy, and I get it. That's why I've tested and reviewed the best container security solutions for you.
In my experience, the right tool can make a significant difference. These solutions help protect your infrastructure and give you peace of mind. I'll walk you through my top picks, focusing on their unique benefits and how they can fit your team's needs.
Expect a detailed, unbiased review that cuts through the noise. Let's find the tool that best addresses your challenges and supports your development goals.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Container Security Solutions Summary
This comparison chart summarizes pricing details for my top container security solutions selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for auto-fixing container vulnerabilities | Free plan available + free demo | From $350/month | Website | |
| 2 | Best for application-centric container security | Free demo + 15-day free trial available | From $7/host/month | Website | |
| 3 | Best for container vulnerability management | Free plan + free demo available | From $25/contributing developer/month | Website | |
| 4 | Best for secure container registry | Not available | Pricing upon request | Website | |
| 5 | Best for full-stack container risk assessment | Free demo available | Pricing upon request | Website | |
| 6 | Best for comprehensive cloud-native security | Free demo available | Pricing upon request | Website | |
| 7 | Best for full lifecycle container protection | Not available | Pricing upon request. | Website | |
| 8 | Best for vulnerability and compliance scanning | Not available | Pricing upon request. | Website | |
| 9 | Best for runtime protection of your container environment | Not available | Pricing upon request. | Website | |
| 10 | Best for container visibility and forensics | Not available | Pricing upon request. | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Container Security Solution Reviews
Below are my detailed summaries of the best container security solutions that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Aikido Security is a comprehensive application security platform that covers the entire spectrum from code to cloud, featuring tools for vulnerability management, secrets detection, and compliance monitoring.
Why I Picked Aikido Security: The platform's container image scanning capability identifies vulnerabilities, outdated packages, and license risks. It scans for open-source vulnerabilities and intelligently prioritizes findings based on the sensitivity of the data managed by the container. This prioritization allows you to focus on the most critical threats first, ensuring that resources are allocated efficiently to mitigate risks.
The platform also employs instant deduplication to consolidate reported vulnerabilities and utilizes auto-ignore rules for fast triaging, allowing you to customize severity scores based on specific contexts.
Standout Features & Integrations:
Other standout features include its secrets detection capability, which is crucial for safeguarding sensitive information by identifying exposed API keys and passwords, therefore preventing unauthorized access. It also offers cloud posture management (CSPM), dynamic application security testing (DAST), open-source dependency scanning, static code analysis, surface monitoring, and firewall capabilities.
Integrations include Amazon Web Services (AWS), Google Cloud, Microsoft Azure Cloud, Drata, Vanta, AWS Elastic Container Registry, Docker Hub, Jira, Asana, and GitHub.
Pros and Cons
Pros:
- Code-to-cloud security
- Has a comprehensive dashboard and customizable reports
- Scalable for growing teams
Cons:
- Ignores vulnerabilities if no fix is available
- No endpoint security or intrusion detection capabilities
New Product Updates from Aikido Security
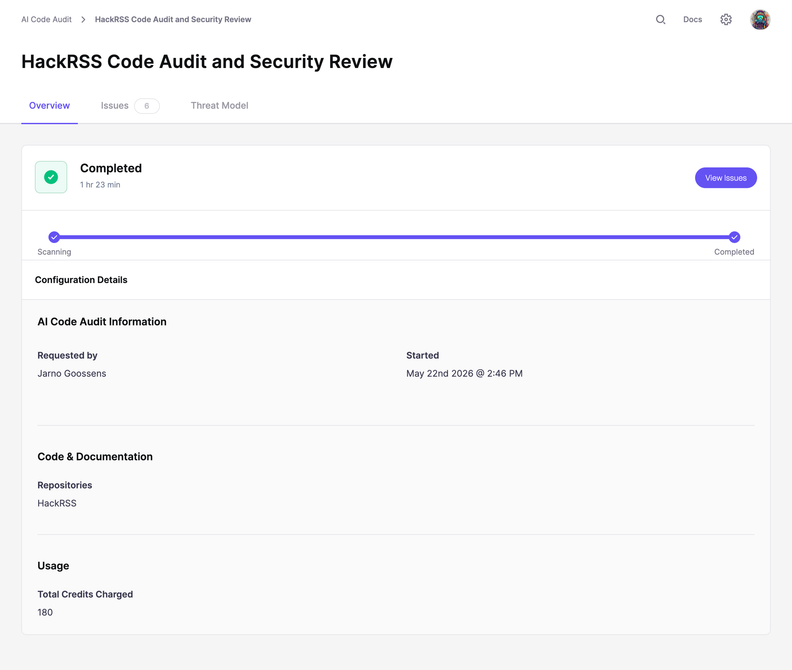
Aikido Security Adds Code Audit for Source Code Analysis
Aikido Security introduces Code Audit, bringing pentest-grade security reasoning directly to your source code to uncover logic flaws and vulnerabilities missed by pattern scanners. For more information, visit Aikido Security's official site.
Dynatrace offers robust monitoring solutions that deliver insights into every aspect of the application lifecycle. Given the rise in containerized application deployments, Dynatrace's focus on application-centric security becomes ever more crucial, ensuring that applications within containers remain free of vulnerabilities and threats.
Why I Picked Dynatrace: After comparing several tools, Dynatrace emerged as a top contender due to its unique application-centric approach to container security. While many tools provide container security, Dynatrace pivots this notion by ensuring the applications within these containers are secure.
This differentiation was significant in my judgment, and it's the reason why I determined Dynatrace to be the "best for application-centric container security."
Standout Features & Integrations:
One of Dynatrace's standout features is its full-stack monitoring, which covers applications, containers, infrastructure, and cloud. The AI-powered, automatic, and dynamic baselining helps in proactive anomaly detection. Furthermore, Dynatrace offers real-user monitoring to track and improve user experiences.
When it comes to integrations, Dynatrace offers compatibility with numerous platforms, from cloud providers to CI/CD tools. Its integrations with AWS, Azure, Kubernetes, and Jenkins, among others, enable monitoring and security across various deployment scenarios.
Pros and Cons
Pros:
- Broad integration range supports various deployment infrastructures
- AI-powered anomaly detection streamlines threat identification
- Comprehensive full-stack monitoring from infrastructure to applications
Cons:
- While integrations are vast, there might be gaps in some niche technologies or platforms
- Customization may require advanced expertise
- The depth of features might be overwhelming for some users
Snyk stands as a formidable security tool that empowers developers to find and fix vulnerabilities in containers, applications, and open-source libraries. Its expertise in scanning and rectifying container-based vulnerabilities makes it deserving of the title "Best for container vulnerability management."
Why I Picked Snyk: In the process of determining the most suitable tools for this list, Snyk was hard to overlook due to its in-depth vulnerability scanning capabilities tailored for containers. The clarity and specificity of its container-focused vulnerability alerts made it stand apart from others.
Given the rising prominence of containerized applications, I believe Snyk rightly fits the bill as "best for container vulnerability management."
Standout Features & Integrations:
Snyk not only identifies vulnerabilities but also automates the fixing process, enabling faster resolution. It provides detailed insights into the vulnerability's origin, helping developers trace the issue back to its source.
As for integrations, Snyk easily connects with various CI/CD platforms, source control systems, and container orchestration tools. Its broad spectrum of integrations ensures that developers can incorporate it into their existing workflows with minimal disruption.
Pros and Cons
Pros:
- Broad range of integrations with popular development tools and platforms
- Detailed insights into vulnerability origins
- Comprehensive container vulnerability scanning and auto-fixing
Cons:
- Reliance on integrations can lead to potential compatibility issues
- Lack of transparent pricing information
- Might come off as overwhelming for smaller teams or projects
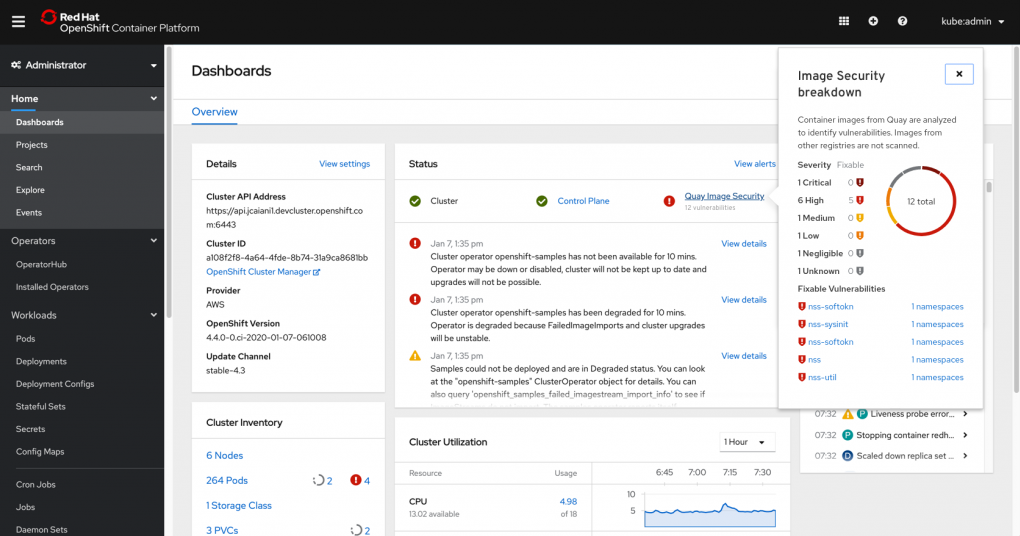
Red Hat Quay is a trusted solution known for its secure container registry capabilities. As businesses increasingly depend on containerized applications, having a dependable registry with a focus on security is paramount, which is where Quay shines.
Why I Picked Red Hat Quay: Selecting the right tools for this list involved rigorous comparison and judgment. Red Hat Quay stood out for its commitment to security, especially when it comes to container registry. Its integrated security features are a testament to its dedication to ensuring containers remain uncompromised.
I'm of the opinion that when it comes to a secure container registry, Red Hat Quay clearly fits the description, making it the "best for secure container registry."
Standout Features & Integrations:
Red Hat Quay boasts a slew of advanced security features, including automated vulnerability scanning and robot accounts for automated processes. Its geo-replication feature ensures that containers are available and deployable across different regions.
In terms of integrations, Red Hat Quay supports various container runtime environments and orchestration platforms. Its compatibility with Kubernetes and OpenShift, among others, makes it a versatile choice for diverse infrastructure setups.
Pros and Cons
Pros:
- Extensive integration capabilities with major container orchestration tools
- Geo-replication aids in ensuring the global availability of containers
- Automated vulnerability scanning provides an added layer of security
Cons:
- Reliance on Red Hat infrastructure could lead to vendor lock-in concerns
- Some features might require a steeper learning curve for new users
- Absence of transparent pricing might deter potential users
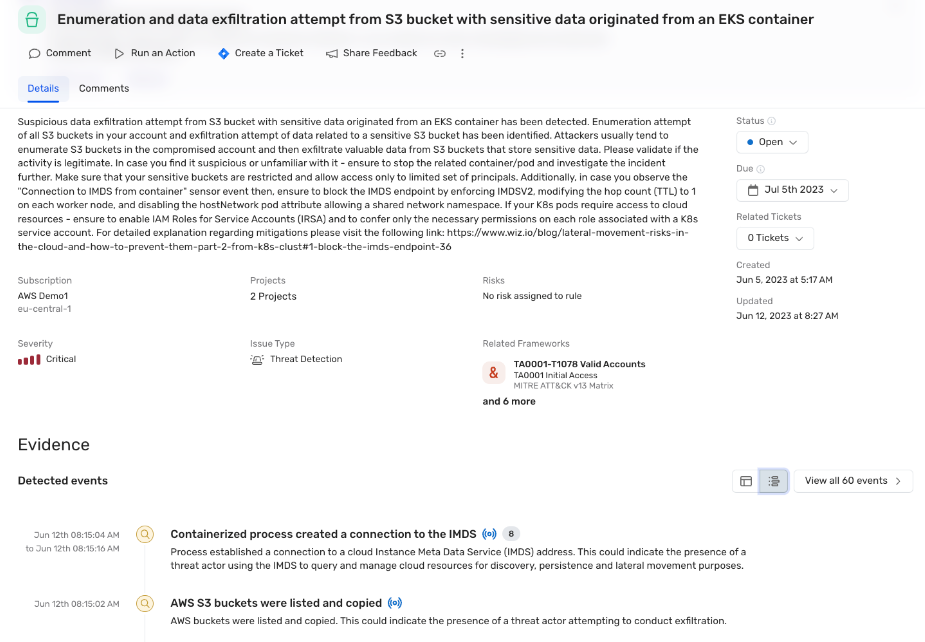
Wiz is a security solution that offers a comprehensive assessment of container risks across an entire tech stack. Through its advanced analysis, it provides organizations with a deeper understanding of their container vulnerabilities and potential threats, justifying its recognition as the 'best for full-stack container risk assessment.'
Why I Picked Wiz: When selecting tools for the list, Wiz stood out due to its robust approach to full-stack container security. What sets it apart is its ability to analyze vulnerabilities in depth across all layers of a tech stack, from the application to the infrastructure. After comparing and judging various tools, I determined that Wiz indeed stands out as the "best for full-stack container risk assessment."
Standout Features & Integrations:
Wiz is known for its in-depth risk assessment that spans the entirety of an organization's tech stack, ensuring no stone is left unturned. The tool offers actionable insights that are prioritized based on risk severity, ensuring teams can address the most pressing vulnerabilities first.
Integration-wise, Wiz supports a broad range of cloud platforms, including AWS, Azure, GCP, and more. It also pairs with various CI/CD tools, ensuring security checks can be an integral part of the development process.
Pros and Cons
Pros:
- Extensive integration support with major cloud platforms and CI/CD tools
- Prioritized risk findings ensure that teams tackle the most critical threats first
- Comprehensive full-stack analysis covers all aspects of container vulnerabilities
Cons:
- As it's specialized in full-stack risk assessment, it might be overkill for teams looking for more basic security checks
- Requires a more strategic setup and understanding of the tech stack to fully utilize its potential
- The breadth of the tool might be overwhelming for smaller teams or simpler setups
Prisma Cloud by Palo Alto Networks offers a holistic approach to securing cloud-native applications and infrastructure. It provides an extensive suite of security capabilities that encompass various stages of the application lifecycle, from development to runtime. The tool's comprehensive nature makes it particularly apt for businesses keen on end-to-end cloud security.
Why I Picked Prisma Cloud: After assessing a variety of tools, I determined that Prisma Cloud uniquely addressed a range of cloud-native security challenges. Many solutions in the market focus on individual aspects, but Prisma Cloud stood out because of its ability to provide a comprehensive set of security features.
In my judgment, it is indeed the top choice for those seeking thorough cloud-native security, which is why I believe it's "Best for comprehensive cloud-native security."
Standout Features & Integrations:
Among its wide array of features, Prisma Cloud offers robust threat intelligence, compliance assurance, and vulnerability management. Furthermore, its dynamic policy engine enables users to create custom security protocols, tailoring protection to specific organizational needs.
In terms of integrations, Prisma Cloud offers support for a broad range of platforms and services, including AWS, Azure, GCP, Kubernetes, and more. These integrations ensure that businesses can deploy and manage Prisma Cloud across diverse cloud environments with ease.
Pros and Cons
Pros:
- Wide-ranging platform and service integrations
- Ability to tailor security protocols with a dynamic policy engine
- Provides an end-to-end cloud-native security solution
Cons:
- Overlapping features might not be utilized by all businesses, leading to potential over-purchasing
- Given its comprehensive nature, there might be a steeper learning curve for some users
- Lack of transparent pricing might be a deterrent for some
NeuVector offers an all-in-one security solution specifically tailored to containerized applications. Designed to protect containers from their build to their runtime, NeuVector ensures that every phase of a container's life cycle is shielded from potential threats.
Why I Picked NeuVector: I selected NeuVector due to its holistic approach to container security. While many tools focus on just one aspect of container protection, NeuVector distinguishes itself by providing robust defenses throughout the full container lifecycle. This comprehensive strategy is why I believe NeuVector is best for those seeking all-encompassing protection for their container deployments.
Standout Features & Integrations:
NeuVector boasts a set of features that enable automatic container security, deep packet inspection, and vulnerability scanning, ensuring that containers are safeguarded at every stage. The tool also provides runtime visibility, which allows users to monitor and detect any malicious behaviors or vulnerabilities actively.
In terms of integrations, NeuVector works with popular orchestration tools like Kubernetes. It also integrates well with CI/CD pipelines, ensuring that security is enforced from the very first step of the development process. Plus, its compatibility with major cloud platforms facilitates a smooth and protected container deployment across various environments.
Pros and Cons
Pros:
- Effective integration with CI/CD pipelines and cloud platforms
- Active runtime visibility and deep packet inspection
- Comprehensive protection across the full container lifecycle
Cons:
- Some features might have a learning curve for beginners
- May require a detailed setup process for optimal configuration
- Pricing details are not transparent
Qualys Container Security (CS) specializes in providing containerized applications with thorough vulnerability assessments and compliance scans. By offering these services, Qualys ensures that developers and organizations are always abreast of potential threats and are in line with industry compliance standards.
Why I Picked Qualys Container Security (CS): When determining which tools to include on this list, Qualys Container Security (CS) stood out due to its emphasis on both vulnerability and compliance scanning. It's not just about identifying threats; it's about ensuring your containerized applications meet the necessary compliance standards.
In my judgment, the dual focus on these two critical areas is what makes it unique, positioning Qualys CS as the best for those in need of robust vulnerability detection paired with comprehensive compliance checks.
Standout Features & Integrations:
Qualys Container Security offers real-time vulnerability management, which not only identifies threats but also provides detailed insights to address them. Additionally, its compliance scanning ensures that your containers meet industry-specific regulations, reducing the risk of breaches and penalties.
On the integration front, Qualys CS supports a wide range of CI/CD tools, enabling developers to embed security checks directly into their development processes. Furthermore, its compatibility with popular container platforms like Docker and Kubernetes ensures an easy and efficient security scanning experience.
Pros and Cons
Pros:
- Effective integration with CI/CD tools and major container platforms
- Comprehensive compliance scanning to meet industry standards
- Real-time vulnerability management with detailed insights
Cons:
- Specific advanced features could require additional setup
- Might have a slight learning curve for beginners
- Lack of transparent pricing details
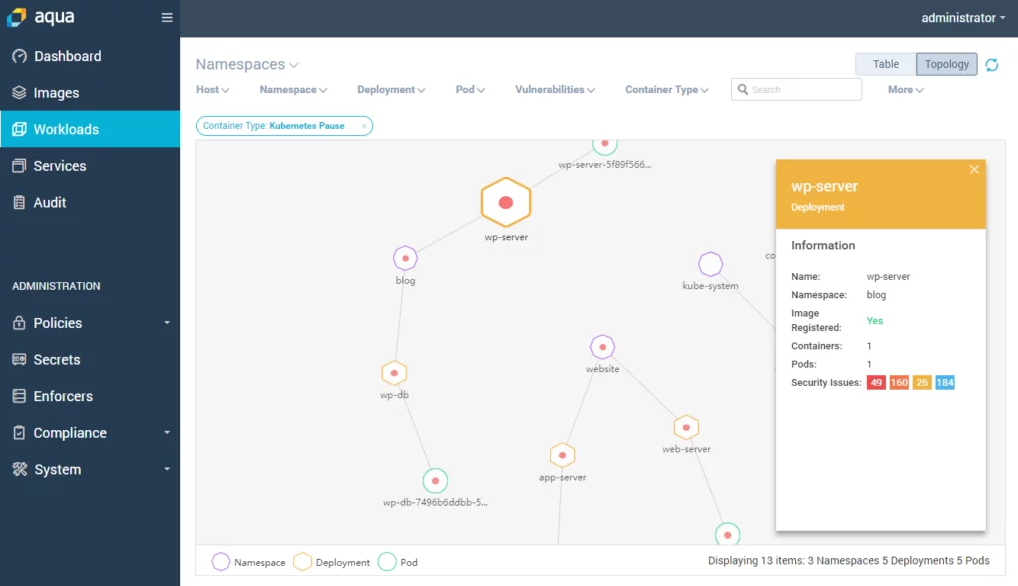
Aqua Security focuses on ensuring your containerized applications run safely in their designated environment. This platform prioritizes the security of containers while they're active, safeguarding them from potential threats during their operation, and directly addressing the need for robust runtime protection.
Why I Picked Aqua Security: As I delved into the myriad of container security solutions available, Aqua Security piqued my interest because of its concentrated attention on runtime protection. Most tools prioritize the initial setup, but once your containers are live, they're at their most vulnerable.
This is where Aqua steps in. I believe it's best for those who need a tool that offers rigorous security while their containers are in action, given its emphasis on real-time defenses.
Standout Features & Integrations:
Aqua Security brings to the table advanced runtime protection mechanisms, which monitor container activity and can detect and respond to anomalies in real-time. The tool also offers vulnerability scanning, ensuring containers are free of potential security risks before they go live.
Integration-wise, Aqua Security is compatible with a variety of container orchestration tools like Kubernetes, Docker, and OpenShift. Additionally, it supports multiple CI/CD tools, streamlining security into the development process for a cohesive defense strategy.
Pros and Cons
Pros:
- Easy integration with major orchestration and CI/CD tools
- Offers proactive vulnerability scanning for containers
- Tailored real-time runtime protection
Cons:
- Some advanced features might not be straightforward for beginners
- Initial setup might require a bit of acclimatization
- Lack of transparent pricing can be a hurdle for some users
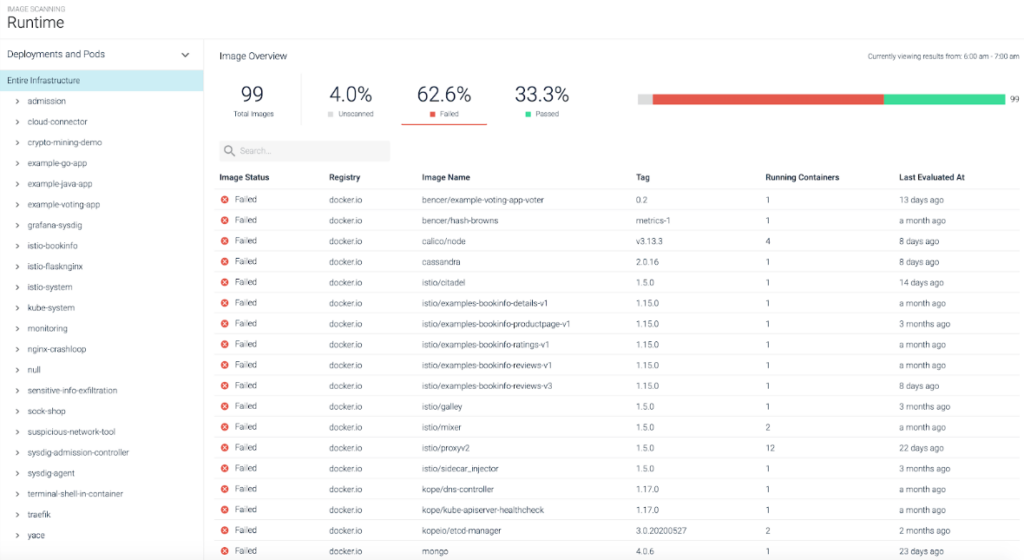
Sysdig specializes in offering a granular level of visibility into containerized environments. Its tools not only monitor but also dive deep into containers to offer forensic insights, making it an invaluable asset when the need arises to investigate incidents or ensure compliance.
Why I Picked Sysdig: When assessing the various tools on the market, Sysdig grabbed my attention with its unparalleled forensic capabilities. Many tools offer visibility, but few provide the depth and breadth of information that Sysdig does.
I judged it as the prime candidate for those prioritizing a meticulous examination of their container environments, precisely because of its superior visibility and post-incident investigation strengths.
Standout Features & Integrations:
Sysdig's standout features include detailed container monitoring, real-time security data, and comprehensive forensic capabilities, allowing users to delve deep into container activities past and present. Moreover, its adaptive alerts can notify users of any unusual patterns or potential threats within their environment.
Integration-wise, Sysdig easily interacts with popular platforms such as Kubernetes, AWS, and Docker. Its adaptability ensures that users can draw insights from a variety of sources, reinforcing their security and operational postures.
Pros and Cons
Pros:
- Robust integration options with key platforms
- Offers adaptive alerts for proactive threat management
- Unrivaled forensic and deep dive capabilities
Cons:
- Some users may experience a learning curve with advanced features
- Might be overwhelming for beginners due to its depth
- Lack of transparent pricing can deter potential users
Other Container Security Solutions
Here are some additional container security solutions options that didn’t make it onto my shortlist, but are still worth checking out:
- Cilium
For eBPF-powered networking and security
- Orca Security
For side-scanning container technology
- PingSafe
For adaptive threat defense
- Mend.io
Good for automating container security compliance
- Microsoft Defender for Cloud
Good for integrating security within Azure cloud services
- Anchore
Good for in-depth container image inspection and certification
- NetScaler
Good for container traffic management and load balancing
- Trend Micro Cloud Security
Good for hybrid cloud protection across major platforms
- Lacework
Good for comprehensive threat detection across your cloud stack
- Red Hat Advanced Cluster Security for Kubernetes
Good for Kubernetes-specific security solutions within clusters
- ARMO
Good for runtime workload protection across environments
- F5 Distributed Cloud App Infrastructure Protection (AIP)
Good for scaling and securing applications in multi-cloud environments
- Tenable Container Security Scanner
Good for vulnerability management in Docker images
Container Security Solutions Selection Criteria
When selecting the best container security solutions to include in this list, I considered common buyer needs and pain points like vulnerability management and compliance requirements. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Vulnerability scanning
- Compliance checks
- Runtime protection
- Integration with CI/CD pipelines
- Image scanning
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Machine learning-based threat detection
- Automated remediation
- Advanced policy enforcement
- Real-time alerting
- Role-based access control
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Customizable dashboards
- Easy navigation
- User-friendly design
- Minimal learning curve
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Supportive chatbots
- Informative webinars
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multi-channel support
- Fast response times
- Knowledgeable staff
- Comprehensive FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible plans
- No hidden fees
- Cost vs. features offered
- Free trial availability
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Positive feedback on functionality
- Reports on ease of use
- Satisfaction with support
- Comments on performance
- Overall recommendation rate
How to Choose a Container Security Solution
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the tool grow with your business? Consider if it handles increased workloads and users without needing constant upgrades. |
| Integrations | Does it work with your existing tools? Check for compatibility with CI/CD pipelines, cloud providers, and other essential software. |
| Customizability | Can you tailor it to your needs? Look for options to adjust settings, dashboards, and alerts to match your workflow. |
| Ease of use | Is it user-friendly? Ensure the interface is intuitive and requires minimal training for your team to get started. |
| Implementation and onboarding | How quickly can you start? Evaluate the setup time, availability of resources like training, and support during the initial stages. |
| Cost | Does it fit your budget? Compare pricing plans, watch for hidden fees, and consider the value provided for the price. |
| Security safeguards | Are there strong protections? Look for encryption, access controls, and compliance with industry standards to ensure data safety. |
| Compliance requirements | Does it meet regulations? Verify if the solution aligns with legal standards relevant to your industry, like GDPR or HIPAA. |
What Are Container Security Solutions?
Container security solutions are tools designed to protect containerized applications from vulnerabilities and threats. IT professionals, developers, and security teams generally use these tools to ensure applications run securely in various environments, whether they're using Docker alternatives or other container platforms. Vulnerability scanning, compliance checks, and runtime protection help with identifying risks, meeting regulations, and safeguarding operations. These tools provide essential security to keep your containerized applications safe and compliant.
Features
When selecting container security solutions, keep an eye out for the following key features:
- Vulnerability scanning: Identifies and alerts you to potential security risks within your container images and running applications.
- Compliance checks: Ensures that your containers meet industry standards and regulations like GDPR and HIPAA.
- Runtime protection: Monitors and defends against threats during the execution of containerized applications.
- Integration capabilities: Works seamlessly with your existing CI/CD pipelines and cloud providers to maintain security across development stages.
- Role-based access control: Allows you to set permissions and manage user access to sensitive information and actions.
- Automated remediation: Provides automatic fixes for identified vulnerabilities, reducing the need for manual intervention.
- Real-time alerting: Notifies your team immediately about security incidents, allowing for quick response.
- Customizable dashboards: Offers a tailored view of security metrics and alerts, making it easier to monitor what's important to you.
- Encryption: Ensures that data within containers is protected from unauthorized access.
- Machine learning-based threat detection: Uses advanced algorithms to identify and predict potential threats, enhancing overall security measures.
Benefits
Implementing container security solutions provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: By using vulnerability scanning and runtime protection, you reduce the risk of breaches and protect sensitive data.
- Regulatory compliance: Compliance checks ensure your operations meet necessary legal standards, avoiding fines and legal issues.
- Time savings: Automated remediation and real-time alerting allow your team to respond quickly to threats without manual effort.
- Improved efficiency: Integration capabilities with existing tools streamline processes and maintain security throughout development.
- Access control: Role-based access control helps manage who can access what, reducing the chance of unauthorized actions.
- Informed decision-making: Customizable dashboards provide insights into security metrics, helping you make better-informed security decisions.
- Data protection: Encryption ensures data is safe from unauthorized access, maintaining confidentiality and integrity.
Costs & Pricing
Selecting container security solutions requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in container security solutions:
Plan Comparison Table for Container Security Solutions
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic vulnerability scanning, limited compliance checks, and community support. |
| Personal Plan | $5-$25/user/month | Advanced scanning, basic runtime protection, and email support. |
| Business Plan | $30-$75/user/month | Full compliance checks, integration capabilities, and role-based access control. |
| Enterprise Plan | $100+/user/month | Customizable dashboards, machine learning threat detection, and dedicated support. |
Container Security Solutions FAQs
What trade-offs should you expect between open source and commercial container security tools?
With open source tools, you often get flexibility, customization, and no license fees—but you’ll usually shoulder more integration work, tuning, and support burden. Commercial solutions tend to bundle more out-of-the-box features (dashboards, alerts, policy engines), but you may be locked into vendor constraints or higher cost as you scale. You’ll want to weigh your team’s maturity, your environments’ complexity, and your willingness to build glue between tools.
What challenges arise when securing containers across multicloud or hybrid infrastructures?
In multicloud settings, you’ll face inconsistent APIs, differing identity models, and divergent network policies. A solution that works in AWS might not map cleanly to Azure or on-prem. You’ll need tooling that abstracts across these differences (or uses a central control plane) and enables security posture uniformity across clouds.
How can I resolve issues with containers exiting unexpectedly in AWS Fargate?
Unexpected container exits in AWS Fargate may be due to resource limitations or misconfigurations. Check the task definition for correct resource allocations and review logs for error messages. Adjusting memory or CPU settings might resolve the issue.
How do you manage false positives in vulnerability scans of container images?
False positives are common when scanners flag low-impact issues or dependencies your app doesn’t actually use. To reduce noise, tune your scanner thresholds, suppress alerts from low-risk findings, and correlate scan results over time to see persistent issues. You can also cross-validate findings with multiple tools or use a meta-framework (e.g. LUCID) to reduce inconsistencies across scanners.
What’s Next:
If you're in the process of researching container security solutions, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.