10 Best Threat Intelligence Solutions Shortlist
In the ever-evolving world of cybersecurity, ransomware, firewalls, and indicators of compromise (IOCs) consistently challenge organizations. I've discerned the criticality of threat intelligence solutions, whether they're on-premise or SaaS-based. Tools like eXtended Detection and Response (XDR) and Endpoint Detection and Response (EDR) not only fortify against threat actors but also streamline workflows in Security Operations Centers (SOCs). Drawing from multiple sources, these tools offer a comprehensive view of your security posture, aiding security analysts in fending off data breaches and enhancing threat management.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Threat Intelligence Solutions Summary
This comparison chart summarizes pricing details for my top threat intelligence solutions selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for intelligence on third-party risks | Free demo available | Pricing upon request | Website | |
| 2 | Best for proactive issue identification and reporting | Free demo available | Pricing upon request | Website | |
| 3 | Best for extended detection & response | Free trial + free demo available | Pricing upon request | Website | |
| 4 | Best for high-performance network security | Not available | Available upon request | Website | |
| 5 | Best for DDoS attack mitigation | Free demo available | Pricing upon request | Website | |
| 6 | Best for integrated Microsoft ecosystem protection | Not available | From $20/user/month (billed annually). | Website | |
| 7 | Best for advanced email threat prevention | Not available | From $8/user/month. | Website | |
| 8 | Best for enterprise-level threat analysis | Not available | Pricing upon request. | Website | |
| 9 | Best for cloud-native endpoint security | Not available | From $12/user/month (billed annually) | Website | |
| 10 | Best for collaborative threat sharing | Not available | Pricing upon request. | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Threat Intelligence Solutions Reviews
Below are my detailed summaries of the best threat intelligence solutions that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Prevalent is a threat intelligence and risk management platform focused on helping teams assess and monitor risks related to third-party vendors. With its vendor risk monitoring tools, Prevalent offers visibility into the security practices of your organization's external partners, reducing the unknowns that could impact your security posture.
Why I Picked Prevalent: Its threat intelligence feature reveals any third-party cyber incidents across 550,000 companies, allowing you to detect issues before they become a risk to your own organization. Prevalent achieves this by monitoring a range of data sources, from criminal forums and dark web pages to various threat feeds and code repositories, helping you spot exposed credentials or vulnerabilities within your vendors’ systems. By keeping your team aware of these threats, Prevalent enables you to act faster when a vendor’s security practices or incidents could affect your own network.
Standout features & integrations:
In addition to its cyber intelligence features, Prevalent includes automated risk assessment questionnaires, standardized risk scoring, and continuous monitoring. These features simplify the process of evaluating your vendors' security profiles without adding manual work. Integrations include Active Directory, BitSight, ServiceNow, SecZetta, and Source Defense.
Pros and Cons
Pros:
- Strong security protocols to protect data
- Users can tailor reports according to specific needs
- Extensive functionalities for managing vendor risk
Cons:
- Challenges in migrating data can complicate the initial setup
- The platform is complex and comes with a learning curve
Best for proactive issue identification and reporting
ManageEngine Log360 is a comprehensive security information and event management (SIEM) solution designed to enhance organizational security by integrating essential capabilities such as User and Entity Behavior Analytics (UEBA), Data Loss Prevention (DLP), and Cloud Access Security Broker (CASB).
Why I Picked ManageEngine Log360: The platform integrates advanced threat intelligence feeds that are regularly updated to ensure the latest threat data is available. This allows Log360 to detect and mitigate threats such as malicious IPs, domains, and URLs. The real-time monitoring and alerting system ensures that security teams are immediately notified of any suspicious activities, enabling swift action to prevent potential breaches. This proactive approach reduces the risk of data loss and enhances the overall security posture of an organization.
Standout features & integrations:
The privileged user monitoring capability ensures that activities of high-privilege accounts are closely audited to detect any unusual behavior or privilege escalations. Additionally, the integrated CASB feature enhances cloud security by providing comprehensive visibility into cloud events and ensuring compliance, while the SOAR capabilities automate incident management and response. Integrations include Microsoft Exchange, Amazon Web Services (AWS), Microsoft Entra ID, Microsoft Azure, and Active Directory.
Pros and Cons
Pros:
- Comprehensive log management capabilities
- Excellent visibility and auditing
- Customizable reporting options
Cons:
- Occasional performance issues, particularly when dealing with large volumes of data
- Initial setup can be complex and time-consuming
New Product Updates from ManageEngine Log360
ManageEngine Log360 Adds New Log Source Integrations
ManageEngine Log360 introduced new integration support for NetFlow Analyzer and Firewall Analyzer, along with enhanced audit log parsing for OpManager products. The updates help teams centralize log collection and improve monitoring and analysis workflows. For more information, visit ManageEngine Log360's official site.
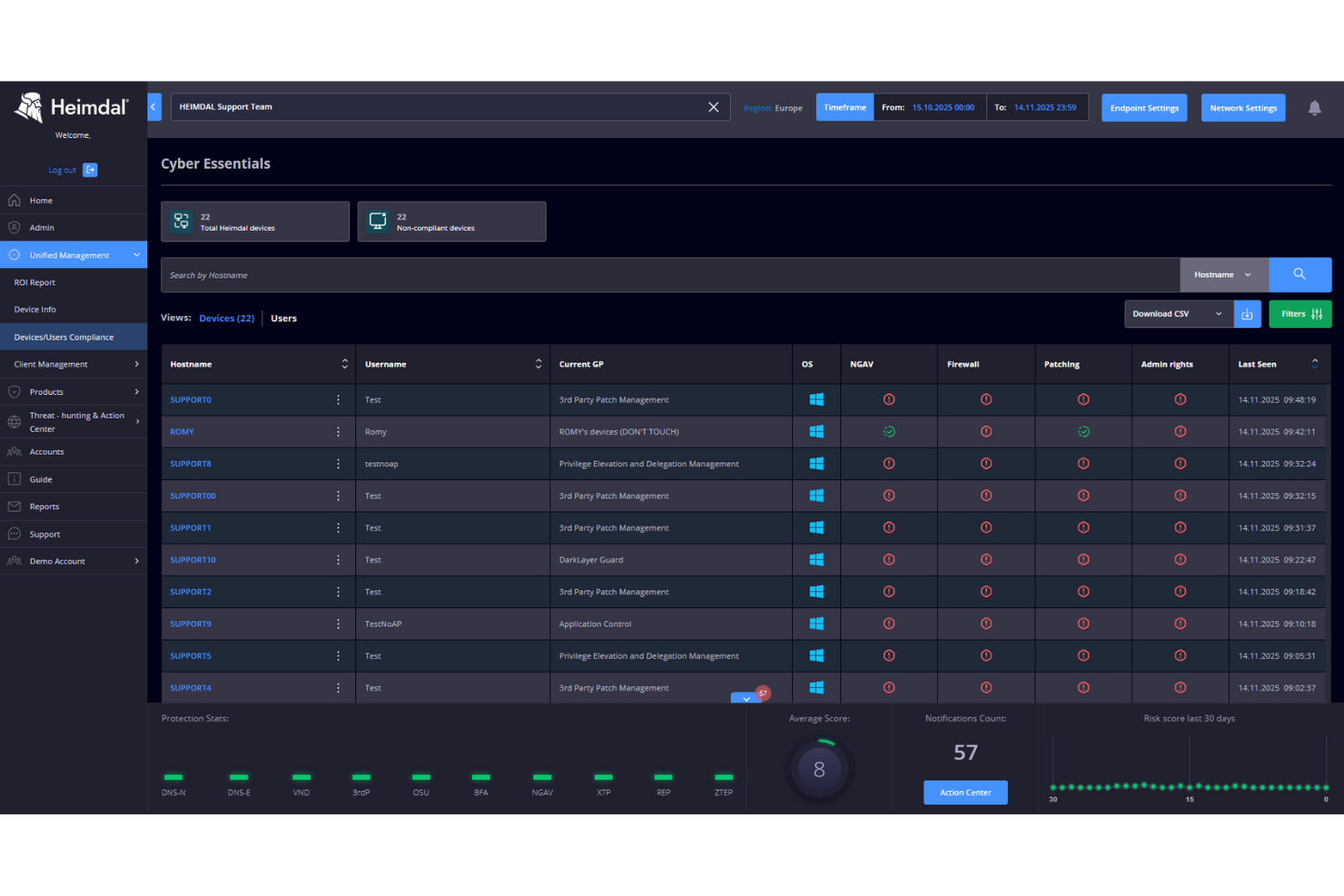
Heimdal offers a cybersecurity platform that brings together multiple threat intelligence capabilities in a single solution. It’s well-suited for enterprises, Managed Service Providers (MSPs), and Managed Security Service Providers (MSSPs). The platform is built to meet the security demands of regulated industries such as healthcare, education, and government, protecting networks, endpoints, and cloud environments. With an emphasis on advanced threat detection, real-time monitoring, and automated remediation, Heimdal helps organizations manage compliance requirements, data governance, and evolving cybersecurity threats.
Why I Picked Heimdal
I picked Heimdal for its Extended Detection & Response (XDR) capabilities, which deliver unified visibility and threat detection across networks, endpoints, and cloud environments. This approach is useful for organizations that need a clearer security picture and faster, more coordinated responses to incidents. Heimdal’s User and Entity Behaviour Analytics (UEBA) also stands out by identifying anomalies in user and system behaviour, helping teams spot unusual activity early and reduce risk quickly.
Heimdal Key Features
In addition to its XDR and UEBA capabilities, I also found:
- Threat Hunting: Proactive detection and response capabilities to identify and mitigate threats before they escalate.
- Network Security: Comprehensive DNS security that safeguards against web-based threats and data breaches.
- Vulnerability Management: Automated tools for effective patch and asset management to ensure compliance and reduce security risks.
- Managed Services: 24/7 monitoring and response from a dedicated security operations center (SOC) to ensure continuous protection.
Heimdal Integrations
Native integrations are not currently listed by Heimdal.
Pros and Cons
Pros:
- Unified platform for security management
- Strong privileged access management controls
- Automated OS and third-party patching
Cons:
- Advanced setup requires learning curve
- Reporting customization can be limited
FortiGate NGFW, developed by Fortinet, stands as a formidable line of defense for networks, offering layered protection against myriad threats. With its capacity to handle significant network traffic without compromising security, it is the optimal choice for high-performance network security.
Why I Picked FortiGate NGFW: After assessing various network security solutions, I chose FortiGate NGFW because of its remarkable balance between performance and comprehensive security. Its ability to scale without losing the granularity of its protection makes it distinct. Its proficiency in delivering security at high speeds is the prime reason it is the best for environments where performance is paramount.
Standout features & integrations:
FortiGate NGFW boasts multi-layered security capabilities, from intrusion prevention to advanced threat protection. It also incorporates machine learning for threat detection, ensuring an updated response to evolving threats. As for integrations, it meshes well with the Fortinet Security Fabric, allowing for unified insights and coordinated responses across different Fortinet solutions.
Pros and Cons
Pros:
- Integration within the broader Fortinet ecosystem
- Scalability to suit varying organizational sizes
- Multi-layered security features
Cons:
- The user interface can be complex for novices
- Priced higher than some competitors
- Might require expertise for advanced configurations
Netscout offers comprehensive tools designed to monitor and protect your network infrastructure. With a primary emphasis on DDoS attack mitigation, it equips businesses to defend themselves against disruptive and malicious online attacks.
Why I Picked Netscout: While sifting through many network protection solutions, Netscout prominently stood out. I chose it because of its proven track record in successfully fending DDoS attacks. Its unique network visibility approach and proactive defense mechanisms make it superior in DDoS attack mitigation.
Standout features & integrations:
Netscout boasts advanced traffic analysis capabilities, pinpointing abnormalities that may signify an attack. Additionally, its automated threat intelligence system ensures that defenses are always updated. Integrations are diverse, linking seamlessly with major network hardware providers, cloud platforms, and SIEM systems.
Pros and Cons
Pros:
- Seamless integration with diverse platforms
- Advanced traffic analysis tools
- Proven DDoS mitigation capabilities
Cons:
- Pricing transparency could be improved
- Initial setup requires technical know-how
- Might be overkill for smaller businesses
Best for integrated Microsoft ecosystem protection
Microsoft Defender Threat Intelligence is Microsoft's flagship security solution, expertly crafted to guard its vast ecosystem. Ensuring seamless protection across the Microsoft suite, it rightly earns its place for offering the best integrated Microsoft ecosystem protection.
Why I Picked Microsoft Defender Threat Intelligence: In determining the leading threat intelligence platforms, Microsoft Defender stood out for its native integration within the Microsoft ecosystem. In my opinion, and after judging its capabilities, I chose it because of its streamlined functionality across the myriad of Microsoft applications. Its strength in ensuring protection within the Microsoft ecosystem is undeniably the rationale behind its designation as the best in that niche.
Standout features & integrations:
Microsoft Defender brings its advanced threat-hunting capabilities combined with post-breach insights. The solution also provides automated investigation and remediation features, boosting the efficiency of threat response. As for integrations, Microsoft Defender excels with native compatibility across the entire Microsoft suite, including Azure, Office 365, and Windows endpoints.
Pros and Cons
Pros:
- Automated remediation features
- Advanced threat-hunting tools
- Native protection across Microsoft platforms
Cons:
- Can be complex for novice users
- Pricing might be on the steeper side for smaller organizations
- Less versatility outside the Microsoft ecosystem
Best for advanced email threat prevention
Mimecast's solution is a dedicated shield against the diverse threats that plague email communication today. Guarding inboxes from phishing, impersonation, and malicious attachments, it shines brightest in advanced email threat prevention.
Why I Picked Mimecast Email Security with Targeted Threat Protection: Email security remains a vital concern for organizations, and after comparing numerous tools, Mimecast emerged as my selection. I determined that its depth in email protection and real-time intelligence positioned it a notch above the rest. This specialized focus on advanced threats, particularly those targeting email, makes it the best pick for robust email defense.
Standout features & integrations:
Mimecast offers URL protection, deterring users from inadvertently accessing malicious sites. Attachment protection ensures files are safe before they're opened, and impersonation protection safeguards against deceiving emails. As for integrations, Mimecast pairs well with most major email platforms, including Microsoft Office 365 and Google Workspace.
Pros and Cons
Pros:
- Real-time threat intelligence
- Integrates smoothly with major email platforms
- Comprehensive email threat protection suite
Cons:
- Occasional false positives
- Might be overkill for smaller organizations
- Some features might have a learning curve
IBM Threat Intelligence is a platform that provides exhaustive insights into cyber threats on an enterprise scale. Designed for large-scale operations, it is a leading choice for organizations requiring an in-depth, macro-level view of cyber threats.
Why I Picked IBM Threat Intelligence: When comparing platforms for enterprise threat insights, IBM's offering consistently exceeded my list. What set it apart was its robustness, tailored for the extensive requirements of large organizations. Given its capacity to provide a comprehensive analysis at an enterprise scale, it’s unsurprising that I deem it the best in its category.
Standout features & integrations:
IBM Threat Intelligence showcases features such as extensive threat data repositories and advanced analytical tools. Furthermore, it incorporates AI-driven insights for more accurate threat predictions. Regarding integrations, the platform synergizes well with IBM's suite of security tools and many third-party enterprise solutions.
Pros and Cons
Pros:
- AI-driven insights
- Exhaustive threat data repositories
- Tailored for large-scale operations
Cons:
- Some features require technical proficiency
- The pricing structure can be ambiguous
- Might be overkill for small businesses
Best for cloud-native endpoint security
Crowdstrike Falcon Endpoint Protection Platform provides security teams with comprehensive visibility and protection across their network endpoints. Rooted in a cloud-native architecture, it stands out as the preeminent choice for organizations migrating or operating in cloud environments.
Why I Picked Crowdstrike Falcon Endpoint Protection Platform: In my journey of determining the most effective endpoint security platforms, Crowdstrike Falcon became a clear front-runner. It stands out due to its unique cloud-centric approach. This cloud-native architecture, combined with its efficient threat detection capabilities, is why it is unparalleled for cloud-driven endpoint security.
Standout features & integrations:
Crowdstrike Falcon offers real-time monitoring and response capabilities, ensuring threats are neutralized swiftly. It also employs AI-driven analysis for proactive threat hunting. Integrations include compatibility with major cloud service providers and an array of SIEM, SOAR, and IT operations platforms.
Pros and Cons
Pros:
- Efficient AI-driven threat analysis
- Cloud-native architecture offers flexibility
- Comprehensive endpoint protection suite
Cons:
- Occasional false alerts
- Some competitors offer broader integrations
- Might be complex for smaller businesses
IBM X-Force Exchange, a creation of tech giant IBM, is a platform designed to foster collaboration in threat intelligence. Its primary strength lies in enabling organizations to share and acquire threat data collaboratively, epitomizing its capability in collaborative threat sharing.
Why I Picked IBM X-Force Exchange: Selecting a platform that excelled in fostering collaboration was paramount, and IBM X-Force Exchange was a natural choice. Upon comparing platforms, I determined that its emphasis on sharing and collaborating on threat intelligence set it apart. This collaborative ethos is precisely why it's the best platform for those prioritizing joint defense and shared knowledge.
Standout features & integrations:
IBM X-Force Exchange showcases a rich collection of threat intelligence backed by IBM's extensive research. It also offers a user-friendly interface to create and share collections of threat indicators. Regarding integrations, the platform is compatible with major SIEM solutions, orchestration tools, and a range of IBM's own security products.
Pros and Cons
Pros:
- Integrates well with multiple enterprise solutions
- Emphasis on collaborative defense
- Rich threat intelligence database
Cons:
- Pricing clarity could be improved
- Relies heavily on community participation
- Can be overwhelming for those new to threat-sharing platforms
Other Threat Intelligence Solutions
Below is a list of additional threat intelligence solutions that I shortlisted, but did not make it to the top 10. Definitely worth checking them out.
- Flashpoint Intelligence Platform
For deep and dark web intelligence
- Cyble Vision
For real-time compromised data alerts
- Cyware Labs
For situational awareness feeds
- Dataminr
For real-time event detection
- Intezer Analyze
For code reuse detection in malware
- Cyberint
For targeted cyber threat intelligence
- ActivTrak
Good for workforce productivity and insights
- OnSecurity
Good for penetration testing and vulnerability assessment
- CrowdSec
Good for community-driven security responses
- PhishLabs
Good for combatting phishing attacks
- Lookout
Good for mobile security and risk management
- LogPoint
Good for granular event log analysis
- CYREBRO
Good for centralized cybersecurity operations
- Defendify All-In-On Cybersecurity®
Good for comprehensive cybersecurity coverage
- Silo by Authentic8
Good for secure and anonymous web browsing
Threat Intelligence Solutions Selection Criteria
When selecting the best threat intelligence solutions to include in this list, I considered common buyer needs and pain points like timely threat detection and integration with existing security systems. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Threat detection and analysis
- Incident response support
- Threat data integration
- Automated alerts and notifications
- Vulnerability assessment
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Machine learning capabilities
- Customizable dashboards
- Real-time threat intelligence sharing
- Advanced analytics and reporting
- Geolocation-based threat insights
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Ease of navigation
- Customization options
- Learning curve for new users
- Integration with existing tools
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Webinars and live demos
- Supportive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multichannel support options
- Response time to inquiries
- Quality of documentation
- Access to a dedicated account manager
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Pricing compared to competitors
- Availability of free trials
- Transparent pricing models
- Scalability of pricing plans
- Features included in basic plans
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on functionality
- Reports on customer support experiences
- Comments on ease of use
- Testimonials on ROI and benefits
How to Choose Threat Intelligence Solutions
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the solution grow with your needs? Consider future expansion and whether the tool can handle increased data and user load. |
| Integrations | Does it work with your existing tools? Check for compatibility with your current security systems and software stack. |
| Customizability | Can you tailor the tool to fit your workflows? Look for options to adjust settings and features to match your team's processes. |
| Ease of use | Is the interface user-friendly? Evaluate the learning curve for your team and whether training is required for effective use. |
| Implementation and onboarding | How long does it take to set up? Consider the time and resources needed for initial setup and whether vendor support is available during this phase. |
| Cost | Does the pricing fit your budget? Compare costs against features offered and consider any hidden fees or long-term contracts. |
| Security safeguards | Are there robust security measures? Make sure the solution complies with industry standards and offers features like encryption and access controls. |
| Support availability | Is support accessible when needed? Check if there’s 24/7 support and multiple contact options like chat, email, and phone. |
What Are Threat Intelligence Solutions?
Threat intelligence solutions are tools that gather and analyze information about potential cybersecurity threats. Security analysts, IT professionals, and cybersecurity teams generally use these tools to enhance their organization's security posture. Automated alerts, threat data integration, and incident response support help with proactive threat management and informed decision-making. Overall, these tools provide valuable insights to protect your organization from cyber threats.
Features
When selecting threat intelligence solutions, keep an eye out for the following key features:
- Threat detection and analysis: Identifies potential threats and provides insights to help mitigate risks before they impact your organization.
- Incident response support: Offers tools to efficiently manage and respond to security incidents, minimizing damage and recovery time.
- Automated alerts: Sends real-time notifications of potential threats, allowing your team to take immediate action.
- Threat data integration: Combines threat intelligence data with existing security tools for a comprehensive view of potential risks.
- Customizable dashboards: Allows you to tailor the interface to display the most relevant data for your team's needs.
- Machine learning capabilities: Utilizes advanced algorithms to predict and identify emerging threats, enhancing proactive security measures.
- Advanced analytics and reporting: Provides in-depth analysis and visualizations to better understand threat patterns and trends.
- Geolocation-based threat insights: Offers information on threats specific to different geographic regions, helping to prioritize responses.
- Training and support resources: Includes access to training materials and customer support to ensure effective use and implementation.
- Integration with existing tools: Ensures compatibility with your organization's current security infrastructure, facilitating smooth operations.
Benefits
Implementing threat intelligence solutions provides several benefits for your team and your business. Here are a few you can look forward to:
- Proactive threat management: Automated alerts and threat detection help your team address risks before they become serious issues.
- Enhanced decision-making: Advanced analytics and reporting provide insights that guide your security strategies and resource allocation.
- Improved incident response: Incident response support tools enable quicker and more effective reactions to security breaches.
- Cost efficiency: By preventing potential threats and reducing incident impact, these solutions can save costs related to data breaches and downtime.
- Tailored security strategies: Customizable dashboards allow you to focus on the most relevant data, optimizing your security efforts.
- Increased threat awareness: Machine learning capabilities keep your team informed about emerging threats, enhancing overall security awareness.
- Regional threat insights: Geolocation-based threat information helps prioritize responses based on regional risks, ensuring resources are used effectively.
Costs and Pricing
Selecting threat intelligence solutions requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in threat intelligence solutions solutions:
Plan Comparison Table for Threat Intelligence Solutions
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited alerts, and community support. |
| Personal Plan | $10-$30/ user/month | Threat detection and analysis, basic reporting, and email support. |
| Business Plan | $50-$100/ user/month | Advanced analytics, incident response support, integration with existing tools, and phone support. |
| Enterprise Plan | $150-$300/ user/month | Customizable dashboards, machine learning capabilities, geolocation-based insights, and dedicated account management. |
Threat Intelligence Solutions FAQs
How can threat intelligence solutions improve our security posture?
These tools provide insights into potential threats, allowing your team to take proactive measures. They help identify vulnerabilities and prioritize responses. By understanding threat patterns, you can develop better defense strategies and allocate resources effectively.
Which are some of the cheapest threat intelligence software options?
CrowdSec is one of the more affordable options, especially for smaller businesses or individual users.
Which software options are on the more expensive side?
Solutions like IBM Threat Intelligence or Cisco Talos are pricier, and designed to cater to enterprise-level requirements.
Are there any free threat intelligence tools available?
Yes, CrowdSec, for example, offers a community version that is free to use. However, it’s essential to note that free versions may lack some advanced features available in their paid counterparts.
How do I measure the ROI of a threat intelligence solution?
Assess the reduction in incident response time and the number of prevented breaches. Calculate the cost savings from avoided downtime and data loss. Consider improvements in threat awareness and decision-making as part of the overall value.
What’s Next:
If you're in the process of researching threat intelligence solutions, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.