Software Supply Chain Security Tools Shortlist
Software supply chain security tools help you detect, monitor, and prevent threats across your code, dependencies, and development process. These tools focus on application security and open source security, identifying known vulnerabilities before they impact production. They often include capabilities like software composition analysis and automated security testing to protect sensitive data and ensure safer software delivery. By integrating into your pipeline, they give teams visibility and control over risks across the entire supply chain. This list gives you a clear, up-to-date look at the top tools trusted by IT teams to secure every link in your software supply chain. You’ll find options for different environments, risk profiles, and workflows—so you can choose the right fit for your team’s needs.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Software Supply Chain Security Tools Summary
This comparison chart summarizes pricing details for my top software supply chain security tool selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for developer-first vulnerability scanning | Free plan + free demo available | From $25/contributing developer/month | Website | |
| 2 | Best for AI-powered code security | Free demo available | Pricing upon request | Website | |
| 3 | Best for end-to-end supply chain security | 14-day free trial + free plan + free demo available | From $135/user/month + consumption (billed annually) | Website | |
| 4 | Best for customizable security scanning rules | Free plan + free demo available | From $30/contributor/month | Website | |
| 5 | Best for policy-based container security | 14-day free trial + free demo available | Pricing upon request | Website | |
| 6 | Best for risk-based code-to-cloud visibility | Free demo available | Pricing upon request | Website | |
| 7 | Best for advanced supply chain threat detection | 14-day free trial + free plan + free demo available | From $500/month | Website | |
| 8 | Best for continuous binary and container scanning | 14-day free trial + free demo available | From $150/month | Website | |
| 9 | Best for CI/CD supply chain protection | Free plan + free demo available | $350/month | Website | |
| 10 | Best for secure container image supply chains | Free plan available | Pricing upon request | Website |
-

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Software Supply Chain Security Tools Reviews
Below are my detailed summaries of the software supply chain security tools that made it onto my shortlist. My reviews offer a detailed look at the features, capabilities, and integrations of each platform to help you find the best one for you.
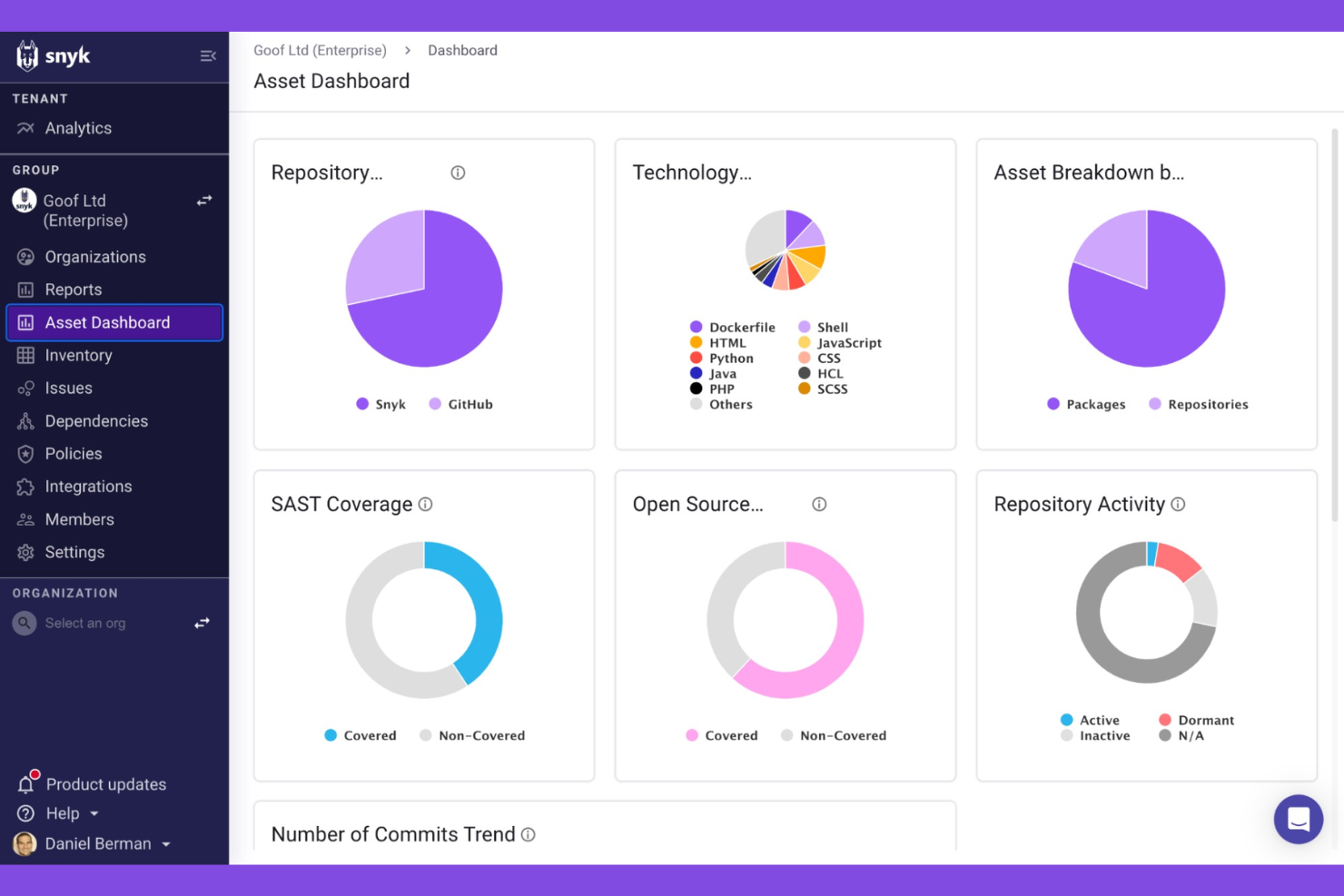
Snyk is a software supply chain security platform that provides automated vulnerability detection, code scanning, license compliance, and remediation tools for developers and security teams.
Who Is Snyk Best For?
Development teams and security engineers at technology-driven companies who want automated vulnerability detection and remediation in their software supply chain.
Why I Picked Snyk
I picked Snyk as one of the best because I rely on its developer-first approach to catch vulnerabilities early in the coding process. I like that it scans for malicious code across open source dependencies, container images, and infrastructure as code, helping secure the broader development ecosystem. My team also benefits from insights like dependency metadata and automated remediation suggestions, which make it easier to fix issues quickly without leaving our workflow.
Snyk Key Features
- License compliance management: Tracks and flags open source license issues in dependencies.
- SBOM generation: Automatically creates software bills of materials for every project.
- Custom security policies: Lets you define and enforce organization-specific security rules.
- Integration with CI/CD pipelines: Connects directly to build tools for continuous monitoring.
Snyk Integrations
Snyk offers native integrations with GitHub, GitLab, Bitbucket, Azure DevOps, Jenkins, Jira, Docker Hub, CircleCI, Travis CI, and Slack. An API is available for custom integrations.
Pros and Cons
Pros:
- License compliance tracking for third-party packages
- Automated remediation for detected vulnerabilities
- Real-time scanning of open source dependencies
Cons:
- Advanced features require higher-tier plans
- Limited reporting options for compliance audits
Checkmarx is a software supply chain security platform that provides automated code scanning, open source risk analysis, and AI-driven threat detection for development teams.
Who Is Checkmarx Best For?
Security and DevOps teams at large enterprises who need automated code and supply chain risk analysis.
Why I Picked Checkmarx
I picked Checkmarx as one of the best because I rely on its AI-driven supply chain risk detection to surface threats that traditional scanners miss. My team uses its automated code analysis and open source risk management to catch vulnerabilities early in our pipelines. I like how it correlates findings across code, dependencies, and infrastructure for a unified risk view.
Checkmarx Key Features
- SBOM generation: Automatically creates software bills of materials for all tracked components.
- Policy management: Lets you define and enforce security policies across projects.
- Dependency graph visualization: Maps relationships and risk across your software supply chain.
- Audit logging: Tracks all user actions and policy enforcement for compliance.
Checkmarx Integrations
Checkmarx offers native integration into the Checkmarx One platform and supports developer workflows with integrations into CI/CD pipelines and source code repositories. An API is available for custom integrations.
Pros and Cons
Pros:
- Supports multi-language and multi-framework projects
- Provides detailed SBOM and dependency mapping
- AI-driven detection of supply chain threats
Cons:
- Reporting customization options are restricted
- False positives can require manual review
Sonatype is a software supply chain security platform that helps organizations identify and reduce security risks across the software development lifecycle. It provides automated policy enforcement, continuous monitoring, vulnerability detection, and license compliance for both open source and proprietary components.
Who Is Sonatype Best For?
Enterprise security and DevOps teams who need automated policy enforcement and monitoring across complex software supply chains.
Why I Picked Sonatype
I picked Sonatype as one of the best because I rely on its automated policy enforcement to keep our software supply chain compliant at every stage. I like that it continuously monitors open source and proprietary components for vulnerabilities and license risks. My team uses its granular policy controls to block risky dependencies before they ever reach production.
Sonatype Key Features
- SBOM generation: Automatically creates software bills of materials for every build.
- Continuous dependency scanning: Monitors third-party libraries for new vulnerabilities.
- Role-based access control: Lets you manage user permissions and restrict sensitive actions.
- Audit logging: Tracks all security events and changes within your CI/CD environment.
Sonatype Integrations
Sonatype offers native integrations with Jenkins, GitHub, GitLab, Bitbucket, Azure DevOps, Bamboo, Nexus Repository, Jira, and Slack. An API is available for custom integrations.
Pros and Cons
Pros:
- License risk detection for third-party libraries
- Detailed SBOM generation for every build
- Automated policy enforcement for open source components
Cons:
- Documentation can be sparse for complex setups
- Limited reporting customization for compliance needs
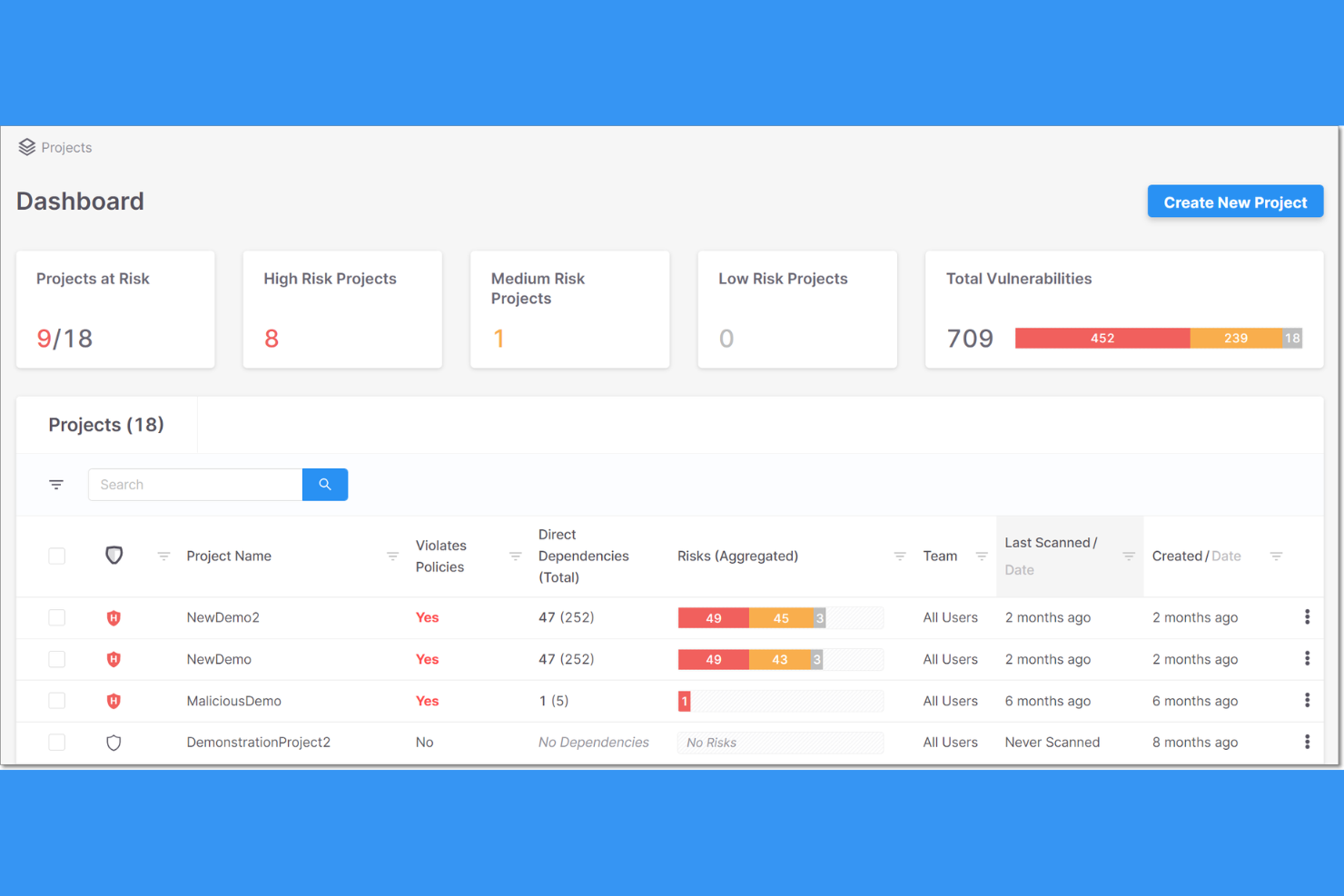
Semgrep is a software supply chain security tool that combines code scanning, dependency analysis, and policy enforcement to help teams identify and manage risks across their development workflows.
Who Is Semgrep Best For?
Security engineers and DevSecOps teams at technology-driven companies who need automated code and dependency security across their software supply chain.
Why I Picked Semgrep
I picked Semgrep as one of the best because I rely on its automated code and dependency security to catch vulnerabilities before they reach production. I use its supply chain insights to track open source risks and policy violations across our repositories. My team benefits from its actionable findings, which help us prioritize and remediate issues quickly.
Semgrep Key Features
- Custom rule creation: Lets you write and enforce your own security policies.
- CI/CD pipeline integration: Connects directly with build and deployment workflows.
- SBOM generation: Produces software bills of materials for dependency tracking.
- Third-party package monitoring: Continuously scans for risks in open source libraries.
Semgrep Integrations
Semgrep offers native integrations with GitHub, GitLab, Bitbucket, Azure DevOps, Jenkins, and Jira, and provides an API for custom integrations.
Pros and Cons
Pros:
- Community-driven rule library for rapid updates
- Customizable rules for dependency risk detection
- Fast, code-aware supply chain scanning engine
Cons:
- No native support for binary artifact scanning
- Advanced rule writing requires YAML proficiency
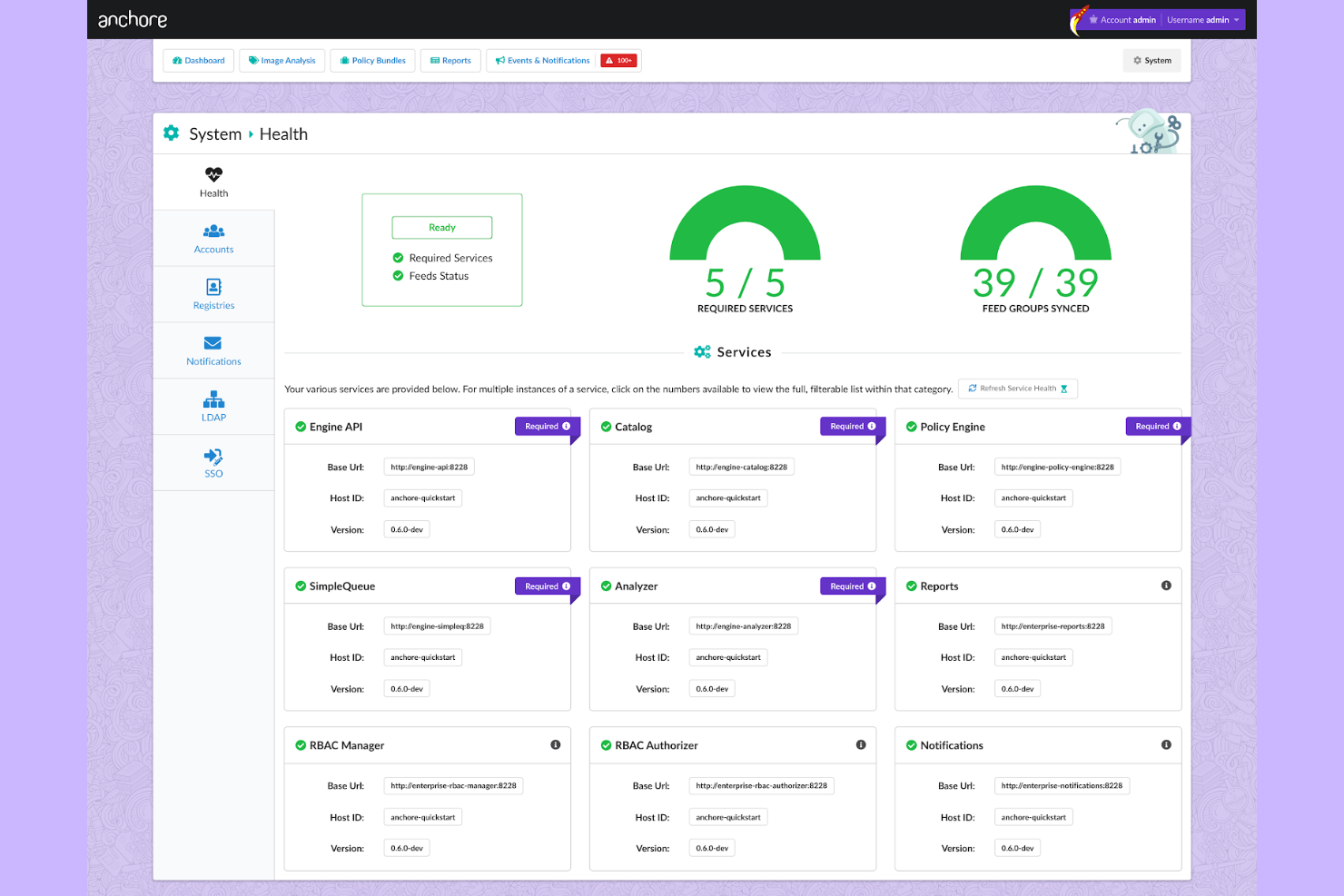
Anchore is a software supply chain security platform that provides automated container image scanning, policy enforcement, vulnerability detection, and compliance checks for containerized applications.
Who Is Anchore Best For?
Security and DevOps teams at enterprises running containerized workloads in regulated industries.
Why I Picked Anchore
I picked Anchore as one of the best because I rely on its automated container image scanning and policy enforcement to catch vulnerabilities before deployment. My team uses it alongside SCA tools to analyze open source software and enforce rules that support risk mitigation at every stage of our CI/CD pipeline. I also like that it provides detailed reports on vulnerabilities and policy violations, helping us maintain a secure software supply chain.
Anchore Key Features
- SBOM generation: Automatically creates software bills of materials for container images.
- Multi-registry scanning: Scans images across multiple container registries for vulnerabilities.
- Role-based access control: Lets you manage user permissions and access within the platform.
- REST API: Enables integration with external tools and custom workflows.
Anchore Integrations
Anchore offers native integrations with Jenkins, GitHub, GitLab, Azure DevOps, and Jira, and provides an API for custom integrations. It also supports CI/CD workflows through its API.
Pros and Cons
Pros:
- Supports automated remediation workflows
- Open source engine available for customization
- Strong policy-based container image scanning
Cons:
- Scan speeds can be slow on large images
- Limited support for non-container artifacts
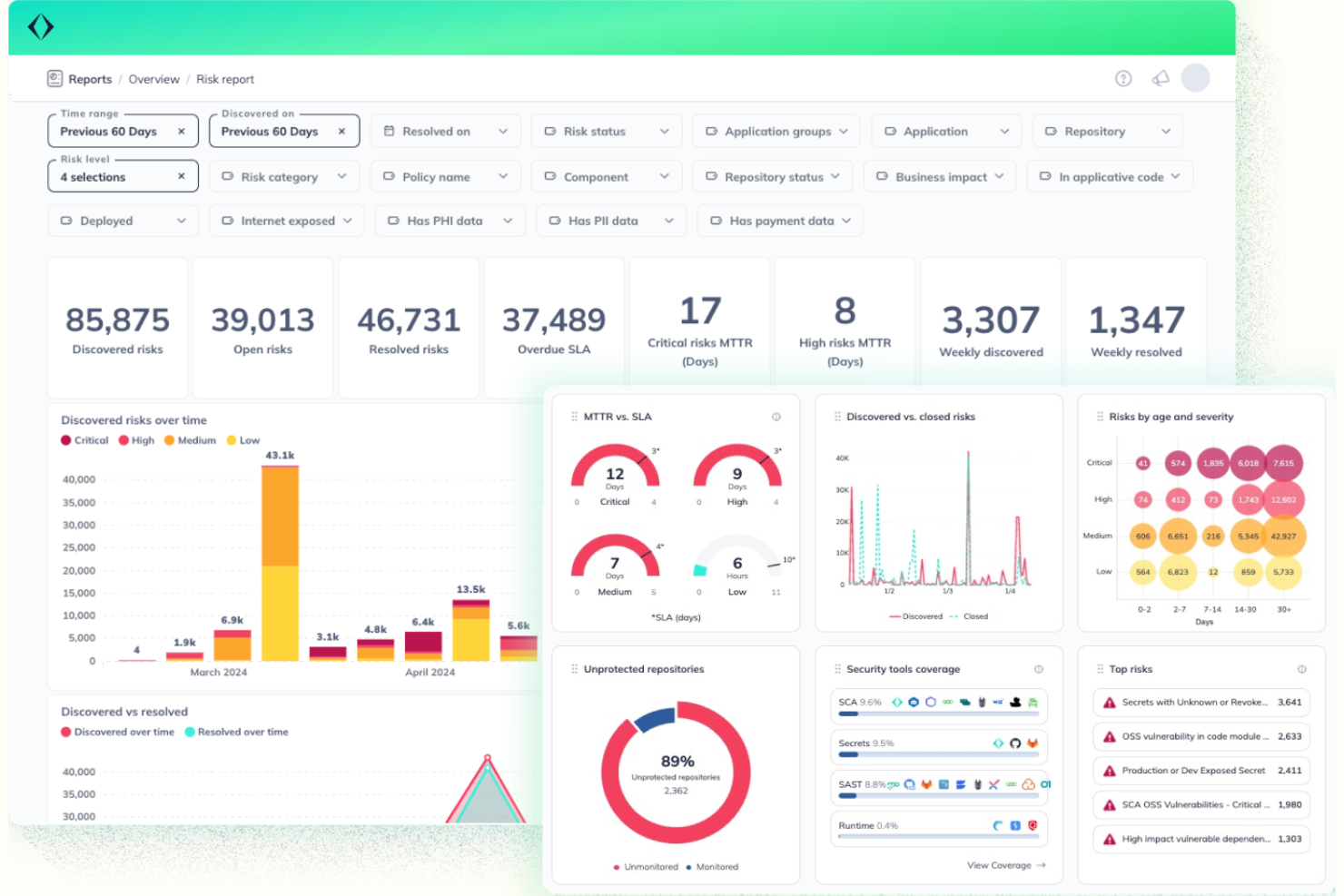
Apiiro is a software supply chain security platform that provides code risk analysis, CI/CD pipeline monitoring, and automated remediation for development and security teams.
Who Is Apiiro Best For?
Security and engineering teams at large enterprises needing end-to-end risk visibility and remediation across their software supply chain.
Why I Picked Apiiro
I picked Apiiro as one of the best because I rely on its end-to-end risk visibility and remediation across the software supply chain. I use its code risk analysis to identify vulnerabilities early, and its automated remediation workflows help my team address issues before they reach production. I also like how Apiiro maps risks to business context, so we can prioritize what matters most.
Apiiro Key Features
- SBOM management: Lets you generate, track, and manage software bills of materials for all components.
- Policy-driven controls: Enable you to enforce custom security and compliance policies across your pipelines.
- Third-party dependency scanning: Identifies vulnerabilities in open-source and third-party libraries.
- Audit trail and reporting: Provides detailed logs and reports for all risk and remediation activities.
Apiiro Integrations
Apiiro offers native integrations with GitHub, GitLab, Bitbucket, Azure DevOps, Jenkins, Jira, and Slack, and provides an API for custom integrations.
Pros and Cons
Pros:
- Supports SBOM management and export
- Context-aware risk prioritization
- Native integration with major CI/CD tools
- Automated remediation for code and dependencies
- End-to-end risk mapping across pipelines
Cons:
- Scan speeds can be slow on large images
- Limited support for non-container artifacts
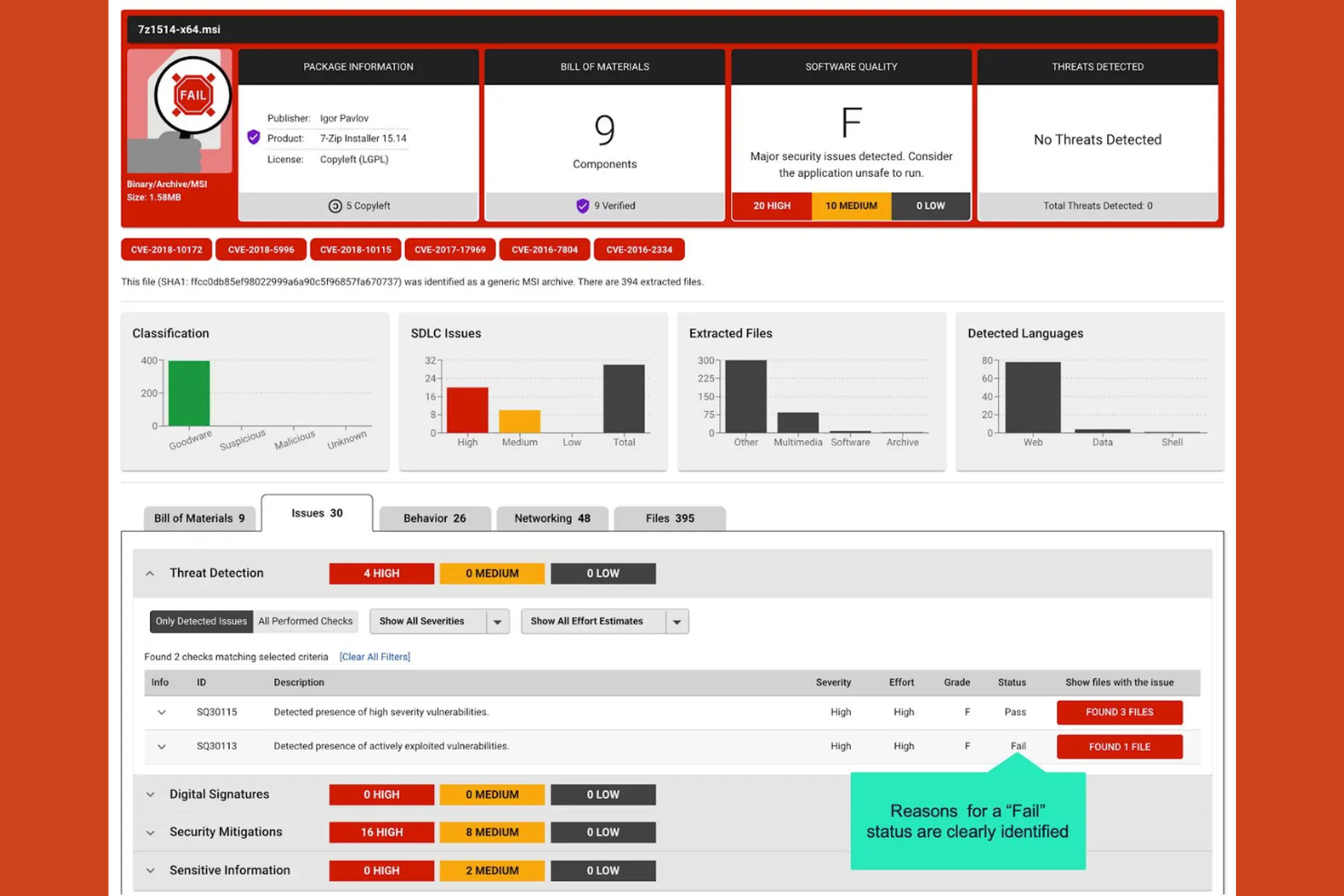
ReversingLabs is a software supply chain security platform that delivers advanced threat detection, binary analysis, and continuous monitoring for software artifacts and components.
Who Is ReversingLabs Best For?
Security teams at large enterprises and software vendors who need advanced threat detection and analysis for their software supply chain.
Why I Picked ReversingLabs
I picked ReversingLabs as one of the best because I rely on its advanced threat detection and deep binary analysis to uncover hidden risks across third-party components. My team uses its continuous monitoring to strengthen our cybersecurity posture and catch supply chain threats early, similar to high-profile risks seen in incidents like SolarWinds. I also value its detailed file reputation and malware analysis, which give me confidence in securing both open source and proprietary software.
ReversingLabs Key Features
- Automated policy enforcement: Enforces security policies across the software supply chain.
- SBOM management: Generates and manages software bills of materials for all artifacts.
- Tamper detection: Identifies unauthorized changes in software packages.
- Integration with CI/CD pipelines: Connects directly to build and deployment workflows.
ReversingLabs Integrations
Native integrations are not currently listed. The tool supports integrations via API for custom workflows and can connect to CI/CD pipelines.
Pros and Cons
Pros:
- Tamper detection for software packages
- Automated SBOM generation and management
- Deep binary analysis for software artifacts
Cons:
- Limited open source vulnerability scanning features
- High resource usage for deep analysis
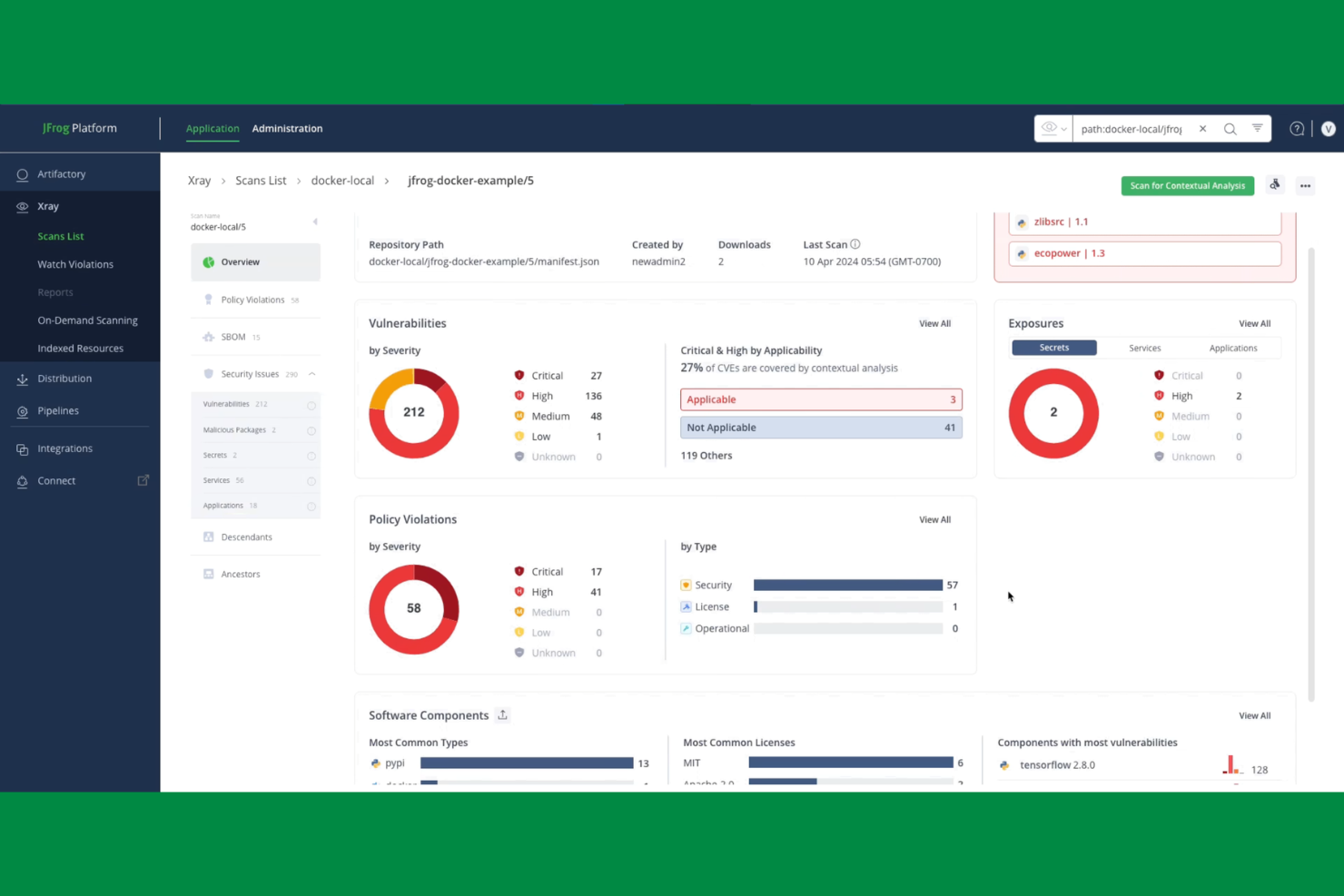
JFrog Xray is a software supply chain security tool that provides deep binary and container scanning, vulnerability detection, and license compliance analysis across your artifacts and dependencies.
Who Is JFrog Xray Best For?
Enterprise DevOps and security teams in technology, finance, and manufacturing who need deep scanning of binaries and containers for vulnerabilities and license compliance.
Why I Picked JFrog Xray
I picked JFrog Xray as one of the best because I rely on its deep recursive scanning for vulnerability management across binaries and containers. I like that it analyzes dependencies in open-source projects all the way down the chain, not just surface-level packages. My team also benefits from features like authentication controls and its integration with JFrog Artifactory to automate continuous scanning within our CI/CD workflows.
JFrog Xray Key Features
- Policy-based security controls: Set and enforce custom security and compliance policies for artifacts.
- SBOM generation: Automatically creates software bills of materials for tracked components.
- REST API access: Integrate scanning and reporting into external systems and workflows.
- License compliance management: Detects and flags open source license issues in dependencies.
JFrog Xray Integrations
JFrog Xray offers native integrations with JFrog Artifactory, Jenkins, Jira, GitHub, GitLab, Bitbucket, Azure DevOps, and Slack. An API is available for custom integrations, and it supports CI/CD workflows through its API.
Pros and Cons
Pros:
- Supports multi-package and multi-language projects
- Real-time vulnerability database updates
- Deep binary and container scanning capabilities
Cons:
- Complex initial setup for hybrid environments
- Limited support for non-JFrog repository types
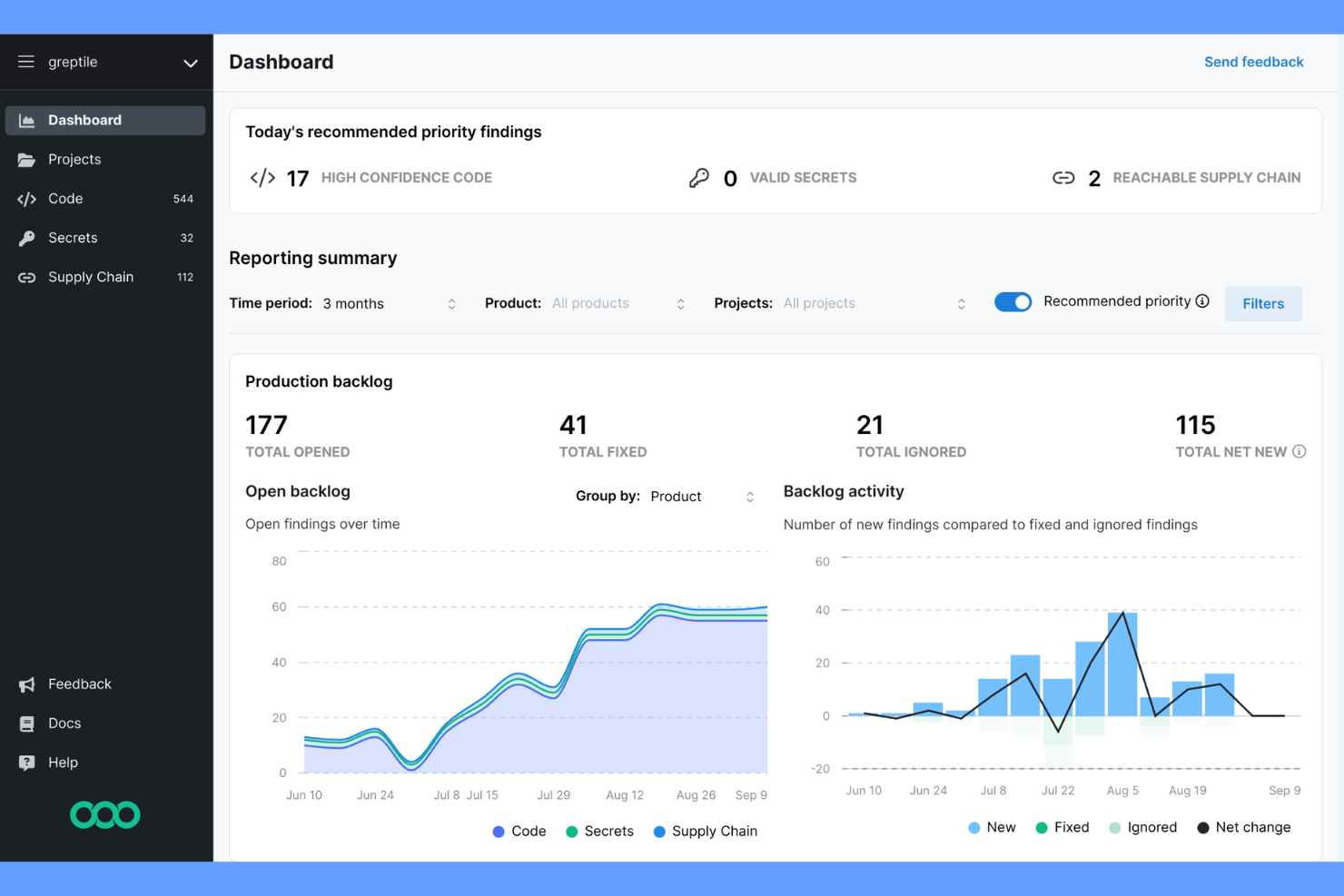
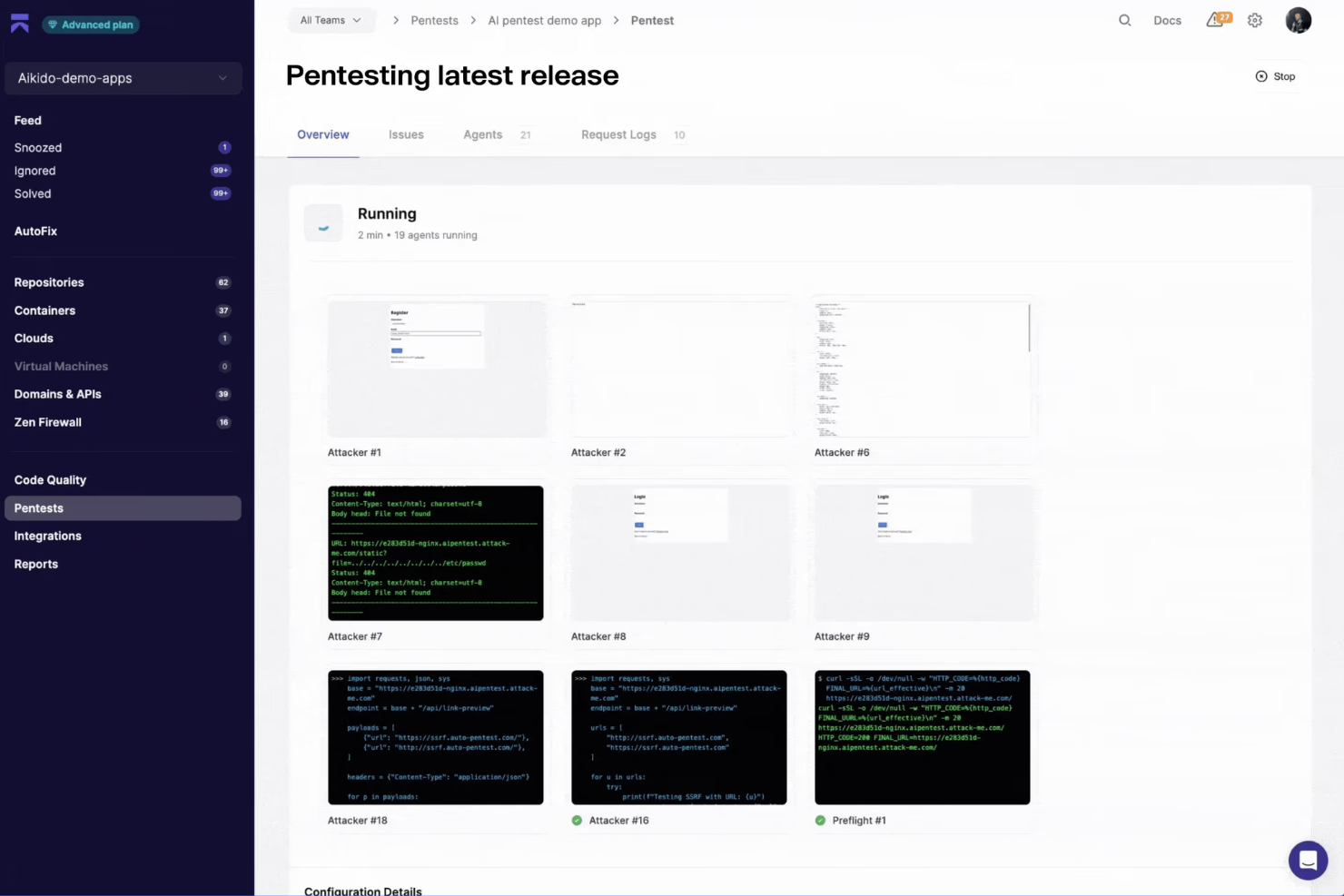
Aikido is a software supply chain security platform that focuses on automated detection and prevention of threats in CI/CD pipelines, offering real-time monitoring and actionable insights for development teams.
Who Is Aikido Best For?
Security and DevOps teams at tech companies who need automated supply chain protection in their CI/CD workflows.
Why I Picked Aikido
I picked Aikido as one of the best because it actively detects and blocks supply chain attacks right in the CI/CD pipeline. I like that it monitors build processes for suspicious activity and enforces security policies automatically. My team is able to get real-time alerts when threats are detected, so we can respond quickly.
Aikido Key Features
- Dependency scanning: Continuously scans open source and third-party dependencies for vulnerabilities.
- SBOM generation: Automatically creates software bills of materials for every build.
- Role-based access control: Lets you manage user permissions and restrict access to sensitive actions.
- Audit logging: Tracks all security events and changes within your CI/CD environment.
Aikido Integrations
Aikido offers native integrations with GitHub, GitLab, Bitbucket, Jira, Slack, Azure DevOps, AWS, Google Cloud, Docker Hub, and Jenkins. An API is available for custom integrations.
Pros and Cons
Pros:
- SBOM generation for every build
- Real-time monitoring of CI/CD pipelines
- Automated detection of supply chain attacks
Cons:
- Advanced features require higher-tier plans
- No on-premises deployment option
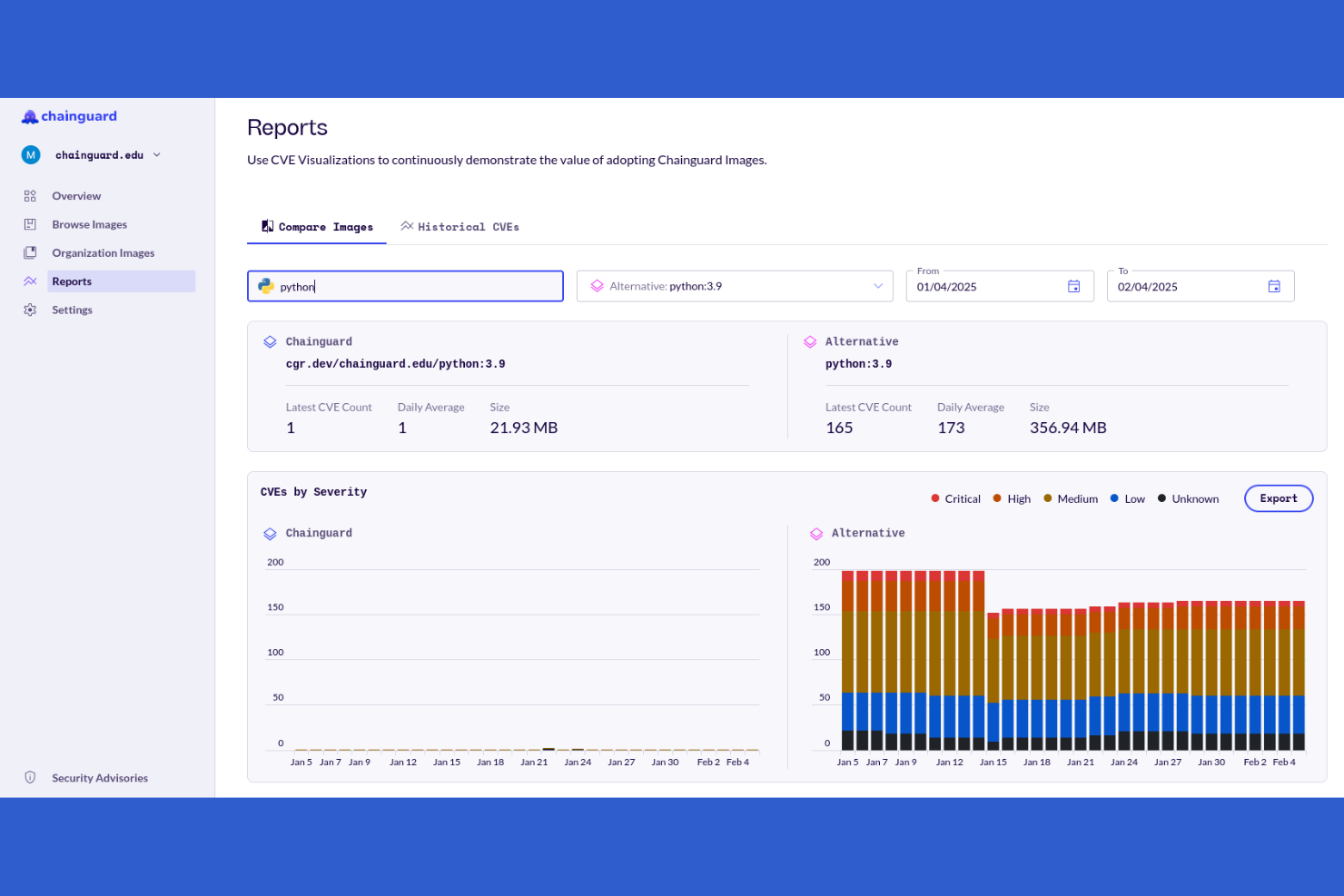
Chainguard is a software supply chain security platform that provides secure, minimal container images, continuous vulnerability monitoring, automated updates, and provenance tracking for containerized workloads.
Who Is Chainguard Best For?
Platform and security teams at cloud-native organizations that need secure, continuously updated container images for production workloads.
Why I Picked Chainguard
I picked Chainguard as one of the best because I rely on its secure, minimal container images that are continuously monitored and updated to protect against software supply chain attacks. My team uses it to manage trusted software components, automate patching, and ensure every image we deploy safeguards sensitive information. I also like that it provides SBOMs out of the box, helping us meet compliance requirements without extra manual work.
Chainguard Key Features
- Policy enforcement: Apply custom security policies to container images before deployment.
- Vulnerability feeds integration: Pulls from multiple vulnerability databases for up-to-date scanning.
- Role-based access control: Manage user permissions and access to container images.
- Audit logging: Tracks all image activity and security events for compliance and investigation.
Chainguard Integrations
Chainguard offers native integrations with AWS, GitLab, JFrog Xray, Snowflake, and Appian. The tool supports integrations via API for custom workflows.
Pros and Cons
Pros:
- Policy enforcement for image security standards
- Built-in SBOM generation for compliance needs
- Automated image updates with signed provenance
Cons:
- Documentation lacks depth for advanced use cases
- Pricing may be high for small teams
Other Software Supply Chain Security Tools
Here are some additional software supply chain security tools options that didn’t make it onto my shortlist, but are still worth checking out:
- Cycode
For unified code and pipeline security
- Kusari
For open-source supply chain integrity
- Zscaler
For zero-trust cloud security
- Veracode
For application supply chain security
- Wiz
For cloud supply chain visibility
- Bitsight
For third-party cyber risk management
- IntegrityNext
For supply chain compliance automation
- Nudge Security
For SaaS supply chain discovery
- Exiger
For AI supply chain risk analysis
- Everstream Analytics
For predictive supply chain risk insights
- Jit
For DevSecOps security and compliance
- Reflectiz
For web supply chain monitoring
Software Supply Chain Security Tools Selection Criteria
When selecting the best software supply chain security tools to include in this list, I considered common buyer needs and pain points like identifying hidden vulnerabilities in dependencies and automating compliance reporting. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Scan code and dependencies for vulnerabilities
- Generate software bills of materials
- Monitor for supply chain threats
- Automate vulnerability remediation workflows
- Integrate with CI/CD pipelines
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- AI-driven threat detection
- Real-time risk scoring dashboards
- Automated policy enforcement
- Dependency graph visualization
- Context-aware prioritization of findings
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Simple and intuitive user interface
- Clear navigation and dashboard layout
- Customizable alerting and reporting
- Minimal manual configuration required
- Fast access to key features
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Step-by-step product tours
- Availability of training videos and webinars
- Pre-built templates for common use cases
- In-app chat or chatbot support
- Detailed onboarding documentation
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Fast response times
- Access to technical experts
- Community forums or knowledge base
- Personalized onboarding assistance
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Transparent pricing structure
- Flexible subscription options
- Features included at each tier
- Cost compared to similar tools
- Free trial or demo availability
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Positive feedback on core functionality
- Reports of reliable performance
- User satisfaction with support
- Comments on ease of integration
- Feedback on update frequency and improvements
How to Choose Software Supply Chain Security Tools
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the tool handle your current and projected codebase size, user count, and number of integrations as your organization grows? |
| Integrations | Does it natively connect with your CI/CD, code repositories, ticketing, and alerting systems? Are APIs available for custom workflows? |
| Customizability | Can you tailor policies, alerts, and reporting to your organization’s risk profile and compliance needs? |
| Ease of use | Is the interface intuitive for both security and development teams? Will it require extensive training or ongoing support to use daily? |
| Implementation and onboarding | How long does setup take, and what resources are required? Are there migration tools, onboarding guides, or dedicated support for rollout? |
| Cost | Are pricing tiers transparent and predictable? Does the cost scale with usage, seats, or features? Watch for hidden fees or add-ons. |
| Security safeguards | What certifications, encryption standards, and data handling practices does the vendor follow? Are there audit logs and access controls? |
| Compliance requirements | Does the tool support your industry’s regulatory standards (e.g., SOC 2, ISO 27001, GDPR)? Can it generate compliance-ready reports? |
What Are Software Supply Chain Security Tools?
Software supply chain security tools are specialized platforms that help organizations identify, monitor, and mitigate risks in the components, dependencies, and processes used to build and deliver software. These tools scan code, third-party libraries, and infrastructure for vulnerabilities, track software bills of materials, and support compliance with security standards throughout the development lifecycle.
Features of Software Supply Chain Security Tools
When selecting software supply chain security tools, keep an eye out for the following key features:
- Vulnerability scanning: Scans source code, dependencies, and containers for known and emerging security vulnerabilities throughout the development lifecycle.
- SBOM generation: Automatically creates a software bill of materials to inventory all components and dependencies in your applications.
- Dependency tracking: Monitors third-party and open source libraries for updates, risks, and license compliance issues.
- Policy enforcement: Lets you define and automate security policies to block risky code or components from entering your environment.
- Risk prioritization: Uses context and severity to rank vulnerabilities, helping teams focus on the most urgent threats first.
- CI/CD integration: Connects directly with your build and deployment pipelines to automate security checks and remediation steps.
- Audit logging: Records user actions, policy changes, and security events for compliance and forensic analysis.
- Alerting and reporting: Notifies teams of critical issues and generates detailed reports for stakeholders and auditors.
- Remediation guidance: Provides actionable steps or automated fixes to resolve identified vulnerabilities and misconfigurations.
Benefits of Software Supply Chain Security Tools
Implementing software supply chain security tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Reduced vulnerability risk: Automated scanning and monitoring help you catch and address security issues before they impact your software or users.
- Improved compliance: Built-in policy enforcement and audit logging make it easier to meet regulatory requirements and pass security audits.
- Faster incident response: Real-time alerts and risk prioritization let your team quickly identify and remediate the most urgent threats.
- Greater visibility: SBOM generation and dependency tracking give you a clear view of all components in your software supply chain.
- Simplified workflows: CI/CD integrations and automated remediation steps reduce manual work and keep security checks in sync with development.
- Better decision-making: Detailed reporting and risk scoring help stakeholders understand security posture and allocate resources where they’re needed most.
- Improved collaboration: Centralized dashboards and alerting keep security, development, and compliance teams aligned on shared risks and actions.
Costs and Pricing of Software Supply Chain Security Tools
Selecting software supply chain security tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in software supply chain security tools solutions:
Plan Comparison Table for Software Supply Chain Security Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic vulnerability scanning, limited SBOM generation, and community support. |
| Personal Plan | $10-$30/user/month | Advanced scanning, basic policy enforcement, limited integrations, and email support. |
| Business Plan | $40-$80/user/month | Full CI/CD integration, risk prioritization, audit logging, reporting, and standard customer support. |
| Enterprise Plan | $100-$200/user/month | Custom policy management, advanced compliance tools, dedicated onboarding, premium support, and SLAs. |
Software Supply Chain Security Tools FAQs
Here are some answers to common questions about software supply chain security tools:
How do software supply chain security tools help prevent supply chain attacks?
These tools scan code, dependencies, and build processes for vulnerabilities and suspicious changes. By monitoring for known threats and enforcing security policies, they help you catch risks early and reduce the chance of compromised components making it into production.
Can software supply chain security tools integrate with my existing CI/CD pipeline?
Yes, most tools offer integrations with popular CI/CD platforms like Jenkins, GitHub Actions, and GitLab CI. This lets you automate security checks as part of your build and deployment workflows, so vulnerabilities are flagged before code is released.
What is a software bill of materials (SBOM) and why does it matter?
An SBOM is a detailed inventory of all components and dependencies in your software. It’s important because it gives you visibility into what’s in your codebase, helps with vulnerability tracking, and is increasingly required for regulatory compliance.
Do these tools support open source and proprietary code?
Yes, most solutions can scan both open source and proprietary codebases. They typically support a wide range of programming languages and package managers, so you can monitor all your software assets for risks.
How often should I run scans with these tools?
You should run scans continuously or at every code commit if possible. Frequent scanning ensures new vulnerabilities are caught quickly and helps maintain a strong security posture as your codebase evolves.