10 Best Network Security Software Shortlist
Securing your network is one of the toughest challenges organizations face. Cyberattacks are becoming more sophisticated, whether it’s malware, phishing, or targeted breaches, and even a single vulnerability can lead to devastating consequences. If you’ve dealt with struggles like protecting sensitive data, managing sprawling IT systems, or staying ahead of new threats, you know how critical it is to have reliable network security software in place.
The right network security tools do more than just block unauthorized access—they actively monitor vulnerabilities, prevent breaches, and give you confidence that your systems are protected. Over the years, I’ve worked with a wide range of security solutions across different industries, helping teams move from reactive problem-solving to proactive defense. In this guide, I’ve evaluated the best network security software, breaking down their features and strengths to help you choose the one that best fits your unique environment.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Network Security Software Summary
This comparison chart summarizes pricing details for my top network security software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for deployment across global teams | Free plan available | From $5/user/month (billed annually) | Website | |
| 2 | Best for zero trust access | 14-day free trial + free demo available | From $7/user/month (billed annually) | Website | |
| 3 | Best for DNS security and threat hunting | Free trial + free demo available | Pricing upon request | Website | |
| 4 | Best for real-time network alerts | 30-day free trial + free demo available | From $10/month (billed annually) | Website | |
| 5 | Best for secure network access | 30-day free trial | From $10/user/month | Website | |
| 6 | Best for continuous scans | 30-day free trial | From $119.99/year (billed annually) | Website | |
| 7 | Best for tailored network security solutions | Free demo available | Pricing upon request | Website | |
| 8 | Best for individual users and home environments | 30-day free trial | From $211/year | Website | |
| 9 | Best comprehensive security services | 30-day free trial | From $15/user/month | Website | |
| 10 | Best for advanced security analytics | Free trial + free demo available | From $0.07/GB data ingested | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Network Security Software Reviews
I’ll explain each tool’s features, integrations, and pricing below, so you can choose the solution that matches your network security needs.
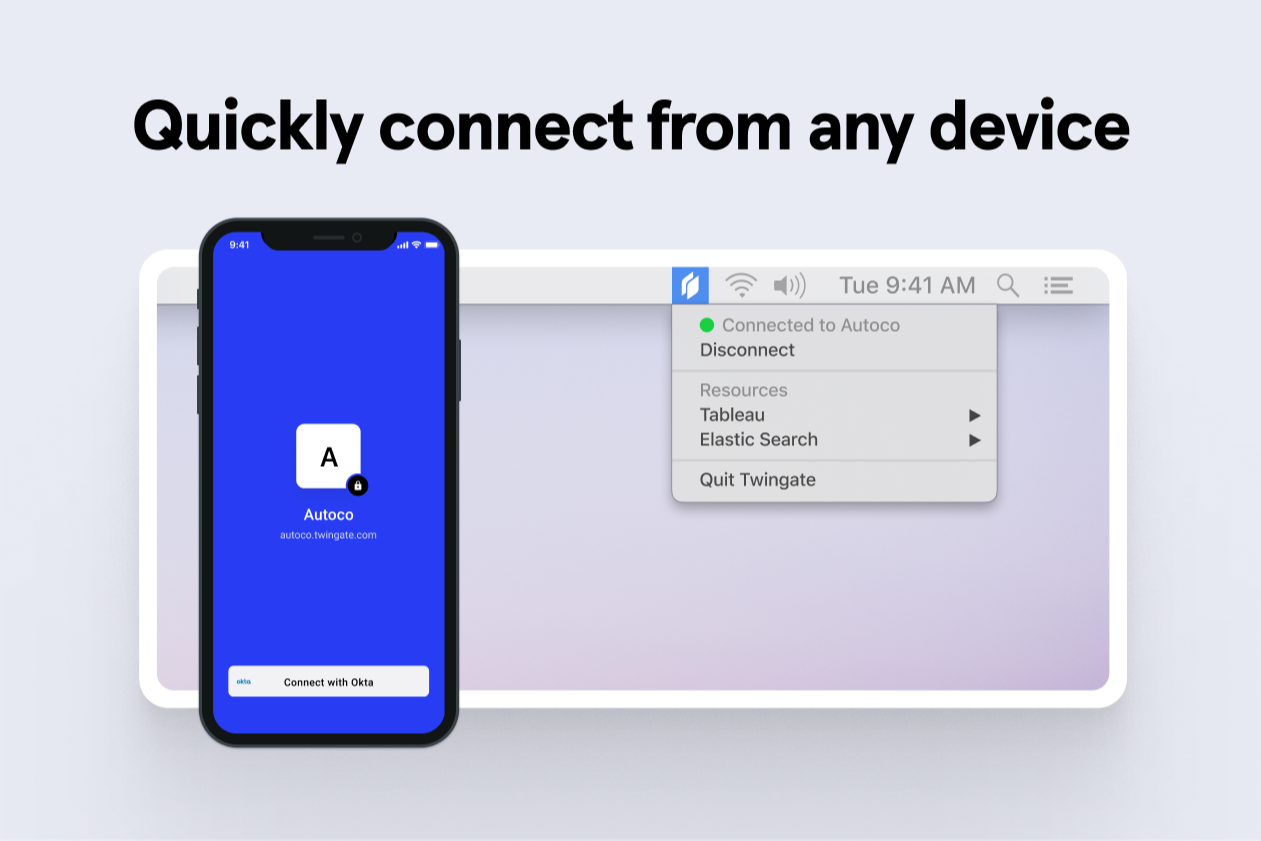
Twingate is a zero trust network security platform focused on securing remote access, resource segmentation, identity integration, and policy-based access for distributed teams.
Who Is Twingate Best For?
Twingate is a strong fit for IT and security teams managing remote or distributed workforces who need to move away from traditional VPN-based access models.
Why I Picked Twingate
I've included Twingate in my top picks because it deploys without requiring firewall changes or open inbound ports. There's no hardware to rack, and my team can get a relay running in under 30 minutes using Twingate's Docker-based connectors. For global rollouts, that speed matters—especially when you're onboarding contractors or remote offices across multiple regions simultaneously.
Twingate Key Features
- Zero trust access controls: Twingate applies least-privilege policies so users only reach the specific resources they're authorized to access.
- Split tunneling: Route only relevant traffic through Twingate, keeping other internet traffic on the user's local connection.
- Device posture checks: Enforce access policies based on device security status, such as OS version or endpoint protection status.
- Activity logging: Track user access events across all resources with detailed logs for auditing and incident review.
Twingate Integrations
Twingate offers native integrations with Okta, Azure Active Directory, Google Workspace, OneLogin, and JumpCloud. It supports automated user provisioning through SCIM and provides an API for custom integrations.
Pros and Cons
Pros:
- Automated user provisioning with SCIM support
- Peer-to-peer encrypted tunnels for low latency
- Native integration with Okta, Google, Azure AD
Cons:
- Some audit features not available for all plans
- Advanced device posture checks need higher tiers
NordLayer is a cloud-based network security platform tailored for businesses, providing secure access to corporate resources and safeguarding sensitive data.
Why I picked NordLayer: I like its implementation of Zero Trust Network Access (ZTNA). This approach ensures that only authorized users can access specific resources, minimizing the risk of unauthorized entry. Another feature that stands out is NordLayer's threat protection measures. It includes tools like DNS filtering and web protection to prevent access to malicious websites, safeguarding your team from potential online threats.
NordLayer Standout Features and Integrations:
Standout features include multi-factor authentication, which adds an extra layer of security by requiring users to provide multiple forms of verification before accessing company resources. Additionally, NordLayer offers a cloud firewall that monitors and controls incoming and outgoing network traffic based on predetermined security rules, providing a barrier against potential threats. The platform also supports site-to-site connections, allowing secure communication between different office locations or networks.
Integrations include Entra ID, Okta, OneLogin, JumpCloud, Google Workspace, Google Cloud, IBM Cloud, and AWS.
Pros and Cons
Pros:
- Provides robust VPN support
- Security measures like AES-256 encryption and multi-factor authentication
- Utilizes a zero-trust framework
Cons:
- Server setup can be complex
- Number of available server locations could be expanded
New Product Updates from NordLayer
NordLayer Enhances Security with Download Protection
NordLayer introduces a Download Protection feature that safeguards files from threats by scanning and blocking malicious downloads in real time. For more information, visit NordLayer's official site.
In the realm of cybersecurity, Heimdal offers a versatile platform designed to meet the demands of businesses seeking to safeguard their network environments. With a comprehensive suite of features, it appeals to industries ranging from healthcare to education, aiming to address challenges such as unauthorized access, data breaches, and compliance with standards like ISO 27001 and HIPAA. For those prioritizing a solution that integrates DNS security, threat hunting, and endpoint protection, Heimdal stands out as a compelling choice.
Why I Picked Heimdal
I picked Heimdal for its unique approach to network security, notably its combination of DNS security and threat hunting capabilities. These features allow your team to stay ahead of potential threats by intercepting and analyzing suspicious network activity in real-time. Additionally, Heimdal's Extended Detection and Response (XDR) platform provides enhanced threat detection across multiple environments, offering a comprehensive view of your network's security posture. For organizations that need to ensure compliance and protect sensitive data, Heimdal's managed services offer 24/7 support to maintain robust security.
Heimdal Key Features
Aside from its standout features, Heimdal offers additional functionalities that enhance its network security capabilities.
- Vulnerability Management: Automates the process of identifying and addressing vulnerabilities within your network, reducing the risk of exploitation.
- Unified Endpoint Management: Provides tools for remote desktop access and privileged access management, ensuring secure control over endpoint devices.
- Email & Collaboration Security: Protects against email threats and fraud, safeguarding communication channels from phishing attacks.
- Ransomware Encryption Protection: Offers advanced protection against ransomware threats, preventing unauthorized data encryption.
Heimdal Integrations
Native integrations are not currently listed by Heimdal; however, the platform supports API-based custom integrations.
Pros and Cons
Pros:
- Detailed asset and license visibility
- Strong vulnerability and threat detection
- Automates patching across endpoints
Cons:
- Interface requires onboarding time
- No native integrations available
Site24x7 is a cloud-based network monitoring tool designed to help you track the health and performance of your network infrastructure. It offers visibility into various network components, including devices, interfaces, and traffic patterns.
Why I picked Site24x7: I picked Site24x7 because it includes several features that directly support network security efforts. Its network configuration management lets you detect unauthorized device changes and stay compliant with security policies, helping prevent misconfigurations that could be exploited. The traffic analysis tools, which support NetFlow, sFlow, and J-Flow, give you visibility into bandwidth usage and potential malicious activity by highlighting traffic anomalies.
Site24x7 Standout Features and Integrations:
Standout features include real-time alerts that ensure you’re immediately notified of changes or threats across your infrastructure. The tool also offers automated compliance audits, continuously checking your network devices against industry standards and internal policies to ensure adherence.
Integrations include AWS, Microsoft Azure, Google Cloud Platform, VMware, Amazon EventBridge, Zoho Analytics, Moogsoft, Jira, ConnectWise, PagerDuty, Microsoft Teams, and Slack.
Pros and Cons
Pros:
- Automated compliance audits
- Real-time alerts for immediate issue detection
- Comprehensive network monitoring capabilities
Cons:
- Excessive alerts can be overwhelming for users
- Lacks more robust security features, like threat detection
New Product Updates from Site24x7
Site24x7 Enhances Database and Storage Monitoring
Site24x7 now includes a Used Storage (%) metric for OpenSearch nodes and unified monitoring for OCI MySQL DB Systems, giving you clear visibility into disk space and database health. For more information, visit Site24x7’s official site.
Perimeter 81 is a network security software focusing on secure remote access and cloud security. It provides a secure VPN, multi-factor authentication, and network segmentation to protect remote workers and cloud resources.
Why I picked Perimeter 81: I picked Perimeter 81 for its zero-trust network architecture and granular access controls, which provides me with secure connectivity for the distributed workforce. The user-centric design and seamless integration with existing infrastructure have simplified the remote access process, allowing employees to work from anywhere securely.
Perimeter 81 Standout Features and Integrations:
Standout Features that I thought were useful include secure network access and a user-centric design prioritizing ease of use and accessibility. It has a Software-Defined Perimeter (SDP) and Zero Trust Network Access (ZTNA) architecture, which drastically reduces the risk of unauthorized access and strengthens overall network security while allowing approved users to connect securely. Perimeter 81 also offers device management, traffic inspection, and secure web gateways.
Integrations include native integration with popular identity providers (e.g., Active Directory, Azure AD, Okta) and cloud providers (e.g., AWS, Azure)
Pros and Cons
Pros:
- Offers granular access control and auditing capabilities
- Centralized management and policy enforcement
- Provides secure access to on-premises and cloud resources from anywhere
Cons:
- Integration with some legacy systems may require additional configuration
- Limited customization options for VPN protocols and settings
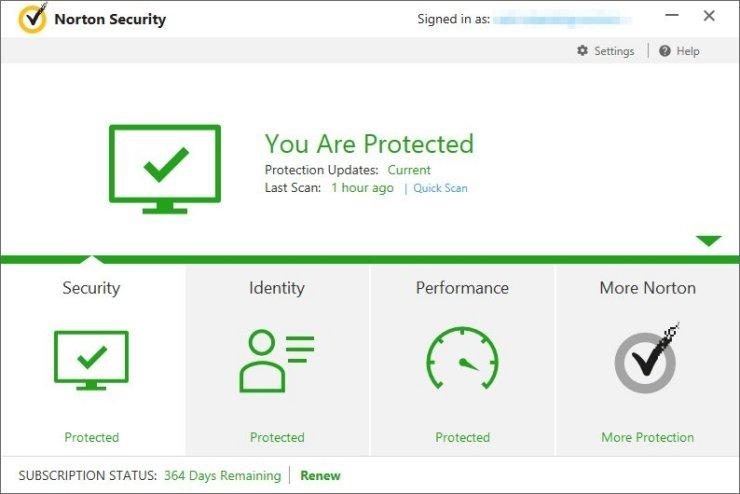
Norton is built for the network security needs of small businesses, offering broad protection for devices and sensitive data. It focuses on defending against common cyber threats while keeping systems secure and operational. Features such as real-time threat monitoring and a secure VPN help protect daily business activity and reduce exposure to online risks.
Why I Picked Norton
I chose Norton primarily for its real-time threat protection, a core requirement for effective network security. It continuously scans for malware and ransomware, helping prevent data loss and system compromise. Norton’s secure VPN adds encrypted connections for team members, supporting safe remote and online work. Together, these features cover essential security needs for businesses looking to protect their network and data.
Norton Key Features
In addition to the standout features, Norton offers an array of functionalities to enhance your team's security infrastructure.
- Cloud Backup: Provides 500 GB of secure cloud storage to protect critical business data from loss due to theft or failures.
- Password Manager: Offers encrypted storage for sensitive credentials, ensuring that passwords remain secure and accessible only to authorized users.
- Dark Web Monitoring: Alerts you if your personal information is found on the dark web, helping to prevent identity theft.
- Driver Updater: Automatically updates outdated or vulnerable drivers, maintaining your system's security and performance.
Norton Integrations
Native integrations are not currently listed by Norton.
Pros and Cons
Pros:
- Cloud backup supports data recovery
- Includes VPN and firewall security
- Strong real time malware protection
Cons:
- Fewer native business integrations
- Limited device cap for teams
Acunetix is a network security software solution that protects against advanced persistent threats (APTs). It employs machine learning algorithms and behavior-based analysis to detect and respond to sophisticated cyber-attacks.
Why I picked Acunetix: Acunetix truly impressed me with its vulnerability scanner and its tailored network security solutions. Working closely with their team, they understood my business requirements and provided me with a customized security package. From firewall management to advanced threat intelligence, their expertise and attention to detail helped me strengthen my network security and stay one step ahead of potential threats.
Acunetix Standout Features and Integrations:
Standout Features include a customizable approach to meet specific business requirements, which consists of incidence response, remediation, and security information and event management (SIEM). This allows me to design a comprehensive security infrastructure that aligns precisely with my unique needs and provides robust protection against cyber threats.
Integrations include built-in integrations with third-party tools like Azure DevOps (Microsoft TFS), JIRA, GitHub, and Citrix.
Pros and Cons
Pros:
- Customizable and scalable to fit the needs of different organizations
- Comprehensive network traffic analysis and visibility into potential vulnerabilities
- Real-time alerts and automated response
Cons:
- Pricing may be higher compared to some other network security solutions
- May require specialized expertise for initial setup and configuration
ESET Internet Security provides comprehensive solutions with features like advanced threat detection, firewall, anti-phishing, and secure browsing. Its lightweight and efficient design makes it a reliable choice for protecting against cyber threats.
Why I picked ESET Internet Security: I consider this tool the best for individual users and home environments because it offers comprehensive protection, including firewall, email scanning, and web browsing for up to 10 of your devices. ESET also has a long-standing reputation in the cybersecurity industry, known for its consistent and reliable security solutions across multiple platforms and devices.
ESET Internet Security Standout Features and Integrations:
Features I appreciated most in ESET Internet Security include a Device Control System that lets you choose the devices that can connect to your PC. I also liked how the Network Inspector let me track my network by receiving notifications when new unregistered devices connect. ESET also offers advanced threat detection, firewall protection, ransomware shield, anti-phishing, anti-spam, and secure payment protection to provide a safe browsing environment for online shopping and banking.
Integrations include Splunk, ServiceNow, Cisco Umbrella, IBM QRadar, McAfee ePO, and SolarWinds MSP RMM. It also integrates natively with other ESET technologies, including Secure VPN, Anti-Theft, SysInspector, Secure Authentication, and Cloud Administrator.
Pros and Cons
Pros:
- Minimal impact on system performance
- Excellent mobile security app for Android
- Offers anti-theft features for stolen devices
Cons:
- Multi-device protection is expensive
- No iOS support
McAfee+ offers a robust suite of security tools, including antivirus, firewall, identity theft protection, and secure VPN. Its AI-powered threat intelligence, with real-time scanning and automatic updates, provides proactive protection against malware, ransomware, and other cyber threats.
Why I picked McAfee+: As someone who values comprehensive security, McAfee+ has been my go-to solution for protecting my personal and business data. Its antivirus, firewall, and identity theft protection feature have a repetition for effectiveness, giving me peace of mind that my digital assets are properly safeguarded.
McAfee+ Standout Features and Integrations:
Standout Features include real-time scanning and threat intelligence features to detect and remove malware, as well as a firewall to prevent unauthorized network access. The identity theft protection component safeguards personal information, including credit card details and Social Security numbers, providing an extra layer of security.
Integrations include native integrations with McAfee MVISION Cloud and McAfee ePO and pre-built integrations with third-party tools like North Star, Trellix, D3 Security, Aruba Networks, and tray.io.
Pros and Cons
Pros:
- Strong customer support
- Provides multi-device protection across different platforms
- User-friendly interface
Cons:
- The initial installation process can be lengthy and resource-intensive
- High system resource usage
Elastic offers a range of solutions for security analytics, log management, and SIEM, leveraging its Elasticsearch, Logstash, and Kibana (ELK) stack. The platform's ability to adapt to meet any organization's security needs makes it an ideal solution for detecting and responding to security incidents.
Why I picked Elastic: Elastic's security analytics and SIEM solutions have been instrumental in detecting and responding to security incidents in my organization. The scalability and flexibility of the platform have allowed me to handle large volumes of log data and perform real-time analysis, enabling proactive threat mitigation.
Elastic Standout Features and Integrations:
Standout Features include advanced capabilities for security analytics, log management, and SIEM. It allows me to collect, analyze, and visualize security-related log data from multiple sources in a unified location. The platform's scalability provides efficient handling of large volumes of data, while its flexible architecture allows for customization and integration with existing security tools and workflows.
Integrations include native integration with Elastic Agent and pre-built connectors for third-party tools like Google Cloud, AWS, Microsoft Azure, Red Hat OpenShift, IBM Cloud, Oracle, Splunk, Webroot, and VMware.
Pros and Cons
Pros:
- Large and active community
- Powerful search and visualization capabilities
- Scalable and flexible platform
Cons:
- Resource-intensive deployment, particularly for larger-scale implementations
- Setting up and configuring the Elastic stack may require technical expertise
Other Network Security Software Options
Still didn’t find the perfect network security tool for you? Here are a few more that didn’t make my top list but are worth checking out for other uses:
- Avira Prime
For privacy-focused individuals and organizations
- Webroot
For cloud-based threat detection
- Commvault
For robust data protection and backup solutions
- Astra Pentest
For comprehensive vulnerability scanning
- ManageEngine Log360
For centralized log management
- CrowdStrike
For AI-driven endpoint protection
- NordVPN
VPN for personal use
- Cloudflare
For web app security and performance optimization
- Snort
For real-time network intrusion detection and prevention
- pfSense
Open-source solution for robust network security
- Palo Alto Network
For security orchestration, automation, and response (SOAR)
- Cisco
For network access control and identity management
Network Security Software Selection Criteria
When selecting the best network security software to include in this list, I considered common buyer needs and pain points like protecting against data breaches and ensuring compliance with security regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Protecting against unauthorized access
- Detecting network intrusions
- Monitoring network traffic
- Managing security policies
- Ensuring data encryption
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Advanced threat intelligence
- Automated incident response
- Integration with IoT devices
- Real-time analytics dashboard
- Compliance management tools
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Ease of navigation
- Intuitive interface design
- Customizable dashboards
- Minimal training required
- User-friendly reporting tools
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars and workshops
- Comprehensive documentation
- Dedicated onboarding support
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Live chat and phone support
- Access to a knowledge base
- Prompt response times
- Availability of support forums
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing models
- Availability of free trials
- Cost versus feature set
- Flexible subscription plans
- Discounts for long-term contracts
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on ease of use
- Comments on feature effectiveness
- Reports on customer support experiences
- Value for money perceptions
How to Choose Network Security Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your business? Consider future expansion and whether the tool can handle increased data and user loads without significant upgrades. |
| Integrations | Does it work with your existing tools? Check for compatibility with your current systems, such as CRM, ERP, or cloud services, to ensure a smooth workflow. |
| Customizability | Can you tailor it to your needs? Look for options to adjust settings, reports, and alerts to fit your specific operational requirements. |
| Ease of use | Is it user-friendly? Consider the learning curve for your team. A simple interface can save time and reduce training costs. |
| Implementation and onboarding | How quickly can you get started? Evaluate the setup time and resources needed, including the availability of support during the transition phase. For companies native to Illinois, working with a cybersecurity company in Chicago can provide in-person benefits during setup. |
| Cost | Is it within your budget? Compare the pricing models and watch for hidden fees. Check if there are discounts for annual subscriptions or larger teams. |
| Security safeguards | Does it meet your security needs? Verify the presence of encryption, multi-factor authentication, and other security measures to protect your data. |
| Compliance requirements | Does it meet industry standards? Ensure the software complies with relevant regulations like GDPR, HIPAA, or PCI DSS for your industry. |
What's Network Security Software?
Network security software is designed to strengthen your IT infrastructure and keep sensitive data safe. This is done with tools like antivirus software, intrusion detection and prevention systems (IDS/IPS), encryption, and security protocols. Network security software can protect from external threats like phishing and malware, as well as threats occurring within a network, such as unauthorized resource access. Unified threat management platforms excel at providing this comprehensive protection across multiple attack vectors.
By implementing network security software, service providers, institutions, and organizations can mitigate cyber risks and achieve real-time threat detection to maintain network infrastructure's reliability. Organizations should also consider specialized firewall audit software to ensure their perimeter defenses are properly configured and compliant.
Features
When selecting network security software, keep an eye out for the following key features:
- Intrusion detection: Monitors network traffic for suspicious activities and alerts administrators to potential threats.
- Threat monitoring: Continuously analyzes the network for vulnerabilities and signs of cyber attacks to prevent breaches.
- Encryption: Protects sensitive data by encoding it, ensuring that only authorized users can access the information.
- Multi-factor authentication: Requires multiple forms of verification before granting access, enhancing security by reducing unauthorized logins.
- Compliance management: Helps organizations adhere to industry regulations like GDPR or HIPAA by providing necessary security controls.
- Real-time analytics: Offers immediate insights into network activity, allowing for quick responses to potential security incidents.
- Automated incident response: Provides automated actions to mitigate threats, minimizing damage and downtime.
- Integration capabilities: Ensures compatibility with existing defense tools like internet security software, facilitating a cohesive security strategy.
- Customizable alerts: Allows users to set specific criteria for alerts, ensuring that they receive relevant and timely notifications.
- User-friendly interface: Simplifies the management and monitoring of network security, reducing the learning curve for IT teams.
Benefits
Implementing network security software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced data protection: Encryption and multi-factor authentication help keep sensitive data secure from unauthorized access.
- Proactive threat management: Intrusion detection and threat monitoring from firewall software allow for early identification and mitigation of potential threats.
- Regulatory compliance: Compliance management features assist in meeting industry standards, reducing the risk of legal penalties.
- Reduced downtime: Automated incident response minimizes the impact of security breaches, ensuring business continuity.
- Improved decision-making: Real-time analytics provide insights into network activity, enabling informed decisions about security strategies.
- Streamlined operations: Integration capabilities ensure that the software works well with existing systems, simplifying overall network management.
- Increased user confidence: A user-friendly interface makes it easier for IT teams to manage security, boosting confidence in their ability to protect the network.
Costs and Pricing
Selecting network security software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in network security software solutions:
Plan Comparison Table for Network Security Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat monitoring, limited support, and community access. |
| Personal Plan | $5-$25/user/month | Threat detection, basic encryption, and limited integrations. |
| Business Plan | $30-$75/user/month | Advanced threat management, multi-factor authentication, and compliance tools. |
| Enterprise Plan | $100-$200/user/month | Full encryption, automated incident response, and dedicated support. |
People Also Ask
Here are some FAQs about network security software you can explore to make a more practical decision that addresses your security needs:
How does network security software work?
What is the difference between network security software and incident response software?
What are the fundamental principles of network security?
What’s Next:
If you're in the process of researching network security software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.