10 Best Database Security Software Shortlist
In today's digital landscape, keeping your data secure is more challenging than ever. With cyber threats constantly evolving, you need reliable tools to protect your databases from breaches and unauthorized access.
As someone who independently tests and reviews software, I understand the pain points you face. You want solutions that are effective, easy to integrate, and compliant with regulations.
In this article, I'll share my top picks for database security software. I've evaluated each one based on features, user experience, and industry needs. Whether you're part of a small team or a large organization, you'll find options that fit your specific requirements. Let's find the right tool to safeguard your data.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Database Security Software Summary
This comparison chart summarizes pricing details for my top database security software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for encrypted database access | 21-day free trial | From $199/user/year (billed annually) | Website | |
| 2 | Best for integrated cloud applications and platform services | Free demo available | Pricing upon request | Website | |
| 3 | Best for managed security services | Free demo available | Pricing upon request | Website | |
| 4 | Best for full disk and file encryption | 30-day free trial | Pricing upon request | Website | |
| 5 | Best for threat prevention across all networks | Free demo available | Pricing upon request | Website | |
| 6 | Best for real-time database monitoring | Not available | Pricing upon request | Website | |
| 7 | Best for centralized database vulnerability assessments | Not available | Pricing upon request | Website | |
| 8 | Best for data risk analytics and insights | Not available | Pricing upon request | Website | |
| 9 | Best for user behavior analytics | Not available | Pricing upon request | Website | |
| 10 | Best for comprehensive database performance monitoring | Not available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best Database Security Software Reviews
Below are my detailed summaries of the best database security software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
DbVisualizer gives you a unified workspace to explore, audit, and secure your databases without bouncing between multiple tools, which can be a relief when you’re responsible for keeping sensitive data environments under control. If you manage mixed data sources or oversee SQL work across teams, you’ll find that it brings structure and clarity to tasks that often feel scattered. It helps you stay focused on protecting data access while still giving you the flexibility to troubleshoot and analyze quickly.
Why I Picked DbVisualizer
I picked DbVisualizer for its strong emphasis on database security features: Controlled access, encrypted connections, and guardrails that protect sensitive information. You can connect through SSH tunnels to ensure encrypted data transfer, which reduces exposure when working across cloud or on-prem environments. You can also set user permissions within the tool to restrict data alteration, helping your team avoid risky changes. I appreciate that it even includes a local master password option, giving you a way to secure stored credentials on your machine rather than leaving them exposed.
DbVisualizer Key Features
In addition to its security features, DbVisualizer offers several tools that enhance database management:
- Visual Query Builder: Enables easy table manipulation and data visualization through a drag-and-drop interface.
- Reusable Queries: Allows users to save and reuse queries with variables and bookmarks for efficient database management.
- Performance Analytics: Provides insights into database performance to optimize operations and enhance user experience.
- Inline Editing: Facilitates direct data editing within the database, simplifying data management tasks.
DbVisualizer Integrations
Integrations include DB2, MariaDB, MySQL, Oracle, PostgreSQL, SQL Server, SQLite, Sybase, Vertica, and H2. An API is available for custom integrations.
Pros and Cons
Pros:
- Version control improves security and audit tracking of SQL scripts
- User permission controls reduce accidental data modifications
- Strong SSH encryption keeps remote connections secure
Cons:
- Permission controls require careful setup across teams
- Large result sets may slow performance during security reviews
New Product Updates from DbVisualizer
DbVisualizer Adds AI Assistant and New Database Support
DbVisualizer introduces an AI assistant, OS-native file chooser support, and new database compatibility with Impala and Neo4j. These updates help users write SQL faster, simplify file handling, and expand database connectivity. For more information, visit DbVisualizer’s official site.
Oracle is a titan in the world of database management systems, offering a comprehensive suite of tools that help businesses manage and secure their data. Known for its integration prowess, Oracle brings together cloud applications and platform services under a unified environment, a trait that proves pivotal for many enterprises.
Why I Picked Oracle:
In the process of evaluating various tools, Oracle consistently stood out for its comprehensive offerings. My judgment was driven by its established reputation and the opinions of countless industry professionals who laud its capabilities. Among the myriad offerings available, Oracle's distinct ability to integrate cloud applications and platform services set it apart, reinforcing my belief that it's truly the best for organizations seeking integration capabilities.
Standout Features & Integrations:
Oracle is renowned for its advanced security mechanisms, which encompass data encryption, data masking, and a robust firewall, ensuring a formidable defense against potential threats. Additionally, its machine-learning capabilities aid in activity monitoring and flagging anomalies. Integrations are a strong suit for Oracle; it effortlessly connects with cloud giants like AWS and Microsoft's Azure. Moreover, its compatibility extends to various operating systems, including Linux and Windows, thereby solidifying its position as a versatile database management system.z
Pros and Cons
Pros:
- Comprehensive integrations with major cloud providers and operating systems
- High scalability catered for both small businesses and large enterprises
- Robust data security solutions with advanced encryption and firewall
Cons:
- On-premises setup requires dedicated resources and maintenance.
- The depth of features can be overwhelming for simple tasks
- Might be complex for users new to database management systems
Trustwave specializes in providing advanced security solutions that are tailored to meet the unique needs of various organizations. Their managed security services are designed to offer a comprehensive protection strategy, ensuring that businesses are safeguarded from evolving threats. Their expertise in this particular domain justifies their reputation as the best for managed security services.
Why I Picked Trustwave:
When it came to selecting the right tool for managed security, Trustwave was among the top contenders. I chose Trustwave after thorough comparisons and determining that their approach to security solutions is both innovative and efficient. Their dedication to providing end-to-end managed services makes them stand out from the crowd. Given their longstanding reputation and proven track record, it's clear to see why they are "Best for..." managed security services.
Standout Features & Integrations:
Trustwave offers a robust security suite, including SIEM integration, advanced security controls against hackers, and activity monitoring to ensure real-time response to threats. They have also incorporated machine learning techniques to predict and prevent potential security risks. Trustwave's integrations are extensive; they work with major cloud providers like AWS and Azure and support integrations with popular database management systems like Oracle Database and PostgreSQL.
Pros and Cons
Pros:
- Adheres to GDPR guidelines ensuring data privacy alongside threat management
- Wide range of integrations with popular cloud providers and database systems, improving its adaptability
- Comprehensive managed security services that cover both on-premises and cloud-based environments.
Cons:
- The depth of services provided may introduce a learning curve for some IT teams
- Setup and initial configuration might be complex for businesses with simpler needs
- Some businesses might find the extensive features more than they require
Sophos SafeGuard Encryption is a comprehensive security tool designed to encrypt entire disks and individual files, ensuring they remain inaccessible to unauthorized users. Recognizing the crucial need to keep sensitive information out of the wrong hands, Sophos delivers top-tier encryption capabilities that are vital in the present digital age, solidifying its position as the go-to for full disk and file encryption.
Why I Picked Sophos SafeGuard Encryption:
In the maze of security products available, choosing the right one often comes down to its efficiency and reliability. After determining and comparing a slew of options, Sophos SafeGuard Encryption stood out to me primarily for its dual capacity: it doesn't just stop at full disk encryption but goes beyond to encrypt individual files. This unique combination is why I strongly feel it's "Best for..." businesses or individuals that need a holistic approach to their encryption strategy.
Standout Features & Integrations:
Sophos SafeGuard Encryption stands out with its advanced security features, providing robust protection against hackers and potential security threats. It uses key management systems efficiently, ensuring only authorized access to the encrypted data. Notably, the tool boasts of integrations with leading operating systems like Windows and Linux, as well as compatibility with cloud database systems such as AWS and Azure, expanding its utility across multiple platforms.
Pros and Cons
Pros:
- Extensive compatibility with leading operating systems and cloud databases offers flexibility in deployment.
- Robust key management ensures stringent access control to encrypted data.
- Dual capability for both full disk and file encryption improves overall security posture.
Cons:
- Some users may desire more granularity in encryption settings and controls.
- Interface might not be as user-friendly for newcomers in comparison to some competitors.
- Potential complexity in initial setup might require technical expertise.
Check Point provides a robust security posture for organizations, emphasizing the prevention of threats across varied networks. As cyber threats continue to evolve, Check Point stays at the forefront, making it an excellent choice for those who prioritize comprehensive threat prevention across all network environments.
Why I Picked Check Point:
During my research process, choosing the right tools was paramount, and Check Point caught my attention for its specialized focus on threat prevention. I judged its merits based on comprehensive comparisons, and it clearly emerged as a leader. What makes it particularly stand out is its holistic approach to security, covering every nook and cranny of an organization's network. Given its prowess, I confidently believe it's "Best for..." ensuring consistent threat prevention across all networks.
Standout Features & Integrations:
Check Point boasts an advanced security suite, with features including a top-tier firewall, SIEM integration, and advanced security protocols against hackers and potential misconfigurations in systems like MySQL. Its integrations are vast, connecting with major cloud providers such as AWS and Azure. Additionally, Check Point supports integrations with database servers, including Oracle Database, PostgreSQL, and more.
Pros and Cons
Pros:
- Comprehensive threat prevention across diverse networks, be it on-premises or cloud-based
- Broad integration capabilities, making it compatible with popular cloud providers and database systems
- Adherence to GDPR, ensuring data privacy is maintained while managing threats
Cons:
- For smaller organizations, the breadth of features might be more than required
- Depending on the setup, there might be complexities during the initial configuration
- The wide range of features might demand a steeper learning curve for IT teams
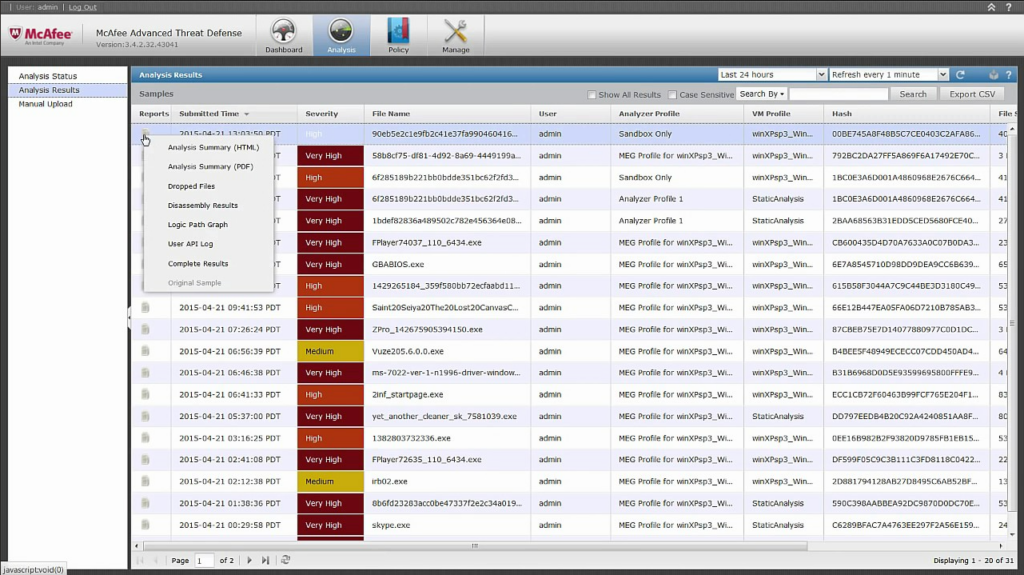
McAfee Database Security is a pivotal tool that ensures databases are shielded from potential threats, providing organizations with a safety net in an era of evolving cybersecurity challenges. Their expertise in real-time database monitoring makes them invaluable for enterprises that prioritize swift threat detection and instantaneous response.
Why I Picked McAfee Database Security:
In the midst of analyzing various security tools, McAfee's name echoed prominently. What fueled my decision to select this tool over others was its outstanding reputation in security solutions, coupled with the consistent feedback from professionals. McAfee distinctly outshines in delivering real-time database monitoring, making it my top choice for organizations that can't afford to have even the slightest delay in detecting security threats.
Standout Features & Integrations:
McAfee's prowess lies in its capability to provide real-time activity monitoring, ensuring swift detection of misconfigurations, SQL Injections, and unauthorized data access. This is further improved by their advanced security policies and a robust firewall that mitigates potential threats. McAfee Database Security integrates with SIEM systems, enabling businesses to have a comprehensive overview of their security posture. Further, its compatibility with major database servers, including MySQL and Oracle Database, amplifies its versatility.
Pros and Cons
Pros:
- Effective integrations with SIEM systems and major database servers
- Advanced security controls against SQL Injections and data breaches
- Strong real-time monitoring capabilities
Cons:
- Certain advanced features may have a steep learning curve
- Predominantly focuses on databases, which might necessitate additional tools for holistic security
- The interface might be intricate for newcomers
Fortinet FortiDB is a security product designed specifically to assess vulnerabilities across databases. As cyber threats continue to evolve, centralizing database vulnerability assessments becomes a crucial strategy, making FortiDB an essential tool in strengthening security measures.
Why I Picked Fortinet FortiDB:
When I was selecting the optimal security tool, Fortinet FortiDB caught my attention primarily due to its focus on centralized database vulnerability assessments. Compared to many other security products in the market, FortiDB distinguishes itself with a centralized approach, making vulnerability management more streamlined and comprehensive. Thus, I concluded that it is "Best for..." organizations that seek a centralized methodology for database vulnerability assessments, allowing them to bolster their security posture effectively.
Standout Features & Integrations:
Fortinet FortiDB boasts a robust set of features, including advanced security controls, activity monitoring, and data encryption capabilities that secure databases from potential threats. Its SIEM integration provides comprehensive logging and reporting, and the tool integrates with popular database management systems like Oracle Database, PostgreSQL, and MySQL. It's also designed to address common misconfigurations that might expose databases to hackers.
Pros and Cons
Pros:
- SIEM integration improves logging and reporting capabilities
- Integrates smoothly with popular database management systems
- Emphasizes centralized vulnerability assessments, streamlining security management
Cons:
- Requires periodic updates to keep abreast with evolving security threats
- Some features might require a steep learning curve for those unfamiliar with database security nuances
- Might be overkill for smaller businesses that don’t need centralized vulnerability management
Imperva Data Security emerges as a comprehensive solution designed to safeguard sensitive data while also offering deep analytical insights into potential risks. With the increasing importance of data management and security, Imperva excels by providing targeted analytics that aids businesses in understanding and mitigating potential vulnerabilities, justifying its reputation as the go-to tool for data risk analytics and insights.
Why I Picked Imperva Data Security:
My journey in selecting the right tools was intensive, and Imperva's offering stood out immediately. The choice became clear when I discerned its unparalleled focus on data risk analytics combined with insights that aren't typical of many providers. This unique combination makes Imperva distinctly superior. I've always believed that understanding risks is half the battle in security, and this tool, in my opinion, is "Best for..." businesses seeking not just protection but also clarity on their data vulnerabilities.
Standout Features & Integrations:
Imperva is lauded for its advanced security suite, particularly its capabilities in data encryption, data masking, and ensuring data privacy in line with GDPR. Additionally, its robust firewall protects against threats such as SQL Injection and other data breaches. Integrations are a key strength, with Imperva linking with cloud databases like AWS and Azure while also offering compatibility with popular database management systems, including Oracle Database, PostgreSQL, and MySQL.
Pros and Cons
Pros:
- Comprehensive firewall and security controls, ensuring protection against modern threats
- Broad integration with popular cloud providers and database systems
- Advanced data analytics offering deeper insights into vulnerabilities
Cons:
- As a comprehensive suite, it might be overkill for organizations with limited data management needs
- Some features might have a learning curve, especially for smaller teams
- Might be overwhelming for businesses only seeking basic security solutions
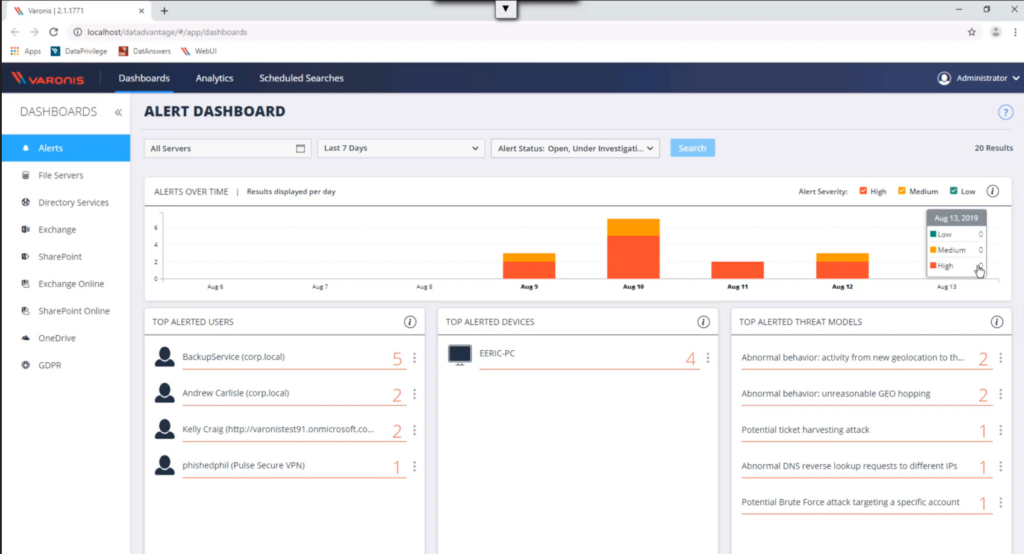
Varonis Data Security Platform is a comprehensive security solution that centers on monitoring and analyzing user behavior to prevent potential data breaches. Given the increasing importance of understanding user patterns to fortify security, Varonis excels at leveraging user behavior analytics as its main defense mechanism.
Why I Picked Varonis Data Security Platform:
In the process of determining the right tool for this list, I gravitated towards Varonis due to its distinct approach to security using user behavior analytics. Many platforms offer generic security solutions, but Varonis stands out because of its specialized focus on analyzing user patterns. I am of the firm opinion that it is "Best for..." organizations that want to emphasize user behavior analytics for bolstering their security posture.
Standout Features & Integrations:
One of the core features of Varonis is its advanced user activity monitoring, which provides real-time insights into any unusual patterns. This is complemented by its data encryption and data masking capabilities that add an additional layer of security. Its integration landscape is expansive, working in harmony with popular cloud providers like AWS and Azure, and is also compatible with database servers like Oracle Database and PostgreSQL.
Pros and Cons
Pros:
- Specialized in user behavior analytics, offering a unique approach to data security
- Extensive activity monitoring tools backed by machine learning for improved threat detection
- Compatibility with a broad range of cloud database providers and database management systems
Cons:
- Some features might be redundant for smaller businesses that only need basic security solutions
- Requires consistent updates to adapt to evolving security landscapes
- Might have a learning curve for businesses that are new to user behavior analytics tools
Best for comprehensive database performance monitoring
SolarWinds Database Management is a robust tool that allows users to monitor, optimize, and improve database performance. With the increasing complexity of database ecosystems, having a solution that offers a holistic view of database health and performance is crucial, and that's where SolarWinds shines.
Why I Picked SolarWinds Database Management:
In my process of selecting database management tools, I was particularly drawn to SolarWinds due to its comprehensive approach to monitoring database performance. Among the plethora of tools I compared, SolarWinds stood out because of its intricate detailing and all-encompassing perspective on database health. I determined that it truly is "Best for..." those who need an overarching view of their database's performance and want to take preemptive measures based on detailed insights.
Standout Features & Integrations:
SolarWinds offers a myriad of features, from advanced security mechanisms to in-depth activity monitoring. Its ability to identify potential SQL Injection threats and provide data masking ensures data privacy and security. Integrating with a variety of database servers such as Oracle Database, PostgreSQL, and MySQL, it offers versatility to cater to diverse database management systems. The tool also incorporates cloud data functionalities, enabling a smooth transition for those using cloud database solutions.
Pros and Cons
Pros:
- Comprehensive monitoring capabilities provide a holistic view of database performance
- Integration with various database servers ensures compatibility and versatility
- Advanced security features, including data masking and SQL Injection threat detection, bolster security posture
Cons:
- May come with a steeper learning curve for beginners due to its extensive features
- Some users might experience challenges with customization and tweaking to specific needs
- The comprehensive nature might be overwhelming for users seeking simpler solutions
Other Database Security Software
Here are some additional database security software options that didn’t make it onto my shortlist, but are still worth checking out:
- NetApp Data Protection
For scalable data backup solutions
- Digital Guardian Data Protection
For data loss prevention tasks
- DataSunrise
For automated data protection
- CrowdStrike Falcon
Good for endpoint threat detection
- Idera SQL Compliance Manager
Good for SQL server auditing
- Tenable
Good for risk-based vulnerability management
- Alert Logic
Good for managed detection and response
- AppGuard
Good for proactive malware blocking
- Cloudera Navigator
Good for big data security and governance
- Trend Micro Data Protection
Good for hybrid cloud security
- Protegrity Data Protection
Good for enterprise data-centric security
- Qualys Cloud Platform
Good for vulnerability management at scale
- Kaspersky Data Center Security
Good for safeguarding complex infrastructures
Database Security Software Selection Criteria
When selecting the best database security software to include in this list, I considered common buyer needs and pain points like protecting sensitive data and ensuring compliance with regulations. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Monitor database activity
- Detect and prevent unauthorized access
- Ensure data encryption
- Provide audit trails
- Support compliance reporting
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Automated threat detection
- Real-time alerts
- Integration with SIEM systems
- User behavior analytics
- Cross-platform support
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface design
- Ease of navigation
- Customizable dashboards
- Speed of setup
- Accessibility across devices
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Availability of templates
- Onboarding support and chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multichannel support options
- Responsiveness to inquiries
- Availability of support documentation
- Access to a dedicated support team
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Pricing transparency
- Comparison with competitors
- Features included in base price
- Availability of free trials
- Scalability of pricing plans
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Frequency of positive feedback
- Commonly mentioned issues
- User testimonials
- Feedback on customer support experience
How to Choose Database Security Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your organization? Consider future database size, user numbers, and data volume. Look for tiered pricing or scalable features. |
| Integrations | Does it work with your existing systems? Check for compatibility with databases, cloud services, and security tools. Avoid manual integration pitfalls. |
| Customizability | Can you tailor the software to your needs? Look for options to adjust settings, reports, and alerts to fit your workflows. |
| Ease of use | Is the interface intuitive for your team? Test for simple navigation and user-friendly design to ensure quick adoption by all team members. |
| Implementation and onboarding | How quickly can you get started? Evaluate training resources, product tours, and support during setup to minimize disruption. |
| Cost | Does the pricing fit your budget? Compare subscription fees, hidden costs, and available discounts to ensure affordability. |
| Security safeguards | Does it meet your security standards? Verify encryption, access controls, and data protection features to safeguard sensitive information. |
| Compliance requirements | Does it support your regulatory needs? Check for built-in compliance reporting and support for industry-specific regulations. |
What Is Database Security Software?
Database security software is designed to protect databases from threats like unauthorized access and data breaches. IT professionals, database administrators, and security teams generally use these tools to ensure data integrity and compliance. Encryption, access controls, data masking software, and audit trails help with safeguarding data, monitoring activity, and meeting regulatory standards. These tools provide essential protection and peace of mind for organizations managing sensitive information.
Features
When selecting database security software, keep an eye out for the following key features:
- Encryption: Protects data by converting it into a secure format, ensuring that only authorized users can access sensitive information.
- Access controls: Manages user permissions to prevent unauthorized access to the database, helping maintain data integrity.
- Audit trails: Tracks database activity and changes, providing a record for compliance and forensic analysis.
- Real-time alerts: Notifies security teams of suspicious activities or potential threats, enabling quick response to protect data.
- User behavior analytics: Monitors patterns in user activity to detect anomalies that may indicate security breaches.
- Compliance reporting: Provides tools for generating reports to demonstrate adherence to industry regulations and standards.
- Integration capabilities: Works seamlessly with existing systems and security tools to enhance overall data protection.
- Automated threat detection: Uses algorithms to identify potential threats and vulnerabilities without manual intervention.
- Customizable dashboards: Allow users to tailor the interface to display relevant security metrics and insights.
- Cross-platform support: Ensures compatibility with various database systems and environments, providing flexibility for diverse IT infrastructures.
Benefits
Implementing database security software provides several benefits for your team and your business. Here are a few you can look forward to:
- Data protection: Keeps sensitive information safe from breaches with encryption and access controls.
- Regulatory compliance: Helps meet industry standards through compliance reporting and audit trails.
- Threat detection: Identifies potential security threats with real-time alerts and automated threat detection.
- User accountability: Monitors user actions with audit trails, ensuring accountability and traceability.
- Operational efficiency: Reduces manual security tasks by automating threat detection and reporting.
- Risk mitigation: Minimizes the impact of potential data breaches with user behavior analytics and access management.
- Security insights: Provides valuable insights into security posture through customizable dashboards and reports.
Costs & Pricing
Selecting database security software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in database security software solutions:
Plan Comparison Table for Database Security Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited access controls, and community support. |
| Personal Plan | $5-$25/user/month | User access management, basic encryption, and email support. |
| Business Plan | $30-$75/user/month | Advanced threat detection, compliance reporting, and priority support. |
| Enterprise Plan | $100-$250/user/month | Custom integrations, full audit trails, dedicated account manager, and 24/7 support. |
Database Security Software FAQs
Here are some answers to common questions about database security software:
How does database security software protect against unauthorized access?
Database security software uses encryption, access controls, and user authentication to prevent unauthorized access. You can set permissions for different users, ensuring that only those with the right credentials can access sensitive data. Regular audits also help identify any unauthorized access attempts.
What are the common challenges when implementing database security software?
Implementation challenges may include compatibility with existing systems, the complexity of setup, and the need for staff training. It’s important to plan for these issues by seeking vendors that offer strong support and clear onboarding processes to ease the transition.
Do these tools only support specific databases?
While some database security tools are designed for specific database systems like Oracle Database or PostgreSQL, many others are versatile and support multiple database management systems, both on-premises and cloud-based.
How often should database security measures be updated?
Security measures should be updated regularly to protect against new threats. Many tools offer automated updates and threat detection to keep your database secure. It’s wise to review your security policies periodically and adjust them as necessary to address evolving risks.
What’s Next:
If you're in the process of researching database security software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.