Best DAST Tools Shortlist
Here’s my shortlist of the best DAST tools:
The best DAST tools help security and engineering teams identify exploitable vulnerabilities in live applications, validate fixes against real-world attack patterns, and maintain continuous visibility into runtime risk. By testing software from the outside in, they surface flaws that static scans can’t catch, such as authentication bypasses, misconfigured headers, and injection points that only appear under specific runtime conditions.
Many teams adopt DAST after hitting operational roadblocks like chasing false positives from static scans, struggling to reproduce issues in staging, or wasting hours reviewing unprioritized findings. Without runtime-focused testing, these blind spots can slip into production undetected.
I’ve evaluated DAST platforms directly in active CI/CD pipelines, assessed their integration with common deployment frameworks, and worked with teams replacing legacy scanners that stalled releases. These hands-on tests revealed which tools fit seamlessly into real build cycles and produce actionable, prioritized results.
In this guide, you’ll see which DAST tools provide the clearest vulnerability context, integrate cleanly with modern workflows, and actually help reduce noise so your team can focus on fixing what matters.
Why Trust Our Software Reviews
Best DAST Tools Summary
This comparison chart summarizes pricing details for my top DAST tools selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for AI-based vulnerability discovery | Free demo available | Pricing upon request | Website | |
| 2 | Best for compliance needs | Free demo available | From $69/month | Website | |
| 3 | Best for small businesses | 14-day free trial + free demo available | From $149/month | Website | |
| 4 | Best for authenticated DAST | Free plan available + free demo | From $350/month | Website | |
| 5 | Best for automated scanning | Free demo available | Pricing upon request | Website | |
| 6 | Best for detailed reports | Free demo available | Pricing upon request | Website | |
| 7 | Best for continuous DAST in dev cycles | Free demo available | Pricing upon request | Website | |
| 8 | Best for cloud integration | Free trial available | Pricing upon request | Website | |
| 9 | Best for real-time analysis | Free demo available | Pricing upon request | Website | |
| 10 | Best for enterprise solutions | Free demo available | Pricing upon request | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best DAST Tool Reviews
Below are my detailed summaries of the best DAST tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
For teams working through application security challenges, Escape provides a DAST solution focused on AI-based vulnerability discovery. It helps identify security issues while accounting for application logic, which is useful for testing APIs and web applications. Escape provides broader security testing coverage, helping teams better protect their software from emerging risks.
Why I Picked Escape
I picked Escape for its AI-based vulnerability discovery, which helps identify security issues that basic scanners can miss, especially in applications with complex logic. It also integrates with CI/CD pipelines, so teams can run security tests as part of regular development work. This makes it easier to maintain consistent security checks without slowing down releases.
Escape Key Features
In addition to its standout AI-driven testing, Escape offers:
- API Discovery & Security: Escape offers a platform for discovering, documenting, and securing your APIs, ensuring they are protected throughout their lifecycle.
- GraphQL Security Testing: With native GraphQL support, the tool helps secure this increasingly popular API format.
- Custom Security Checks: You can create tailored tests to suit specific security requirements, providing flexibility and precision in your security strategy.
- Compliance Management: Simplifies report generation and compliance with industry standards.
Escape Integrations
Integrations include GitHub, GitLab, Jenkins, AWS, Azure DevOps, Jira, Bitbucket, Slack, Trello, and Confluence.
Pros and Cons
Pros:
- Continuous scanning and verification that support ongoing security monitoring
- Seamless integrations that fit into existing development and security workflows
- Strong API vulnerability detection, including coverage for REST and GraphQL endpoints
Cons:
- Platform upgrades can take time to apply and adapt to
- Setup process can be complex and may require configuration adjustments
Astra Pentest is a Dynamic Application Security Testing (DAST) tool for engineering teams. It excels in integrating with CI/CD pipelines and conducting extensive security tests, including the OWASP Top 10 and known vulnerabilities.
Why I picked Astra Pentest: Its focus on compliance needs makes it ideal for businesses adhering to standards like ISO 27001 and GDPR. The tool's AI-driven intelligence ensures tailored testing, while authenticated scanning offers comprehensive coverage. Continuous security monitoring aids in maintaining compliance, and its ability to scan behind login pages adds depth to its testing capabilities.
Standout features & integrations:
Features include AI-powered intelligence for specific testing needs, authenticated scanning for thorough assessments, and continuous monitoring to keep your applications secure. It also offers compliance simplification with major standards.
Integrations include Slack, Jira, GitHub, GitLab, Bitbucket, AWS, Azure, and Trello.
Pros and Cons
Pros:
- Compliance reporting capabilities
- Continuous learning from real pentests
- AI-driven vulnerability detection
Cons:
- Not suited for very large enterprises
- Limited offline support
Intruder is a cloud security platform for small businesses seeking continuous vulnerability management. It provides external, internal, cloud, web application, and API vulnerability scanning to help organizations identify security weaknesses. Users benefit from detailed reporting and compliance features.
Why I picked Intruder: It's perfect for small businesses due to its focus on comprehensive vulnerability scanning, which includes external and internal assessments. Intruder's detailed reporting helps you understand and address security issues effectively. The platform's compliance features are ideal for meeting regulatory requirements. Its private bug bounty service adds another layer of security by identifying vulnerabilities that traditional scanners might miss.
Standout features & integrations:
Features include private bug bounty services to discover hidden vulnerabilities, detailed compliance reporting to satisfy regulatory needs, and proactive change detection to maintain security as your organization grows.
Integrations include Slack, Jira, AWS, Azure, Google Cloud, Zapier, Microsoft Teams, Splunk, ServiceNow, and PagerDuty.
Pros and Cons
Pros:
- Responsive customer support
- Easy setup process
- Effective vulnerability testing
Cons:
- Limited customization options
- May require technical knowledge
New Product Updates from Intruder
Intruder GregAI Adds Persistent Chat History
Intruder introduces persistent chat history with GregAI, enhancing user experience by maintaining conversation threads even after closing the chat. For more information, visit Intruder's official site.
Aikido Security is a DAST tool focused on surface monitoring, serving security teams and IT departments. It helps identify and manage vulnerabilities across web applications and APIs.
Why I picked Aikido Security: It's tailored for surface monitoring, offering features like continuous scanning and real-time alerts. The tool's ability to map and assess your digital assets provides a clear view of your security posture. Its user-friendly interface simplifies monitoring tasks, making it accessible for teams with varying levels of expertise. Aikido's detailed analytics further enhance its monitoring capabilities.
Standout features & integrations:
Features include continuous scanning to keep your systems secure, real-time alerts to notify your team of threats, and a user-friendly interface that simplifies monitoring. Detailed analytics provide insights into your security posture.
Integrations include Slack, Jira, GitHub, GitLab, Bitbucket, AWS, Azure, and Microsoft Teams.
Pros and Cons
Pros:
- Effective surface monitoring
- Real-time threat alerts
- User-friendly interface
Cons:
- May require technical expertise
- Limited offline functionality
New Product Updates from Aikido Security
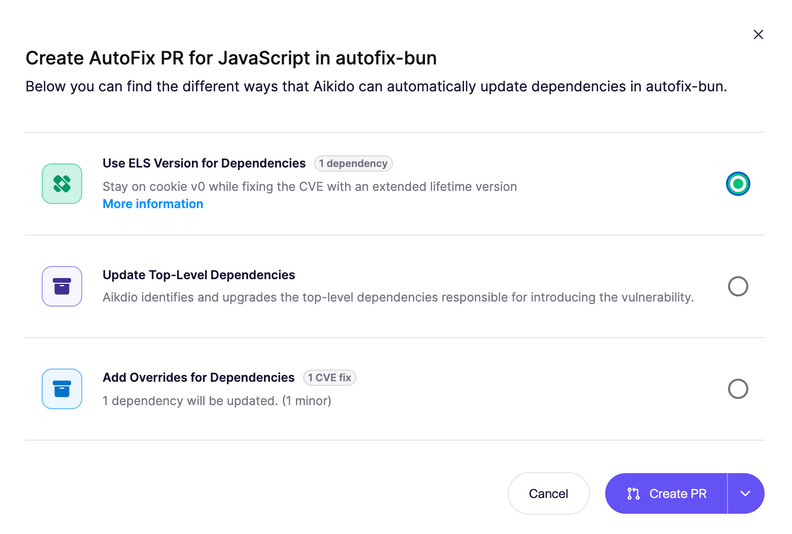
Aikido Security Introduces AI Fix Prompts and Pentest Modeling
Aikido Security introduces new features including AI-powered fix prompts, real-time pentest threat modeling, and Alibaba Cloud support to strengthen application security workflows. For more information, visit Aikido Security’s official site.
Invicti is a DAST tool designed for development and security teams focusing on automated scanning and vulnerability management. It helps identify and remediate vulnerabilities in web applications and services efficiently.
Why I picked Invicti: The tool excels in automated scanning, offering features like proof-based scanning to verify vulnerabilities. It provides detailed reports that help your team prioritize remediation efforts. Invicti's scalability ensures it adapts to your organization's needs, making it suitable for teams of all sizes. The tool's ease of integration with development workflows enhances its appeal for continuous security testing.
Standout features & integrations:
Features include proof-based scanning to confirm vulnerabilities, detailed reporting to guide remediation, and scalability to grow with your organization. The tool also integrates easily with development workflows for continuous testing.
Integrations include Jira, Jenkins, GitHub, GitLab, Bitbucket, Azure DevOps, ServiceNow, Slack, Trello, and Microsoft Teams.
Pros and Cons
Pros:
- Proof-based scanning confirmation
- Scalable for growing organizations
- Easy integration with workflows
Cons:
- Initial setup complexity
- High starting cost
New Product Updates from Invicti
Invicti Enterprise Adds WebLogic Support and Security Enhancements
The latest Invicti Enterprise v25.10.0 release introduces WebLogic support for Java Shark sensors and improved secrets management through SEM integrations. It also refines API consistency and strengthens overall platform stability. For more information, visit Invicti's official site.
Acunetix is a DAST tool tailored for security teams and developers focusing on web application security. It efficiently scans and identifies vulnerabilities, providing detailed insights for remediation.
Why I picked Acunetix: The tool excels in generating detailed reports that help your team address security issues comprehensively. Its advanced scanning engine detects a wide range of vulnerabilities, including SQL Injection and XSS. Acunetix's ability to scan both web applications and APIs adds value to your security strategy. The tool's user-friendly interface ensures that even those with limited security expertise can benefit from its features.
Standout features & integrations:
Features include advanced scanning capabilities to detect vulnerabilities, a user-friendly interface for ease of use, and support for scanning both web applications and APIs. The tool also offers detailed vulnerability reports to guide your remediation efforts.
Integrations include Jira, Jenkins, GitHub, GitLab, Bitbucket, Microsoft Teams, ServiceNow, Slack, Azure DevOps, and Bamboo.
Pros and Cons
Pros:
- Supports web and API scanning
- Detailed vulnerability reports
- Advanced scanning capabilities
Cons:
- Not ideal for very large enterprises
- Occasional false positives
You want a DAST solution that helps you uncover real vulnerabilities in your live web applications without waiting for the next pentesting cycle, and DerScanner meets you right at that need. It gives your team a way to test running applications the same way an attacker would, helping you spot issues earlier and reduce the expensive rework often uncovered in late-stage pentests.
Why I Picked DerScanner
I picked DerScanner because it treats DAST not as an occasional security exercise but as a repeatable process you can embed directly into your development cycles. Its real-time scanning against live applications lets you uncover issues like SQL injection, XSS, and configuration flaws without needing source-code access, making it a strong fit for teams securing both first-party and third-party apps. I also like that it pairs DAST with interactive analysis, correlating dynamic findings with static ones so you focus on vulnerabilities that are both visible in code and exploitable in practice.
DerScanner Key Features
In addition to its unique DAST capabilities, DerScanner offers several other features that enhance its utility as a security tool:
- Traditional and Passive Scanners: These tools help detect vulnerabilities in real-time without needing access to the source code.
- AJAX Web Scanners: Specialized scanners designed to identify vulnerabilities in web applications that use AJAX technologies.
- Automatic Scanners: Automated scanning at regular intervals to continuously check for new vulnerabilities without manual intervention.
- Fuzzers: Tools that test the robustness of applications by inputting unexpected or random data to identify potential weaknesses.
DerScanner Integrations
Integrations include GitHub, GitLab, Bitbucket for VCS hosting, GitLab CI, Azure DevOps Server, TeamCity, Jenkins, IntelliJ IDEA, Eclipse, Visual Studio, SonarQube, and Jira.
Pros and Cons
Pros:
- Supports on-premises deployment for code privacy control.
- Shows correlations between static and dynamic findings.
- Catches runtime vulnerabilities with dynamic attack simulations.
Cons:
- Some integrations require scripting or manual configuration.
- May be complex to set up for small teams with limited security expertise.
Qualys Web Application Scanning is a DAST tool designed for security and IT teams, focusing on identifying vulnerabilities in web applications. It offers comprehensive scanning capabilities to keep your web applications secure.
Why I picked Qualys Web Application Scanning: It's ideal for cloud integration, providing seamless connectivity to your cloud services. The tool's comprehensive scanning capabilities ensure your applications remain secure in dynamic environments. With its ability to detect both known and unknown vulnerabilities, it offers robust protection. Its cloud-based architecture allows for easy scaling as your organization grows.
Standout features & integrations:
Features include comprehensive scanning capabilities that detect known and unknown vulnerabilities, a cloud-based architecture for easy scaling, and robust protection for dynamic environments. It also offers detailed reporting to guide remediation efforts.
Integrations include ServiceNow, Splunk, AWS, Azure, Google Cloud, Jira, IBM QRadar, McAfee ePolicy Orchestrator, Tenable, and Microsoft Teams.
Pros and Cons
Pros:
- Comprehensive vulnerability scanning
- Easy cloud integration
- Scalable for growing businesses
Cons:
- Limited offline functionality
- Initial setup complexity
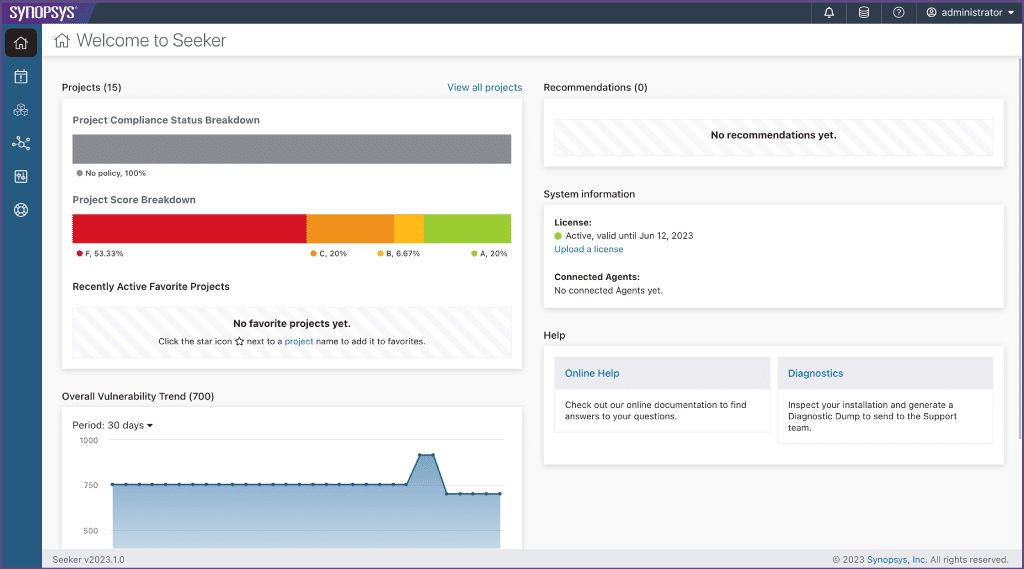
Synopsys Seeker is an interactive application security testing (IAST) tool designed for developers and security professionals. It provides real-time analysis and feedback on security vulnerabilities in web applications during runtime.
Why I picked Synopsys Seeker: It excels in real-time analysis, offering insights during the development lifecycle. This helps your team address vulnerabilities as they occur, reducing the time to remediation. Seeker's ability to provide detailed insights into data flows and security issues enhances its value. Its integration with CI/CD pipelines makes it a practical choice for continuous testing environments.
Standout features & integrations:
Features include runtime vulnerability detection to catch issues early, detailed insights into data flows for better understanding, and integration with CI/CD pipelines for continuous testing. It also provides actionable feedback to guide developers in fixing vulnerabilities.
Integrations include Jenkins, Jira, GitHub, GitLab, Azure DevOps, Bamboo, Bitbucket, TeamCity, Rally, and Slack.
Pros and Cons
Pros:
- Real-time vulnerability analysis
- Detailed data flow insights
- Supports continuous testing environments
Cons:
- High learning curve
- Not ideal for small teams
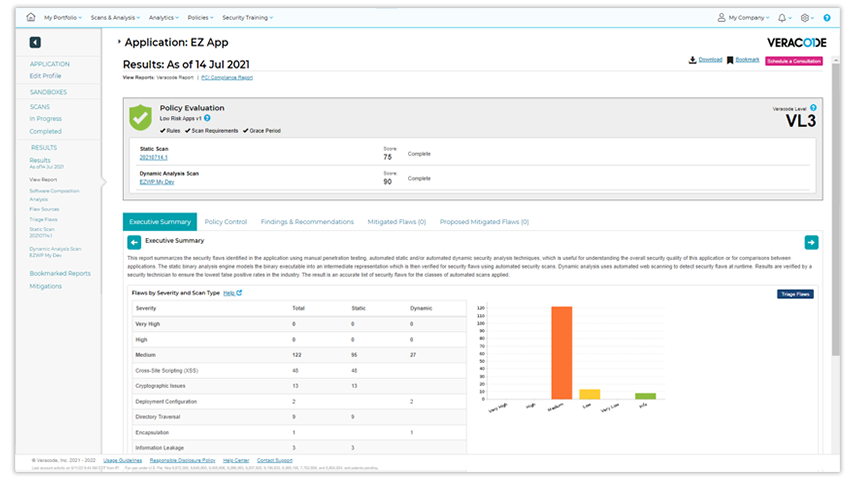
Veracode is an application security platform for enterprise-level security teams, focusing on comprehensive code analysis. It helps organizations secure their applications by identifying vulnerabilities in both static and dynamic code.
Why I picked Veracode: It’s tailored for enterprise solutions, offering comprehensive security for complex environments. Veracode provides both static and dynamic analysis, ensuring thorough coverage of your codebase. Its detailed reporting helps your team prioritize vulnerabilities effectively. The platform's scalability makes it suitable for large organizations with extensive security needs.
Standout features & integrations:
Features include comprehensive static and dynamic code analysis, detailed vulnerability reporting to help prioritize issues, and scalability to support large organizations. The platform also offers comprehensive security for complex environments.
Integrations include Jira, Jenkins, GitHub, GitLab, Azure DevOps, Bitbucket, ServiceNow, Bamboo, Slack, and Visual Studio.
Pros and Cons
Pros:
- Comprehensive code analysis
- Suitable for large organizations
- Scalable for enterprise needs
Cons:
- Initial setup complexity
- Not ideal for small teams
Other DAST Tools
Here are some additional DAST tools options that didn’t make it onto my shortlist, but are still worth checking out:
- Detectify
For continuous updates
- AppCheck
For UK-based support
- Mend.io
For SLDC application security
- NowSecure
For mobile app security
- Probely
For agile development teams
- ImmuniWeb
For compliance testing
- Nessus
For vulnerability assessment
- Wireshark
For network protocol analysis
- Checkmarx
For static and interactive application security testing
- Contrast Security
For real-time application monitoring
- Pentest-Tools.com
For quick security audits
- CyCognito
For discovering unknown assets
- OWASP ZAP (Zed Attack Proxy)
For open-source enthusiasts
- Portswigger Burp Suite
For penetration testers
- Rapid7 AppSpider
For continuous scanning
- IBM Security AppScan
For large-scale applications
- Micro Focus Fortify WebInspect
For enterprise-level security
- Radware AppWall
For web application firewall
- Wallarm FAST
For API security testing
- CloudDefense
For cloud-native security
DAST Tool Selection Criteria
When selecting the best DAST tools to include in this list, I considered common buyer needs and pain points like vulnerability detection accuracy and integration with development workflows. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detecting vulnerabilities in web applications
- Providing detailed security reports
- Integrating with CI/CD pipelines
- Supporting multiple web technologies
- Offering automated scanning capabilities
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat intelligence updates
- Ability to scan behind login pages
- Customizable security policies
- Advanced data flow analysis
- Integration with cloud environments
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface design
- Ease of navigation through features
- Complexity vs. power balance
- Availability of user guides and documentation
- Customizable dashboards and reports
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos and tutorials
- Interactive product tours for new users
- Templates to speed up setup
- Access to webinars and workshops
- Support from chatbots or live agents
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- Availability of 24/7 support channels
- Responsiveness to customer inquiries
- Access to a knowledge base or help center
- Personalized support options
- Community forums for peer support
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing compared to features
- Availability of flexible pricing plans
- Cost-effectiveness for small vs. large teams
- Transparency in pricing structure
- Discounts for long-term commitments
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Consistency in positive feedback
- Commonly mentioned strengths and weaknesses
- Frequency of updates and improvements
- Overall satisfaction ratings
- User feedback on support and service quality
How to Choose DAST Tools
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
| Scalability | Ensure the tool can grow with your organization. Look for solutions that handle increasing workloads and more users as your team expands. |
| Integrations | Check compatibility with your existing systems, like CI/CD pipelines, issue trackers, and cloud platforms, to streamline your workflow. |
| Customizability | Look for tools that allow adjustments to suit your specific security policies and reporting needs, ensuring they align with your team’s workflows. |
| Ease of Use | Consider the learning curve and how quickly your team can get up to speed. Intuitive interfaces and comprehensive documentation are key. |
| Budget | Evaluate the total cost of ownership, including any additional fees for integrations or support. Make sure it fits within your team’s financial constraints. |
| Security Safeguards | Verify the tool’s ability to handle sensitive data and its compliance with industry standards like GDPR, ensuring your security measures are up to date. |
| Support | Assess the level of customer support available, such as 24/7 assistance or dedicated account managers, to help resolve issues promptly. |
| Performance | Test the tool’s speed and accuracy in detecting vulnerabilities, ensuring it meets your team’s needs for timely and reliable security assessments. |
What Are DAST Tools?
DAST tools are software solutions that scan web applications to find security vulnerabilities. Security professionals and developers generally use these tools to enhance the security posture of their applications.
Automated scanning, real-time alerts, and detailed reporting capabilities help with identifying and fixing vulnerabilities efficiently. These solutions along with enterprise penetration testing tools provide immense value by ensuring applications are secure against potential threats.
Features of DAST Tools
When selecting DAST tools, keep an eye out for the following key features:
- Automated scanning: This feature automatically scans web applications for vulnerabilities, saving time and ensuring thorough coverage.
- Real-time alerts: Provides instant notifications about detected vulnerabilities, allowing your team to respond quickly to potential threats.
- Detailed reporting: Offers comprehensive reports that help prioritize remediation efforts and track security improvements over time.
- Integration capabilities: Connects with existing systems like CI/CD pipelines and issue trackers to streamline workflows and enhance productivity.
- Customizability: Allows users to tailor the tool to fit their specific security policies and reporting needs, ensuring it aligns with organizational workflows.
- Scalability: Supports growing teams and workloads, making it suitable for organizations of all sizes.
- Compliance support: Ensures that security measures meet industry standards like GDPR, keeping your organization compliant.
- User-friendly interface: Provides an intuitive design that reduces the learning curve and helps teams quickly get up to speed.
- Vulnerability detection accuracy: Ensures precise identification of security issues, minimizing false positives and focusing on real threats.
- Cloud compatibility: Works effectively with cloud environments, offering flexibility for businesses operating in the cloud.
Benefits of DAST Tools
Implementing DAST tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security: By detecting vulnerabilities early, these tools help prevent security breaches and protect sensitive data.
- Time efficiency: Automated scanning saves your team time by continuously monitoring applications without manual intervention.
- Compliance readiness: Ensures your security practices meet industry standards, making compliance audits smoother and less stressful.
- Cost savings: Identifying and fixing vulnerabilities early reduces the potential costs associated with security breaches and data loss.
- Enhanced productivity: Integration with existing systems streamlines workflows, allowing your team to focus on other critical tasks.
- Scalability: Supports growing businesses by adapting to increased workloads and larger teams without sacrificing performance.
- Actionable insights: Detailed reports provide clear guidance on addressing vulnerabilities, helping your team prioritize remediation efforts effectively.
Costs and Pricing of DAST Tools
Selecting DAST tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in DAST tools solutions:
Plan Comparison Table for DAST Tools
| Plan Type | Average Price | Common Features |
| Free Plan | $0 | Basic vulnerability scanning, limited reporting, and community support. |
| Personal Plan | $10-$30 /user /month | Automated scanning, basic integrations, and email support. |
| Business Plan | $50-$100 /user /month | Advanced scanning capabilities, comprehensive reporting, API access, and priority support. |
| Enterprise Plan | $150-$300/user /month | Customizable security policies, dedicated account manager, extensive integrations, and 24/7 support. |
DAST Tools FAQs
Here are some answers to common questions about DAST tools:
Is it true that DAST tools review source code?
No, DAST tools don’t review your application’s source code. Instead, they analyze running applications from the outside, identifying security flaws by simulating real attacks. To review your source code, you’d use SAST tools, which look at the code itself.
How do DAST tools differ from SAST tools?
DAST tools test your application in its running state, finding security issues visible from the outside. SAST tools analyze your source code before deployment to catch flaws early. Using both types together gives you a more complete view of your application’s security.
Can DAST tools integrate with CI/CD pipelines?
Yes, most modern DAST tools easily integrate with CI/CD pipelines. This lets you automate scanning for vulnerabilities every time code is pushed or deployed, helping you catch issues before they reach production.
What challenges might I face when implementing DAST tools?
You might face challenges like false positives, configuration overhead, and limited visibility into business logic flaws. It’s important to fine-tune scan parameters and educate your team to get value from your DAST investment.
How can I reduce false positives with DAST tools?
You can reduce false positives by refining scan settings, updating attack signatures, and validating results manually or with SAST. Regularly reviewing and adjusting exclusions will focus your results on real, actionable risks.
Are DAST tools suitable for testing APIs and microservices?
Yes, many DAST tools now support APIs and microservices, but you’ll get the best results by choosing a tool built with modern application architectures in mind. Check for OpenAPI/Swagger integration and multi-endpoint coverage.
What kinds of vulnerabilities do DAST tools detect best?
DAST tools are strongest at catching runtime issues like SQL injection, cross-site scripting, insecure authentication, and misconfigurations. But they may miss vulnerabilities like business logic flaws or those hidden in inaccessible code paths.
What's Next?
If you're in the process of researching DAST tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.