Best Cybersecurity Solutions Shortlist
Here’s my shortlist of the best cybersecurity solutions:
In today's digital landscape, safeguarding your data and systems is more important than ever. Cybersecurity threats are evolving, making it tough to keep up. You need reliable solutions that protect without complicating your workflow.
I've spent years testing and reviewing software, and I know what works. In my experience, the right cybersecurity tools can make a big difference in your team's efficiency and peace of mind.
In this article, I'll share my top picks for cybersecurity solutions. You'll get an unbiased look at each option, focusing on what truly matters: effectiveness, ease of use, and value. Let's find the best fit for your needs.
Why Trust Our Software Reviews
Best Cybersecurity Solutions Summary
This comparison chart summarizes pricing details for my top cybersecurity solutions selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for AI-powered ransomware detection | Free demo available | From $179.99/endpoint (billed annually) | Website | |
| 2 | Best for compliance testing | Free demo available | From $69/month | Website | |
| 3 | Best for integrated security controls | Free demo available | Pricing upon request | Website | |
| 4 | Best for API attack protection | 30-day free trial available | Pricing upon request | Website | |
| 5 | Best managed SOC for small teams | Free demo available | Pricing upon request | Website | |
| 6 | Best for government solutions | Not available | Pricing upon request | Website | |
| 7 | Best for zero-trust application control | 30-day free trial + free demo available | Pricing upon request | Website | |
| 8 | Best for enterprise network security | 30-day free trial + free demo available | Pricing upon request | Website | |
| 9 | Best for securing industrial IoT environments | Not available | Pricing upon request | Website | |
| 10 | Best for global DDoS and attack surface defense | Free trial + free demo available | Pricing upon request | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit Website -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Cybersecurity Solution Reviews
Below are my detailed summaries of the best cybersecurity solutions that made it onto my shortlist. My reviews offer a detailed look at the key features, pros and cons, integrations, and ideal use cases of each tool to help you find the best one for you.
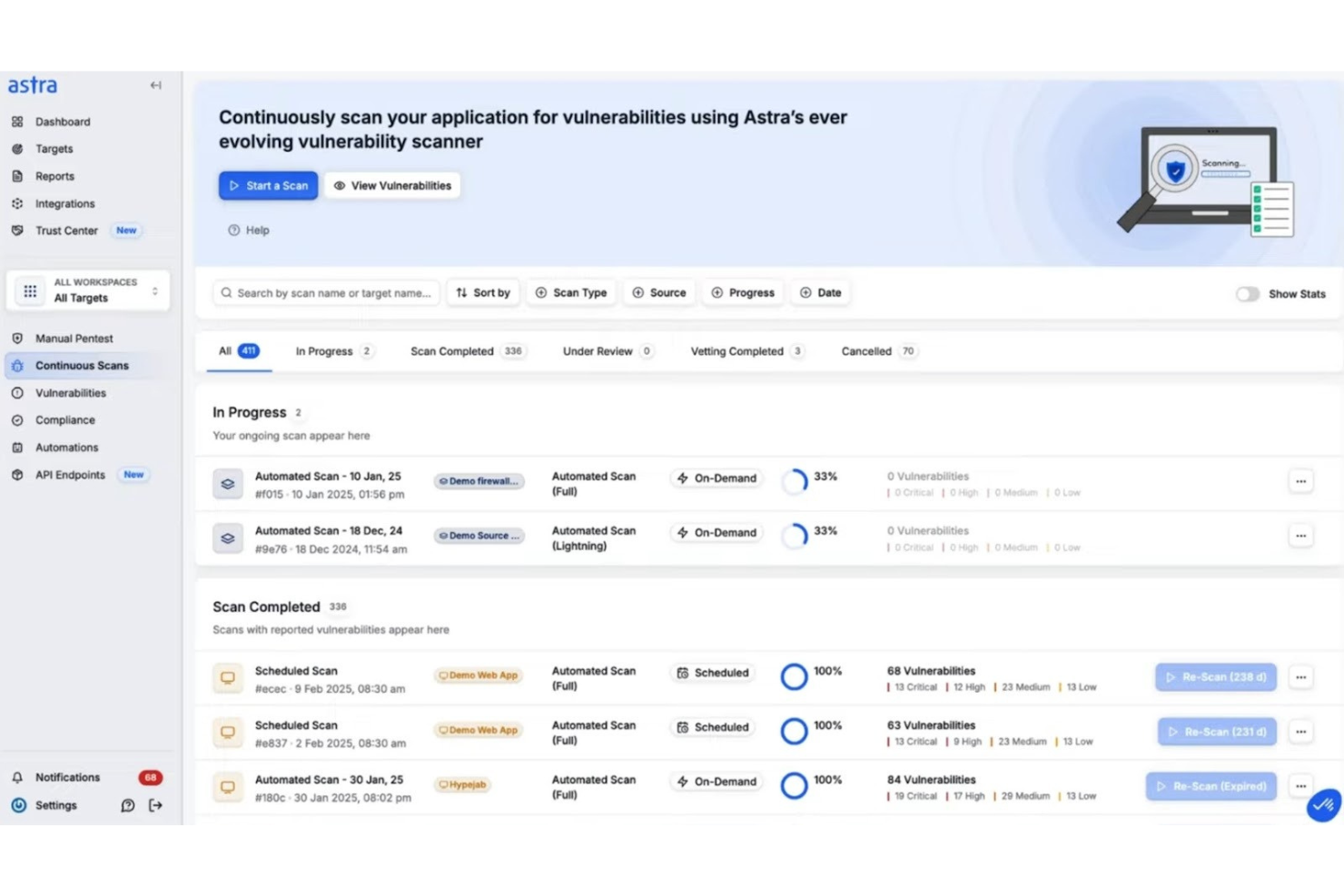
SentinelOne is an AI-driven cybersecurity platform delivering extended detection and response (XDR) across endpoints, primarily serving large enterprises in sectors such as finance, health care, and education. It includes built-in antivirus capabilities and advanced malware protection.
Why I picked SentinelOne: It offers AI-powered threat management by detecting malware, ransomware, zero-day attacks, and insider threats. The Singularity platform integrates various security functions and generative AI to automate security processes, helping to improve your team's efficiency by reducing manual tasks.
Standout Features and Integrations:
Features include a cloud-native application protection platform for complete security, automated incident response to minimize manual intervention, and advanced threat intelligence for insights into potential cyber threats.
Integrations include AWS, IBM QRadar, Palo Alto Networks, Microsoft Azure, Google Cloud, Slack, and more.
Pros and Cons
Pros:
- Generative AI operations
- Strong ransomware protection
- Detects and blocks malware threats
Cons:
- Rollback features require careful policy setup
- Complex initial setup
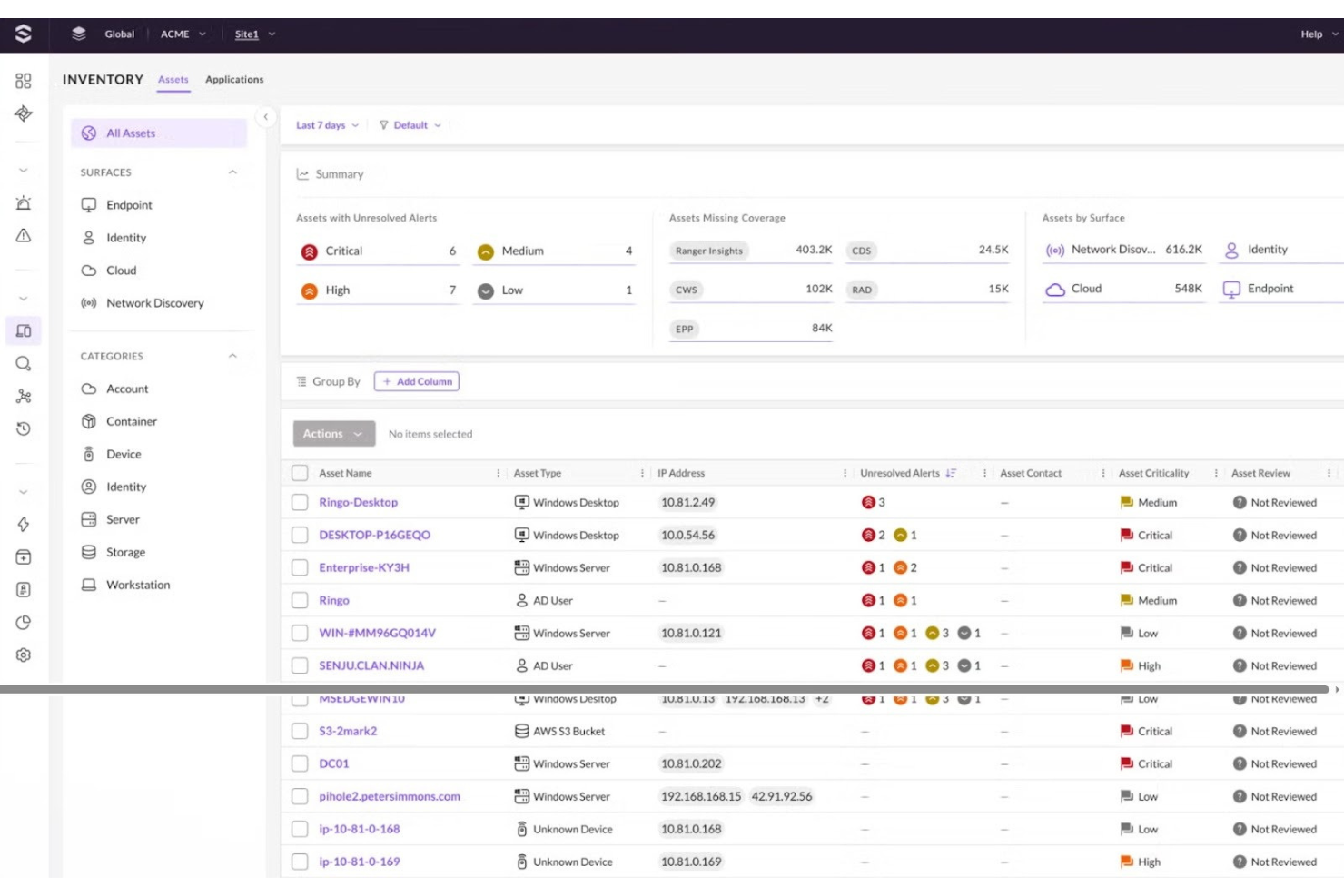
Astra is a cybersecurity tool designed for penetration testing and vulnerability assessment, mainly used by businesses needing to meet compliance standards. It helps identify security weaknesses and ensure that applications and networks are secure. Astra’s primary functions include detecting vulnerabilities and providing actionable insights for remediation.
Why I picked Astra: Its focus on compliance testing makes it ideal for businesses needing to adhere to regulatory standards. Astra provides detailed vulnerability reports that help you understand and address security gaps.
Standout Features and Integrations:
Features include continuous vulnerability scanning to keep your systems secure, detailed reporting to identify and address issues, and an intuitive dashboard for easy management of security tasks.
Integrations include Slack, Jira, GitHub, Bitbucket, GitLab, and more.
Pros and Cons
Pros:
- Actionable remediation insights
- Intuitive management dashboard
- Effective compliance testing
Cons:
- SMB budgets may find pricing restrictive
- Pentest scheduling may delay urgent scans
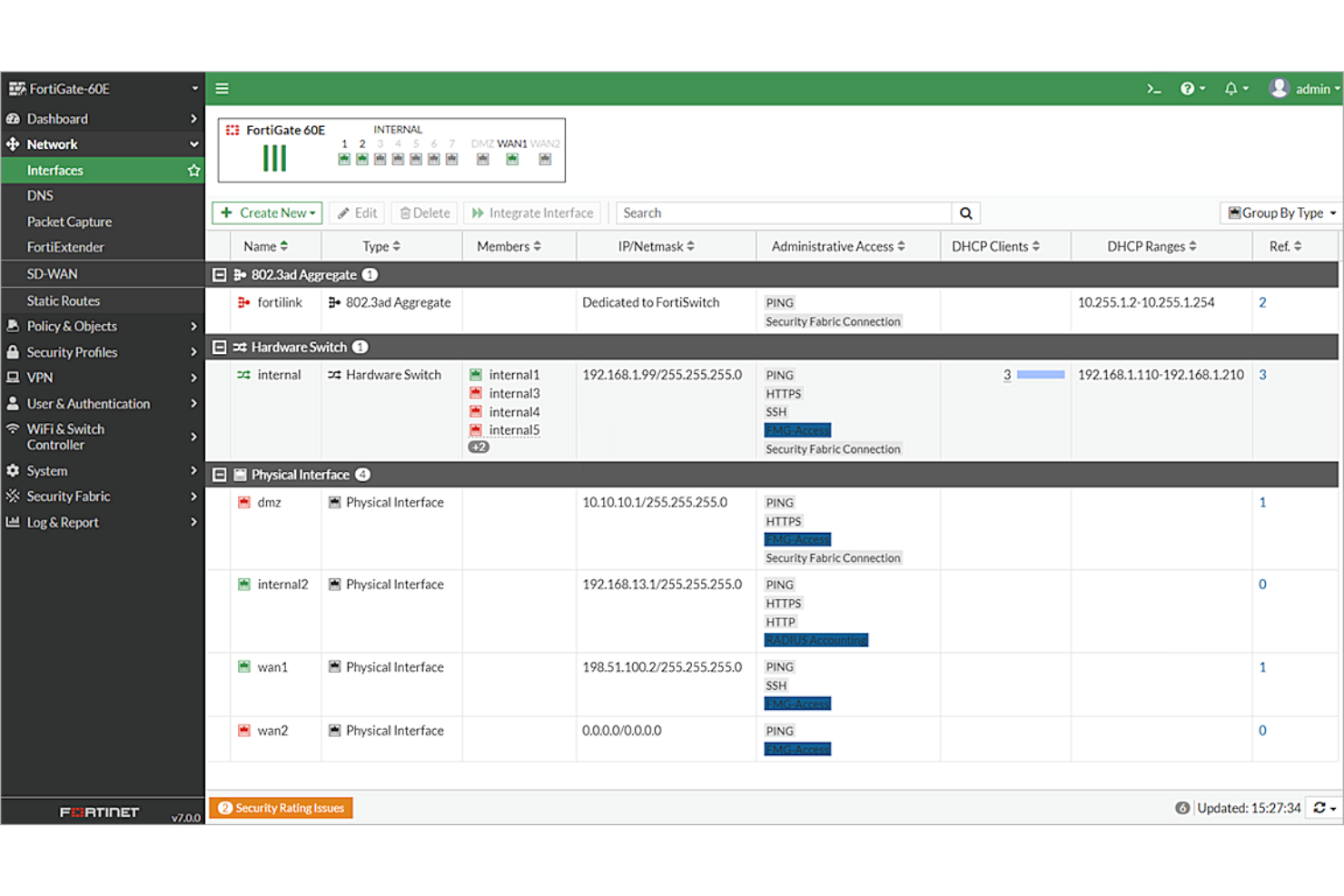
Fortinet is a cybersecurity solution that provides integrated security services through its Fortinet Security Fabric, catering to enterprises, service providers, and mid-sized organizations. It focuses on protecting networks, applications, and data with its broad suite of security products. Fortinet’s key functions include threat protection, secure networking, and endpoint security.
Why I picked Fortinet: Its integrated security approach makes it ideal for businesses needing a unified strategy. Fortinet's Security Fabric architecture connects different security tools to amplify threat visibility and operational coordination. The FortiGate firewalls offer advanced threat protection and secure networking. This thorough coverage helps your team efficiently manage security across the entire network.
Standout Features and Integrations:
Features include advanced firewalls to block malicious activities, secure SD-WAN for optimized network connectivity, and endpoint protection to safeguard devices on your network.
Integrations include AWS, Microsoft, Google Cloud, IBM, Splunk, ServiceNow, and more.
Pros and Cons
Pros:
- Extensive endpoint protection
- Efficient network management
- Unified security platform
Cons:
- Hardware dependency for full capabilities
- Complex licensing structure
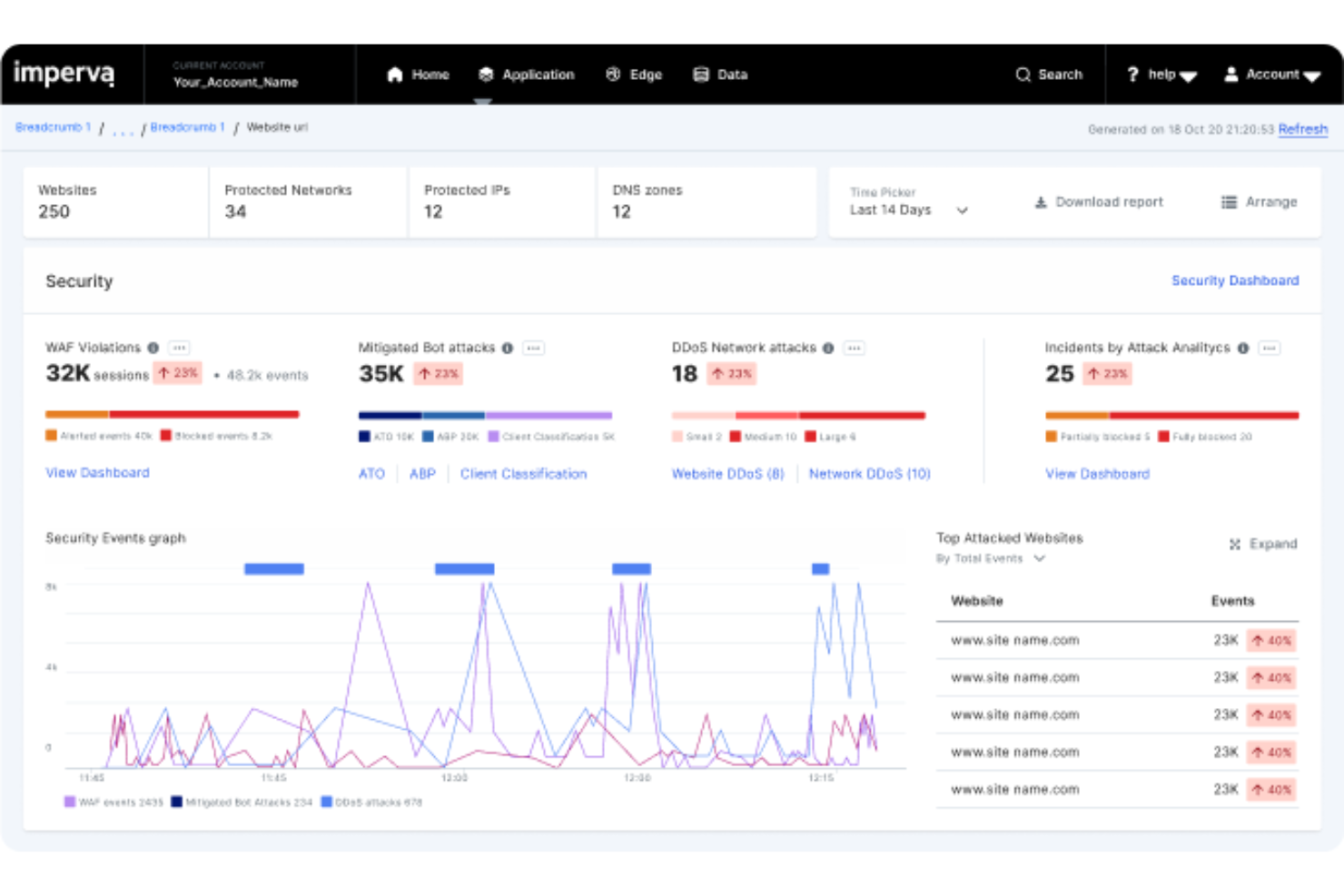
Imperva is a cybersecurity solution designed to protect applications and data in cloud environments from external threats. It is widely used by cybersecurity companies and security teams needing to protect their digital assets. Imperva is frequently recognized in Gartner reports for its leadership in application and data security.
Why I picked Imperva: It delivers real-world protection for sensitive data through its web application firewall (WAF), distributed denial of service (DDoS) mitigation, and API security. Imperva’s key functionalities protect data across cloud and hybrid environments. Its platform integrates well with SIEM tools for centralized monitoring and threat response.
Standout Features and Integrations:
Features include advanced threat analytics for real-time insights into potential risks, a user behavior analytics tool to detect insider threats, and automated security incident responses to reduce manual intervention.
Integrations include AWS, Microsoft Azure, Google Cloud, Splunk, CrowdStrike, IBM, and more.
Pros and Cons
Pros:
- Automated incident response
- Real-time threat insights
- Effective DDoS mitigation
Cons:
- High cost for small businesses
- Limited customization options
ARIA Cybersecurity offers advanced cloud and on-premises IT and operational technology (OT) security solutions for small teams and businesses. Its AZT PROTECT solution specifically safeguards OT environments, including sectors such as pharmaceuticals, manufacturing, and utilities, to protect against cyber threats. ARIA Cybersecurity's key functions include defending critical applications and endpoints with AI-driven technology.
Why I picked AZT PROTECT: It provides effective information security solutions for small teams needing system-wide protection. The integration of multiple security tools into a single platform improves threat detection and response.
Standout Features and Integrations:
Features include a fully automated cloud-based security operations center (SOC) for efficient management, machine learning capabilities for improved threat detection, and network traffic monitoring for end-to-end visibility.
Integrations are not publicly listed.
Pros and Cons
Pros:
- Reduces overall cyber risk exposure
- Cost-effective SOC solution
- Offers managed security services
Cons:
- Limited brand recognition
- Requires technical expertise
Carahsoft is an IT solutions provider and distributor, primarily serving government agencies and educational institutions. It offers a wide range of cybersecurity products that support secure operations and compliance with government standards. The platform connects public sector organizations with leading software vendors through established government contract vehicles.
Why I picked Carahsoft: Its focus on government solutions supports compliance with stringent regulations. Carahsoft provides access to a variety of cybersecurity tools tailored for public sector needs. The ability to bundle software solutions adds value for teams managing complex IT environments.
Standout Features and Integrations:
Features include a broad marketplace for easy procurement, tailored solutions for government compliance, and bundled offerings that combine multiple software tools for more efficient operations.
Integrations are not publicly listed.
Pros and Cons
Pros:
- Strong partner ecosystem
- Offers bundled solutions
- Simplifies procurement processes
Cons:
- High dependency on partnerships
- Limited to public sector
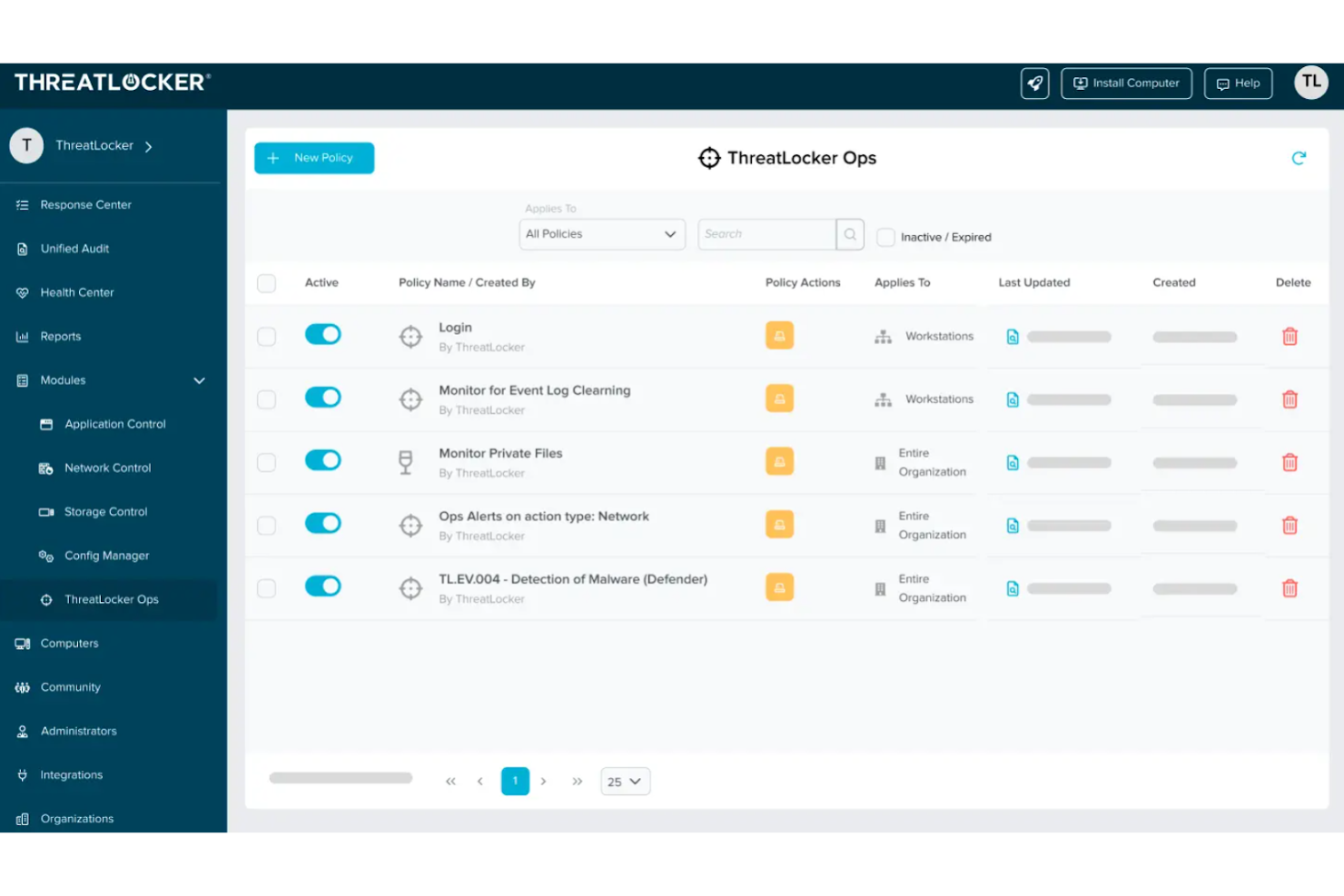
ThreatLocker is a cybersecurity solution focused on application control and endpoint protection, catering mainly to businesses of all sizes, including small and medium-sized organizations. It helps manage application permissions and prevent unauthorized software from running. The key function is to improve security by ensuring only approved applications can execute.
Why I picked ThreatLocker: It excels in application control, making it ideal for businesses needing strict software usage policies. Its policy-driven approach allows you to define what applications are permitted. The ringfencing feature isolates applications, reducing the risk of data breaches. This tool's simplicity and focus on application control make it an asset for maintaining a secure environment.
Standout Features and Integrations:
Features include storage control to manage access to data, audit logs for tracking application activity, and a simple interface that makes managing permissions straightforward.
Integrations include ConnectWise Manage, ConnectWise Automate, Datto SaaS Protection, and more.
Pros and Cons
Pros:
- Detects insider threats
- Protects against zero-day exploits
- Granular security controls
Cons:
- Can be restrictive
- Requires policy setup
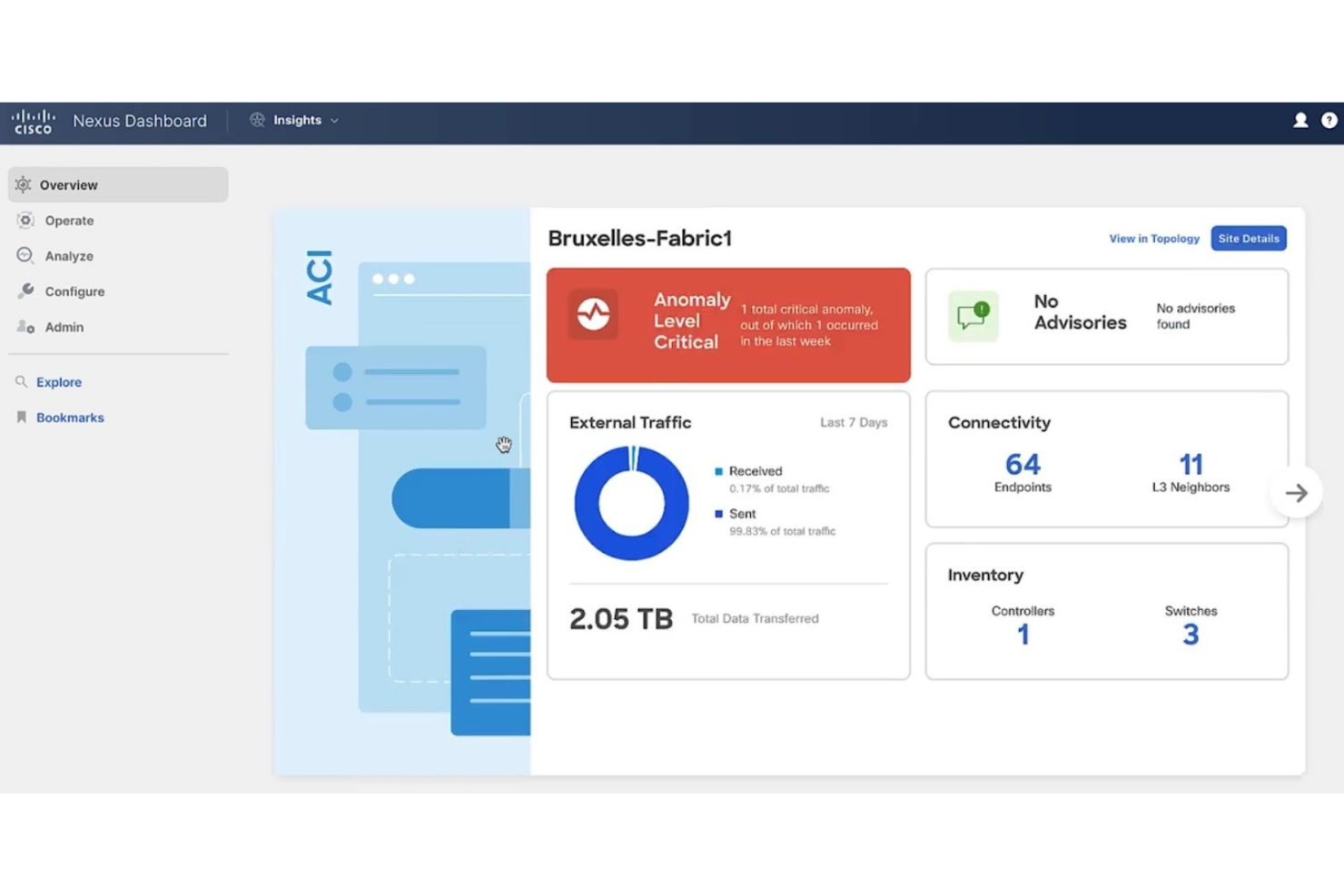
Cisco Security provides full-spectrum cybersecurity solutions focused on enterprise network and access security, catering mainly to large enterprises. It helps secure network infrastructure and ensure reliable communication across cloud, on-premises, and hybrid environments. Cisco Security’s core functions include threat detection, virtual private network (VPN) solutions, and identity-based secure access control.
Why I picked Cisco Security: It excels in protecting large-scale networks and zero-trust access, making it a top choice for enterprises needing reliable infrastructure protection. Cisco Security’s threat intelligence provides real-time global threat insights. Its secure access solutions help control and manage network access.
Standout Features and Integrations:
Features include advanced threat detection analytics, identity and policy enforcement to manage who can access your network, and powerful VPN solutions for secure remote connectivity.
Integrations include AWS, Microsoft Azure, Google Cloud, ServiceNow, and more.
Pros and Cons
Pros:
- Reliable VPN solutions
- Effective threat intelligence
- Integrates with SIEM platforms
Cons:
- Deployment complexity in multi-vendor environments
- Fragmented licensing across products
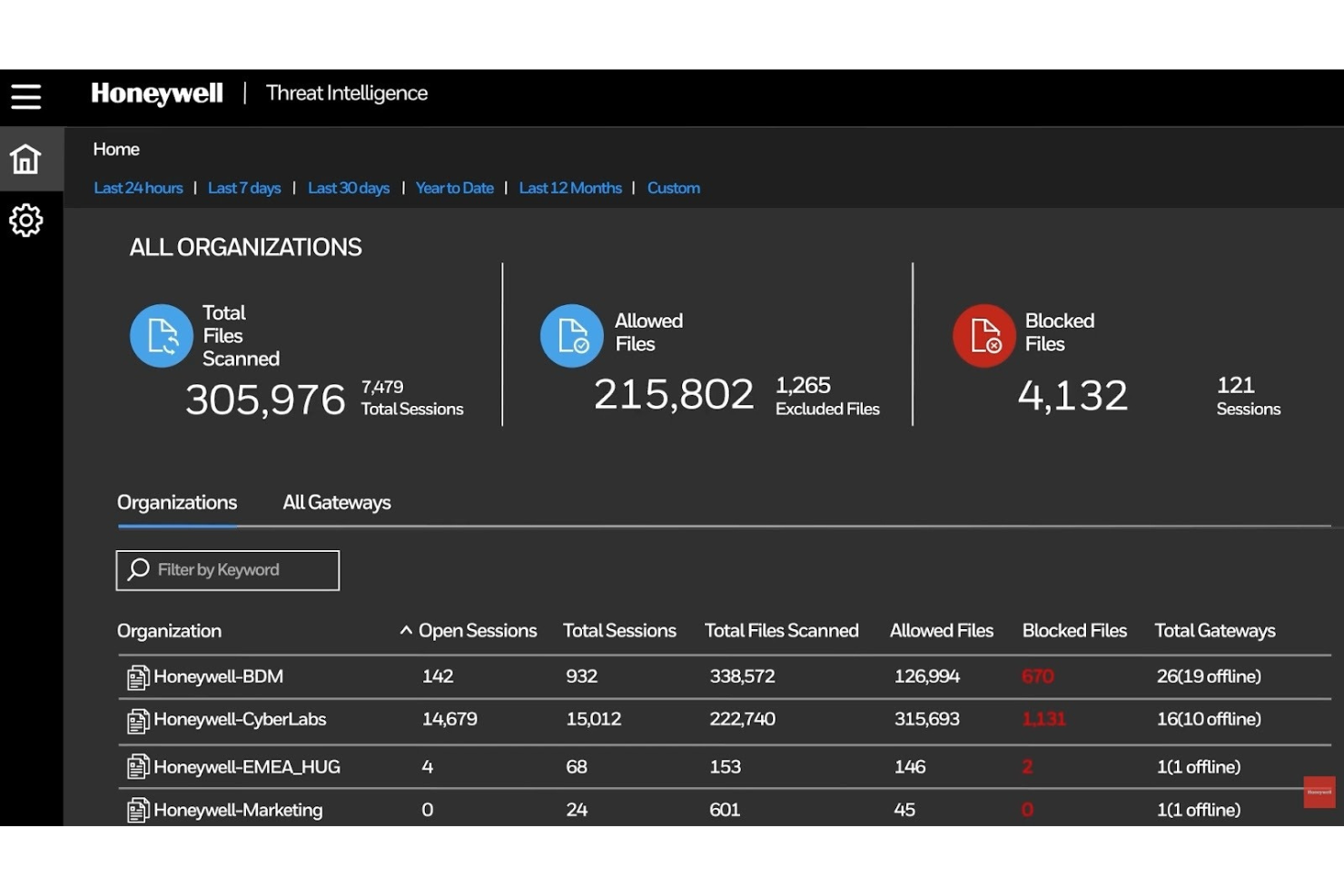
Honeywell provides cybersecurity solutions designed for industrial environments, focusing on sectors such as manufacturing and energy. It offers protection for critical infrastructure and OT systems. The main value lies in securing industrial networks and ensuring operational continuity.
Why I picked Honeywell: It's tailored for industrial security, making it suitable for manufacturing and energy sectors. Honeywell's Industrial Cyber Insights provides continuous asset discovery and risk visualization and near real-time visibility into cyber threats. The Secure Media Exchange feature helps control and monitor removable media. Its ability to integrate cybersecurity into industrial processes ensures safety and regulatory compliance.
Standout Features and Integrations:
Features include continuous asset discovery and risk assessment, vulnerability management, and incident response planning to ensure quick recovery from potential threats.
Integrations are not publicly listed.
Pros and Cons
Pros:
- Effective incident response
- Automated vulnerability management
- Tailored for industrial use
Cons:
- High resource requirements
- Complex portfolio overlap
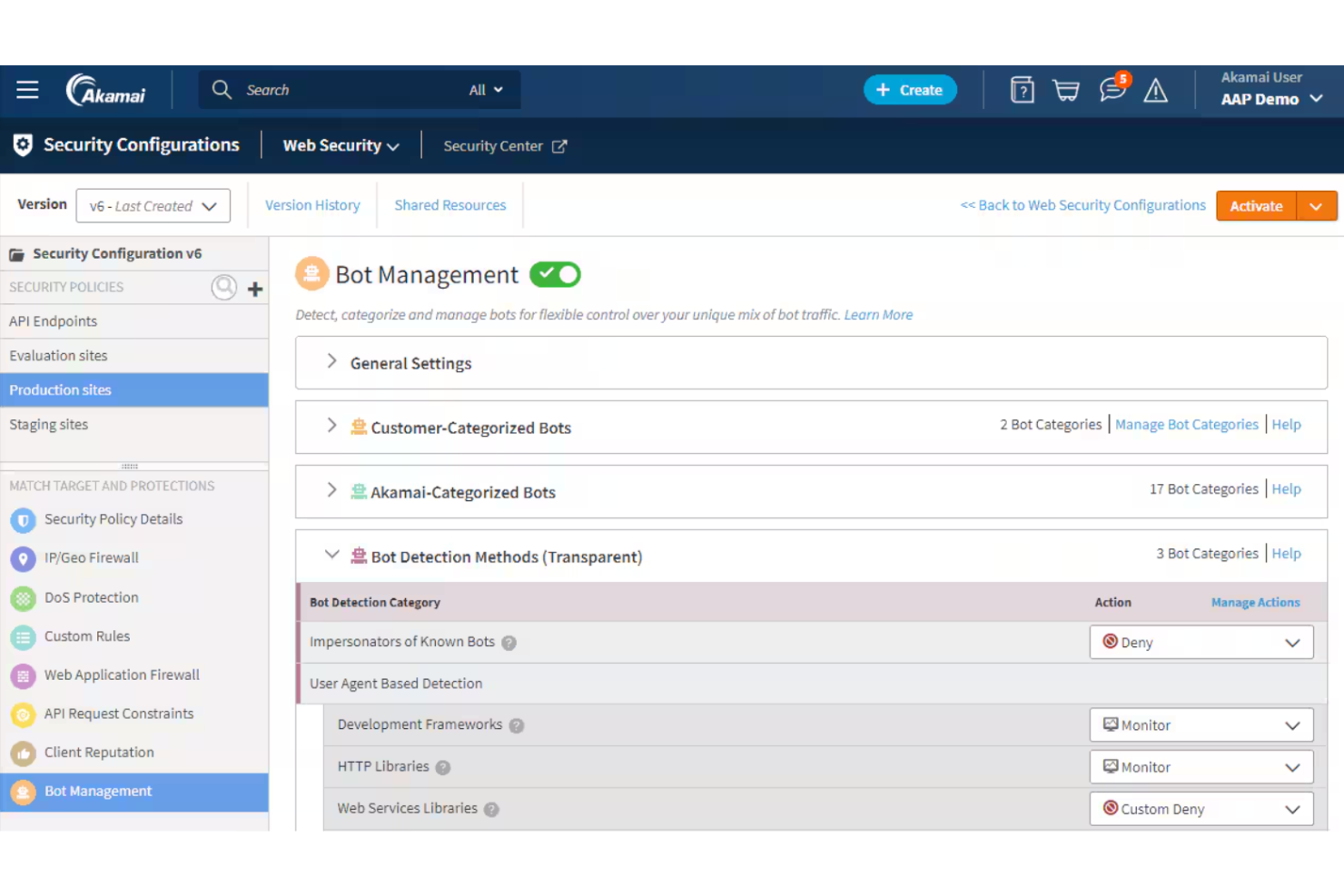
Akamai Security is a cybersecurity solution tailored for businesses needing extensive global coverage. It serves enterprises that need protection and performance at internet scale. Akamai Security offers content delivery, cloud security, and application performance services.
Why I picked Akamai Security: Its massive ecosystem is unmatched, making it ideal for businesses operating in multiple countries. Akamai Security's content delivery network ensures fast and reliable access to your digital assets, and the application performance services optimize the user experience. For teams needing a broad international presence, Akamai Security provides the necessary infrastructure.
Standout Features and Integrations:
Features include cloud security services, SIEM integrations, bot protection, advanced web application security, and automated threat mitigation for global environments.
Integrations are not publicly listed.
Pros and Cons
Pros:
- Protects cloud workloads
- Secures applications and APIs
- Extensive global network
Cons:
- Debugging false positives can be time-intensive
- Complex configuration
Other Cybersecurity Solutions
Here are some additional cybersecurity solutions options that didn’t make it onto my shortlist but are still worth checking out:
- Radware
For DDoS protection
- NordLayer
For remote access to cloud apps
- Sophos
For endpoint malware and ransomware defense
- Palo Alto Networks
For cloud workload threat protection
- Miratech Prevalent
For third-party cyber risk management
Cybersecurity Solution Selection Criteria
When selecting the best cybersecurity solutions to include in this list, I considered common buyer needs and pain points like data protection and threat detection. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Threat detection and response
- Data encryption and protection
- Network security management
- User access control
- Compliance monitoring
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Advanced threat analytics
- Automated incident response
- Cloud integration capabilities
- Machine learning for threat prediction
- Real-time monitoring dashboards
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Customizable dashboards
- Ease of navigation
- Minimal learning curve
- Responsive design for mobile access
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Thorough user documentation
- Access to webinars and tutorials
- Supportive chatbots for guidance
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multiple support channels
- Responsive customer service
- Access to a knowledge base
- Availability of dedicated account managers
Value for Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Transparent pricing structure
- Availability of free trials
- Broad feature set
- Scalability with business growth
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on reliability
- User experiences with support
- Comments on ease of use
- Insights into feature effectiveness
How To Choose a Cybersecurity Solution
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What To Consider |
|---|---|
| Scalability | Can the solution grow with your business? Consider future needs and whether the tool can handle increased data or user volume without a drop in performance. |
| Integrations | Does it connect with your existing systems? Check for compatibility with your current software stack to avoid workflow disruptions. |
| Customizability | Can you tailor the tool to fit your specific needs? Look for options that allow adjustments to suit your unique processes and preferences. |
| Ease of use | Is the tool intuitive for your team? A user-friendly interface reduces training time and increases adoption rates. |
| Implementation and onboarding | How quickly can your team start using it effectively? Assess the resources provided for setup, including tutorials, support, and documentation. |
| Cost | Does the pricing align with your budget? Consider the total cost of ownership, including any hidden fees or charges beyond the initial price. |
| Security safeguards | Are there strong measures to protect your data? Look for encryption, access controls, and regular security updates to ensure data integrity and safety. |
| Compliance requirements | Does it meet industry regulations? Ensure the solution supports compliance with standards relevant to your industry, such as GDPR or HIPAA, to avoid legal issues. |
What Are Cybersecurity Solutions?
Cybersecurity solutions are tools designed to protect systems, networks, and data from cyber threats and unauthorized access. IT professionals, security analysts, and network administrators typically use these tools to safeguard sensitive information and help ensure business continuity. Features such as threat detection, data encryption, and access control support threat prevention and maintain data integrity. Overall, these tools provide essential protection and peace of mind for businesses operating in the digital space.
Features
When selecting cybersecurity solutions, keep an eye out for the following key features:
- Threat detection: Identifies potential threats in real time to prevent data breaches and attacks.
- Data encryption: Secures sensitive information by converting it into code that is unreadable by unauthorized users.
- Access control: Manages who can access your systems and data, ensuring only authorized users have entry.
- Vulnerability scanning: Detects weaknesses in your system that could be exploited by attackers.
- Incident response: Provides tools and protocols for responding quickly to security breaches and minimizing damage.
- Compliance support: Helps meet industry regulations and standards, reducing the risk of legal issues.
- Network monitoring: Keeps an eye on network traffic to detect unusual patterns and potential threats.
- Automated updates: Ensure your software is always current with the latest security patches and improvements.
- User behavior analytics: Analyze user actions to identify abnormal behavior that may indicate a security threat.
- Reporting and dashboards: Offer clear, visual insights into your security posture and areas that need attention.
Benefits
Implementing cybersecurity solutions provides several benefits for your team and your business. Here are a few you can look forward to:
- Data protection: Safeguards sensitive information from breaches through encryption and strong access controls.
- Regulatory compliance: Helps ensure your business meets industry standards and regulations, avoiding legal penalties.
- Threat prevention: Identifies and mitigates risks before they become serious issues, keeping systems secure.
- Operational continuity: Supports uninterrupted business operations during cyber intrusions with effective incident response capabilities.
- Improved trust: Builds confidence among clients and partners by demonstrating a commitment to security.
- Resource efficiency: Automates many security tasks, freeing up your team to focus on other priorities.
- Increased visibility: Provides clear insights into your security posture through extensive reporting and analytics.
Costs and Pricing
Selecting cybersecurity solutions requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in cybersecurity solutions:
Plan Comparison Table for Cybersecurity Solutions
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited data encryption, and basic user access control. |
| Personal Plan | $5-$25/user/month | Improved threat detection, advanced data encryption, and customizable user access controls. |
| Business Plan | $30-$75/user/month | Full threat detection, detailed compliance support, and detailed reporting and analytics. |
| Enterprise Plan | $80-$150/user/month | All-inclusive threat detection, automated incident response, and full integration capabilities. |
Cybersecurity Solutions FAQs
Here are some answers to common questions about cybersecurity solutions:
How do I measure the effectiveness of a cybersecurity solution?
Start by tracking key metrics such as detection rates, false positives, response times, and the number of blocked threats. Review incident logs regularly, and test your defenses with simulated attacks. Compare results against your security goals to see if the solution meets your requirements. Gather feedback from your IT team on usability and performance to round out your evaluation.
How often should I update or reassess my cybersecurity solution?
You should review your cybersecurity solution every six-12 months. Major system changes, new threats, or compliance updates might require more frequent reviews. Schedule regular penetration testing and audits, and adjust your setup based on those findings. Stay current on threat intelligence so you can adapt quickly to new risks.
Can cybersecurity solutions help reduce incident response times?
Yes, many cybersecurity solutions automate detection and alerting, letting you respond faster to threats. Real-time dashboards, automated workflows, and integrations with your incident response tools help slash response times. By centralizing threat information, these platforms make it easier for your team to act quickly and keep damage to a minimum.
How do I ensure my team gets the most value from our cybersecurity tools?
Train your staff on the tools, and set clear processes for monitoring and responding. Encourage regular drills and knowledge sharing. Leverage reporting features to spot performance gaps, and adjust your approach as needed. Make sure you’re using all relevant features, and regularly review tool usage to maximize your investment.
What’s Next:
If you're in the process of researching cybersecurity solutions, connect with a SoftwareSelect advisor for free recommendations.