10 Best Attack Surface Management Tools Shortlist
Managing your organization's attack surface can feel overwhelming. With threats constantly evolving, keeping track of common vulnerabilities and exposures, or CVEs, is a challenge. That's where attack surface management tools come in.
These tools offer a detailed view of your digital footprint and help you identify and manage potential risks before they become serious issues. They implement a zero trust approach, provide a clear view of your digital assets, and ensure that security controls are properly configured and effective, helping your team stay ahead of threats.
I've reviewed the top attack surface management tools to give you an unbiased look at what each offers. In this article, you'll find insights into the tools that can best meet your needs. Let's dive into the options and find the right fit for your team.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Attack Surface Management Tools Summary
This comparison chart summarizes pricing details for my top selections for attack surface management tools to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for automated threat detection | Free demo available | From $179.99/endpoint (billed annually) | Website | |
| 2 | Best for compliance management | 30-day free trial + free demo available | Pricing upon request | Website | |
| 3 | Best for cloud-native applications | Free demo available | Pricing upon request | Website | |
| 4 | Best for integration with DevOps tools | Free trial + free demo available | From $1.62/asset/month (billed annually) | Website | |
| 5 | Best for continuous monitoring | 7-day free trial + free demo available | From $4,390/year | Website | |
| 6 | Best for attack surface discovery | Free demo available | Pricing upon request | Website | |
| 7 | Best for web application security | 14-day free trial + free demo available | From €90/month | Website | |
| 8 | Best for small to midsize teams | Free demo available | From $399/month | Website | |
| 9 | Best for large enterprises | Free demo available | Pricing upon request | Website | |
| 10 | Best for internet-facing asset discovery | Free plan + free demo available | Pricing upon request | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Attack Surface Management Tool Reviews
Below are my detailed summaries of the best attack surface management tools that made it onto my shortlist. My reviews offer a detailed look at the key features, pros and cons, integrations, and ideal use cases of each tool to help you find the best one for you.
SentinelOne is an endpoint protection platform designed for businesses that need cybersecurity measures. It primarily serves IT teams across various industries, providing automated threat detection and response.
Why I picked SentinelOne: SentinelOne excels in automated threat detection by offering real-time endpoint protection. Its ability to detect threats swiftly without human intervention sets it apart.
Standout features and integrations:
Features include real-time threat detection, AI-driven analytics, and rollback capabilities. Your team benefits from automated incident response, reducing their manual workload. The platform's threat intelligence offers detailed insights into potential risks.
Integrations include Microsoft Active Directory, Splunk, IBM Security, Okta, AWS, and more.
Pros and Cons
Pros:
- Smooth user interface
- Fast rollback capabilities
- Strong AI detection
Cons:
- Rare console outages
- Some tuning needed
Qualys is a cloud-based security platform designed for businesses that focus on compliance management and vulnerability assessment. It serves IT and security teams by providing continuous visibility into their security posture.
Why I picked Qualys: Qualys excels in compliance management, offering features that ensure your organization meets regulatory standards by keeping your team informed about potential risks.
Standout features and integrations:
Features include real-time monitoring, detailed compliance reports, and continuous vulnerability assessments. Your team can leverage these tools to maintain a strong security posture, and the platform's cloud-based nature ensures easy access and updates.
Integrations include ServiceNow, Splunk, AWS, Google Cloud, IBM, and more.
Pros and Cons
Pros:
- Unified IT and security workflows
- Predictive tech debt tracking
- Enterprise-grade capabilities
Cons:
- Unclear unit definitions and documentation gaps
- Can have fragmented module licensing
Wiz is a cloud security platform tailored for businesses that utilize cloud-native applications. It helps teams identify and manage security risks across multi-cloud environments.
Why I picked Wiz: Wiz offers a thorough view of security across cloud-native applications, making it ideal for teams working in cloud environments. It provides deep IAM visibility into workloads and configurations, helping you spot vulnerabilities quickly. The platform's risk prioritization ensures your team focuses on the most important issues first. Its ability to integrate with various cloud providers adds to its appeal for businesses that rely on cloud infrastructures.
Standout features and integrations:
Features include real-time cloud workload protection, detailed risk assessment, and automated compliance checks. Your team benefits from continuous security testing, reducing manual oversight. The platform's intuitive dashboard simplifies understanding and managing cloud risks.
Integrations include AWS Security Hub, Azure DevOps, Google Cloud Pub/Sub, Wiz Terraform, GitHub, GitLab, Slack, Jira, PagerDuty, and more.
Pros and Cons
Pros:
- Automated compliance checks
- Effective risk prioritization
- Strong cloud integration
Cons:
- Requires cloud expertise
- Higher learning curve
Rapid7 is a cybersecurity platform tailored for IT and security teams that focuses on vulnerability management and threat detection. It helps organizations assess and improve their security posture by integrating with DevOps tools.
Why I picked Rapid7: Rapid7 integrates well with DevOps tools, making it a top choice for teams that need cohesive security processes to identify and address potential threats.
Standout features and integrations:
Features include vulnerability assessments, detailed analytics, and effective remediation tools. Your team can leverage these insights to improve security processes, and the platform's integration capabilities ensure alignment with your DevOps environment.
Integrations include AWS, Azure, Google Cloud, Slack, Jira, ServiceNow, Microsoft Teams, and more.
Pros and Cons
Pros:
- Aligned workflow integration
- Business-centric risk scoring
- Strong DevOps integration
Cons:
- Occasional performance lags
- Can be resource-intensive
Tenable is a cybersecurity platform tailored for IT and security professionals, focusing on vulnerability management and continuous monitoring. It helps organizations maintain a secure environment by providing insights into potential threats.
Why I picked Tenable: Tenable is distinguished by its continuous monitoring capabilities, ensuring your team is always aware of vulnerabilities and making it a valuable tool for organizations needing constant vigilance.
Standout features and integrations:
Features include real-time data, detailed vulnerability insights, and prioritized remediation efforts. Your team benefits from continuous updates that keep security measures current, and the platform's user-friendly interface simplifies managing complex data.
Integrations include AWS Security Hub, Azure, Google Cloud, Splunk, ServiceNow, IBM QRadar, Jira, and more.
Pros and Cons
Pros:
- Deep exposure scoring capabilities
- Flexible deployment options
- Vulnerability detection backed by Nessus
Cons:
- Expensive pricing and licensing
- Limited reporting flexibility
CyCognito offers a platform focused on discovering misconfigurations and managing external attack surfaces. It's designed for security teams who need to identify and mitigate risks outside their direct control.
Why I picked CyCognito: CyCognito excels in identifying external attack surfaces by providing full visibility into third-party risks. The platform helps prioritize vulnerabilities based on their potential impact, improving your team's response efforts and external attack surface management.
Standout features and integrations:
Features include automated reconnaissance, risk prioritization, and shadow IT discovery. Your team can quickly identify and address vulnerabilities. The platform's detailed insights help you understand external risks better without overwhelming your resources.
Integrations include ServiceNow, Splunk, Palo Alto Networks, Tenable, and more.
Pros and Cons
Pros:
- Automated reconnaissance
- Thorough cyber asset visibility
- Effective external risk discovery
Cons:
- No internal network coverage
- Requires some security expertise
Detectify is a security platform tailored for web applications, serving developers and security teams. It scans your web applications for vulnerabilities, helping you secure your digital assets effectively.
Why I picked Detectify: Detectify focuses on web application security, with features that identify vulnerabilities quickly so that your team stays ahead of new threats. Its dedication to web application security makes it a top choice for developers who need to protect their projects.
Standout features and integrations:
Features include automated scanning, continuous updates, and detailed security reports. Your team can identify vulnerabilities with the platform's intuitive interface, and the insights provided help prioritize and address security issues.
Integrations include Slack, Jira, Azure, PagerDuty, Splunk, ServiceNow, AWS, and more.
Pros and Cons
Pros:
- Automated subdomain discovery and monitoring
- 100% payload-based testing
- Regular updates from ethical hackers
Cons:
- No internal networks coverage
- No self-service option
Halo Security offers an attack surface management solution that caters to small to midsize teams. It focuses on identifying and managing vulnerabilities to improve your organization's security posture.
Why I picked Halo Security: Halo Security's design is best for small to midsize teams, as it simplifies vulnerability management. Its focus on ease of use and effective threat detection makes it a practical choice.
Standout features and integrations:
Features include automated scanning to identify potential threats and exposed assets quickly, a user-friendly dashboard, and clear insights into your security status. Your team can navigate the interface without extensive training. The tool also offers real-time alerts to keep you updated on potential risks.
Integrations include AWS, Azure, Google Cloud, Slack, Jira, ServiceNow, and more.
Pros and Cons
Pros:
- Good for small teams
- On-demand manual penetration testing
- Simple setup process
Cons:
- Basic reporting options
- Limited advanced features
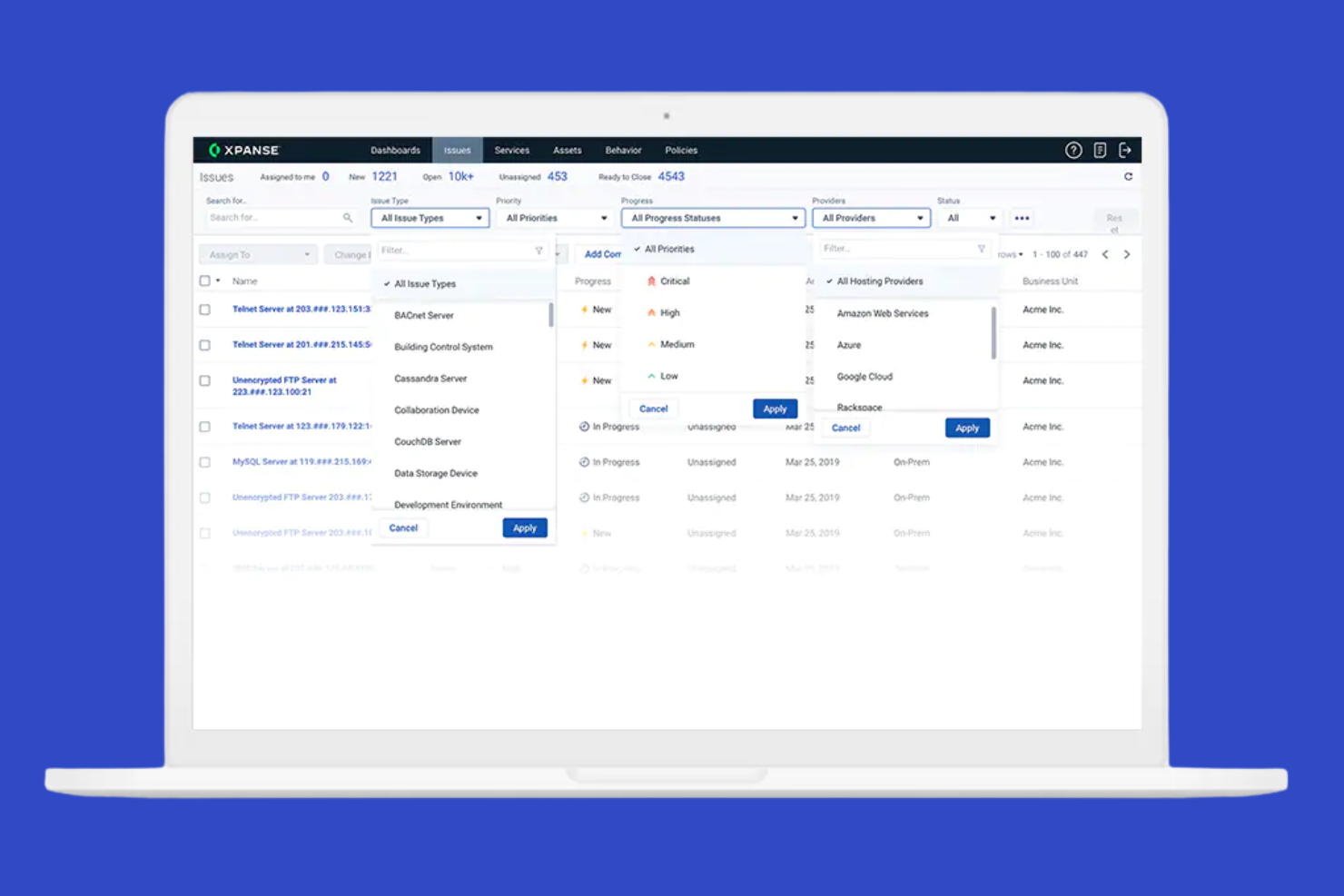
Palo Alto Networks Cortex Xpanse is a cybersecurity platform designed for large enterprises that need advanced threat detection and response capabilities. It focuses on unifying security operations to help teams manage and mitigate risks efficiently.
Why I picked Palo Alto Networks Cortex Xpanse: Cortex Xpanse offers sophisticated threat detection and response features tailored for large and growing enterprises, keeping your operations secure.
Standout features and integrations:
Features include advanced threat detection, automated incident response, and powerful analytics to find hidden threats across your network. The platform's scalability supports growth without compromising security.
Integrations include Splunk, ServiceNow, IBM QRadar, Jira, and more.
Pros and Cons
Pros:
- Trace unmanaged assets to stakeholders
- Native integration with Cortex XSOAR
- Scans the entire IPv4 space daily
Cons:
- High technical expertise needed
- No built-in dark web scanning
Censys is a cybersecurity platform designed for organizations that need to discover and monitor internet-facing assets, including IoT devices. It focuses on providing comprehensive visibility into external threats to help security teams manage vulnerabilities effectively.
Why I picked Censys: Censys excels in identifying internet-facing assets, offering visibility into potential exposures, making it ideal for organizations that need to secure their online presence.
Standout features and integrations:
Features include continuous internet scanning, detailed asset inventories, and risk assessment tools. Your team benefits from real-time data about potential threats, and the platform's insights help prioritize vulnerabilities for effective management.
Integrations include Splunk, ServiceNow, AWS, Azure, Google Cloud, Slack, Jira, and more.
Pros and Cons
Pros:
- Offers strong integration support with SIEMs
- Uncovers external assets
- Detailed asset inventories
Cons:
- Occasional false positives
- Limited internal cloud-native environment information
Other Attack Surface Management Tools
Here are some additional attack surface management tools that didn’t make it onto my shortlist but are still worth checking out:
- RiskProfiler
For risk-based prioritization
- Intruder
For vulnerability scanning
- Bitsight
For cybersecurity ratings
- Aikido
For developers
Attack Surface Management Tool Selection Criteria
When selecting the best attack surface management tools to include in this list, I considered common buyer needs and pain points, such as identifying hidden vulnerabilities and managing external threats. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Identify external vulnerabilities
- Monitor network traffic for threats
- Provide risk assessment reports
- Offer continuous monitoring
- Detect unauthorized access
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Automated threat intelligence updates
- Customizable alerts and notifications
- Integration with third-party security tools
- Advanced data visualization dashboards
- Machine-learning-based anomaly detection
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Simple navigation
- Minimal learning curve
- Responsive design
- Customizable user settings
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates and guides
- Supportive chatbots
- Webinars and live demos
Customer Support (10% of total score)
To assess each software provider's customer support services, I considered the following:
- 24/7 availability
- Multiple support channels
- Response time for queries
- Access to a knowledge base
- Quality of technical support
Value for Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Features offered at each price tier
- Availability of discounts or offers
- Transparent pricing structure
- Trial period or money-back guarantee
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Commonly mentioned pros and cons
- Frequency of updates and improvements
- Support experience feedback
- Recommendations by users
How To Choose an Attack Surface Management Tool
It's easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here's a checklist of factors to keep in mind:
| Factor | What To Consider |
|---|---|
| Scalability | Can the tool grow with your business? Consider current needs and future expansion. |
| Integrations | Does it work with existing systems? Check compatibility with your current software. |
| Customizability | Can you tailor the tool to fit your workflows? Look for flexible configuration options. |
| Ease of use | Is the tool intuitive? A steep learning curve can slow down your team's productivity. |
| Implementation and onboarding | How quickly can your team get up to speed? Look for tools with strong support and resources. |
| Cost | Does the pricing fit your budget? Consider total cost, including setup and ongoing fees. |
| Security safeguards | Does the tool meet your security standards? Look for compliance with industry regulations. |
| Support availability | What support does the vendor offer? Consider 24/7 availability and support channels. |
What Are Attack Surface Management Tools?
Attack surface management tools are software products that help organizations identify, monitor, and manage potential vulnerabilities in their digital environments. These tools are generally used by IT and security professionals to improve their organization's security posture. Features, such as continuous monitoring, risk assessment, and automated alerts, help with identifying threats, prioritizing vulnerabilities, and maintaining security. Overall, these tools provide users with the ability to proactively manage and reduce security risks.
Features
When selecting attack surface management tools, watch for the following key features:
- Continuous monitoring: Provides real-time visibility into your digital environment, helping you stay informed about new vulnerabilities and entry points as they arise.
- Risk assessment: Evaluates the potential impact of identified vulnerabilities, allowing you to prioritize remediation efforts effectively.
- Automated alerts: Send notifications about key risks, ensuring your team can respond quickly to emerging threats, such as malware.
- Vulnerability scanning: Identifies weaknesses in your systems and applications, helping you address attack vectors before they can be exploited by threat actors.
- Asset discovery: Maps out all internet-facing assets, giving you a complete view of your attack surface.
- Integration capabilities: Connect with existing tools and platforms, ensuring a cohesive security strategy across your organization.
- Customizable reporting: Offers tailored insights into your security posture, allowing you to generate reports that meet your specific needs.
- Compliance management: Helps ensure your organization meets regulatory requirements by providing detailed compliance reports.
- Threat intelligence updates: Deliver the latest threat data to keep your security measures current and effective.
- User-friendly interface: Simplifies navigation and management, making it easier for your team to use the tool efficiently.
Benefits
Implementing attack surface management tools provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security posture: By continuously monitoring vulnerabilities, these tools help you strengthen your organization's security defenses.
- Proactive threat management: Automated alerts and risk assessments enable your team to address potential threats before they escalate.
- Efficient resource allocation: Prioritizing vulnerabilities based on risk allows your team to focus efforts where they're most needed.
- Regulatory compliance: Compliance management features ensure that your organization meets industry standards and legal requirements.
- Improved visibility: Asset discovery and mapping provide a clear view of your digital landscape, reducing blind spots.
- Informed decision making: Customizable reports deliver insights that support strategic planning and security investments.
- Reduced manual workload: Automation features minimize the need for manual attack surface monitoring and analysis, freeing up your team's time.
Costs and Pricing
Selecting attack surface management tools requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in attack surface management tools solutions:
Plan Comparison Table for Attack Surface Management Tools
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic monitoring, limited alerts, and community support. |
| Personal Plan | $99-$399/month | Vulnerability scanning, risk assessment reports, and email support. |
| Business Plan | $149-$499/month | Continuous monitoring, automated alerts, and integration capabilities. |
| Enterprise Plan | $4,390+/year | Advanced threat intelligence, compliance management, and dedicated support. |
Attack Surface Management Tools FAQs
Here are some answers to common questions about attack surface management tools:
What industries benefit most from attack surface management tools?
Industries with significant digital assets would benefit greatly, such as finance and healthcare. These sectors often face strict regulatory requirements and high cybersecurity risks. By using attack surface management tools, your team can better protect sensitive data and ensure compliance with industry standards.
Can small businesses use attack surface management tools effectively?
Small businesses can use these tools effectively to manage their security posture. These tools help identify vulnerabilities and prioritize risks, which is important with limited resources. Look for solutions with scalable pricing and features that match your specific needs to get the most value.
How often should you update attack surface management tools?
You should update these tools regularly to ensure they’re effective against the latest threats. Many solutions offer automated updates, keeping your system current without manual intervention. Regular updates help your team stay ahead of emerging vulnerabilities and improve overall security management.
What's Next:
If you're in the process of researching attack surface management tools, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.