10 Best Vulnerability Scanning Software Shortlist
With so many different vulnerability scanning software available, figuring out which is right for you is tough. You know you want to proactively discover and address security gaps before they can be exploited but need to figure out which tool is best. I've got you! In this post I'll help make your choice easy, sharing my personal experiences using dozens of different vulnerability scanning tools with a variety of teams and projects, with my picks of the best vulnerability scanning software.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Vulnerability Scanning Software Summary
This comparison chart summarizes pricing details for my top vulnerability scanning software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for comprehensive code-to-cloud security | Free plan available + free demo | From $350/month | Website | |
| 2 | Best for proactive vulnerability management | 14-day free trial + free demo available | From $149/month | Website | |
| 3 | Best for enterprise vulnerability mitigation | Free 30-day trial and demo available | $1,195 for 100 workstations and a single-user license | Website | |
| 4 | Best for identifying potential security weaknesses across an organization's network | 30-day free trial + free demo available | From $338.50/year | Website | |
| 5 | Best for proof-based vulnerability scanning | Free demo available | Pricing upon request | Website | |
| 6 | Information security solution that provides deep visibility into global assets | 30-day free trial + free demo available | Pricing upon request | Website | |
| 7 | Best vulnerability scanning software to lower the rate of false positives | Free trial + free demo available | Pricing upon request | Website | |
| 8 | Best for hybrid scanning with AcuSensor Technology | Free demo available | Pricing upon request | Website | |
| 9 | Vulnerability scanning tool great for crawling JavaScript-heavy applications | Free plan available | From $475/user/year | Website | |
| 10 | Offers external threat intelligence solution with clear and dark web monitoring | Free trial + free demo available | From $1.62/asset/month (billed annually) | Website |
-

Site24x7
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

GitHub Actions
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8 -

Docker
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6
Best Vulnerability Scanning Software Reviews
Below are my detailed summaries of the best vulnerability scanning software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
Aikido Security is a comprehensive DevSecOps platform designed to provide end-to-end security for code and cloud environments. It integrates various security scans and features, including vulnerability management, SBOM generation, cloud posture management, container image scanning, and dependency scanning.
One of the key strengths of Aikido Security is its all-in-one platform that integrates multiple scanning capabilities, including Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Cloud Security Posture Management (CSPM), Software Composition Analysis (SCA), Infrastructure as Code (IaC) scanning, container scanning, and secrets detection.
This holistic approach ensures that all potential vulnerabilities across different layers of an application and its infrastructure are identified and addressed. By providing full coverage from code to cloud, Aikido Security helps organizations maintain a robust security posture. The software also supports compliance with standards such as SOC 2 and ISO 27001:2022 by automating the collection of evidence and generating detailed security reports.
Aikido integrates with Amazon Web Services (AWS), Google Cloud, MS Azure Cloud, DigitalOcean, Drata, Vanta, GitHub, GitLab Cloud, Bitbucket, Jira, Slack, Docker Hub, AWS Elastic Container Registry, GCP Artifact Registry, CircleCI, and Jenkins.
New Product Updates from Aikido Security
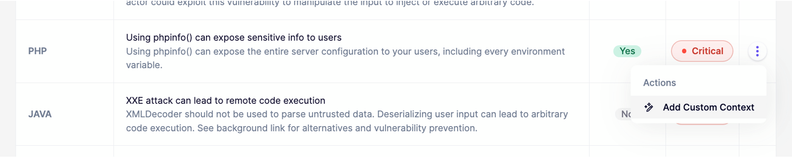
Aikido Security Enhances AI Pentest and AutoTriage Accuracy
Aikido Security introduces AI Pentest vulnerability escalation and custom context for AutoTriage to enhance exploitability assessment and reduce false positives. For more information, visit Aikido Security's official site.
Intruder is a cloud-based vulnerability scanner that aims to help businesses of all sizes discover security weaknesses in their online systems. The tool provides continuous monitoring of the network to identify vulnerabilities and reduce the attack surface.
Intruder provides a proactive security monitoring service, which includes regular scans to detect new threats as they emerge. Its network vulnerability scanning checks for over 10,000 vulnerabilities automatically. The tool then prioritizes the results to help focus on the issues that matter most and provide clear information on how to fix them.
Integrations are natively available with Slack, MS Teams, Jira, Github, and Gitlab. Other integrations can be accessed through Zapier and API.
Intruder costs from $196/month/application. A 14-day free trial is also available.
New Product Updates from Intruder
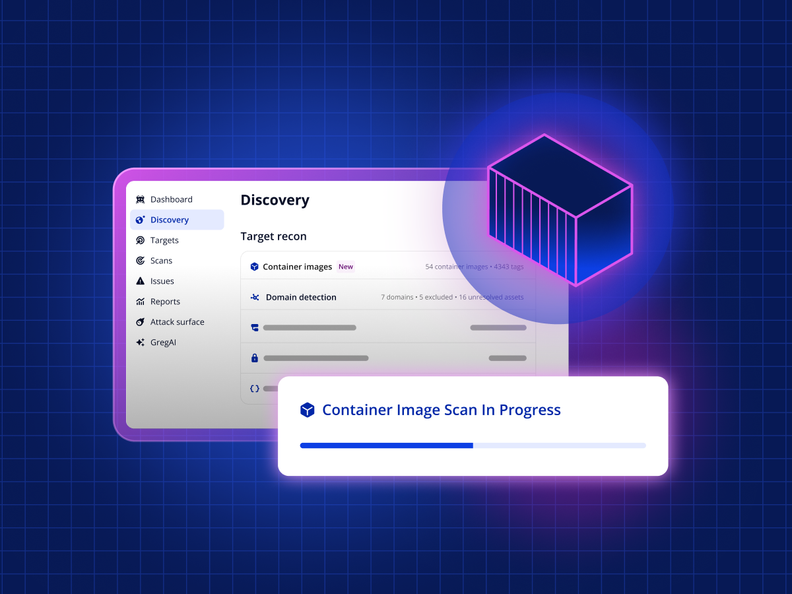
Intruder Unveils Agentless Container Image Scanning
Intruder introduces agentless container image scanning across cloud platforms. This update helps teams detect vulnerabilities before deployment with less setup. For more information, visit Intruder’s official site.
Best for enterprise vulnerability mitigation
ManageEngine Vulnerability Manager Plus is a comprehensive tool designed for enterprise vulnerability management, offering features such as secure configuration deployment, compliance, automated patch deployment, and zero-day vulnerability mitigation. It goes beyond the capabilities of traditional vulnerability management tools, providing executive reports, antivirus audits, deployment policies, and role-based administration.
Its ability to automate vulnerability assessment, patch management, and compliance management from a single console makes it a standout choice for large organizations with complex security needs. ManageEngine Vulnerability Manager Plus distinguishes itself with its robust capabilities, including detailed insights and reports that streamline the vulnerability management process. Its all-in-one platform for managing network vulnerabilities and its prioritization-focused approach to identifying and addressing vulnerabilities make it an ideal choice for enterprises.
ManageEngine Vulnerability Manager Plus offers a comprehensive Vulnerability Assessment feature that identifies and prioritizes a wide array of vulnerabilities, considering factors like exploitability and severity. Its integrations include Active Directory, Azure AD, AWS, and G Suite, which facilitates the management and monitoring of vulnerabilities across different platforms and services. The software provides tools for vulnerability assessment, compliance, patch management, network device security configuration management, and zero-day vulnerability mitigation.
Best for identifying potential security weaknesses across an organization's network
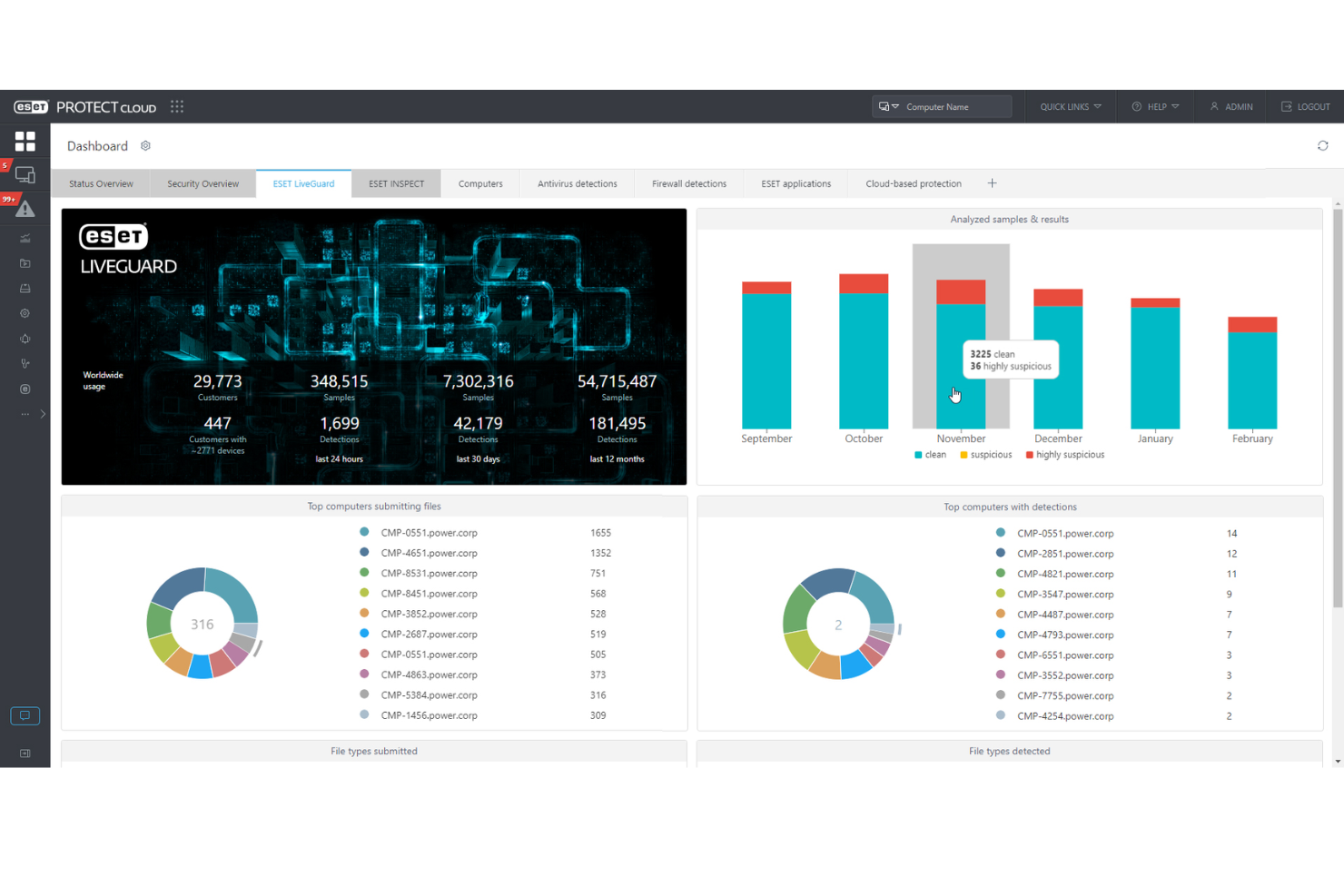
ESET PROTECT Complete provides a robust cybersecurity framework designed to protect businesses from a wide range of digital threats. This solution offers a suite of tools including endpoint protection, cloud sandboxing, and data encryption, aiming to deliver a secure, manageable, and comprehensive defense mechanism against malware, ransomware, and phishing attacks.
As a vulnerability scanning software, ESET PROTECT Complete excels in identifying and addressing potential security weaknesses across an organization's network. It provides detailed vulnerability reports, highlighting areas of concern and recommending actionable steps to mitigate risks. Its scanning engine is both thorough and efficient, ensuring minimal disruption to operational activities while maintaining a high level of security awareness.
ESET PROTECT Complete natively integrates with a variety of tools, including ESET Endpoint Security, ESET Endpoint Antivirus, ESET Security Management Center, ESET Dynamic Threat Defense, ESET Secure Authentication, ESET File Security for Microsoft Windows Server, ESET Mail Security for Microsoft Exchange Server, ESET Full Disk Encryption, Microsoft Active Directory, and SIEM tools.
ESET PROTECT Complete offers pricing upon request + a 30-day free trial.
Invicti is a comprehensive web application and API security tool designed to help enterprises identify and fix vulnerabilities in their web assets. It offers automated discovery and security testing for web applications and APIs, integrating seamlessly into the software development lifecycle.
Invicti offers proof-based scanning technology. Unlike traditional scanners that merely identify potential vulnerabilities, Invicti goes a step further by safely exploiting these vulnerabilities in a read-only manner to confirm their existence. This can reduce false positives, saving development teams valuable time that would otherwise be spent on manual verification.
The software's comprehensive scanning capabilities cover a wide range of vulnerabilities, including those in complex applications and server configurations. Integrations include MuleSoft Anypoint Exchange, Amazon API Gateway, Apigee API hub, Kubernetes, Azure Boards, Bitbucket, Bugzilla, FogBugz, DefectDojo, Freshservice, GitHub, GitLab, Jazz Team Server, and Jira.
Qualys
Information security solution that provides deep visibility into global assets
Qualys analyzes misconfigurations and threats across your global tech environment with six sigma accuracy. The system provides real-time alerts on zero-day vulnerabilities, compromised assets, and network irregularities. You can quarantine compromised assets with a single click, buying you more time to investigate and contain an attack.
To protect your IT environment, you need to know which assets are connected to your network. Qualys’ free Global AssetView application helps security teams accomplish this by automatically identifying all known and unknown assets on a network. You can quickly grab detailed information about each asset, including installed software, running services, and vendor lifecycle information. The application also helps with asset organization, enabling teams to categorize assets into product families with custom tagging.
Qualys supports native integrations with AWS, Azure, and Google Cloud.
Pricing is based on several factors, including the number of user licenses, Qualys Cloud Platform Apps, internal web applications, and IP addresses your team will be utilizing.
Best vulnerability scanning software to lower the rate of false positives
New Relic is an all-in-one observability platform that helps you monitor, troubleshoot, and tune your full stack. It allows companies to monitor and enhance their network’s security by identifying possible weaknesses that could be exploited by hackers. With New Relic, you can proactively scan their systems for potential vulnerabilities, getting a comprehensive overview of their security status, which can help in making informed decisions and creating effective cybersecurity strategies.
Moreover, New Relic offers real-time vulnerability scanning, which is exceptionally crucial in today's rapidly-evolving digital landscape where new threats emerge by the minute. With its continuous and automatic scanning, you can quickly detect and resolve any security issues. The platform's vulnerability triage feature gives you information based on criticality. Then, it displays a prioritized list of your vulnerable libraries as well as suggestions on which libraries to update to. This is perfect if you are not sure what to prioritize.
Lastly, New Relic's vulnerability scanning is known for its accuracy. The tool's comprehensive scanning capabilities dramatically reduce false positives, ensuring that the IT team's focus is not diverted by irrelevant alerts. The quality of its reporting also provides teams with all the crucial information needed to address vulnerabilities effectively. By providing a clear picture of the security landscape of a system, New Relic makes it easier.
New Relic integrates with over 600 applications within the categories of application monitoring, infrastructure, security, traffic simulation, logging, AWS, Azure, Google Cloud Services, open-source monitoring, machine learning ops, and Prometheus.
Acunetix is a web application and API security scanner designed to automate security testing for organizations, providing a robust solution for identifying, testing, and addressing vulnerabilities in web applications and APIs.
One of the most notable features is its AcuSensor Technology, which combines black-box scanning techniques with feedback from sensors placed inside the source code. This hybrid approach allows for highly accurate scanning with a low false-positive rate, ensuring that developers can trust the results and focus on genuine vulnerabilities.
The software is designed to be user-friendly, with a Login Sequence Recorder that simplifies the testing of password-protected areas and DeepScan technology that can interpret SOAP, XML, AJAX, and JSON. These features make it easier for security teams to conduct comprehensive scans without extensive manual intervention.
Vulnerability scanning tool great for crawling JavaScript-heavy applications
Burp Suite offers vulnerability scanning tools to fit the needs of enterprises and individual QA testers. Enterprise DevSecOps teams benefit from Burp Suite’s ability to automate security testing at scale. Manual and automated penetration testing is available in Burp Suite Professional Edition, which was designed for individual use by security engineers and bug bounty hunters.
Burp Suite features a research-based vulnerability scanning tool known as Burp Scanner. PortSwigger’s research team regularly discovers vulnerabilities before hackers can exploit them, providing advanced protection to users.
Burp Scanner also has a powerful crawl engine that can easily navigate obstacles like CSRF tokens and volatile URLs. It can also handle crawling JavaScript-heavy applications other scanners can’t with its embedded Chromium browser.
Development teams can easily integrate Burp Suite into their tech stack with integrations available for Jenkins and Jira.
Burp Suite Enterprise starts at $6,995/year. Burp Suite Professional costs $399 with a free trial available.
Rapid7
Offers external threat intelligence solution with clear and dark web monitoring
Rapid7 delivers cybersecurity and compliance solutions to help organizations manage vulnerabilities in their IT environment. Security analysts can automate threat monitoring across multiple platforms, including local, cloud, and virtual infrastructure. With Rapid7’s expertly vetted detections, your security team can maintain a high signal-to-noise ratio and mitigate critical threats early.
Rapid7 also protects against external threats with Threat Command. The external threat intelligence tool monitors thousands of sources across the clear and dark web to identify threats targeting your business. Threat Command delivers highly contextualized alerts, enabling teams to turn threat intelligence into action quickly.
Rapid7 users have access to a robust library of integrations with third-party tools, including Azure, Proofpoint, AWS, Teams, Cisco, Slack, and Jira.
Various plans are available for each of Rapid7’s products. Organizations can purchase each solution individually or together.
Other Vulnerability Scanning Software
Here are some additional vulnerability scanning software options that didn’t make it onto my shortlist, but are still worth checking out:
- Tenable
Automates threat prioritization based on in-depth threat analysis
- Imperva
Enterprise-grade cybersecurity solution that guards against complex DDoS attacks
- CyCognito
For attacker-perspective vulnerability check
- Microsoft Baseline Security Analyzer
Free Windows security scanner with built-in remediation guidance
- Intruder
Vulnerability scanner that tracks average remediation time
- Probely
Web app and API vulnerability scanner that’s easily accessible to developers
- Cyberpion
EASM solution with multi-layer vulnerability assessment engine
- beSECURE
Leading provider of governance, risk, and managed security solutions
- Astra Pentest
For continuous vulnerability scanning & pentesting for 9300+ test cases
- GFI Languard
Network security software with patch management tool
Vulnerability Scanning Software Selection Criteria
When selecting the best vulnerability scanning software to include in this list, I considered common buyer needs and pain points like identifying real vulnerabilities and reducing false positives. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Detecting known vulnerabilities
- Scanning web applications
- Providing detailed vulnerability reports
- Offering risk assessment
- Supporting compliance requirements
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Automated patch management
- Real-time threat alerts
- Integration with CI/CD pipelines
- Customizable dashboards
- Advanced threat intelligence
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Simple navigation
- Clear reporting tools
- Minimalistic design
- Accessibility features
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Onboarding templates
- Responsive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multichannel support options
- Knowledgeable support staff
- Quick response times
- Comprehensive help documentation
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Features included in basic plans
- Discounts for annual subscriptions
- Transparent pricing structure
- Cost relative to features offered
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on reliability
- Comments on ease of use
- Opinions on feature effectiveness
- Reports on customer support experience
How to Choose Vulnerability Scanning Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your needs? Consider if it supports increasing asset volumes or additional users without degrading performance or incurring excessive costs. |
| Integrations | Does it integrate with your existing tools? Check for compatibility with your current systems like CI/CD pipelines, ticketing systems, and communication platforms. |
| Customizability | Can you tailor the software to fit your workflows? Look for options to customize dashboards, reports, and alerts to match your team’s processes and preferences. |
| Ease of use | Is the interface intuitive for your team? Evaluate if the design minimizes the learning curve and allows quick access to essential functions. |
| Implementation and onboarding | How long will it take to get up and running? Consider the resources needed for setup, including training materials, support availability, and potential downtime during transition. |
| Cost | Is the pricing transparent and within budget? Compare subscription models, hidden fees, and value provided at each pricing tier to ensure it aligns with your financial plan. |
| Security safeguards | Does it offer adequate protection for your data? Review encryption standards, data storage policies, and compliance with industry regulations to ensure your information remains secure. |
| Compliance requirements | Does it meet your industry's regulatory standards? Verify if the tool supports frameworks like GDPR, HIPAA, or PCI DSS, which are crucial for legal compliance in many sectors. |
What Is Vulnerability Scanning Software?
Vulnerability scanning software is a tool that checks computer systems, networks, and apps for weaknesses that hackers could exploit. IT teams, security analysts, and compliance officers use it to spot things like outdated software, missing updates, or weak spots in settings. It helps you catch problems before attackers do, showing what to fix first and making sure you’re following security rules.
Features
When selecting vulnerability scanning software, keep an eye out for the following key features:
- Automated scanning: Automatically identifies security vulnerabilities without manual intervention, saving time and reducing human error.
- Detailed reporting: Provides comprehensive reports that help prioritize vulnerabilities and guide remediation efforts.
- Integration capabilities: Connects with existing tools like CI/CD pipelines and ticketing systems to streamline workflows.
- Risk assessment: Evaluates the severity of identified vulnerabilities to help prioritize actions based on potential impact.
- Compliance support: Ensures adherence to industry regulations like GDPR, HIPAA, or PCI DSS, maintaining legal compliance.
- Customizable dashboards: Allows users to tailor views and reports to fit specific needs and preferences.
- Real-time alerts: Notifies users of newly discovered vulnerabilities or threats, enabling quick response.
- Patch management: Automates the deployment of security patches, reducing the workload on IT teams.
- Advanced crawling technology: Detects hidden threats in web applications, ensuring thorough coverage.
- Proof-based scanning: Confirms vulnerabilities to reduce false positives, focusing efforts on real threats.
Benefits
Implementing vulnerability scanning software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security posture: Regular scans help identify and fix vulnerabilities, reducing the risk of breaches.
- Time savings: Automated scanning and patch management free up your team's time for other important tasks.
- Regulatory compliance: Ensures your systems meet industry standards, helping avoid legal penalties.
- Risk prioritization: Detailed reports and risk assessments help focus resources on the most significant threats.
- Enhanced decision-making: Customizable dashboards and reports provide insights that support informed security strategies.
- Quick threat response: Real-time alerts enable your team to act fast when new vulnerabilities are detected.
- Reduced false positives: Proof-based scanning ensures that efforts are directed at genuine threats, not false alarms.
Costs & Pricing
Selecting vulnerability scanning software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in vulnerability scanning software solutions:
Plan Comparison Table for Vulnerability Scanning Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic scanning capabilities, limited reporting, and community support. |
| Personal Plan | $5-$25/user/month | Automated scanning, customizable dashboards, and email alerts. |
| Business Plan | $25-$100/user/month | Advanced reporting, integration capabilities, and compliance support. |
| Enterprise Plan | $100-$500/user/month | Full feature access, dedicated support, advanced analytics, and custom integrations. |
Vulnerability Scanning Software FAQs
Here are some answers to common questions about vulnerability scanning software:
What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning identifies potential security weaknesses in your system, while penetration testing involves actively exploiting those vulnerabilities to assess their impact. Scanning is typically automated and provides a broad overview, whereas penetration testing is more manual and detailed. Use vulnerability scanning for regular checks and penetration testing for in-depth analysis.
How often should you run vulnerability scans?
Run vulnerability scans at least monthly, but more frequently if your systems change often. Regular scanning helps catch new vulnerabilities and keeps your security measures up-to-date. If you’re in a highly regulated industry, you might need to scan more often to meet compliance standards.
Can vulnerability scanning software detect all security issues?
No, vulnerability scanning software can’t detect all security issues. While it identifies known vulnerabilities, it may miss zero-day threats or newly discovered vulnerabilities. Combine scanning with other security practices like penetration testing and monitoring to provide a more comprehensive security approach.
Is vulnerability scanning software difficult to set up?
No, most modern vulnerability scanning software is designed to be user-friendly and quick to set up. You’ll typically follow a guided setup process, and many tools offer templates or automated configurations. However, more advanced features might require a deeper understanding of your network architecture.
What’s Next:
If you're in the process of researching vulnerability scanning software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.