10 Best PKI Software Shortlist
Here's my pick of the 10 best software from the 23 tools reviewed.
Managed PKI software helps you issue, track, and renew digital certificates so your team can secure systems without constantly fighting expiration dates, compliance gaps, or manual key handling.
Many teams turn to these tools after spending too much time chasing down expiring certs, juggling internal processes, or worrying that something will slip through the cracks during audits. It's not that public key infrastructure is new, it's that managing it at scale without dedicated tools can quickly become unmanageable.
I’ve worked with organizations to select and implement PKI tools that reduce risk, meet policy requirements, and make certificate management less of a burden on already stretched teams. This guide is built around that experience, to help you choose a solution that fits your environment and gives you back time to focus on other priorities.
Why Trust Our Software Reviews
Best PKI Software Summary
This comparison chart summarizes pricing details for my top PKI software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for automated security management | Not available | Pricing upon request | Website | |
| 2 | Best for certificate lifecycle tasks | Not available | Pricing upon request | Website | |
| 3 | Best for brand-backed reliability | Not available | From $7.50/user/month (billed annually) | Website | |
| 4 | Best for Windows-based PKI setups | Not available | From $972/user (billed annually) | Website | |
| 5 | Best for enterprise certificate issuance | Not available | Pricing upon request | Website | |
| 6 | Best for multi-protocol integration | Not available | Open source project and Available for free | Website | |
| 7 | Best for zero-touch certificate renewal | Not available | Pricing upon request | Website | |
| 8 | Best for protocol and hardware support | Not available | Pricing upon request | Website | |
| 9 | Best for flexible PKI deployment | Not available | Pricing upon request | Website | |
| 10 | Best for digital identity control | Not available | From $10/user/month (billed annually) | Website |
-

Aikido Security
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.7 -

ManageEngine Log360
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.2 -

Dynatrace
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.5
Best PKI Software Reviews
Below are my detailed summaries of the best PKI software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
HashiCorp Vault takes charge of your digital security, providing a comprehensive suite for identity-based access and safeguarding sensitive data across various systems. The tool impressively automates the management of secrets, encryption keys, and certificates.
Why I Picked HashiCorp Vault:
I chose HashiCorp Vault due to its commitment to security automation. In the dynamic landscape of digital security, Vault excels at streamlining the process and reducing manual oversight. The tool's remarkable focus on automation provides a formidable shield for sensitive data.
Hence, I believe HashiCorp Vault truly stands out as the best choice for businesses needing to handle automated security management.
Standout Features and Integrations:
Vault’s dynamic secrets feature reduces the risk of unwanted data exposure by creating secrets on demand that get revoked after use. Its encryption as a service module allows users to encrypt data without dealing with the complexities of key management.
As for integrations, Vault plugs into your existing infrastructure seamlessly. It works well with popular platforms like AWS, Google Cloud, and Azure, providing extensive coverage.
Pros and Cons
Pros:
- Dynamic secrets ensure maximum data safety
- Wide array of integrations for versatile deployment
- Robust and flexible key and secrets management
Cons:
- Pricing structure is not transparently listed
- Detailed documentation may be overwhelming
- Steep learning curve for new users
DigiCert PKI Platform provides scalable and reliable high-assurance certificate solutions. It shines in lifecycle management by simplifying and automating the processes of issuing, renewing, and managing digital certificates, making it the best choice for these tasks.
Why I Picked DigiCert PKI Platform:
I chose the DigiCert PKI Platform due to its comprehensive approach to certificate lifecycle management, which makes it stand out among other tools. Its automation of intricate certificate-related processes supports why it's the best for lifecycle management, ensuring certificate operations remain efficient and streamlined.
Standout Features and Integrations:
The platform's notable features include automated certificate issuance and renewal, intuitive UI for easy management, and robust APIs for integration. DigiCert PKI Platform also offers key integrations with widely used systems like Microsoft Active Directory, Microsoft Autoenrollment, and other IT infrastructure components, extending its certificate lifecycle management capabilities into these environments.
Pros and Cons
Pros:
- Offers a user-friendly management interface
- Robust APIs enable integration with various systems
- Streamlines certificate issuance and renewal processes
Cons:
- Setup and configuration can be time-consuming
- Some users may find the platform’s extensive features overwhelming
- Pricing structure can be complex and is not directly available
GoDaddy PKI Platform is a comprehensive security solution that helps organizations manage digital certificates for their systems and services. GoDaddy, as a globally recognized brand, ensures that its PKI platform is backed by a level of trust and reliability that's hard to beat.
Why I Picked GoDaddy PKI Platform:
In choosing tools for this list, GoDaddy PKI Platform stood out for its association with a highly trusted brand in the domain and hosting industry. Its global recognition provides a level of reliability, which was the deciding factor in determining it as the best for reliability among the lot.
Standout Features and Integrations:
GoDaddy PKI Platform comes with robust features, including management of SSL/TLS certificates and multiple domain support. Its integrations are noteworthy too, featuring support for various servers and systems like Apache, Microsoft servers, and more.
Pros and Cons
Pros:
- Good integration with various servers and systems
- Supports the management of multiple domain certificates
- Backed by a globally recognized and trusted brand
Cons:
- Some advanced features may only be available at higher pricing tiers
- Support services have received mixed reviews
- The pricing structure may be complicated for some
Best for Windows-based PKI setups
Microsoft Active Directory Certificate Services (AD CS) is a role in Windows Server that allows the creation of a fully functional public key infrastructure (PKI). Being tightly integrated with the Microsoft ecosystem, it becomes the go-to PKI solution for Windows-centric environments.
Why I Picked Microsoft Active Directory Certificate Services (AD CS):
In the process of selecting PKI tools, AD CS caught my attention due to its seamless integration within the Microsoft ecosystem. This integration, I believe, positions it as the best choice for Windows-centric environments, where it can provide a streamlined and native PKI solution.
Standout Features and Integrations:
AD CS features include the ability to customize certificate contents and extensions, and it supports automated certificate issuance through templates. Its biggest strength is its integration with Microsoft Active Directory, allowing for simple deployment and management of certificates within a Windows environment.
Pros and Cons
Pros:
- Automated certificate issuance through templates
- Customizable certificate contents and extensions
- Seamless integration within the Microsoft ecosystem
Cons:
- Requires a Windows Server license, which can be pricey for smaller organizations
- Can be complex to set up without a good understanding of PKI principles
- Limited to Windows environments
GlobalSign PKI is a platform designed to secure organizations' digital identities at scale. It excels in issuing large volumes of certificates and automated enrollment, making it a top choice for businesses seeking robust, enterprise-level protection.
Why I Picked GlobalSign PKI:
When selecting tools for this list, I evaluated each based on their distinctive qualities. GlobalSign PKI emerged due to its capacity to handle high-volume issuance and automated enrollment, which are critical in enterprise-level protection. This robust capability justifies why I believe it is the best for businesses that require extensive protection.
Standout Features and Integrations:
GlobalSign PKI has a robust set of features, including certificate lifecycle management, automated enrollment, and support for multiple certificate types. It offers integrations with Microsoft Active Directory and other IT infrastructure systems, ensuring wide coverage of protection across different organizational applications.
Pros and Cons
Pros:
- Offers automated enrollment for ease of use
- Handles high-volume certificate issuance efficiently
- Provides extensive enterprise-level protection
Cons:
- The platform may have a steep learning curve for those new to PKI solutions
- Some customers have reported slow customer service response times
- Lack of transparent pricing can be challenging for potential users
Keycloak is an open-source Identity and Access Management solution that can authenticate users with existing LDAP or Active Directory credentials. Its edge lies in providing out-of-the-box support for multiple protocols, which supports seamless integration and makes it the best choice for this specific need.
Why I Picked Keycloak:
Keycloak earned its place on this list for its strong integrative capabilities, particularly its native support for multiple protocols. I selected it as the best for seamless integration as it ensures a simplified and efficient setup across diverse systems, which sets it apart in the marketplace.
Standout Features and Integrations:
Keycloak excels with features like Single-Sign-On (SSO), identity brokering, and its built-in support for multiple protocols such as OpenID Connect, SAML 2.0, and LDAP. Keycloak can also integrate smoothly with various applications and services, including microservices, monoliths, and cloud services, making it versatile for many infrastructural setups.
Pros and Cons
Pros:
- Versatile integration with various types of applications and services
- Strong feature set including SSO and identity brokering
- Support for multiple protocols enables seamless integration
Cons:
- Updates and new features are dependent on the open-source community
- Support is reliant on community or paid services
- May require technical expertise for setup and management
Venafi is a distinguished PKI platform that centralizes and automates the lifecycle of digital certificates. Because of its automation features, particularly zero-touch issuance, and renewal of certificates, Venafi is best suited for those who seek streamlined certificate management.
Why I Picked Venafi:
When I was determining which PKI platform to include on this list, Venafi stood out due to its advanced automation capabilities. Its feature of zero-touch issuance and renewal of certificates distinguishes it from the crowd, leading to my decision that it is best for automation.
Standout Features and Integrations:
Venafi stands out with its advanced automation for the lifecycle of certificates, including issuance, renewal, and revocation. In addition to this, it integrates with leading IT systems like cloud providers, DevOps tools, and more, making it a highly adaptable platform.
Pros and Cons
Pros:
- Provides visibility into all machine identities and their associated risks
- Integrates with leading IT systems
- Advanced automation of certificate lifecycle
Cons:
- Customer support may be slow during off-peak hours
- Can be complex to set up and manage without adequate training
- Pricing is not transparent and requires a custom quote
Best for protocol and hardware support
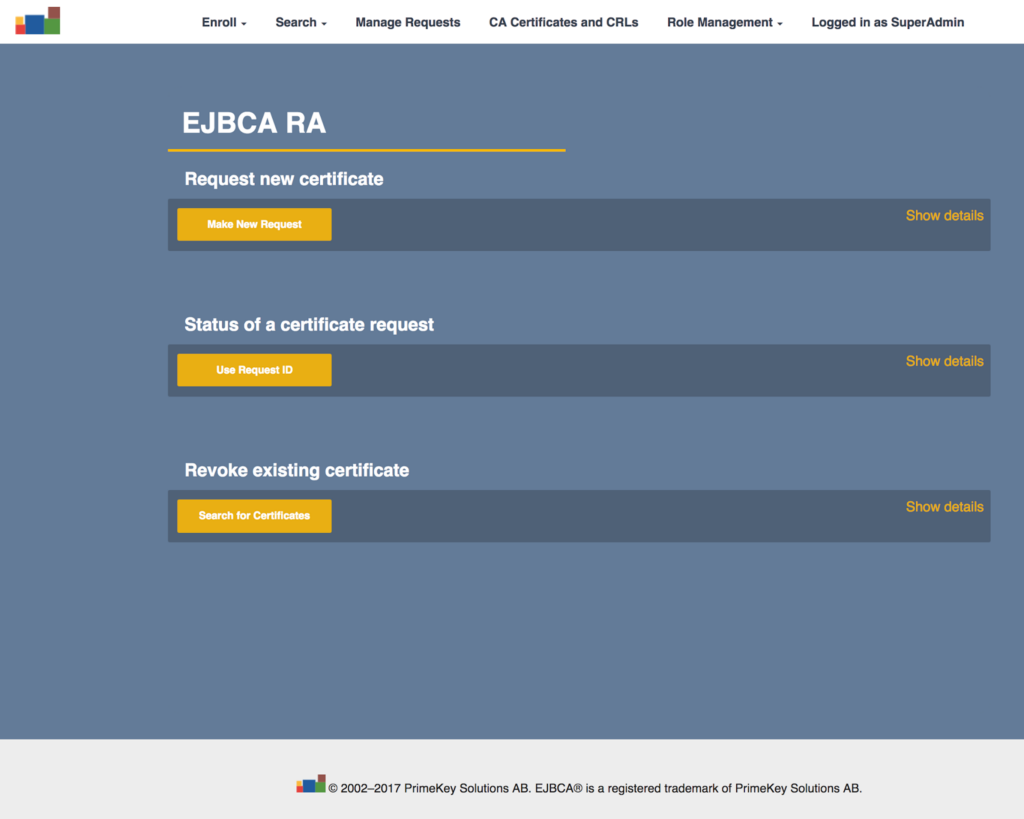
EJBCA is a robust, platform-agnostic PKI solution, designed to enable seamless issuance and management of digital certificates. Given its ability to support all major protocols and hardware, EJBCA is best for interoperability in diverse IT environments.
Why I Picked EJBCA:
I selected EJBCA for this list because it stands apart with its broad interoperability. Its compatibility with major protocols and hardware sets it apart and makes it an ideal choice for diverse IT ecosystems. Therefore, I judged it to be the best for interoperability.
Standout Features and Integrations:
EJBCA boasts a rich feature set, including extensive certificate life cycle management, flexible integrations, and support for hardware security modules. It integrates with a variety of platforms and devices, reinforcing its standing as a versatile, interoperable PKI solution.
Pros and Cons
Pros:
- Extensive platform and device integrations
- Robust certificate life cycle management
- High interoperability with major protocols and hardware
Cons:
- Community support may not be as responsive or comprehensive as Enterprise support
- May be complex to set up for those unfamiliar with Java-based applications
- Enterprise version pricing is not publicly available
PrimeKey EJBCA® Enterprise serves as a robust Certificate Authority, ensuring secure and flexible management of digital identities. The software is tailored to meet the needs of organizations of all scales, providing a range of customizable options to match the complexity of varying IT environments.
Why I Picked PrimeKey EJBCA® Enterprise:
I selected PrimeKey EJBCA® Enterprise for its adaptability. In a tech landscape teeming with varying needs and use cases, this PKI solution's customizable nature offers a clear advantage. Its ability to mold itself to the unique requirements of an organization makes it the best for those seeking a flexible deployment option.
Standout Features and Integrations:
PrimeKey EJBCA® Enterprise shines with its powerful certificate management system and adaptable workflows. It supports multiple Certificate Authority (CA) hierarchies and a wide array of certificate profiles. On the integration front, it syncs well with HSMs from vendors like Thales and Utimaco, and it offers a REST API for seamless integration with existing IT infrastructure.
Pros and Cons
Pros:
- Robust integration options, including REST API
- Comprehensive certificate and workflow management
- Versatile and customizable to suit unique requirements
Cons:
- Transparent pricing information is not available
- Support might be required for initial setup
- Can be complex for novice users
Ubisecure Certificate Authority is a cutting-edge tool that goes beyond the traditional role of a PKI solution. Not only does it manage digital certificates, but it also shines in its comprehensive approach to identity lifecycle management.
Why I Picked Ubisecure Certificate Authority:
I was drawn to Ubisecure for its robust and comprehensive feature set, particularly around digital identity management. Unlike other tools on this list, Ubisecure presents a broader approach, ensuring all aspects of the digital identity lifecycle are catered to. This makes it stand out, leading me to designate it as the best for digital identity management.
Standout Features and Integrations:
Ubisecure Certificate Authority stands out with its identity-proofing capabilities, identity lifecycle management, and multi-factor authentication support. This tool seamlessly integrates with existing IT environments and supports numerous protocols such as SAML, OAuth, and OpenID Connect, extending its reach and applicability.
Pros and Cons
Pros:
- Strong support for multi-factor authentication
- Robust integration capabilities
- Comprehensive approach to identity management
Cons:
- Limited third-party reviews available for the software
- The user interface may be complex for beginners
- Pricing might be steep for small businesses
Other PKI Software
Here are some additional PKI software options that didn’t make it onto my shortlist, but are still worth checking out: I couldn’t find specific information on PKI software vendors.
- OpenXPKI
Open-source PKI solution
- KeyTalk
For large-scale encryption coverage
- Dogtag Certificate System
For open-source enterprise PKI
- FreeIPA
For Linux-based identity services
- GlobalSign IoT Identity Platform
For identity at IoT scale
- GnuPG
For free OpenPGP-compliant encryption
- keyfactor Command
For complex certificate management
- OpenCA PKI
For flexible academic PKI setups
- OpenSSL
For open-source cryptography tools
- RSA Certificate Manager
For large certificate operations
- Sectona
For controlling privileged account access
- SecureW2
For secure Wi-Fi onboarding
- SafeNet Trusted Access
For smart access and authentication
PKI Software Selection Criteria
When selecting the best PKI software to include in this list, I considered common buyer needs and pain points like managing digital certificates and ensuring data encryption. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Manage digital certificates
- Encrypt sensitive data
- Support multiple authentication methods
- Automate certificate lifecycle management
- Ensure compliance with security standards
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Cloud-based certificate management
- Integration with IoT devices
- Advanced analytics and reporting
- Customizable security policies
- Blockchain-based security
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Clear documentation
- Responsive design
- Customizable dashboard
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive user guides
- Onboarding templates
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 support availability
- Multichannel support options
- Knowledgeable support staff
- Quick response times
- Access to online help centers
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Flexible subscription plans
- Transparent pricing structure
- Discounts for long-term commitments
- Cost relative to features offered
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Overall satisfaction ratings
- Feedback on ease of use
- Comments on feature effectiveness
- Support experience reviews
- Value for money feedback
How to Choose PKI Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your organization? Consider future needs and whether the tool can handle increased certificate volume without performance issues. |
| Integrations | Does it work with your existing systems? Check for compatibility with your current IT infrastructure and any third-party applications you rely on. |
| Customizability | Can you tailor the software to fit your processes? Look for options to customize workflows, policies, and user permissions to match your team's needs. |
| Ease of use | Is the interface user-friendly? A tool that's hard to use can hinder productivity. Look for intuitive navigation and clear instructions. |
| Implementation and onboarding | How long will it take to get up and running? Consider the time and resources needed for setup, and whether the vendor provides adequate onboarding support. |
| Cost | Does the pricing fit your budget? Evaluate not just the upfront costs but also any hidden fees or long-term expenses that may arise. |
| Security safeguards | Are there strong security measures in place? Ensure the software complies with industry standards and offers features like encryption and access controls. |
| Compliance requirements | Does it meet regulatory needs? Check if the software supports compliance with data protection regulations relevant to your industry. |
What Is PKI Software?
PKI software is a tool that helps manage digital certificates and encryption keys to keep data and systems secure. It's mostly used by IT teams, security professionals, and system administrators who need to protect internal systems, user identities, and online communications.
Features like certificate issuance, renewal tracking, and key storage help with staying organized, reducing manual work, and avoiding expired or mismanaged certificates. These tools make it easier to handle encryption without adding extra stress to your workflow.
Features
When selecting PKI software, keep an eye out for the following key features:
- Certificate management: Automates the issuance, renewal, and revocation of digital certificates, saving time and reducing errors.
- Encryption: Protects sensitive data by converting it into a secure format that can only be accessed by authorized users.
- User authentication: Ensures only authorized individuals can access systems and data by verifying user identities.
- Compliance support: Helps organizations adhere to industry regulations and standards, reducing the risk of non-compliance penalties.
- Integration capabilities: Works seamlessly with existing IT infrastructure and third-party applications to maintain workflow continuity.
- Customizable policies: Allow for the creation of tailored security policies to fit specific organizational needs and requirements.
- Scalability: Accommodates growing certificate volumes and organizational changes without compromising performance.
- Access controls: Provide granular control over who can access certain data or systems, enhancing overall security.
- Audit logging: Records system activities for monitoring and analyzing security incidents, aiding in forensic investigations.
- User-friendly interface: Offers intuitive navigation and clear instructions, making it easier for users to manage and operate the software.
Benefits
Implementing PKI software provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Encrypts data and ensures only authorized users have access, protecting your sensitive information.
- Regulatory compliance: Supports adherence to industry standards and regulations, reducing the risk of non-compliance fines.
- Operational efficiency: Automates certificate management tasks, saving time and minimizing the risk of manual errors.
- Scalability: Grows with your organization, accommodating more users and certificates without needing major changes.
- Improved trust: Verifies user identities and encrypts communications, building trust with clients and partners.
- Cost savings: Reduces the need for manual processes and potential security breaches, saving money in the long run.
- Audit readiness: Provides detailed logs and reports for security audits, making it easier to identify and address vulnerabilities.
Costs and Pricing
Selecting PKI software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in PKI software solutions:
Plan Comparison Table for PKI Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic certificate management, limited support, and minimal encryption options. |
| Personal Plan | $10-$30/user/month | Enhanced encryption, user authentication, and compliance support. |
| Business Plan | $40-$80/user/month | Advanced certificate lifecycle management, integration capabilities, and scalability. |
| Enterprise Plan | $100-$200/user/month | Customizable policies, comprehensive support, and extensive audit logging. |
PKI Software FAQs
Here are some answers to common questions about PKI software:
How do you manage digital certificates?
Managing digital certificates involves issuing, renewing, and revoking certificates as needed. You’ll need a system that automates these tasks to reduce errors and save time. PKI software often includes tools to track certificate status and alert you to upcoming expirations.
What is the role of a certification authority?
A certification authority (CA) is a trusted entity that issues digital certificates. These certificates verify the identity of the certificate holder. When choosing PKI software, ensure it supports integration with established CAs or allows you to set up your own.
How does PKI software enhance security?
PKI software enhances security by encrypting data and verifying identities. It uses public and private keys to secure communications. When evaluating options, consider how effectively the software manages keys and whether it supports multi-factor authentication.
Are PKI software tools difficult to use?
The difficulty level can vary depending on the tool. Some PKI software has a steep learning curve due to its extensive features and capabilities. However, most modern PKI tools prioritize user experience, offering intuitive interfaces and comprehensive support to aid in user onboarding and ongoing use.
Can PKI software integrate with existing systems?
Integration is key for a smooth workflow. Most PKI software can connect with IT infrastructure and third-party applications. Check for compatibility with your current systems to avoid disruptions and ensure seamless operations.
How does PKI software handle scalability?
Scalability ensures the software grows with your needs. Whether you’re expanding your team or increasing certificate use, the software should handle more users and data without performance issues. Consider your future plans when assessing scalability options.
What’s Next:
If you're in the process of researching PKI software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.