10 Best Cybersecurity Risk Management Software Shortlist
I reviewed leading cybersecurity risk management software that helps security teams prioritize vulnerabilities, conduct risk assessments, manage third-party risk management, and meet regulatory compliance requirements. This guide focuses on tools designed to reduce risk exposure across modern IT environments.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Cybersecurity Risk Management Software Summary
This comparison chart summarizes pricing, core functions, and use cases for the cybersecurity risk management software in this guide. It helps security teams compare tools, assess scalability, and shortlist options that align with their risk management program, budget, and regulatory requirements.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for AI-driven threat detection | Free demo available | From $179.99/endpoint (billed annually) | Website | |
| 2 | Best for unified attack surface management | 30-day free trial + free demo available | Pricing upon request | Website | |
| 3 | Best for cybersecurity ratings | Free demo available | Pricing upon request | Website | |
| 4 | Best for integrated risk management | Free demo available | From $25/user/month (billed annually, min 5 seats) | Website | |
| 5 | Best for comprehensive risk visibility | Free demo available | Pricing upon request | Website | |
| 6 | Best for continuous security ratings | 14-day free trial + free demo available | Pricing upon request | Website | |
| 7 | Best for financial institutions | Free demo available | Pricing upon request | Website | |
| 8 | Best for AI-driven third-party risk analysis | Free demo available | Pricing upon request | Website | |
| 9 | Best for continuous controls monitoring | Free demo available | Pricing upon request | Website | |
| 10 | Best for third-party risk management | Free trial + free demo available | Pricing upon request | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Cybersecurity Risk Management Software Reviews
Below are concise reviews of the cybersecurity risk management software on my shortlist. Each review covers key functions, standout features, pros and cons, integrations, and ideal use cases to support informed decisions based on your risk posture and requirements.
SentinelOne is an AI-powered cybersecurity platform used by security teams to detect, analyze, and respond to cyber threats across endpoints, cloud workloads, and identities. It’s commonly adopted by mid-sized and enterprise organizations that need real-time detection, automated remediation, and visibility across the attack surface.
Why I picked SentinelOne: SentinelOne stands out for its AI-driven threat detection and automated remediation, powered by behavioral analysis and machine learning. Its Singularity platform unifies endpoint, cloud, and identity security, helping teams reduce risk exposure and maintain visibility as environments scale.
Standout features & integrations:
Features include automated threat detection, real-time threat analysis, and integrated endpoint, cloud, and identity security. Reporting tools provide actionable insights into security risks.
Integrations include CrowdStrike, Splunk, IBM QRadar, Palo Alto Networks, McAfee, Fortinet, ServiceNow, Microsoft Azure, AWS, and Google Cloud.
Pros and Cons
Pros:
- Broad integration ecosystem
- Real-time threat analysis
- Automated threat response
Cons:
- May be more complex than needed for small businesses
- Steeper learning curve for smaller security teams
Qualys is a cybersecurity risk management platform focused on vulnerability management, threat detection, and compliance management across cloud-based and on-prem environments.
Why I picked Qualys: Qualys stands out for its unified attack surface management, combining automated scanning with continuous monitoring. Linking vulnerability data with compliance management helps security teams prioritize risks and maintain regulatory compliance across dynamic environments.
Standout features & integrations:
Features vulnerability and configuration management, threat detection and response, and cloud security capabilities that support continuous monitoring across environments.
Integrations include ServiceNow, Splunk, IBM QRadar, Microsoft Azure, AWS, Palo Alto Networks, McAfee, Fortinet, Tenable, and Salesforce.
Pros and Cons
Pros:
- Links threat detection with compliance management
- Strong continuous monitoring and vulnerability scanning
- Unified attack surface management across assets
Cons:
- Less flexible for highly customized risk workflows
- Can be complex for small security teams without dedicated resources
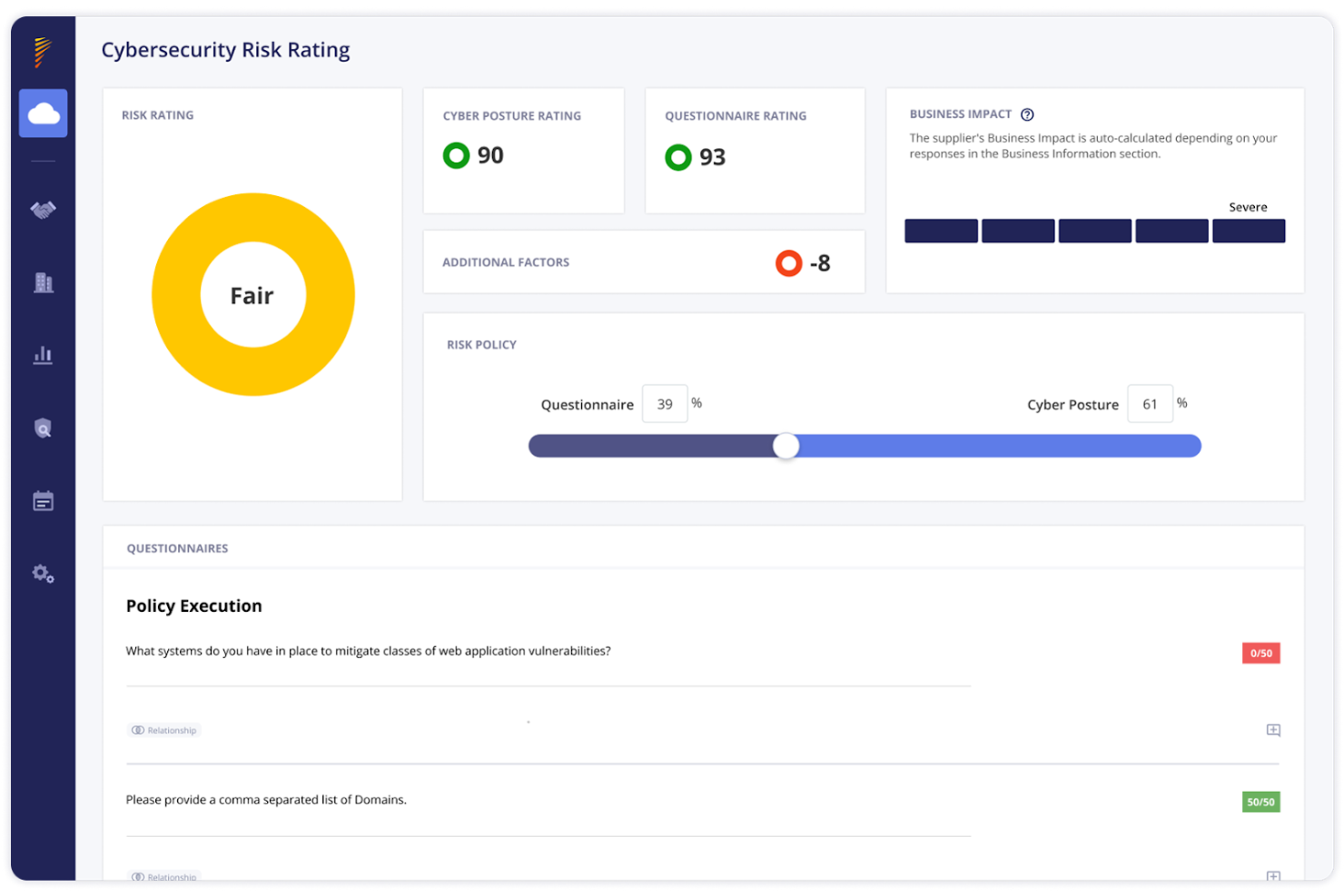
BitSight is a cybersecurity risk management platform focused on third-party risk management and threat intelligence. It’s used by enterprises that need continuous monitoring, risk assessments, and visibility into their security posture.
Why I picked BitSight: BitSight stands out for its security ratings and exposure insights built on continuous monitoring. Real-time data discovery and a broad risk dataset help teams assess vendor risk and overall risk posture. This approach supports informed decisions without requiring deep internal telemetry.
Standout features & integrations:
Features include exposure management for risk identification, cyber threat intelligence for emerging threats, and governance and reporting tools that support compliance and decision-making.
Integrations include ServiceNow, Splunk, IBM QRadar, Palo Alto Networks, AWS, Microsoft Azure, Tenable, McAfee, Fortinet, and Salesforce.
Pros and Cons
Pros:
- Strong third-party risk management support
- Continuous monitoring with broad risk coverage
- Clear security ratings for external risk visibility
Cons:
- Limited visibility into internal controls compared to internal-first tools
- Better suited to enterprise risk programs than small teams
Riskonnect is cybersecurity risk management software used across industries such as healthcare, finance, and manufacturing. It supports IT risk, compliance management, and enterprise risk management with a focus on visibility and informed decision-making.
Why I picked Riskonnect: Riskonnect stands out for integrating risk management processes across IT, compliance, and enterprise workflows. Built-in risk assessments and financial impact analysis support data-driven decision-making. Dashboards provide a clear visualization of assets, vulnerabilities, and risk posture.
Standout features & integrations:
Features include policy and internal control management for compliance, threat intelligence to detect emerging threats, and risk remediation tools to address vulnerabilities.
Integrations include Salesforce, Microsoft Azure, AWS, ServiceNow, IBM QRadar, Palo Alto Networks, McAfee, Fortinet, Tenable, and Splunk.
Pros and Cons
Pros:
- Financial impact analysis for prioritizing risks
- Clear dashboards for risk visibility
- Strong integrated risk management across functions
Cons:
- May feel complex for smaller teams
- Setup and configuration can be time-consuming
Centraleyes is a cybersecurity risk management platform used by organizations in regulated industries, such as finance, insurance, energy, and higher education. It focuses on risk management, compliance management, and third-party risk management.
Why I picked Centraleyes: Centraleyes stands out for providing comprehensive visibility across risk management and compliance workflows. Support for more than 180 regulatory requirements makes it well-suited to highly regulated industries. Executive dashboards and AI governance tools help stakeholders stay informed.
Standout features & integrations:
Features include AI governance automating compliance tasks, executive dashboards for stakeholders, and regulatory watch services that track changes to industry standards.
Integrations include Microsoft Azure, AWS, ServiceNow, Splunk, Salesforce, IBM QRadar, Palo Alto Networks, McAfee, Fortinet, and Tenable.
Pros and Cons
Pros:
- Strong visibility across compliance and risk workflows
- Built-in third-party risk management
- Supports 180+ compliance frameworks
Cons:
- May feel complex for smaller organizations
- Setup and configuration can be time-consuming
SecurityScorecard is a cybersecurity risk management platform that provides continuous security ratings for internal environments and third-party vendors, helping teams monitor security posture at scale.
Why I picked SecurityScorecard: SecurityScorecard stands out for its continuous security ratings that surface changes in risk posture across internal systems and vendors. Its scoring model helps security teams prioritize vulnerabilities and take action without deep internal telemetry.
Standout features & integrations:
Features a user-friendly security rating system, continuous monitoring of risk signals, and reporting that supports corrective action and risk mitigation.
Integrations include ServiceNow, Splunk, IBM QRadar, Microsoft Azure, AWS, Palo Alto Networks, McAfee, Fortinet, Tenable, and Salesforce.
Pros and Cons
Pros:
- Strong third-party risk visibility
- Easy-to-interpret scoring for risk prioritization
- Clear, continuous security ratings for internal and vendor risk
Cons:
- Best suited to external risk and vendor monitoring rather than deep internal analysis
- Limited visibility into internal controls compared to telemetry-heavy tools
Ncontracts is cybersecurity risk management software tailored for financial institutions such as banks and credit unions. It supports enterprise risk management, vendor risk management, and compliance management to help organizations manage risk and meet regulatory requirements.
Why I picked Ncontracts: Ncontracts stands out for its focus on financial institutions and specialized compliance management. Real-time risk analysis and tailored regulatory updates support informed decisions in highly regulated environments. Built-in vendor lifecycle management and automated audit processes align well with financial compliance needs.
Standout features & integrations:
Features include real-time risk analysis, tailored regulatory updates, and automated audit processes that streamline compliance management.
Integrations include Salesforce, Microsoft Azure, AWS, ServiceNow, IBM QRadar, Palo Alto Networks, McAfee, Fortinet, Tenable, and Splunk.
Pros and Cons
Pros:
- Built-in vendor risk management workflows
- Strong support for regulatory compliance
- Specialized for financial institutions
Cons:
- Setup and configuration can be time-consuming
- Less suitable for non-financial industries
SAFE Security is a unified, AI-driven cybersecurity risk management platform that gives security teams visibility across first-party and vendor environments. It helps translate technical exposures into business context through continuous monitoring, vendor onboarding, and risk quantification.
Why I picked SAFE Security: Its AI-powered approach to third-party risk management sets it apart. Agentic AI automates vendor discovery and questionnaire workflows, while FAIR-based risk quantification links control gaps to business impact. This helps stakeholders make informed decisions using financially grounded risk metrics.
Standout features & integrations:
Features include automated vendor intake and questionnaire processing, continuous monitoring of vendor attack surfaces, and data-driven risk quantification that translates control gaps into business-impact metrics.
Integrations include a marketplace of 100+ tools, including AWS, Azure, and CrowdStrike Falcon.
Pros and Cons
Pros:
- Risk quantification tied to business impact
- Continuous monitoring across vendor and internal environments
- Strong AI-driven third-party risk management workflows
Cons:
- Risk quantification models may require stakeholder education and tuning
- Implementation complexity may be high for smaller security teams
CyberSaint is a cybersecurity risk management platform designed for enterprises aiming to assess, measure, and manage cyber risks. It primarily serves security teams and executives by providing tools for compliance management and risk quantification.
Why I picked CyberSaint: CyberSaint stands out for its continuous controls monitoring, which provides real-time compliance visibility and a clearer security posture. AI-driven insights help security teams prioritize vulnerabilities, while automated questionnaires streamline third-party risk management and reduce manual effort.
Standout features & integrations:
Features include real-time compliance monitoring, which keeps your team updated on security standards. The platform also offers AI-driven risk insights to help prioritize cybersecurity actions. Additionally, it automates vendor questionnaires, easing the burden of third-party risk management.
Integrations include ServiceNow, Splunk, IBM QRadar, Microsoft Azure, AWS, Palo Alto Networks, McAfee, Fortinet, Tenable, and Salesforce.
Pros and Cons
Pros:
- Reduces manual effort in third-party risk management
- AI-driven risk prioritization across controls and vendors
- Strong continuous controls monitoring for compliance
Cons:
- Less flexible for teams needing highly customized dashboards
- Better suited to mature security teams with defined controls
Panorays is a cybersecurity risk management platform focusing on managing third-party cyber risks. It serves organizations across industries like financial services, healthcare, and technology, offering tools for risk assessment, vendor engagement, and continuous monitoring.
Why I picked Panorays: Panorays stands out for its Risk DNA model, which evaluates third-party cybersecurity posture and attack surface exposure. Continuous monitoring and vendor engagement tools help teams prioritize remediation and maintain visibility across the supply chain.
Standout features & integrations:
Features real-time third-party risk assessments, actionable threat alerts, and vendor self-guided remediation plans.
Integrations include ServiceNow, Splunk, IBM QRadar, Microsoft Azure, AWS, Palo Alto Networks, McAfee, Fortinet, Tenable, and Salesforce.
Pros and Cons
Pros:
- Improves supply chain risk visibility
- Clear vendor engagement and remediation workflows
- Strong third-party risk management with continuous monitoring
Cons:
- Less focused on internal risk management use cases
- Better suited to teams managing a large vendor ecosystem
Other Cybersecurity Risk Management Software
Here are some additional cybersecurity risk management software options that didn’t make the list, but may still be worth evaluating:
- Balbix
For predictive breach risk reduction
- Axonius
For asset management
- JupiterOne
For mapping asset relationships and risk dependencies
- Sevco
For continuous asset discovery and exposure tracking
- StandardFusion
For mid-size organization risk and incident work
- ServiceNow
For linking risk tasks with daily work
- Vanta
For lightweight vendor risk checks
- isorobot
For mapping controls across teams
Cybersecurity Risk Management Software Selection Criteria
When selecting cybersecurity risk management software for this list, I considered common buyer needs such as identifying vulnerabilities and meeting regulatory compliance requirements. I also used the following framework to keep the evaluation structured and consistent:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Identify vulnerabilities
- Manage compliance
- Monitor cyber threats
- Assess risks
- Automate reporting
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Real-time threat intelligence
- AI-driven risk analysis
- Third-party risk management
- Integration with existing security tools
- Customizable dashboards
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Easy navigation
- Minimal learning curve
- Clear instructions
- Responsive design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to templates
- Chatbot assistance
- Webinars and workshops
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multiple support channels
- Quick response times
- Knowledgeable staff
- Comprehensive documentation
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Feature set versus cost
- Flexible pricing plans
- Discounts for longer commitments
- Free trial availability
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- Positive feedback on functionality
- Praise for ease of use
- Satisfaction with support services
- Complaints about pricing
- Experiences with the onboarding process
How to Choose Cybersecurity Risk Management Software
It’s easy to get bogged down in long feature lists and complex pricing. To stay focused during your software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Will the software grow with your organization? Consider future expansion and whether it can handle increased data volume and users. |
| Integrations | Does it integrate with existing tools? Check compatibility with SIEMs, cloud providers, and your current security ecosystem to avoid data silos. |
| Customizability | Can you tailor the software to your needs? Look for customizable dashboards and reports that support your risk management workflows. |
| Ease of use | Is the interface intuitive? User-friendly tools reduce training time and improve adoption across security teams. |
| Implementation and onboarding | How quickly can you get started? Consider setup effort, onboarding support, and available training resources. |
| Cost | Is the pricing transparent and within budget? Compare upfront and ongoing costs and evaluate value, not just price. |
| Security safeguards | Does the software meet security standards? Look for encryption, access controls, and safeguards that protect sensitive data. |
| Compliance requirements | Does the tool help meet industry regulations? Evaluate coverage for standards such as GDPR, HIPAA, or ISO 27001 based on your industry. |
What Is Cybersecurity Risk Management Software?
Cybersecurity risk management software helps organizations identify, assess, and mitigate cyber risks across their IT environment. Security teams use these tools to protect sensitive data, manage compliance management, and reduce overall risk exposure. Capabilities such as threat detection, vulnerability assessment, and continuous monitoring support informed decisions and a stronger security posture.
Features
When selecting cybersecurity risk management software, look for the following key features:
- Threat detection: Identifies cyber threats in real time to support faster incident response.
- Vulnerability assessment: Scans systems to identify weaknesses and prioritize risk mitigation efforts.
- Compliance management: Supports regulatory compliance with standards such as GDPR and HIPAA.
- Automated reporting: Generates audit-ready reports on security posture, metrics, and risk exposure.
- Real-time monitoring: Continuously monitors activity across the environment to surface emerging threats.
- Third-party risk management: Assesses vendor risk to protect the supply chain and broader ecosystem.
- Risk prioritization: Uses data-driven analysis to prioritize risks based on impact and likelihood.
- Dashboards and visualization: Provides dashboards that help stakeholders make informed decisions.
- Integration capabilities: Connects with existing security tools to support integrated risk management workflows.
Benefits
Implementing cybersecurity risk management software provides several benefits for your team and your business. Here are a few you can look forward to:
- Improved security posture: Identifies vulnerabilities and cyber threats earlier, helping reduce overall risk exposure.
- Stronger regulatory compliance: Supports compliance management with industry standards such as GDPR, HIPAA, and ISO.
- More efficient risk mitigation: Automates risk assessments and prioritization so security teams focus on the most critical issues.
- Better decision-making: Dashboards, metrics, and visualization provide actionable insights for stakeholders.
- Reduced manual effort: Streamlines workflows such as reporting, questionnaires, and vendor risk management.
- Enhanced third-party risk management: Improves visibility into vendor risk across the supply chain.
- Proactive risk management: Continuous monitoring helps teams address emerging threats before they escalate.
- Cost efficiency over time: Reduces the likelihood of costly cyber attacks, audit findings, and compliance gaps.
Costs & Pricing
Selecting cybersecurity risk management software requires understanding common pricing models and plans. Costs vary based on features, team size, and add-ons. The table below summarizes typical plans, average prices, and included features:
Plan Comparison Table for Cybersecurity Risk Management Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited reporting, and community support. |
| Personal Plan | $5-$25/user /month | Threat detection, vulnerability assessment, and basic compliance management. |
| Business Plan | $30-$75/user /month | Advanced monitoring, automated reporting, third-party risk management, and customizable dashboards. |
| Enterprise Plan | $80-$150/user /month | Full feature set, real-time threat intelligence, broad integration capabilities, and dedicated support. |
Cybersecurity Risk Management Software FAQs
Here are some answers to common questions about cybersecurity risk management software:
How do I determine which software is best for my business?
Start by assessing your organization’s needs, including team size, IT complexity, and regulatory compliance requirements. Focus on software that supports your highest-priority use cases, such as threat detection or compliance management. Trials and demos can help validate workflow fit before committing.
Can I integrate cybersecurity risk management software with my existing systems?
Yes. Most cybersecurity risk management software integrates with SIEMs, cloud platforms, and endpoint security tools. Verify compatibility with your existing ecosystem to avoid data silos and integration gaps.
How often should I update my cybersecurity risk management software?
Regular updates are essential for maintaining security and functionality. Follow vendor update guidance, including patches for vulnerabilities and feature improvements. Automatic updates can help reduce operational risk.
What’s Next:
If you're in the process of researching cybersecurity risk management software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.