ThreatLocker vs. Airlock Digital: Comparison & Expert Reviews For 2026
With ransomware hitting organizations more frequently, you can’t afford to gamble on endpoint security anymore. Traditional antivirus isn’t cutting it—that’s why application allowlisting has become a non-negotiable baseline. If you’re choosing between ThreatLocker and Airlock Digital, you’re already ahead of most organizations still relying on signature-based detection.
I’ll walk you through the real differences between these two deny-by-default cybersecurity software, from ThreatLocker’s Ringfencing containment to Airlock Digital’s workflow automation for Essential Eight compliance. I’ll compare pricing structures, deployment timelines, and which platform aligns with your team’s technical maturity.
ThreatLocker vs. Airlock Digital: An Overview
ThreatLocker
Visit ThreatLockerOpens new windowAirlock Digital
Read Airlock Digital ReviewOpens new windowWhy Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
ThreatLocker vs. Airlock Digital Pricing Comparison
| ThreatLocker | Airlock Digital | |
|---|---|---|
| Free Trial | 30-day free trial + free demo available | Free demo available |
| Pricing | Pricing upon request | Pricing upon request |
ThreatLocker vs. Airlock Digital Pricing Hidden Costs
ThreatLocker uses a custom pricing model based on factors like endpoint count, application complexity, and required controls, with no fixed public tiers. While this allows for accurate scoping and predictable budgeting once quoted, organizations must engage with sales to understand the total cost. Potential hidden costs may include higher pricing as environments scale or additional modules are added beyond the initial scope.
Airlock Digital does not publish pricing and requires prospective customers to book a meeting to receive a quote. This lack of upfront pricing transparency makes early cost comparisons difficult and can slow down procurement planning. Hidden costs may only become apparent during sales discussions, such as pricing tied to endpoint growth, feature add-ons, or support requirements. For both platforms, it’s best to request a quote and compare all inclusions to understand the value.
ThreatLocker vs. Airlock Digital Feature Comparison
ThreatLocker delivers modular Zero Trust with four stackable components: Allowlisting, Ringfencing, Elevation Control, and Network Control. Ringfencing is the standout—it stops attackers from weaponizing approved apps like Word or PowerShell by controlling what files, registry keys, and network resources they can access. ThreatLocker’s Unified Audit gives you centralized visibility into every allow/deny decision, cutting SOC alert noise. You’ll enforce least privilege at the application layer, but expect to invest time tuning policies to avoid breaking workflows.
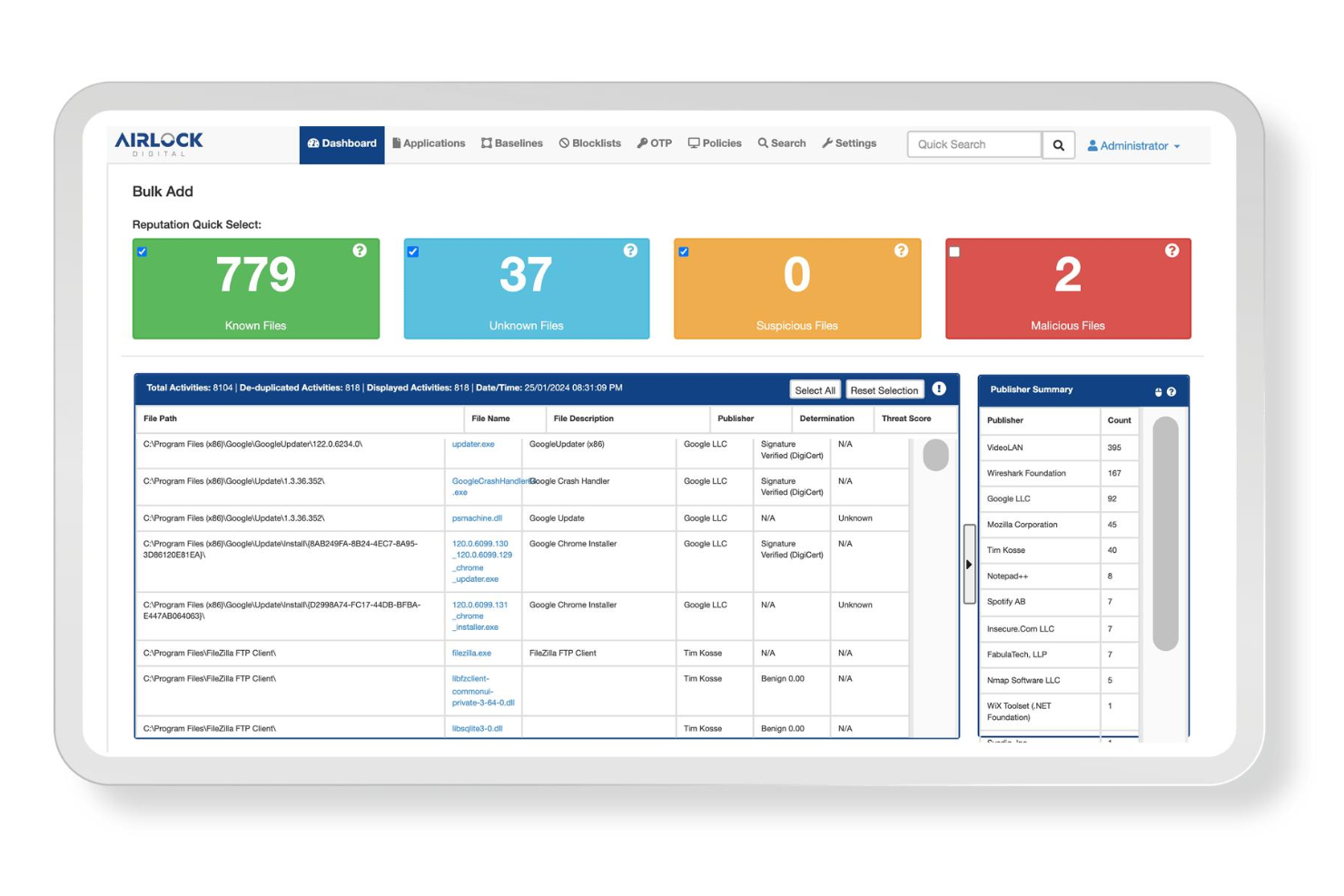
Airlock Digital makes allowlisting operationally practical through workflow-driven automation that prioritizes speed over surgical control. Their discovery engine vets all executable code against a searchable metadata repository and builds flexible policies using repeatable workflows—no scripting required. Airlock requires just a few hours of weekly maintenance, providing leaner teams with quick compliance wins without needing deep allowlisting expertise.
| ThreatLocker | Airlock Digital | |
|---|---|---|
| 2-Factor Authentication | ||
| API | ||
| Access Management | ||
| Anti-Virus | ||
| Audit Management | ||
| Audit Trail | ||
| Batch Permissions & Access | ||
| Compliance Tracking | ||
| DDoS Protection | ||
| Dashboard | ||
| Data Export | ||
| Data Import | ||
| External Integrations | ||
| File Sharing | ||
| File Transfer | ||
| Firewall | ||
| Incident Management | ||
| Malware Protection | ||
| Multi-User | ||
| Notifications | ||
| Password & Access Management | ||
| Policy Management | ||
| Real-time Alerts | ||
| Report & Compliance | ||
| Risk Assessment | ||
| Security Migration | ||
| Threat Detection | ||
| Workflow Management |
ThreatLocker vs. Airlock Digital Integrations
| Tool | ThreatLocker | Airlock Digital |
| Microsoft Intune | ✅ | ✅ |
| Microsoft SCCM | ✅ | ✅ |
| Jamf | ✅ | ✅ |
| Azure Active Directory | ✅ | ✅ |
| Splunk | ✅ | ✅ |
| Elastic | ✅ | ✅ |
| ServiceNow | ✅ | ❌ |
| ConnectWise | ✅ | ❌ |
| Datto RMM | ✅ | ❌ |
| Autotask PSA | ✅ | ❌ |
| Syslog | ✅ | ✅ |
| Microsoft Sentinel | ✅ | ✅ |
| Active Directory | ✅ | ✅ |
| Okta | ✅ | ❌ |
| Crowdstrike | ✅ | ❌ |
Both platforms work directly with the endpoint tools you’re already using—SCCM, Jamf, and InTune—so rolling them out to your Windows, macOS, and Linux machines won’t give your IT team headaches. However, ThreatLocker offers integrations that MSPs will especially appreciate, such as ConnectWise, Datto, and Autotask for service management.
ThreatLocker vs. Airlock Digital Security, Compliance & Reliability
| Factor | ThreatLocker | Airlock Digital |
| Compliance Certifications | ThreatLocker is SOC 2 Type II; it aligns with NIST, CMMC, and CIS frameworks. | Airlock is ISO 27001:2022 certified and Essential Eight Level 3 compliant, as well as the only vendor that achieved E8MM Level 3. |
| Data Encryption | AES-256 encryption for data at rest; TLS 1.2+ for data in transit with cloud-hosted management console. | AES-256 encryption for agent-to-server communication; supports air-gapped deployments with on-premise hosting. |
| Access Control | Role-based access control with multi-tenant architecture; supports Azure AD and SSO integration. | Role-based access control with Active Directory integration; granular policy delegation for distributed security teams. |
| Audit Logging | Unified Audit logs all allow and deny events centrally; immutable logs are protected from tampering with SIEM forwarding. | Centralized execution logging with Trusted Execution Summary feature; logs protected from modification by design per E8MM requirements. |
| Support and Uptime | 24/7/365 Cyber Hero support team with guaranteed response SLAs; cloud infrastructure with multi-region redundancy | Business hours support with escalation paths; optional on-premise deployment for air-gapped environments requiring 99.9% agent uptime |
Security is a top priority for both platforms, with each offering strong encryption and audit trails that can’t be tampered with. They differ in compliance focus, though: ThreatLocker aligns with SOC 2 and CMMC standards, while Airlock Digital built its system to meet Australia’s Essential Eight Level 3 requirements. ThreatLocker runs in the cloud, offering 24/7 support backed by servers in multiple regions, whereas Airlock gives you an on-premise option—perfect for regulated industries that need physically isolated networks or strict control over where their data lives.
ThreatLocker vs. Airlock Digital Ease of Use
| Factor | ThreatLocker | Airlock Digital |
| User Interface | Intuitive dashboard with clear audit logs and granular policy controls; it has a clean design, but policy management has a steep learning curve. | Workflow-driven interface that simplifies allowlisting through a repeatable process; the learning mode builds policies automatically without extensive manual configuration. |
| Initial Setup and Deployment | Easy agent deployment via RMM tools with cloud-only architecture; full implementation typically takes 3-6 months, depending on environment complexity and policy tuning requirements. | Quick Start deployment engagement completes full enforcement in 3 months on average. |
| Onboarding and Training | Dedicated onboarding specialists guide customers through learning mode and policy creation using patient, clear explanations during the onboarding phase. | Tailored implementation advice from the support team with optional partner-delivered full implementation services; learning mode automated initial policy discovery to reduce manual effort. |
| Learning Curve | Steep learning curve for policy management that can introduce errors for non-technical users; mastering Ringfencing and multi-module configurations requires significant investment. | Lower operational learning curve due to workflow automation and repeatable policy templates; designed to make allowlisting practical for teams without deep security expertise. |
| Customer Support | 24/7/365 Cyber Hero support team with an average 60-second response time; highly responsive, knowledgeable staff are genuinely invested in customer success. | Business hours support with escalation paths and tailored advice; qualified partners available for extended implementation assistance, but no round-the-clock vendor support. |
While ThreatLocker’s interface is genuinely intuitive, policy management has a steep learning curve, and your team may rely heavily on their 24/7 support team during the first few months of deployment. Airlock Digital takes a different approach, focusing on operational simplicity with workflow automation that builds policies automatically in learning mode, meaning you’ll reach full enforcement faster and with less reliance on vendor support. You can deploy both platforms through your existing RMM tools without much hassle, but remember ThreatLocker’s cloud-only design won’t work in air-gapped environments, while Airlock offers on-premise options for those scenarios.
ThreatLocker vs Airlock Digital: Pros & Cons
ThreatLocker
- Delivers strong prevention against ransomware and zero-days.
- Granular control over applications, storage, and network access.
- Detailed logging supports compliance, audits, and forensic investigations.
- Steep initial learning curve and tuning period, requires upfront policy work to avoid blocking legitimate apps.
- Not a set-and-forget security solution for most environments.
- End-user friction arises from strict controls that block routine software installs.
Airlock Digital
- Deny by default model blocks unknown and unauthorized applications
- Lightweight agent has minimal impact on endpoint performance
- Centralized management supports Windows, macOS, and Linux environments
- Limited integrations compared to broader cybersecurity platforms
- Requires ongoing policy tuning for dynamic environments
- Pricing may be higher than basic endpoint protection tools
Best Use Cases for ThreatLocker and Airlock Digital
ThreatLocker
- MSPs Managing Multiple Clients Centralized cloud portal and RMM integrations let you deploy and tune policies across diverse environments without constant per-client tweaks.
- Healthcare Organizations Granular storage and elevation controls protect patient data on USBs, shares, and apps while meeting HIPAA compliance through audit trails.
- Educational Institutions Locks down student devices and servers against unauthorized software, reducing risks from unvetted apps in shared environments.
- Midmarket Enterprises Balances strong prevention with learning modes to build allowlists quickly, minimizing disruption during rollout.
- High-Compliance Industries Ringfencing and network controls limit lateral movement and data exfiltration, simplifying audits with detailed enforcement logs.
- Remote/Hybrid Workforces Dynamic network ACLs secure traveling endpoints by whitelisting specific IPs or keywords without VPN overhead.
Airlock Digital
- Government Agencies Meets strict compliance and audit requirements with granular application control.
- Financial Services Protects sensitive data and prevents unauthorized software in regulated environments.
- Healthcare Providers Supports HIPAA compliance and blocks unapproved medical software on endpoints.
- Manufacturing Firms Secures industrial control systems by restricting executable code on shop floor devices.
- IT Security Teams Gives security teams granular visibility and control over endpoint applications.
- Medium Enterprises Fits organizations needing centralized policy management across multiple locations.
Who Should Use ThreatLocker, and Who Should Use Airlock Digital
MSPs juggling multi-tenant environments and enterprises with dedicated security teams will get the most value from ThreatLocker. The platform’s native integrations cut billing and ticketing headaches across your client portfolio. When malware hijacks your trusted apps, Threatlocker’s ringfencing stops it from spreading—a must-have for healthcare, banking, and critical infrastructure clients. Their support team is invaluable for round-the-clock operations or teams still building allowlisting expertise.
Internal IT teams across Australia and New Zealand turn to Airlock Digital when they need to hit Essential Eight Level 3 compliance quickly. Their learning mode watches how your apps behave, then builds allowlisting policies for you—no manual rule-writing required. Airlock’s on-premise deployment offering is great for strict data sovereignty requirements and regulated environments where cloud solutions create compliance headaches.
Differences Between ThreatLocker and Airlock Digital
| ThreatLocker | Airlock Digital | |
|---|---|---|
| Application Containment Strategy | ThreatLocker’s Ringfencing technology goes beyond blocking unauthorized applications by controlling what approved applications can access, limiting file interactions, registry keys, network resources, and other applications to prevent lateral movement. | Airlock Digital focuses exclusively on deny-by-default allowlisting and blocklisting without application behavior containment, trusting that approved applications won’t be weaponized once they pass the allowlist. |
| Customer Support | ThreatLocker provides 24/7/365 Cyber Hero support with quick response times and hands-on policy assistance, functioning as an extension of your security team. | Airlock Digital offers business hours support with escalation paths and operational partner-delivered services, prioritizing self-sufficient operations. |
| Deployment Options | ThreatLocker operates exclusively as a cloud-hosted SaaS platform with no on-premise deployment option, requiring internet connectivity for management console access. | Airlock Digital offers on-premise deployment for air-gapped networks, federal clouds, and regulated environments requiring data sovereignty controls alongside their managed cloud service. |
| Multi-Tenant Management Capabilities | ThreatLocker’s multi-tenant architecture with organization hierarchies allows MSPs to manage hundreds of client environments separately within a single pane of glass, automatically syncing with RMM deployments. | Airlock Digital targets single-organization deployments without native multi-tenant management, making it better suited for internal IT teams managing their own endpoints rather than service providers. |
| Visit ThreatLockerOpens new window | Read Airlock Digital ReviewOpens new window |
Similarities Between ThreatLocker and Airlock Digital
| Auditability | Both platforms provide centralized, immutable audit logs of all execution events with native SIEM integrations for security operations and compliance reporting. |
|---|---|
| Automated Application Discovery | Both platforms include learning modes that automatically discover and catalog all running executables in your environment, building initial allowlist policies without requiring manual identification of every application. |
| Cross-Platform Endpoint Coverage | Both ThreatLocker and Airlock Digital support Windows, macOS, and Linux operating systems from a single management console, enabling unified policy enforcement across heterogeneous enterprise environments. |
| Integrations | Both solutions integrate natively with Microsoft SCCM, Jamf, and Microsoft Intune for straightforward agent deployment and policy distribution, fitting well into existing endpoint management workflows. |
| Zero Trust | Both platforms enforce Zero Trust endpoint protection by blocking all executables by default and only allowing explicitly approved applications to run, preventing ransomware and zero-day exploits from executing. |
| Visit ThreatLockerOpens new window Read Airlock Digital ReviewOpens new window | |