Airlock Digital Review: Pros, Cons, Features, and Pricing Explained
Airlock Digital is a cybersecurity software that uses application allowlisting to help you lock down endpoints and prevent unauthorized code execution. For IT specialists who need to reduce attack surfaces, enforce compliance, and gain granular control over what runs in their environment, Airlock Digital offers a focused alternative to traditional cybersecurity software.
In this review, I’ll break down Airlock Digital’s features, pricing, pros and cons, and where it fits best—so you can decide if it’s the right fit for your security strategy.
Airlock Digital Evaluation Summary
- Pricing upon request
- Free demo available
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Airlock Digital Overview
If you’re judging cybersecurity software by control and precision, Airlock Digital is a top contender. Its allowlisting model gives you more authority over application execution than most alternatives, though it can mean more of an in-depth setup and ongoing management. I think its interface is straightforward, support is responsive, and onboarding is clear for teams familiar with endpoint security. Pricing is competitive for the level of control you get, but integrations are more limited than some broader platforms. I’d suggest Airlock Digital for organizations with strict compliance needs or those prioritizing zero-trust environments.
pros
-
Deny by default model blocks unknown and unauthorized applications
-
Lightweight agent has minimal impact on endpoint performance
-
Centralized management supports Windows, macOS, and Linux environments
cons
-
Limited integrations compared to broader cybersecurity platforms
-
Requires ongoing policy tuning for dynamic environments
-
Pricing may be higher than basic endpoint protection tools
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Our Review Methodology
How We Test & Score Tools
We’ve spent years building, refining, and improving our software testing and scoring system. The rubric is designed to capture the nuances of software selection and what makes a tool effective, focusing on critical aspects of the decision-making process.
Below, you can see exactly how our testing and scoring works across seven criteria. It allows us to provide an unbiased evaluation of the software based on core functionality, standout features, ease of use, onboarding, customer support, integrations, customer reviews, and value for money.
Core Functionality (25% of final scoring)
The starting point of our evaluation is always the core functionality of the tool. Does it have the basic features and functions that a user would expect to see? Are any of those core features locked to higher-tiered pricing plans? At its core, we expect a tool to stand up against the baseline capabilities of its competitors.
Standout Features (25% of final scoring)
Next, we evaluate uncommon standout features that go above and beyond the core functionality typically found in tools of its kind. A high score reflects specialized or unique features that make the product faster, more efficient, or offer additional value to the user.
We also evaluate how easy it is to integrate with other tools typically found in the tech stack to expand the functionality and utility of the software. Tools offering plentiful native integrations, 3rd party connections, and API access to build custom integrations score best.
Ease of Use (10% of final scoring)
We consider how quick and easy it is to execute the tasks defined in the core functionality using the tool. High scoring software is well designed, intuitive to use, offers mobile apps, provides templates, and makes relatively complex tasks seem simple.
Onboarding (10% of final scoring)
We know how important rapid team adoption is for a new platform, so we evaluate how easy it is to learn and use a tool with minimal training. We evaluate how quickly a team member can get set up and start using the tool with no experience. High scoring solutions indicate little or no support is required.
Customer Support (10% of final scoring)
We review how quick and easy it is to get unstuck and find help by phone, live chat, or knowledge base. Tools and companies that provide real-time support score best, while chatbots score worst.
Customer Reviews (10% of final scoring)
Beyond our own testing and evaluation, we consider the net promoter score from current and past customers. We review their likelihood, given the option, to choose the tool again for the core functionality. A high scoring software reflects a high net promoter score from current or past customers.
Value for Money (10% of final scoring)
Lastly, in consideration of all the other criteria, we review the average price of entry level plans against the core features and consider the value of the other evaluation criteria. Software that delivers more, for less, will score higher.
Core Features
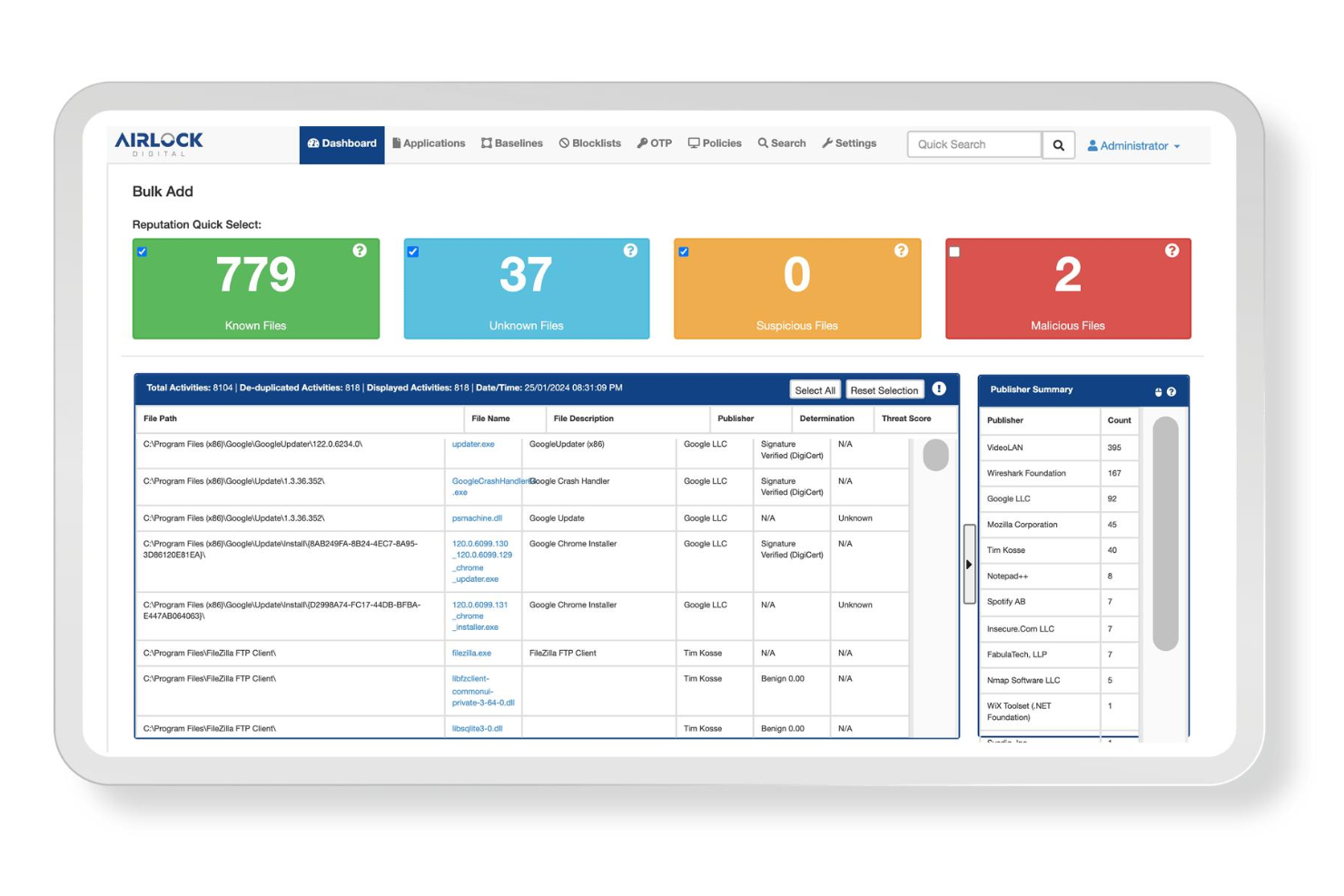
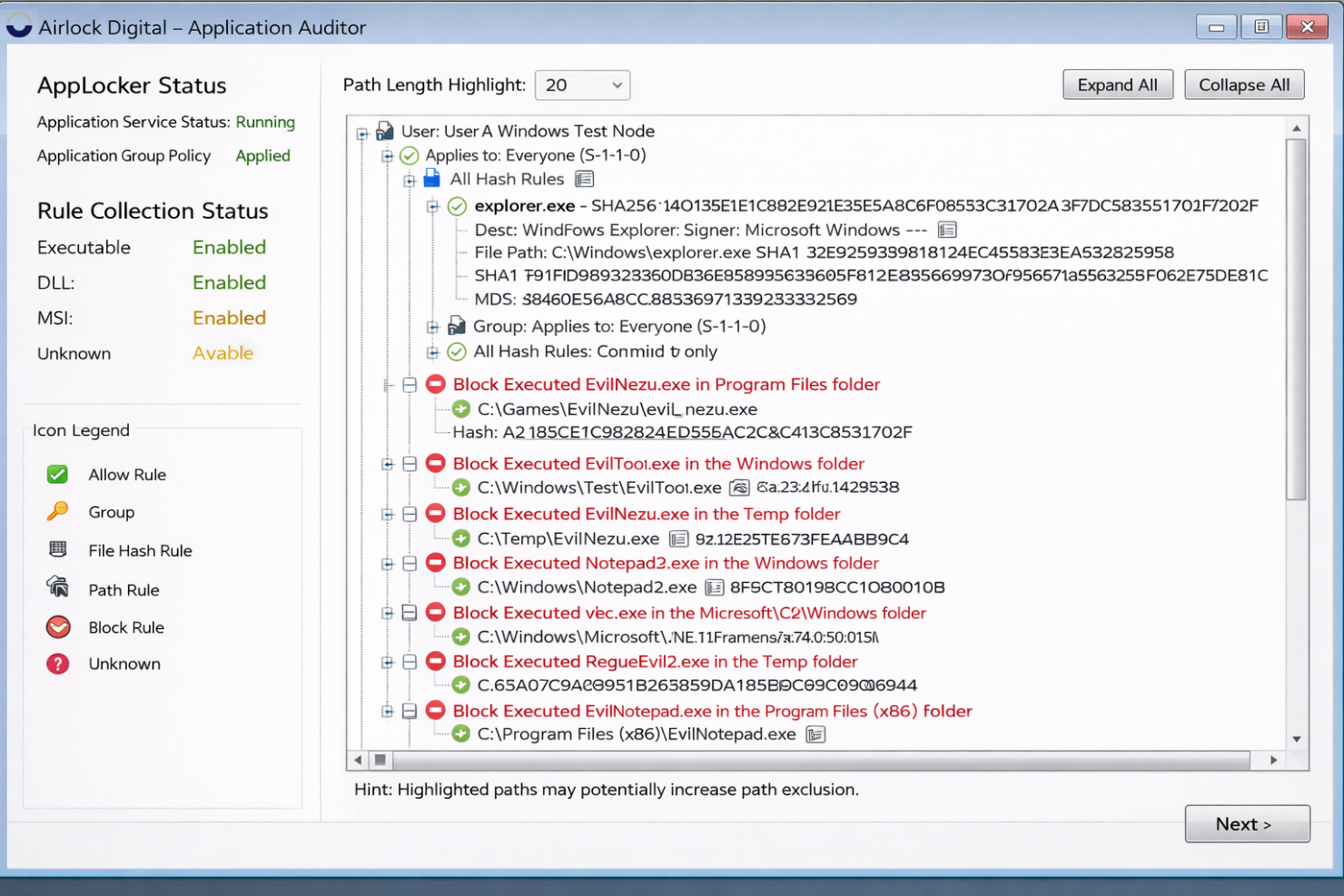
Deny by Default Application Control
Blocks all untrusted and unknown applications from running on endpoints. This approach prevents malware, ransomware, and unauthorized scripts before they can execute.
Centralized Policy Management
Lets you manage application control policies for Windows, macOS, and Linux from a single console. You can quickly update, enforce, and audit policies across your entire environment.
Workflow-Driven Allowlisting
Guides you through discovering, vetting, and approving executable code with repeatable workflows. This makes allowlisting practical and scalable for large organizations.
Blocklisting Capabilities
Allows you to explicitly block known malicious or unwanted files in addition to allowlisting. This dual approach gives you more flexibility in controlling your environment.
File Metadata Repository
Maintains a searchable database of all file metadata across your endpoints. You gain visibility into what’s running and can investigate suspicious files easily.
Legacy System Support
Supports application control on older versions of Windows, macOS, and Linux. This is valuable for organizations with legacy infrastructure that still needs protection.
Ease of Use
Airlock Digital is straightforward for IT teams familiar with application control, offering a clean interface and guided workflows that simplify policy creation and management. Users often mention that onboarding is clear, with helpful documentation and responsive support. However, ongoing policy tuning can be time-consuming in dynamic environments, and less technical users may find the allowlisting process demanding. Overall, it’s user-friendly for security professionals but may require more hands-on management than broader endpoint security tools.
Integrations
Airlock Digital integrates with Jamf, Splunk, Sumo Logic, Crowdstrike, and Microsoft SCCM, among others.
Airlock Digital also offers a rest API for custom integrations and automation.
Airlock Digital Specs
- 2-Factor Authentication
- Access Management
- Anti-Virus
- API
- Audit Management
- Audit Trail
- Batch Permissions & Access
- Compliance Tracking
- Dashboard
- Data Export
- Data Import
- DDoS Protection
- External Integrations
- File Sharing
- File Transfer
- Firewall
- Incident Management
- Malware Protection
- Multi-User
- Notifications
- Password & Access Management
- Policy Management
- Real-time Alerts
- Report & Compliance
- Risk Assessment
- Security Migration
- Threat Detection
- Workflow Management









