10 Meilleurs services de détection et de réponse gérés – Sélection
Dans le domaine de la cybersécurité, j’ai constaté que si les antivirus et les fournisseurs de services de sécurité managés (MSSP) constituent une base essentielle, ils atteignent parfois leurs limites. Les services de détection et de réponse gérés (MDR) comblent ce manque. Ces outils surveillent et contrent les menaces de manière proactive et en temps réel, faisant évoluer votre sécurité d’une simple prévention vers une défense active.
Ils détectent et neutralisent les menaces avant qu’elles ne s’aggravent, évitant la course contre la montre après une brèche. Si vous trouvez la protection continue difficile à gérer, considérez ces services comme un véritable soulagement. Explorons les options pour renforcer votre sécurité.
Qu’est-ce qu’un service de détection et de réponse géré ?
Un service de détection et de réponse géré est une prestation spécialisée en cybersécurité que les entreprises utilisent pour identifier et traiter les menaces de manière proactive. Au lieu de seulement fournir des outils à utiliser en interne, ce service associe technologies de pointe et expertise humaine pour surveiller, détecter et répondre en temps réel aux menaces potentielles.
Les organisations, des petites entreprises aux grands groupes, s’appuient sur ces services afin de renforcer leur posture de sécurité et de réagir avec efficacité face aux menaces avant qu’elles ne dégénèrent. Avec l’évolution constante des menaces numériques, disposer d’un service MDR est aujourd’hui crucial pour protéger ses actifs numériques et préserver l’intégrité de ses opérations.
Résumé des meilleurs services de détection et de réponse gérés
| Service | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Idéal pour la détection d'anomalies comportementales | Essai gratuit + démo gratuite disponible | Tarification sur demande | Website | |
| 2 | Idéal pour une gestion holistique de la sécurité | Not available | Tarification sur demande | Website | |
| 3 | Idéal pour les méthodes de détection basées sur l'IA | Démo gratuite disponible | Tarification sur demande | Website | |
| 4 | Idéal pour les architectures de sécurité intégrées | Not available | Tarification sur demande | Website | |
| 5 | Idéal pour des défenses cloud-natives | Not available | Tarification sur demande | Website | |
| 6 | Idéal pour l’analyse du comportement des utilisateurs | Not available | Tarification sur demande | Website | |
| 7 | Idéal pour l’intelligence avancée sur les menaces | Not available | Tarification sur demande | Website | |
| 8 | Idéal pour les environnements IT hybrides | Not available | Tarification sur demande | Website | |
| 9 | Am besten geeignet zur Zuordnung von App-Installationen auf Marketingkampagnen | 30 Tage kostenlos testen | Preise auf Anfrage | Website | |
| 10 | Idéal pour la persistance dans l’atténuation des menaces | Essai gratuit disponible | Tarification sur demande | Website |
Avis sur les meilleurs services de détection et de réponse gérés
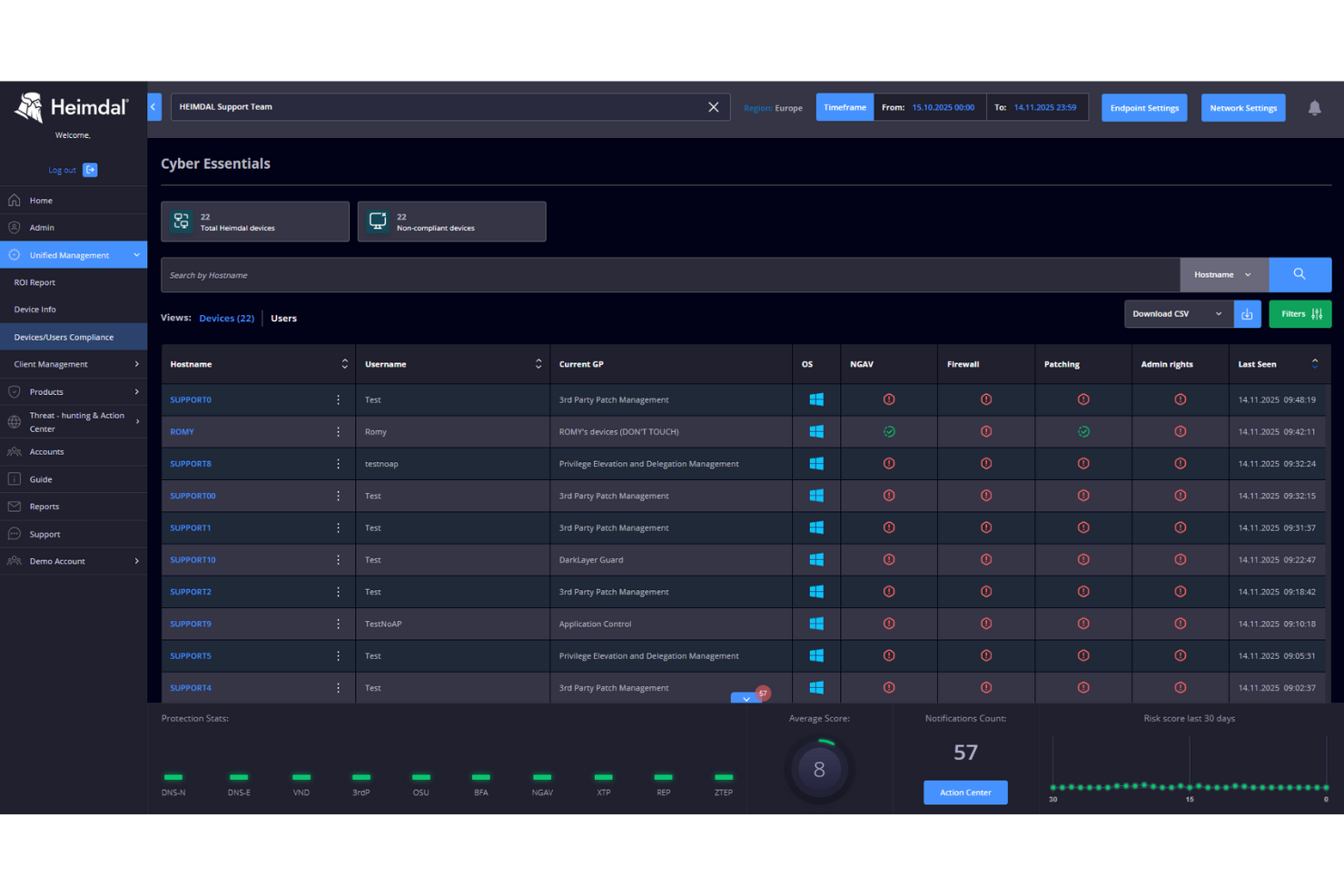
Dans le paysage en constante évolution de la cybersécurité, Heimdal se distingue comme un allié essentiel pour les entreprises à la recherche de services de détection et de réponse gérés. Conçues pour des secteurs tels que la santé, le gouvernement et les infrastructures critiques, les solutions de Heimdal répondent de manière proactive aux défis de la conformité et de la gestion des risques. En tirant parti de leur expertise, vous pouvez renforcer votre posture de sécurité en veillant à ce que les menaces soient détectées et atténuées avant d'avoir un impact sur vos opérations.
Pourquoi j'ai choisi Heimdal
J'ai choisi Heimdal pour sa combinaison unique de technologies avancées et d'analyse humaine experte dans les services de détection et de réponse gérés. Leur surveillance 24h/24 et 7j/7 garantit que votre réseau est constamment sous contrôle, permettant une détection et une réponse immédiates aux menaces. J'apprécie l'intégration par Heimdal de renseignements sur les menaces, qui offrent des informations exploitables pour protéger votre organisation contre les dangers potentiels. Leur accent mis sur une gestion rapide des incidents signifie que votre équipe peut rapidement traiter et atténuer les vulnérabilités, protégeant ainsi votre entreprise contre les cybermenaces.
Fonctionnalités clés de Heimdal
Au-delà de la surveillance poussée et de l'intelligence des menaces, j'ai également identifié d'autres fonctionnalités précieuses qui renforcent vos mesures de cybersécurité :
- Chasse aux menaces : Recherche proactive des menaces potentielles qui peuvent ne pas être immédiatement visibles par les outils automatisés.
- Rapports détaillés : Fournit une vue complète de votre environnement de sécurité, vous aidant à prendre des décisions éclairées.
- Analyse comportementale : Supervise les comportements des utilisateurs et des entités afin de détecter les anomalies pouvant indiquer des violations de sécurité.
- Support SOC 24h/24 et 7j/7 : Offre un accompagnement continu et une expertise pour gérer et répondre efficacement aux incidents de sécurité.
Intégrations Heimdal
Heimdal n'indique pas actuellement d'intégrations natives ; cependant, la plateforme prend en charge des intégrations personnalisées basées sur API.
Pros and Cons
Pros:
- Automatise l’application des correctifs sur tous les endpoints
- Détection efficace des vulnérabilités et menaces
- Visibilité détaillée des actifs et des licences
Cons:
- Aucune intégration native disponible
- Interface nécessitant un temps d'adaptation pour l'onboarding
ConnectWise MDR offre aux entreprises des services de sécurité complets, garantissant que leurs données et systèmes restent protégés contre les cyberattaques. Son approche holistique de la gestion de la sécurité intègre divers outils et stratégies, en faisant une solution tout-en-un pour de nombreuses organisations.
Pourquoi j'ai choisi ConnectWise MDR :
Dans ma recherche des meilleures solutions MDR, j'ai évalué de nombreux fournisseurs de services. ConnectWise MDR a retenu mon attention grâce à son approche globale, mettant l'accent sur une gestion holistique de la sécurité. Sa méthodologie intégrée, couvrant plusieurs aspects de la sécurité sous un même toit, a consolidé sa place dans ma sélection et renforcé sa réputation en tant que référence pour la gestion holistique de la sécurité.
Fonctionnalités remarquables et intégrations :
L'une des fonctionnalités les plus convaincantes de ConnectWise MDR est ses solides capacités EDR, qui améliorent la sécurité des terminaux et réduisent le risque d'attaques par logiciels malveillants. De plus, ses outils d'automatisation de la remédiation contribuent à rationaliser le processus de réponse aux incidents. La plateforme dispose également d'intégrations étendues, notamment avec les principales technologies SIEM et Microsoft, permettant une circulation des données et de la télémétrie de sécurité.
Pros and Cons
Pros:
- Solution MDR complète couvrant un large éventail de besoins en sécurité
- Des capacités EDR robustes renforcent la protection des terminaux
- Capacités d'intégration étendues, y compris avec les principales technologies SIEM
Cons:
- L'approche holistique peut être déstabilisante pour les petites entreprises dépourvues d'une équipe de sécurité dédiée
- La structure tarifaire peut ne pas être transparente ou claire pour tous les clients potentiels
- Nécessite un certain niveau d'expertise interne pour une utilisation optimale.
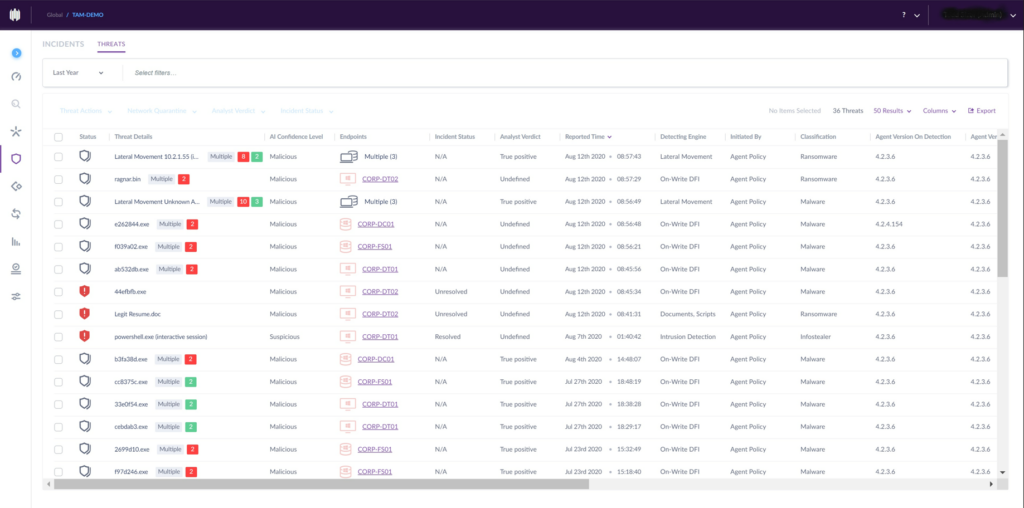
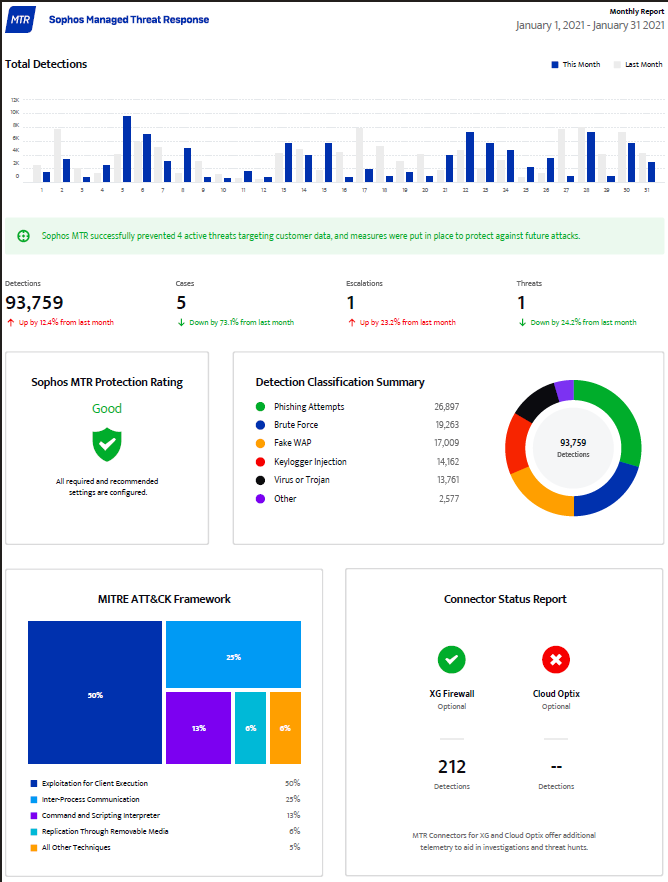
Sophos est un acteur majeur dans le domaine de la cybersécurité, réputé pour l'utilisation de mécanismes d'IA de pointe afin de détecter les menaces potentielles. Il se distingue par sa capacité à exploiter l'apprentissage automatique pour débusquer des cyberattaques sophistiquées, en accord avec sa réputation d'être le meilleur pour les méthodes de détection basées sur l'IA.
Pourquoi j'ai choisi Sophos :
Après avoir comparé de près plusieurs solutions de sécurité, Sophos a retenu mon attention grâce à son approche innovante. Je l'ai choisi principalement pour son accent particulier mis sur l'utilisation de l'IA dans la détection des menaces, une méthode qui offre une précision et une rapidité inégalées. Avec l'émergence quotidienne de menaces toujours plus sophistiquées, le recours à l'IA pour la détection est devenu essentiel, ce qui fait de Sophos le meilleur choix pour les méthodes axées sur l'IA.
Fonctionnalités remarquables et intégrations :
Sophos se distingue par ses solides capacités EDR, offrant une réponse aux incidents en temps réel et limitant l'impact des logiciels malveillants. Les fonctionnalités d'automatisation de la remédiation sont particulièrement remarquables, permettant aux équipes de sécurité de répondre rapidement aux menaces sans intervention manuelle.
En ce qui concerne les intégrations, Sophos s'interface avec les principales plateformes comme Microsoft et divers systèmes SIEM, garantissant ainsi la compatibilité et un meilleur suivi de la sécurité.
Pros and Cons
Pros:
- Des mécanismes avancés d'IA et de machine learning améliorent la précision de détection
- Système EDR puissant pour une sécurité complète des endpoints
- S'intègre efficacement avec les principales plateformes et systèmes SIEM
Cons:
- Peut présenter une courbe d'apprentissage pour ceux non familiers avec l'IA
- Peut être perçu comme complexe par les petites entreprises ayant des besoins de sécurité limités
- Occasionnellement des faux positifs dus à la sensibilité des méthodes de détection par IA.
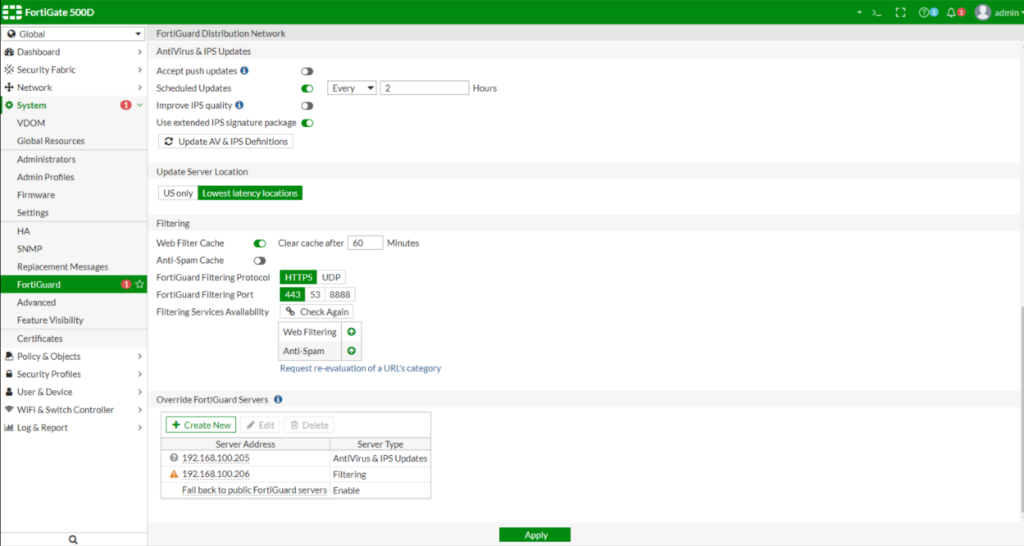
FortiGuard excelle dans la fourniture de services de sécurité robustes, s'intègre aux architectures informatiques complexes. Son accent mis sur une infrastructure de sécurité intégrée est la clé de son succès, garantissant une protection holistique sur l'ensemble des frontières numériques.
Pourquoi j'ai choisi FortiGuard :
Au cours de mon analyse comparant divers outils de sécurité, FortiGuard s'est immédiatement démarqué. Alors que de nombreux outils affichent une multitude de fonctionnalités, la priorité donnée par FortiGuard à une architecture de sécurité totalement intégrée en a fait un choix remarquable. Je l'ai choisi pour cette liste car les entreprises recherchant une approche globale de leur posture de sécurité tireraient un immense bénéfice de sa stratégie intégrée.
Fonctionnalités et intégrations clés :
FortiGuard est reconnu pour ses capacités EDR de pointe, qui renforcent la détection sur les terminaux et réduisent les risques liés aux logiciels malveillants. Ses données de télémétrie avancées procurent aux équipes de sécurité un avantage décisif face aux menaces émergentes.
En matière d'intégration, FortiGuard s'ajuste aisément à la majorité des outils SIEM, aux principales plateformes SaaS ainsi qu'aux technologies Microsoft, renforçant la performance d'un centre d'opérations de sécurité existant.
Pros and Cons
Pros:
- Fonctionnalités EDR complètes assurant une sécurité robuste des terminaux
- Les rapports de télémétrie facilitent la réponse rapide aux incidents et l'identification des menaces émergentes
- Intégration facile avec les principaux outils SIEM et l'écosystème Microsoft
Cons:
- Le manque de transparence sur les prix peut décourager certains utilisateurs
- L'accent fort mis sur l'intégration peut être déroutant pour les petites équipes
- Nécessite un apprentissage approfondi pour ceux qui ne connaissent pas les architectures de sécurité intégrées.
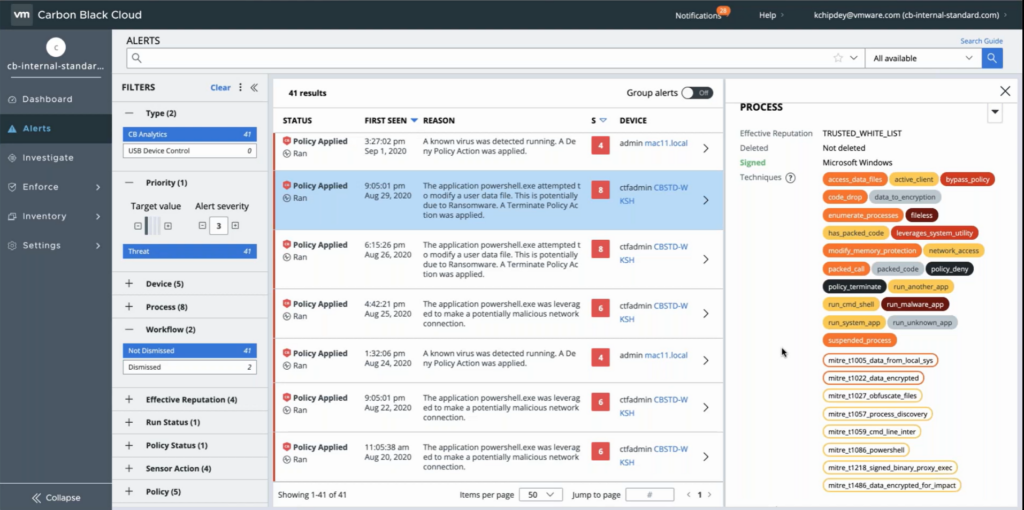
Carbon Black Cloud Managed Detection est un outil de premier plan offrant des mécanismes de défense robustes et natifs du cloud contre les menaces cybernétiques. Essentiel pour les entreprises qui migrent vers le cloud, cet outil se distingue par ses capacités à prévenir, détecter et répondre aux incidents de sécurité dans des environnements cloud.
Pourquoi j'ai choisi Carbon Black Cloud Managed Detection :
Parmi la multitude de solutions de sécurité que j'ai examinées, Carbon Black s'est démarquée grâce à sa forte orientation vers les défenses cloud-natives. À une époque où de plus en plus d'entreprises migrent vers le cloud, le besoin de mécanismes de défense spécialisés dans ces environnements est devenu évident. J'ai estimé que cet outil, grâce à son positionnement unique et son approche axée sur le cloud, était optimal pour les organisations recherchant une protection spécialisée dans le cloud.
Fonctionnalités et intégrations remarquables :
Carbon Black est réputé pour ses capacités EDR, garantissant une détection des postes de travail et une réponse aux incidents de haut niveau, particulièrement dans les environnements cloud. L'outil s'intègre également avec diverses technologies de centres des opérations de sécurité et des outils SIEM, facilitant ainsi la surveillance, l'analyse et la gestion des incidents de sécurité par les équipes de sécurité. En outre, sa solide intégration avec des plateformes comme Microsoft renforce sa proposition de valeur pour les entreprises.
Pros and Cons
Pros:
- Approche cloud-first assurant des défenses spécialisées pour les environnements cloud
- Des capacités EDR solides offrent une sécurité avancée des postes de travail
- Intégrations avec des plateformes majeures telles que Microsoft et les principaux outils SIEM
Cons:
- L'accent mis sur les défenses cloud-natives peut ne pas convenir aux entreprises encore fortement axées sur le local
- Peut s'avérer complexe pour les organisations ne disposant pas d'équipe ou d'expertise en sécurité dédiée
- Le manque de transparence sur la tarification peut compliquer la planification budgétaire.
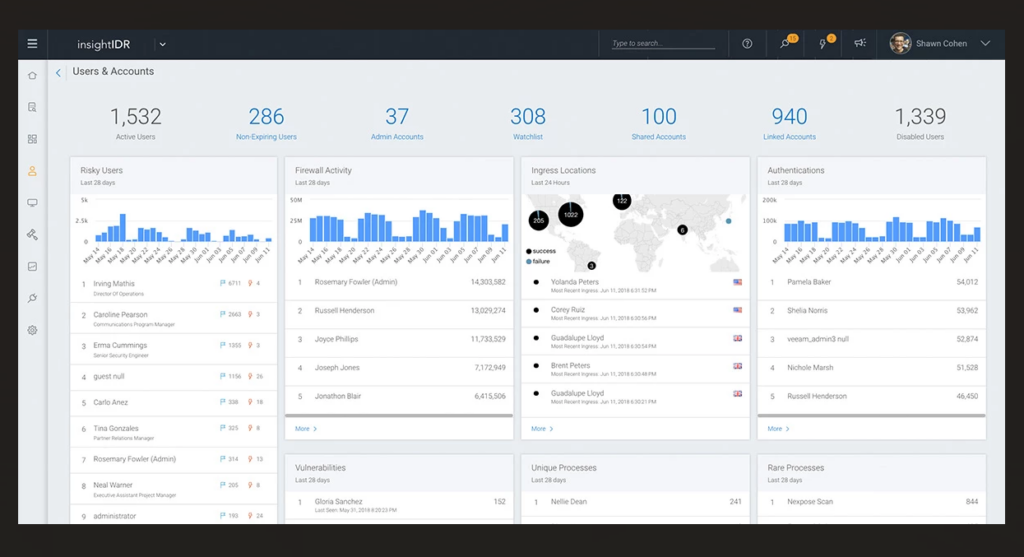
Idéal pour l’analyse du comportement des utilisateurs
Les services Rapid7 de détection et de réponse gérées constituent une solution complète, spécialisée dans l’exploitation de l’analyse du comportement des utilisateurs pour détecter et traiter les violations de sécurité. Son objectif principal est de comprendre les activités des utilisateurs et d’identifier les anomalies susceptibles de signaler des menaces informatiques potentielles.
Pourquoi j’ai choisi les services Rapid7 de Détection et Réponse Gérées :
Pendant mon processus de sélection de services de sécurité, Rapid7 s’est nettement démarqué en raison de sa maîtrise de l’analyse du comportement des utilisateurs. Je l’ai évalué selon divers critères, et sa capacité unique à disséquer les activités des utilisateurs et à discerner les schémas inhabituels en fait une solution incontournable.
La profondeur analytique qu’il offre sur le comportement des utilisateurs, qui le distingue des autres outils, m’a convaincu qu’il est idéal pour les entreprises désireuses de se protéger spécifiquement contre ce type de menaces informatiques.
Caractéristiques et intégrations remarquables :
Rapid7 est reconnu pour ses solides capacités EDR et de réponse aux incidents, garantissant une détection et une gestion rapides des incidents de sécurité. L’intégration de l’outil avec les systèmes de centre des opérations de sécurité et les technologies SIEM assure un contrôle efficace de la sécurité. De plus, ses connexions avec des plateformes telles que Microsoft et les fournisseurs managedXDR renforcent sa portée et son efficacité.
Pros and Cons
Pros:
- Une analyse exceptionnelle du comportement des utilisateurs permet de détecter précocement les activités inhabituelles
- S’intègre efficacement avec des plateformes populaires telles que Microsoft et les outils SIEM
- Les solides capacités EDR et de réponse aux incidents renforcent ses mécanismes de défense
Cons:
- Les entreprises recherchant une solution de sécurité plus généraliste pourraient trouver sa spécialisation trop pointue
- Nécessite une compréhension de base de l’analyse du comportement des utilisateurs pour exploiter tout son potentiel
- L’absence de tarification transparente peut compliquer la planification budgétaire de certaines organisations.
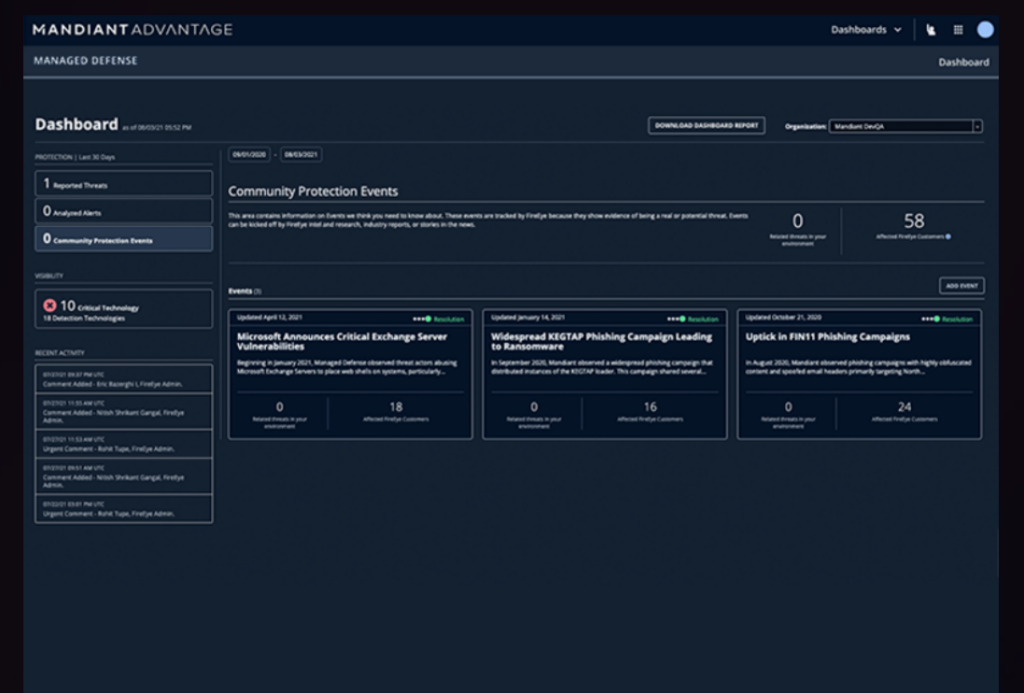
Mandiant propose des solutions de sécurité de pointe, plaçant les entreprises à l'avant-garde de la défense contre les cybermenaces. Sa maîtrise de l’intelligence avancée sur les menaces la distingue, offrant un avantage certain dans le paysage cybernétique complexe d’aujourd’hui.
Pourquoi j'ai choisi Mandiant :
Dans ma recherche pour présélectionner des fournisseurs de MDR, le choix de Mandiant a été une décision réfléchie, influencée par son approche singulière. Mandiant se démarque constamment grâce à son intelligence sur les menaces inégalée, mettant en lumière des menaces émergentes que la plupart des services pourraient négliger.
C'est cet engagement envers une intelligence avancée qui m'a amené à conclure que Mandiant est le choix incontournable pour ceux qui recherchent une compréhension approfondie des potentielles cybermenaces.
Fonctionnalités remarquables et intégrations :
Mandiant est reconnu pour ses capacités d'apprentissage automatique, facilitant une réponse rapide aux incidents et réduisant les faux positifs. Sa fonctionnalité EDR garantit une sécurité complète des endpoints, renforçant les défenses contre les logiciels malveillants. En ce qui concerne les intégrations, Mandiant s’associe sans effort aux principaux outils SIEM, à l’écosystème Microsoft et à diverses applications SaaS, assurant un environnement SOC (centre des opérations de sécurité) cohérent.
Pros and Cons
Pros:
- Intelligence avancée et approfondie sur les menaces pour une meilleure vigilance
- Solides composants d'apprentissage automatique pour une réponse rapide aux incidents
- Intégration avec les principaux outils SIEM et les produits Microsoft
Cons:
- Aucune structure tarifaire claire disponible publiquement
- Peut être complexe à déployer pour les petites équipes de sécurité internes
- L’accent mis sur les fonctionnalités avancées peut faire passer les besoins de base en sécurité au second plan pour certaines entreprises.
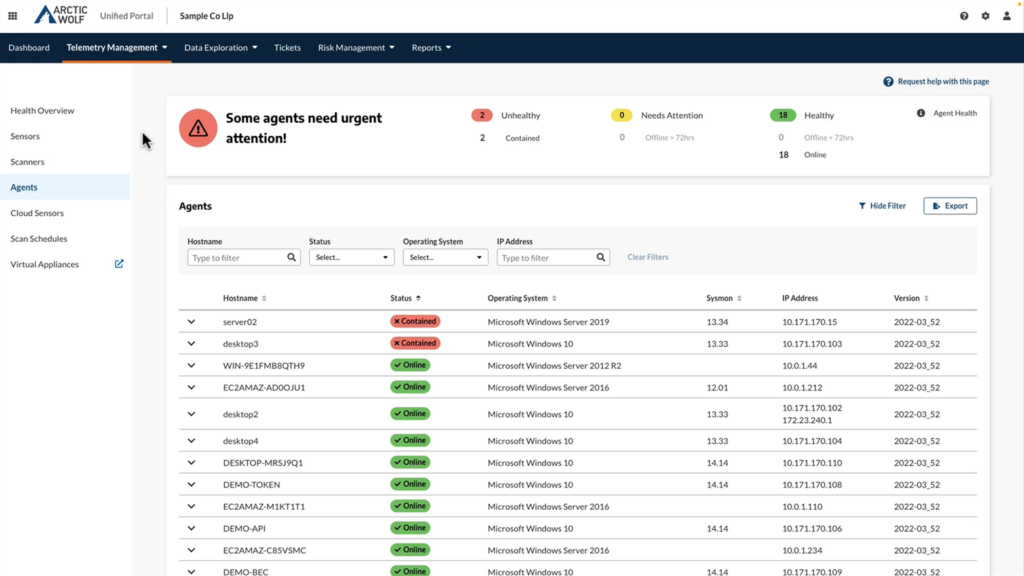
Idéal pour les environnements IT hybrides
Arctic Wolf propose une solution MDR complète conçue pour surveiller efficacement les environnements sur site et cloud. Face à la complexité croissante des configurations informatiques, cet outil est particulièrement adapté aux infrastructures hybrides, ce qui en fait le choix idéal pour les organisations utilisant à la fois des actifs IT traditionnels et modernes.
Pourquoi j'ai choisi Arctic Wolf Managed Detection and Response :
Au cours de mon analyse des solutions MDR, Arctic Wolf s'est imposé comme un choix évident grâce à son expertise dans la gestion des environnements informatiques hybrides. Cette conclusion s'est confirmée après avoir comparé les capacités de différents outils et évalué leur efficacité sur de multiples plateformes.
Pour les organisations qui font le pont entre infrastructures sur site et cloud, disposer d'un outil comme Arctic Wolf garantit une surveillance de sécurité homogène et approfondie.
Caractéristiques remarquables et intégrations :
Arctic Wolf se distingue par ses capacités de détection sur les postes de travail et de réponse aux incidents, garantissant que les menaces sont rapidement identifiées et traitées. Grâce à son SOC performant, l'outil offre une vue d'ensemble complète de la surface d'attaque d'une organisation, permettant aux équipes de sécurité de prioriser les menaces potentielles.
De plus, la plateforme s'intègre facilement avec des logiciels largement utilisés comme Microsoft, offrant des synergies dans les opérations de sécurité et permettant la télémétrie de données.
Pros and Cons
Pros:
- Spécifiquement adapté aux environnements IT hybrides, couvrant à la fois les systèmes sur site et cloud
- Des fonctionnalités EDR et SOC solides assurent la détection et la réponse aux menaces en temps réel
- Intégrations efficaces avec des plateformes logicielles populaires, améliorant la pile technologique
Cons:
- Peut ne pas convenir aux configurations purement cloud ou purement sur site
- Certains utilisateurs pourraient trouver l'interface exigeante, surtout sans expérience préalable avec les environnements hybrides
- Compte tenu de son ensemble de fonctionnalités complètes, il peut être surdimensionné pour les petites entreprises aux infrastructures informatiques limitées.
Am besten geeignet zur Zuordnung von App-Installationen auf Marketingkampagnen
AppsFlyer ist eine erstklassige Plattform für Mobile Attribution und Marketing-Analytics. Sie unterstützt Unternehmen dabei, ihre App-Installationen zu verfolgen und zu analysieren, mit besonderem Schwerpunkt auf der Zuordnung zu bestimmten Marketingkampagnen.
Warum ich AppsFlyer gewählt habe: Ich habe AppsFlyer aufgrund seines außergewöhnlichen Fokus auf die Zuordnung von App-Installationen zu Marketinginitiativen ausgewählt. Im Vergleich zu vielen anderen nimmt AppsFlyer einen einzigartigen, detailorientierten Ansatz ein. Deshalb ist es für mich die beste Wahl, wenn es um die Attribution von App-Installationen auf Marketingkampagnen geht. Es verfolgt nicht nur App-Installationen, sondern zeigt auch genau auf, wie Nutzer die App gefunden und installiert haben.
Herausragende Funktionen & Integrationen:
Die Echtzeit-Berichte von AppsFlyer liefern sofortige Einblicke in die Kampagnenperformance. Die OneLink-Funktion ermöglicht Deep Linking über alle Plattformen und Marketingkanäle hinweg.
Wichtige Integrationen sind unter anderem Facebook, Twitter, Google Ads und mehr als 2.000 weitere Netzwerke, sodass Unternehmen ihre Marketingaktivitäten kanalübergreifend steuern und optimieren können.
Pros and Cons
Pros:
- Detaillierte Attribution von App-Installationen
- Umfassende Integrationen mit führenden Netzwerken
- Echtzeit-Berichte für sofortige Einblicke
Cons:
- Preisdaten sind nicht direkt verfügbar
- Kann aufgrund der Vielzahl an Funktionen für Einsteiger überwältigend sein
- Individuelle Preisgestaltung ist für kleine Unternehmen möglicherweise nicht günstig
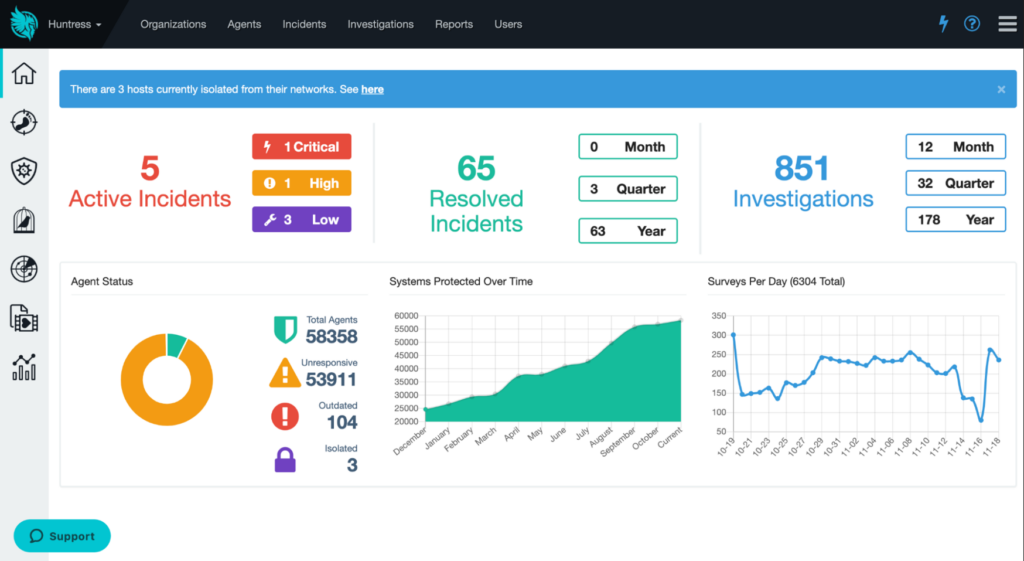
Huntress propose une détection approfondie des menaces et une atténuation persistante pour les entreprises. Son accent mis sur l’éradication à long terme des menaces en fait un outil précieux pour les organisations engagées dans une hygiène cybernétique rigoureuse, notamment lorsqu'elles privilégient la persistance dans l’atténuation des menaces.
Pourquoi j’ai choisi Huntress :
Pour déterminer quel outil inclure, j'ai soigneusement analysé et comparé une multitude de solutions de sécurité. J’ai choisi Huntress principalement pour son insistance inlassable sur l’atténuation persistante des menaces. Cet engagement continu le distingue des autres et renforce ma conviction qu’il est le mieux adapté pour garantir que les menaces ne soient pas seulement détectées mais aussi continuellement atténuées.
Caractéristiques et intégrations remarquables :
Huntress se distingue par ses capacités EDR avancées, permettant aux équipes de sécurité de détecter et neutraliser les menaces avec précision. Les fonctionnalités d’automatisation de la remédiation de la plateforme optimisent davantage les processus de réponse aux incidents. De plus, ses capacités d’intégration avec les SIEM populaires et d’autres outils de sécurité comme Microsoft améliorent son efficacité.
Pros and Cons
Pros:
- Un accent persistant sur l’atténuation à long terme des menaces garantit la sécurité
- Capacités EDR avancées pour une détection et une action précises contre les menaces
- Large éventail d’intégrations, notamment avec les principales technologies SIEM
Cons:
- Peut être complexe pour les petites organisations dépourvues d’analystes de sécurité dédiés
- L’atténuation continue peut nécessiter des ressources supplémentaires pour l’optimisation
- Le manque de transparence sur la tarification peut représenter un obstacle pour certaines entreprises.
Autres services de détection et de réponse gérés
Voici une liste supplémentaire de services MDR que j’ai présélectionnés mais qui n’ont pas atteint le top 10. Ils valent tout de même le détour.
- Expel
Idéal pour des informations opérationnelles 24h/24 et 7j/7
- Binary Defense
Idéal pour des stratégies de sécurité sur mesure
- Netsurion Managed Threat Protection
Idéal pour une protection diversifiée des terminaux
Critères de sélection pour les services de détection et de réponse gérés
Dans l’univers vaste des services de détection et de réponse gérés (MDR), trouver l’outil le plus adapté à votre organisation n’est pas une mince affaire. Sur la base de recherches approfondies et d’expériences concrètes, j’ai personnellement testé et analysé une multitude de ces outils. Parmi la dizaine évaluée, j’ai toujours recherché des fonctionnalités et critères spécifiques afin de garantir non seulement une sécurité robuste mais également une expérience utilisateur optimisée.
Voici les critères essentiels qui ont guidé mes choix :
Fonctionnalité principale
- Détection et réponse sur les endpoints (EDR) : Permet une surveillance et une réaction en temps réel face aux menaces potentielles.
- Centre des opérations de sécurité (SOC) : Offre une veille et une supervision permanente (24/7) des opérations de sécurité.
- Réponse aux incidents : Apporte une capacité de réaction rapide lors de la détection d’incidents de sécurité.
- Renseignement sur les menaces : Fournit des informations actualisées sur les cybermenaces émergentes et les risques en ligne.
- Remédiation automatisée : Permet d’automatiser certaines actions correctives et d’optimiser les délais de réaction.
Fonctionnalités clés
- Protection contre les ransomwares : Protège contre l'un des types de logiciels malveillants les plus courants et destructeurs.
- Orchestration et plans d'action : Rationalise les stratégies de réponse, garantissant des réactions rapides et coordonnées face aux menaces.
- Notifications et alertes : Informe instantanément les équipes de sécurité en cas de menace ou de violation potentielle.
- Conformité aux normes : Respecte des normes reconnues telles que Gartner et ISO, assurant fiabilité et confiance.
- Analyse des causes profondes : Identifie et examine la source principale d'une faille ou d'une vulnérabilité de sécurité.
Facilité d'utilisation
- Interface intuitive : Compte tenu de la complexité des solutions MDR, un tableau de bord facile à utiliser est essentiel. Cette interface doit offrir une vue consolidée des menaces, des charges de travail et des flux de travail.
- Gestion des accès basée sur les rôles : Particulièrement important pour les MDR, car différents membres de l'équipe ont des responsabilités variées. Une fonctionnalité de gestion des employés doit permettre de configurer facilement les accès selon les rôles.
- Bibliothèque d'apprentissage ou programme de formation : Étant donné la complexité inhérente de nombreux outils MDR, une plateforme d'apprentissage intégrée ou un programme de formation structuré peut grandement faciliter l’intégration des utilisateurs.
- Support client réactif : Lorsqu'il s'agit de menaces de sécurité potentielles, un support client rapide et efficace assuré par une équipe d'experts est indispensable. La disponibilité d'experts pour guider et assister peut faire toute la différence lors d'une éventuelle violation de sécurité.
Choisir le bon service MDR est primordial dans le paysage numérique actuel. En comprenant les fonctionnalités de base, en discernant les caractéristiques clés et en veillant à des interfaces et un support conviviaux, les organisations peuvent renforcer leurs défenses contre un large éventail de menaces informatiques.
Questions les plus fréquentes sur les services de détection et de réponse gérés (FAQs)
Quels sont les avantages de l’utilisation des services de détection et de réponse gérés ?
Les services de détection et de réponse gérés (MDR) offrent plusieurs avantages pour les entreprises :
- Expertise en sécurité accrue : Les fournisseurs de MDR disposent d’une équipe d’experts en sécurité dédiée à la détection et à la réponse aux menaces, garantissant que votre entreprise est toujours protégée par des spécialistes.
- Chasse proactive aux menaces : Plutôt que d’attendre les alarmes, les services MDR recherchent activement et neutralisent les menaces, assurant la prise en compte des menaces nouvelles et émergentes.
- Surveillance 24h/24 et 7j/7 : Ces services proposent une surveillance continue, permettant une détection et une atténuation rapide des cyberattaques, quel que soit le moment de la journée.
- Rentable : Recruter une équipe de sécurité interne peut être coûteux. Les services MDR offrent une sécurité de haut niveau à une fraction du prix, permettant aux entreprises de consacrer leurs ressources à d’autres domaines.
- Technologies intégrées : Les solutions MDR sont souvent accompagnées des technologies les plus récentes comme l’apprentissage automatique, l’EDR et le SOC, garantissant aux entreprises de toujours bénéficier d’outils de sécurité à la pointe.
Combien coûtent généralement les services de détection et de réponse gérés ?
Le tarif des services MDR varie en fonction de l’envergure de vos opérations, du nombre de terminaux couverts et des fonctionnalités ou intégrations supplémentaires requises. La plupart des fournisseurs fonctionnent sur un modèle d’abonnement, facturant par terminal ou par utilisateur.
Pouvez-vous expliquer les modèles de tarification habituels des services MDR ?
Bien sûr. Les services MDR suivent généralement ces modèles de tarification :
- Par terminal : Les frais sont basés sur le nombre d’appareils ou de terminaux protégés.
- Par utilisateur : Un prix fixe est appliqué en fonction du nombre d’utilisateurs, indépendamment du nombre d’appareils utilisés.
- Forfait mensuel/annuel : Un tarif fixe couvrant l’ensemble des services, idéal pour les grandes entreprises.
Quelle est la fourchette générale de prix pour les services MDR ?
Les prix des services MDR peuvent varier considérablement, allant de seulement $15/utilisateur/mois pour les offres de base à plus de $100/utilisateur/mois pour des solutions d’entreprise complètes.
Quel est le logiciel le moins cher mentionné ?
Le prix de départ de certains outils peut descendre à $7/utilisateur/mois, comme c’est le cas pour Arctic Wolf Managed Detection and Response. Cependant, il est essentiel d’évaluer les fonctionnalités proposées à ce prix.
Quel est le logiciel le plus cher de la liste ?
Sophos et Secureworks peuvent se placer dans la partie haute de la grille tarifaire, notamment si l’on opte pour les fonctionnalités avancées et une couverture étendue.
Existe-t-il des options d’outils MDR gratuites ?
La plupart des outils MDR n’offrent pas de version entièrement gratuite en raison des ressources et de l’expertise importantes nécessaires, mais certains proposent des essais à durée limitée ou des versions basiques avec moins de fonctionnalités. Il est important de se renseigner chez chaque fournisseur pour savoir si des offres promotionnelles ou périodes d’essai existent.
Autres avis sur des outils de cybersécurité
- Outils de gestion des vulnérabilités
- Systèmes de détection et de prévention des intrusions
- Logiciels de cybersécurité
- Services SOC
Résumé
Dans un paysage de cybersécurité en constante évolution, les services de détection et de réponse gérés (MDR) sont devenus une pièce maîtresse pour les entreprises souhaitant une protection robuste contre les cybermenaces. Offrant l’expertise d’équipes dédiées à la sécurité, la chasse proactive aux menaces et une surveillance permanente, les services MDR fournissent un mécanisme de défense complet aux organisations.
Ces outils diffèrent selon les fonctionnalités, les intégrations et les tarifs, ce qui rend essentiel pour les entreprises d’évaluer leurs besoins spécifiques avant de s’engager pour une solution particulière.
Points clés à retenir
- L’expertise compte : Optez pour des services MDR dotés d’une équipe d’experts en sécurité ayant une expérience avérée dans la gestion de diverses cybermenaces. Leur expertise peut considérablement renforcer les mécanismes de défense de votre organisation.
- Intégration et fonctionnalités : Évaluez l’éventail de technologies et d’intégrations proposé par un outil MDR. Recherchez des solutions qui incluent des fonctionnalités EDR, SOC et d’apprentissage automatique, assurant une approche globale de la sécurité.
- Transparence tarifaire : Si le rapport qualité-prix est crucial, comprendre le modèle de tarification – qu’il soit par terminal, par utilisateur ou forfaitaire – vous permettra d’éviter toute dépense imprévue à terme. Il est tout aussi essentiel de prendre en compte les fonctionnalités incluses pour chaque niveau de prix, afin de garantir un vrai retour sur investissement.
Qu'en pensez-vous ?
Dans un paysage de la cybersécurité en constante évolution, de nouveaux services de détection et de réponse managés, innovants, apparaissent continuellement. Même si j’ai cherché à dresser une liste exhaustive, il existe indéniablement d’excellents outils et solutions que j’ai pu omettre.
J’invite tous les lecteurs et professionnels du secteur à partager ici les services ou outils qui n’auraient pas été mentionnés dans cette liste. Vos suggestions et retours enrichiront la valeur de cette ressource et permettront aussi de s’assurer que les organisations aient accès aux meilleures solutions possibles. Hâte de découvrir vos avis !