10 Best IoT Security Platform Shortlist
In today's tech-driven world, securing your IoT devices is more important than ever. You face challenges like data breaches and unauthorized access, and you need reliable solutions to protect your network. IoT security platforms can help you monitor and safeguard your devices, ensuring they operate safely.
I know choosing the right platform can be overwhelming. That's why I've independently tested and reviewed the best options on the market. I'll share my top picks with you, focusing on what they offer and how they can meet your needs.
In this article, you'll find unbiased insights into each platform's features and benefits. My goal is to help you make an informed decision for your team.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best IoT Security Platforms Summary
This comparison chart summarizes pricing details for my top IoT security platform selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for endpoint protection | Not available | From $10/user/month | Website | |
| 2 | Best for secure device connectivity | Not available | Pricing upon request | Website | |
| 3 | Best for managing, processing, and storing data | Not available | From $0.0045/device/month | Website | |
| 4 | Best for continuous security audits | Free trial available | Pricing upon request | Website | |
| 5 | Best for smart device security | Free demo + free trial available | Pricing upon request | Website | |
| 6 | Best for certificate-based security | Free trial + free demo available | Pricing upon request | Website | |
| 7 | Best for robust identity management | Not available | From $9/user/month (min 5 seats) | Website | |
| 8 | Best for embedded system security | Not available | From $5/user/month (min 5 seats) | Website | |
| 9 | Best for industrial network protection | Not available | Pricing upon request | Website | |
| 10 | Best for cellular IoT network security | Not available | From $10/user/month (billed annually) | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best IoT Security Platforms Reviews
Below are my detailed summaries of the best IoT security platforms that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
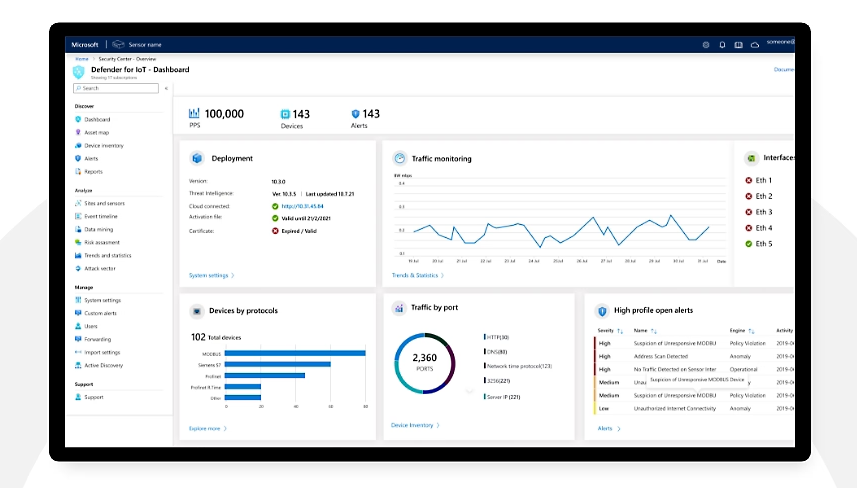
Microsoft Defender for IoT is a comprehensive security solution specifically designed to protect endpoints within IoT environments. It offers a robust defense against various threats targeting IoT devices and is considered best for endpoint protection due to its advanced capabilities in identifying and mitigating risks at the device level.
Why I Picked Microsoft Defender for IoT: I chose Microsoft Defender for IoT after a thorough comparison of different endpoint protection platforms. What made it stand out was its in-depth focus on IoT security, coupled with Microsoft's reputation for reliability.
It incorporates features tailored for IoT devices, making it the best choice for endpoint protection, particularly for those aiming for top-notch security in an IoT ecosystem.
Standout Features & Integrations:
Microsoft Defender for IoT includes state-of-the-art features such as real-time threat detection, vulnerability assessment, and automated response to attacks. It’s equipped with machine learning algorithms that help in identifying new and evolving threats.
Integration with existing security information and event management (SIEM) systems and Microsoft's other security offerings make it a comprehensive tool, ensuring a well-rounded security stance.
Pros and Cons
Pros:
- Advanced threat detection capabilities
- Integrates well with other Microsoft security products
- Specialized in endpoint protection for IoT
Cons:
- Potential compatibility issues with non-Microsoft environments
- Pricing might be higher compared to some competitors
- May require technical expertise to fully utilize
Microsoft Azure Sphere is a comprehensive solution that offers secure and scalable IoT device connectivity. It integrates hardware, software, and cloud services to create a robust security framework for IoT devices, thus earning its reputation as the best for secure device connectivity.
Why I Picked Microsoft Azure Sphere: I chose Microsoft Azure Sphere for its cutting-edge approach to IoT security. By combining hardware, operating system, and cloud services, it provides a unified solution that's hard to match. This integration is what makes it stand out and why I think it's best for secure device connectivity.
The ability to manage and update devices securely without compromising usability provides a strong justification for its selection.
Standout Features & Integrations:
Azure Sphere's standout features include its custom-built hardware with built-in Microsoft security technology, an OS with multiple layers of security, and the Azure Sphere Security Service that ensures secure connectivity. Its integrations with other Azure services provide a cohesive environment for managing and monitoring IoT devices.
Additionally, it can integrate with existing business systems, offering flexibility and efficiency in device management.
Pros and Cons
Pros:
- Flexibility in connecting and managing various IoT devices
- Rich integration capabilities with other Azure services
- Comprehensive security solution integrating hardware, OS, and cloud
Cons:
- Complexity in setup and configuration may require professional assistance
- May require specific hardware compatibility
- Pricing information is not transparent
Google IoT Core is a managed service that allows users to connect, manage, and ingest data from globally dispersed devices. This tool's ability to offer a fully integrated service for all facets of IoT data management aligns with its position as the best for managing, processing, and storing data, bridging the gap between various IoT devices and the data-driven intelligence required by businesses today.
Why I Picked Google IoT Core: I chose Google IoT Core after comparing and judging various tools for IoT data management. Its unified approach to managing, process, and storing data from diverse devices, backed by Google's robust infrastructure, stood out to me.
This complete package is why I think it's best for the use case of managing, processing, and storing data in an IoT environment, giving businesses a comprehensive solution.
Standout Features & Integrations:
Google IoT Core's features include secure device connection and management, rich data processing capabilities, and integration with other Google Cloud services like BigQuery and Dataflow.
These integrations enable users to take advantage of Google's machine learning tools, analytics, and other data processing technologies, providing a cohesive experience within the Google Cloud ecosystem.
Pros and Cons
Pros:
- Robust security features for device connection and management
- Easy integration with other Google Cloud services
- Simplifies the complexity of managing, processing, and storing IoT data
Cons:
- Limited flexibility if you want to use non-Google Cloud services or tools
- Pricing may escalate with a large number of devices
- Can be challenging to implement for those unfamiliar with the Google Cloud Platform
AWS IoT Device Defender is a fully-managed service that provides security metrics and conducts continuous audits for IoT configurations. Its ability to continuously monitor and report on the security posture of devices is why it stands out as the best for continuous security audits, a critical requirement in today's connected landscape.
Why I Picked AWS IoT Device Defender: I chose AWS IoT Device Defender due to its relentless focus on auditing and monitoring IoT devices' security configurations. By selecting this tool, I am prioritizing continuous security monitoring which is essential for detecting deviations from security best practices.
This continuous approach to audits is what makes it different from many others and is why I judge it to be the best for continuous security audits.
Standout Features & Integrations:
AWS IoT Device Defender's standout features include continuous monitoring of security metrics from devices and AWS IoT Core, automatic detection of abnormal behavior, and integration with AWS IoT Core for easier device management.
The integration with other AWS services allows it to function within the AWS ecosystem, enhancing the convenience of setting up and maintaining the security parameters for IoT devices.
Pros and Cons
Pros:
- Highly customizable alerting and reporting
- Integration with AWS IoT Core and other AWS services
- Continuous monitoring and auditing functionality
Cons:
- Specific to AWS ecosystem, limiting flexibility with other providers
- Pricing can become costly depending on the number of devices
- May be complex for smaller organizations or those new to AWS
Palo Alto Networks is a cybersecurity company that offers a comprehensive suite of products aimed at safeguarding smart devices. Their focus on IoT security, threat prevention, and adaptive security measures positions them as an industry leader in protecting smart devices, making them the best for smart device security.
Why I Picked Palo Alto Networks: I chose Palo Alto Networks after carefully comparing various security platforms and determining their effectiveness in the specific area of smart device protection. Its AI-driven threat analysis, real-time monitoring, and the capacity to adapt to evolving threats make it stand out from other security tools.
These attributes contribute to my judgment that Palo Alto Networks is best for smart device security, particularly in an era where the proliferation of connected devices requires robust security measures.
Standout Features & Integrations:
Palo Alto Networks' platform emphasizes real-time threat prevention, advanced AI-driven analysis, and continuous monitoring of smart devices. Its integration capabilities with existing security infrastructures and compatibility with various operating systems help ensure a cohesive defense strategy.
Furthermore, integrations with third-party security information and event management (SIEM) systems provide greater visibility and control.
Pros and Cons
Pros:
- Integration with existing security systems and SIEM platforms
- Comprehensive monitoring of smart devices
- Robust AI-driven threat analysis
Cons:
- May require additional resources for optimal utilization
- Pricing information may be less transparent
- Can be complex to configure
Entrust’s IoT security solution is designed to offer robust certificate-based security, providing the necessary digital assurance for devices within the IoT ecosystem. With the rise of IoT devices in various industries, having a platform that specializes in certificate management becomes crucial, making Entrust the best for this specific security concern.
Why I Picked Entrust: I chose Entrust because of its unique focus on certificate-based security, an essential element for authenticating devices within the IoT landscape. Through evaluating and comparing various platforms, Entrust's capability to manage and secure digital certificates stood out.
This specialization makes it best for organizations looking for a strong solution in certificate-based authentication, ensuring trust in connected devices.
Standout Features & Integrations:
Entrust provides a scalable Public Key Infrastructure (PKI) tailored for IoT, allowing for secure device enrollment and certificate management. The platform integrates well with existing enterprise systems and leading IoT platforms, making it adaptable for various use cases. Its commitment to industry standards and compatibility with multiple certificate formats further solidifies its authority in certificate-based security.
Pros and Cons
Pros:
- Strong integration with enterprise systems
- Scalable PKI tailored for IoT
- Specialized in certificate-based security
Cons:
- Potential compatibility issues with non-standard certificates
- Focused primarily on certificate security, other areas might be less robust
- May be complex for small-scale implementations
Sectigo IoT security platform is designed to safeguard interconnected devices by implementing robust identity management. By focusing on the identification, validation, and securing of devices, it builds a strong defense against unauthorized access.
The platform's best attribute, robust identity management, ensures that only authorized devices and users can interact within the IoT network, thereby enhancing overall security.
Why I Picked Sectigo IoT Security Platform: I chose the Sectigo IoT security platform after evaluating various IoT security tools because of its comprehensive approach to identity management. It uniquely stands out in ensuring that the identity of devices and users is authenticated and secured, providing an added layer of protection against potential threats.
The reason I believe it's best for robust identity management is due to its innovative technology and policies that create an impenetrable defense mechanism against unauthorized access.
Standout Features & Integrations:
Sectigo IoT security platform offers features like digital certificates, embedded device integrity, and strong encryption for complete identity management. These features provide a secure way to validate device identity and integrity, ensuring that only trusted devices can connect to the network.
The platform integrates with existing enterprise systems and various IoT protocols, allowing flexibility and ease of implementation.
Pros and Cons
Pros:
- Advanced encryption and certificate features
- Integration with existing systems
- Comprehensive identity management solution
Cons:
- The cost may be high for small-scale implementations
- May require technical expertise for optimization
- Complexity in setting up certain integrations
Mbed OS is a popular open-source operating system specifically designed to enhance security in embedded systems. The focus on embedded security makes Mbed OS a standout in the realm of IoT, aligning perfectly with its stance as best for embedded system security.
Why I Picked Mbed OS: I chose Mbed OS because of its distinct concentration on security for embedded systems. The embedded systems in IoT devices present unique challenges, and while examining different solutions, Mbed OS's architecture demonstrated specific capabilities to mitigate these challenges.
I found it to be the best for embedded system security due to its robustness, adaptability, and dedicated focus on this specific area.
Standout Features & Integrations:
Mbed OS has an extensive set of features, including support for various microcontroller units (MCUs) and a comprehensive suite of security functionalities. It offers real-time operating system (RTOS) capabilities and integrates with popular development environments and tools, ensuring a streamlined workflow.
The support for industry-standard protocols and extensive documentation makes it highly adaptable for various embedded security applications.
Pros and Cons
Pros:
- Strong integration with popular development tools
- Comprehensive support for various MCUs
- Tailored for embedded system security
Cons:
- Some learning curves for new developers
- Requires technical expertise in embedded systems
- May be overkill for non-embedded use cases
Nozomi Networks is a leading security provider focused on safeguarding industrial networks. The platform offers an array of features to detect and counter threats in critical infrastructure environments, making it the best solution for industrial network protection due to its specialization in securing complex industrial systems.
Why I Picked Nozomi Networks: I chose Nozomi Networks after a careful assessment of tools designed for industrial security. Its commitment to protecting critical infrastructure and ability to adapt to the specific needs of industrial environments made it stand out among the competitors.
Its strong focus on industrial network protection aligns with the growing need for robust security in sectors like manufacturing, energy, and transportation, justifying why it is best for this particular use case.
Standout Features & Integrations:
Nozomi Networks offers features like real-time asset tracking, threat detection, and vulnerability management tailored to industrial networks. Its anomaly detection technology helps in identifying unusual patterns that might signify a breach.
Integration with existing SCADA systems, IT security tools, and industrial protocols ensures a well-rounded defense mechanism.
Pros and Cons
Pros:
- Continuous monitoring and real-time threat detection
- Integration with existing industrial systems and protocols
- Specialized in industrial network environments
Cons:
- Limited applicability outside of industrial contexts
- May require extensive customization for specific industrial setups
- Pricing information is not publicly disclosed
Emnify is a cloud-native communications platform that specializes in secure connectivity for cellular IoT networks. By providing secure data routing and real-time analytics, it ensures the safety and integrity of cellular IoT connections, making it best for cellular IoT network security.
Why I Picked Emnify: I selected Emnify after extensively comparing various platforms designed for IoT security. Its focus on cellular IoT network protection, coupled with powerful analytics and cloud-based architecture, marks it as distinct in the security landscape.
These unique characteristics justify why I think Emnify is best for securing cellular IoT networks, where traditional security measures might not suffice.
Standout Features & Integrations:
Emnify’s platform provides multi-layered security, featuring end-to-end encryption, firewall policies, and real-time monitoring for IoT devices connected via cellular networks. The system is designed to integrate with major cloud providers, such as AWS and Azure, to facilitate efficient management and scaling of IoT networks.
Moreover, APIs are available for custom integrations, extending their reach and adaptability.
Pros and Cons
Pros:
- Easy integrations with major cloud platforms
- Cloud-native architecture facilitates scalability
- Specialized focus on cellular IoT network security
Cons:
- Potentially higher learning curve for those unfamiliar with cellular IoT security measures
- May be over-specialized for broader IT security needs
- Annual billing may not suit all businesses
Other IoT Security Platforms
Here are some additional IoT security platform options that didn’t make it onto my shortlist, but are still worth checking out:
- KeyScaler
For device authentication protocols
- BugProve
For bug tracking and monitoring
- IBM Watson IoT Platform
Good for AI-powered IoT analytics
- Microsoft Azure IoT Hub
Good for reliable device-to-cloud communication
- Forescout
Good for visibility and control over IoT devices
- Cybeats
Good for real-time defense against threats
- Qualys Cloud Platform
Good for continuous security and compliance monitoring
- McAfee Embedded Control
Good for embedded systems security
- Symantec Industrial Control Systems (ICS) Security
Good for protecting industrial control systems
- FortiNAC
Good for network access control and visibility
- Cyberbit
Good for cybersecurity training and simulation
- Trustwave TrustKeeper IoT Security
Good for comprehensive IoT landscape security
- Trend Micro IoT Security
Good for securing IoT environments across devices
- DigiCert IoT Device Manager
Good for managing and securing IoT device certificates
- Kaspersky IoT Infrastructure Security
Good for safeguarding IoT infrastructures
IoT Security Platform Selection Criteria
When selecting the best IoT security platform to include in this list, I considered common buyer needs and pain points like device vulnerability management and network scalability. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Device authentication
- Network monitoring
- Threat detection
- VPN software or data encryption
- Access control
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- AI-driven analytics
- Real-time alerts
- Cloud integration
- Customizable dashboards
- Compliance reporting
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive interface
- Easy navigation
- Customizable settings
- Quick access to features
- Minimal learning curve
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive documentation
- Responsive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multichannel support
- Response time
- Knowledgeable staff
- Availability of FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Transparent pricing model
- Flexible subscription plans
- Cost against features
- ROI potential
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- User satisfaction ratings
- Commonly mentioned pros and cons
- Frequency of updates
- Ease of implementation
- Overall reliability
How to Choose an IoT Security Platform
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the platform handle your growing number of devices? Consider future growth and whether the solution can scale accordingly without requiring major upgrades. |
| Integrations | Does it work with your existing systems? Check compatibility with other tools your team uses to avoid integration headaches. |
| Customizability | Can you tailor it to fit your needs? Look for options that allow adjustments to meet specific workflow requirements. |
| Ease of use | Is the interface user-friendly? Make sure your team can easily navigate and operate the platform without extensive training. |
| Implementation and onboarding | How long will it take to set up? Evaluate the onboarding process, including available support and resources, to ensure a smooth transition. |
| Cost | Does it fit your budget? Compare pricing models and consider the total cost of ownership, including hidden fees or long-term expenses. |
| Security safeguards | Are the security measures sufficient? Ensure the platform provides robust protection against threats and complies with industry standards. |
| Compliance requirements | Does it meet regulatory needs? Verify if the platform supports necessary compliance standards for your industry, like GDPR or HIPAA. |
What Are IoT Security Platforms?
IoT security platforms are tools designed to protect internet-connected devices from threats. IT professionals, network administrators, and security experts typically use these platforms to safeguard devices and ensure secure data transmission. Device authentication, network monitoring, and threat detection capabilities help with managing vulnerabilities and maintaining secure operations. Overall, these tools provide essential protection for connected environments.
Features
When selecting an IoT security platform, keep an eye out for the following key features:
- Device authentication: Confirms the identity of devices connecting to your network, preventing unauthorized access.
- Network monitoring: Continuously observes network traffic to detect unusual activities and potential threats.
- Threat detection: Identifies and alerts users about potential security breaches and vulnerabilities.
- Data encryption: Protects sensitive information by converting it into a secure format during transmission.
- Access control: Manages user permissions to ensure only authorized individuals can access specific data or devices.
- AI-driven analytics: Utilizes artificial intelligence to analyze data and predict potential security risks.
- Compliance reporting: Provides reports to ensure adherence to industry regulations and standards.
- Cloud integration: Connects with cloud services and IoT testing tools to enhance flexibility and data accessibility.
- Customizable dashboards: Allow users to tailor their interface for better visibility and control of security metrics.
- Real-time alerts: Send immediate notifications of security incidents, enabling quick response and mitigation.
Benefits
Implementing an IoT security platform provides several benefits for your team and your business. Here are a few you can look forward to:
- Enhanced security: Protects devices and data from unauthorized access and breaches through features like device authentication and data encryption.
- Improved compliance: Ensures adherence to industry regulations with compliance reporting, reducing legal risks.
- Efficient threat management: Quickly identifies and responds to potential threats using real-time alerts and threat detection capabilities.
- Better network visibility: Offers insights into network activities via network monitoring, helping you detect anomalies faster.
- Increased operational efficiency: Streamlines security management with customizable dashboards and AI-driven analytics.
- Scalability: Supports growing device networks, ensuring security measures expand with your business needs.
- Cost savings: Reduces potential financial losses from security breaches and non-compliance penalties.
Costs & Pricing
Selecting an IoT security platform requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in IoT security platform solutions:
Plan Comparison Table for IoT Security Platforms
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic threat detection, limited device support, and community support. |
| Personal Plan | $10-$30/user/month | Device authentication, network monitoring, and email support. |
| Business Plan | $50-$100/user/month | Advanced threat detection, data encryption, and phone support. |
| Enterprise Plan | $150-$300/user/month | Customizable dashboards, compliance reporting, and a dedicated account manager. |
IoT Security Platforms FAQs
Here are some answers to common questions about IoT security platforms:
How does an IoT security platform handle software updates?
IoT security platforms often support over-the-air updates to apply security patches efficiently. This ensures your devices stay protected against vulnerabilities as new threats emerge. Make sure your chosen platform offers timely updates and a straightforward update process to maintain security.
What user access controls are available in IoT security platforms?
IoT security platforms typically offer strong authentication and authorization protocols like OAuth2 and role-based access control. These controls prevent unauthorized access to devices and data, safeguarding your network. Evaluate the flexibility and strength of these controls to suit your needs.
Are security features enabled by default in IoT platforms?
Many IoT security platforms enable essential security features by default, such as robust initial passwords and disabled functions that could pose risks. This is crucial for reducing vulnerabilities from the start. Verify that your platform of choice follows this practice for enhanced security.
What overall security framework do IoT platforms use?
IoT platforms typically employ multi-layered security strategies, including defense-in-depth and zero trust principles. These frameworks are designed to address the unique vulnerabilities of IoT systems. Understanding the framework a platform uses can help you evaluate its security effectiveness.
Can IoT security platforms be integrated with other tools and systems?
Yes, many IoT security platforms offer integration capabilities with existing business systems, third-party applications, and other IoT analytics platforms. This flexibility ensures that the IoT security system can fit into your existing technological infrastructure.
What’s Next:
If you're in the process of researching IoT security platforms, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.