Best Endpoint Management Software Shortlist
Managing multiple devices and securing data is a challenge you face every day. Endpoint management software can help you tackle these issues by giving you control over your network's endpoints.
I test and review software independently, aiming to give you an unbiased view of the best options available. In my experience, finding the right solution can make a big difference in your team's efficiency and security.
In this article, I'll share my top picks for endpoint management software. You'll learn about features, benefits, and what sets each tool apart. Let's find the right solution for your needs.
Why Trust Our Software Reviews
We’ve been testing and reviewing software since 2023. As tech leaders ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different tech use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our software review methodology.
Best Endpoint Management Software Summary
This comparison chart summarizes pricing details for my top endpoint management software selections to help you find the best one for your budget and business needs.
| Tool | Best For | Trial Info | Price | ||
|---|---|---|---|---|---|
| 1 | Best for compliance UEM workflows | 14-day trial available | Pricing available upon request | Website | |
| 2 | Best for network segmentation control | 14-day free trial + free demo available | From $7/user/month (billed annually) | Website | |
| 3 | Best for user privilege management | Free demo available | Pricing upon request | Website | |
| 4 | Best for identity-based access controls | Free plan available | From $5/user/month (billed annually) | Website | |
| 5 | Best for those needing proactive endpoint protection | Free trial + free demo available | Pricing upon request | Website | |
| 6 | Best for remote IT teams wanting centralized control | Free plan available | Pricing upon request | Website | |
| 7 | Best for businesses needing unified device management | 14-day free trial + free demo available | From $2.20/device/month (billed annually) | Website | |
| 8 | Best for real-time visibility and rapid remediation | Free trial available | Pricing upon request | Website | |
| 9 | Best for businesses invested in the Microsoft ecosystem | 30-day free trial available | From $10/user/month (billed annually) | Website | |
| 10 | Best for robust threat detection capabilities | Not available | From $30/user/month (billed annually) | Website |
-

Freshservice
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.6 -

Deel IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.9 -

Rippling IT
Visit WebsiteThis is an aggregated rating for this tool including ratings from Crozdesk users and ratings from other sites.4.8
Best Endpoint Management Software Reviews
Below are my detailed summaries of the best endpoint management software that made it onto my shortlist. My reviews offer a detailed look at the key features, pros & cons, integrations, and ideal use cases of each tool to help you find the best one for you.
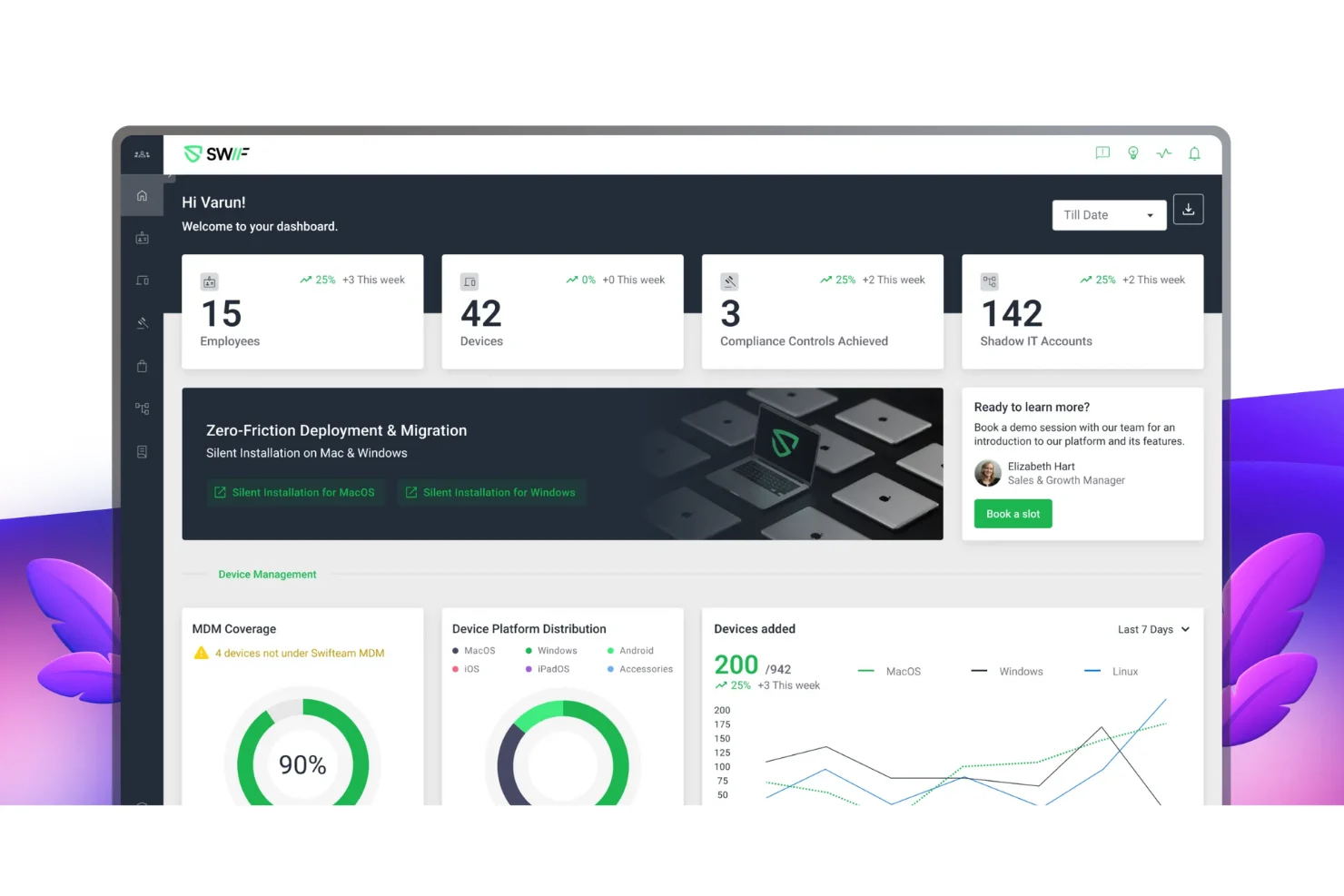
Swif.ai is an endpoint management platform that lets you automate device compliance, deploy software silently, and enforce policies across Windows, macOS, and Linux devices from a single dashboard.
Who Is Swif.ai Best For?
IT teams in regulated industries who need to automate device compliance checks across diverse operating systems.
Why I Picked Swif.ai
I picked Swif.ai as one of the best because I can automate device compliance audits across all endpoints without manual intervention. My team uses its policy engine to schedule recurring compliance checks and generate audit-ready reports. I also like that Swif.ai flags non-compliant devices in real time, so we can act quickly.
Swif.ai Key Features
- Multi-OS support: Manage Windows, macOS, and Linux devices from a single dashboard.
- Remote script execution: Run scripts on endpoints without user interaction or disruption.
- Role-based access control: Assign granular permissions to IT staff based on job function.
- Automated software deployment: Push applications and updates to devices across your environment.
Swif.ai Integrations
Swif.ai offers native integrations with Okta, Azure Active Directory, Google Workspace, Zoom, Deel, Vanta, Drata, Thoropass, Sprinto, Delve, Comply Jet, and SecureFrame. An API is available for custom integrations.
Pros and Cons
Pros:
- Real-time device inventory and status tracking
- Provides automated compliance audit workflows
- Offers silent deployment for large device fleets
Cons:
- Limited advanced reporting customization options
- No free-forever plan is available
NordLayer is a network security platform designed to protect your business's digital assets. It offers cloud-based solutions like business VPN, Zero Trust Network Access (ZTNA), and threat protection to ensure secure connections for your team.
Why I Picked NordLayer:
NordLayer's network segmentation feature lets you divide your network into smaller segments, assigning specific access permissions to different teams or departments. This means you can control who accesses particular resources, reducing the risk of unauthorized access and potential data breaches.
Standout Features & Integrations:
NordLayer has a cloud firewall, which acts as a barrier between your network and potential threats. It filters incoming and outgoing traffic based on predefined security rules, preventing unauthorized access and protecting your company's data. It also offers deep packet inspection, DNS filtering, multi-factor authentication, Zero Trust Network Access, threat intelligence, and password management. Some integrations include Entra ID, Okta, OneLogin, JumpCloud, Google Workspace, Google Cloud, IBM Cloud, and AWS.
Pros and Cons
Pros:
- Provides robust VPN support
- Security measures like AES-256 encryption and multi-factor authentication
- Utilizes a zero-trust framework
Cons:
- Number of available server locations could be expanded
- Server setup can be complex
New Product Updates from NordLayer
NordLayer Browser Adds Policy Prioritization
NordLayer Browser now evaluates security policies top-down by priority, applying the first matching rule to streamline enforcement and reduce ambiguity. For more information, visit NordLayer's official site.
Netwrix Endpoint Management is a security-focused solution designed to help organizations protect, configure, and monitor endpoints across their network. It supports multiple operating systems and deployment options, making it suitable for varied IT environments while maintaining strong compliance controls.
Why I Picked Netwrix:
I chose Netwrix for its strong data protection and compliance capabilities. Its endpoint data loss prevention tools help safeguard sensitive information, while its compliance monitoring ensures systems stay aligned with regulatory requirements like PCI DSS and HIPAA. I also value its user privilege management, which helps enforce least privilege policies and control local admin rights—both critical for preventing unauthorized access. Additionally, its peripheral device control features let you manage and restrict USB drives and other external devices, reducing the risk of malicious data exfiltration.
Standout Features & Integrations:
Key features include lifecycle management for configuring and maintaining endpoints over time, continuous compliance enforcement that detects unauthorized changes, and application deployment tools that allow precise control over installed software. Integrations cover the broader Netwrix ecosystem, including Netwrix Auditor, Access Analyzer, 1Secure DSPM, Directory Manager, Privilege Secure, and Endpoint Protector, enabling a more unified security and compliance strategy.
Pros and Cons
Pros:
- Supports Linux and macOS
- Robust compliance and audit capabilities
- Comprehensive device and peripheral control
Cons:
- Lacks network DLP and mail server integration
- Uninstallation process can be complex
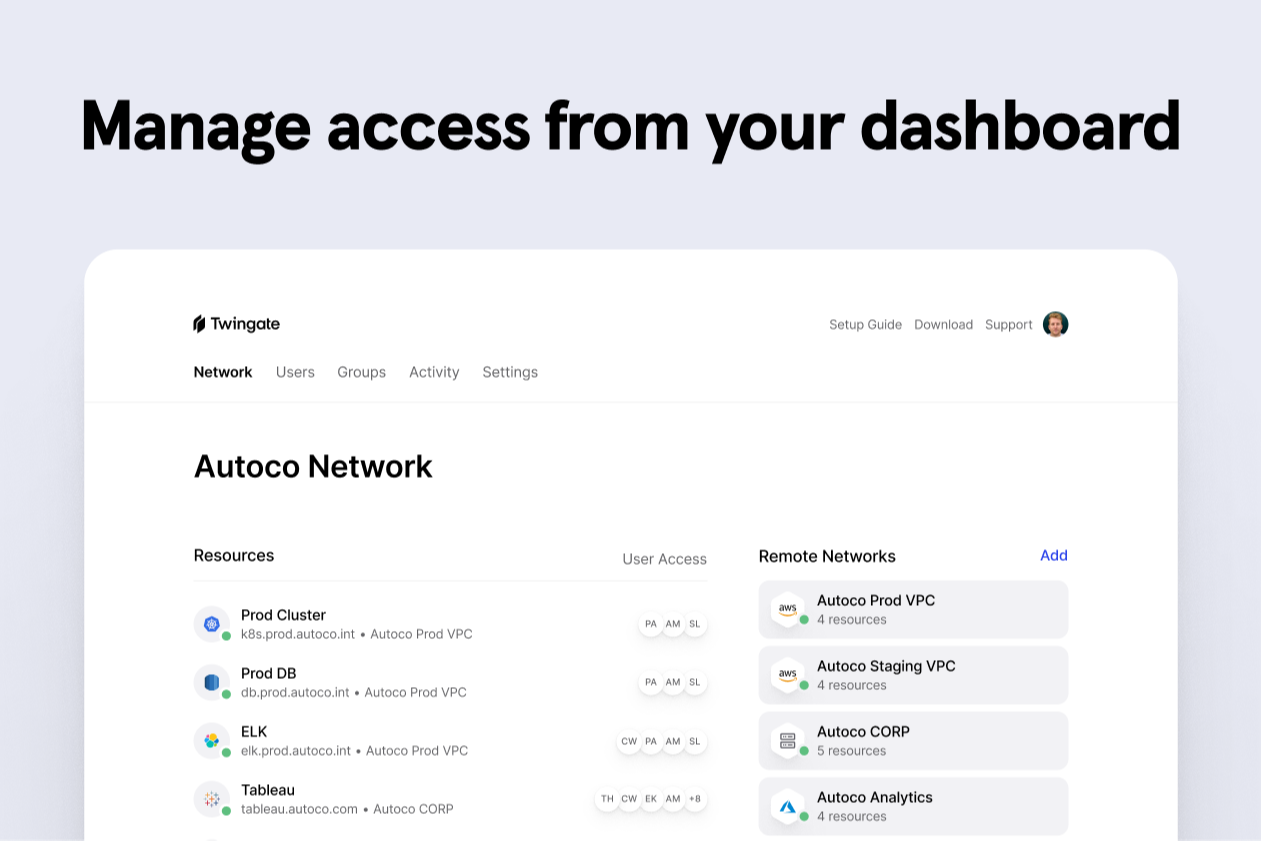
Twingate is a zero trust network access solution for endpoint management that lets you control, secure, and monitor access to on-prem and cloud resources from any device.
Who Is Twingate Best For?
Twingate is a strong fit for IT and security teams managing remote or distributed workforces who need strict, identity-driven access controls without relying on traditional VPNs.
Why I Picked Twingate
Twingate earns its spot on my shortlist because of how tightly it ties access decisions to verified user identity. I particularly like that it enforces least-privilege access at the resource level, so even if a device is compromised, lateral movement across the network is blocked. Its device posture checks add another layer, letting my team gate access based on real endpoint health signals like OS version or firewall status.
Twingate Key Features
- Split tunneling: Route only specific traffic through Twingate while letting other traffic go directly to the internet, giving you precise control over what flows through your secure access layer.
- Audit logs: Track every user access attempt, connection event, and admin change with detailed, exportable logs that support compliance reviews and incident investigation.
- Just-in-time (JIT) access requests: Let users request temporary access to specific resources, with approval workflows that automatically expire access after a set window.
- DNS filtering: Block malicious domains, enforce content policies, and encrypt DNS traffic across endpoints using built-in filtering rules and threat intelligence feeds.
Twingate Integrations
Twingate offers native integrations with Okta, Azure Active Directory, Google Workspace, and OneLogin for identity and access management. An API is available for custom integrations.
Pros and Cons
Pros:
- Zero trust network architecture replaces VPN
- Granular session logging and audit trails
- Policy enforcement at individual resource level
Cons:
- Cannot manage OS updates or patching directly
- Advanced policy automation only on paid plans
Heimdal is an advanced endpoint protection platform that employs a proactive approach to IT security. By deploying a multilayered defense system, it anticipates and mitigates potential threats before they cause damage, making it perfect for those needing proactive protection.
Why I Picked Heimdal:
Heimdal earned its place on this list because of its proactive approach to cybersecurity. Rather than reacting to threats as they occur, Heimdal anticipates them, enabling it to prevent breaches before they happen.
This proactive stance sets it apart from many alternatives, and it's why I believe it's best suited for those in need of anticipatory protection.
Standout Features & Integrations:
Heimdal's notable features include automated patch management, firewall control, and proactive antivirus protection. Additionally, it integrates with a wide variety of platforms, including Windows, macOS, and various server systems, broadening its usability across different IT environments.
Pros and Cons
Pros:
- Includes an automated patch management feature
- Provides extensive platform compatibility
- Offers a proactive approach to cybersecurity
Cons:
- Limited mobile device support
- Advanced features might require a steep learning curve for new users
- The user interface could be more intuitive
Action1 is an endpoint management tool that empowers remote IT teams with centralized control over devices. It strikes a fine balance between providing granular control and maintaining a user-friendly interface, making it an ideal pick for remote IT teams.
Why I Picked Action1:
I chose Action1 due to its strong focus on supporting remote IT teams, offering them a high degree of control over their devices without becoming too complex. Its design prioritizes centralized command, which is a boon for remote teams who need to manage numerous endpoints dispersed geographically.
Standout Features & Integrations:
Action1 offers a cloud-based interface, remote access control, and patch management among its standout features. It has robust integrations with the Windows Update service, enabling patch management across the board.
Pros and Cons
Pros:
- Robust integration with Windows Update for patch management
- Cloud-based interface allows easy access from anywhere
- Ideal for remote IT teams seeking centralized control
Cons:
- Pricing could be more competitive for smaller teams
- Some advanced features might require a steep learning curve
- More suited to Windows environments
Hexnode is a comprehensive unified endpoint management solution that allows businesses to secure and manage their digital devices from a single platform. Given the increasing device diversity in the modern workplace, Hexnode is particularly suitable for businesses requiring robust and flexible device management capabilities.
Why I Picked Hexnode:
I picked Hexnode because of its breadth of device support, including iOS, Android, Windows, macOS, Linux, and even FireOS. This wide-ranging compatibility, coupled with its comprehensive feature set, makes Hexnode a compelling choice for businesses in need of a unified device management solution.
Standout Features & Integrations:
Hexnode offers a range of standout features, such as remote device management, kiosk mode, mobile application management, and comprehensive security policies. These features are crucial for businesses to efficiently manage and secure their devices. On the integration front, Hexnode works with popular enterprise solutions like Slack, Azure, and G Suite, further enhancing its overall utility.
Pros and Cons
Pros:
- Affordable pricing
- Comprehensive device management features
- Wide range of device support
Cons:
- Support response time can be improved
- Customization options may be limited
- Interface can be a bit overwhelming
For teams seeking a reliable solution in endpoint management software, HCL BigFix presents an AI-powered platform designed to optimize IT operations and security. This tool is particularly appealing to industries like healthcare, government, and finance, where maintaining compliance and security is critical. With its capabilities in automated device management and vulnerability remediation, HCL BigFix addresses the challenges of managing extensive IT infrastructures while ensuring continuous compliance and security.
Why I Picked HCL BigFix
I picked HCL BigFix for its unique ability to deliver real-time visibility and rapid remediation across diverse IT environments. Its AI-driven automation streamlines endpoint management tasks, reducing the time needed for vulnerability remediation and compliance checks. The platform's comprehensive approach to continuous compliance monitoring and software asset management makes it an ideal choice for organizations that prioritize robust security and efficient IT operations. By integrating these features, HCL BigFix effectively addresses the complexities of endpoint management and security.
HCL BigFix Key Features
In addition to real-time visibility and rapid remediation, HCL BigFix offers:
- Unified Endpoint Management: This feature allows your team to manage all endpoints across on-premise, cloud, and hybrid environments from a single platform.
- Automated Patch Management: It automates patching, ensuring all devices are up to date with the latest security patches and reducing vulnerability exposure.
- Vulnerability Assessment: This feature provides continuous monitoring and assessment of endpoint vulnerabilities, helping to prioritize and address risks swiftly.
- Software Asset Management: It provides detailed insights into software usage and compliance, enabling better license management and reducing unnecessary costs.
HCL BigFix Integrations
Integrations include ServiceNow, IVR, and Forescout, with options for custom integrations through APIs. Additionally, users can access extensive resources and community support for integration setup and troubleshooting.
Pros and Cons
Pros:
- Efficient in managing software deployment and asset management across platforms
- Supports a wide range of operating systems and environments
- Offers robust security features for comprehensive endpoint protection
Cons:
- Mixed experiences with customer support and customization
- Patching for certain systems, like RedHat Linux, can be challenging
Microsoft Intune is a cloud-based service that focuses on mobile device management (MDM) and mobile application management (MAM). As part of the Microsoft 365 product suite, it is a natural fit for businesses heavily invested in the Microsoft ecosystem, streamlining the management of their devices and applications.
Why I Picked Microsoft Intune:
The decision to include Microsoft Intune on this list was driven by its integration with other Microsoft 365 applications, making it a unique choice for businesses already invested in the Microsoft ecosystem. What sets it apart is its tight-knit connection with familiar office tools, simplifying management tasks for IT departments.
It's particularly beneficial for businesses committed to Microsoft's range of products, as it allows for a more coordinated approach to device and application management.
Standout Features & Integrations:
Microsoft Intune provides robust device and app management features such as policy enforcement, app protection policies, and mobile threat defense. The integrations are also noteworthy, especially with other Microsoft products like Office 365, Teams, and Azure Active Directory, which further strengthens the convenience factor for businesses using Microsoft tools.
Pros and Cons
Pros:
- Provides threat defense capabilities
- Robust device and application management features
- Excellent integration with other Microsoft products
Cons:
- Some features might be complex for small businesses
- May require time for deployment and configuration
- More suitable for businesses already using Microsoft tools
FortiClient Endpoint Agent is a powerhouse when it comes to endpoint security, providing a diverse set of features to keep your network safe. With its robust threat detection capabilities, it can rapidly identify and mitigate risks, making it ideal for environments where security is paramount.
Why I Picked FortiClient Endpoint Agent:
I selected FortiClient Endpoint Agent for this list due to its comprehensive security solutions and its ability to rapidly detect a wide range of threats. Its standout ability to swiftly recognize and neutralize potential risks makes it best suited for businesses that need reliable and robust threat detection.
Standout Features & Integrations:
FortiClient Endpoint Agent delivers features such as automated behavior-based protection, secure remote access, and vulnerability scanning, ensuring your network stays protected. Its ability to integrate with Fortinet Security Fabric broadens the protection and improves threat intelligence.
Pros and Cons
Pros:
- Offers secure remote access
- Delivers automated behavior-based protection
- Provides robust threat detection
Cons:
- Pricing could be more competitive
- Steep learning curve for new users
- The user interface could be more intuitive
Other Endpoint Management Software
Here are some additional endpoint management software options that didn’t make it onto my shortlist, but are still worth checking out:
- Check Point SandBlast Agent
For comprehensive malware protection
- Sophos Endpoint Protection
For small businesses needing advanced security
- Altera
For IT departments seeking an all-in-one solution
- Kandji
For Mac-centric organizations
- Scalefusion
For comprehensive device security
- NinjaOne
For Managed Service Providers (MSPs)
- ManageEngine Endpoint Central
For automating regular endpoint management tasks
- Akamai
Good for businesses seeking a Zero Trust security approach
- Malwarebytes
Good for businesses needing advanced threat detection and remediation
- Cisco Meraki
Good for organizations requiring cloud-managed IT solutions
- Jamf Pro
Good for comprehensive Apple device management
- IBM Security MaaS360
Good for businesses requiring AI-powered insights
- Quest KACE
Good for IT teams requiring automated endpoint management
- Workspace ONE (VMware)
Good for managing and securing any app on any device
- Citrix Endpoint Management
Good for businesses needing secure digital workspaces
- Absolute Secure Endpoint
Good for organizations seeking resilient endpoint security
- Cisco Secure Endpoint
Good for organizations needing threat-centric endpoint protection
Other IT Security Solutions Reviews
Endpoint Management Software Selection Criteria
When selecting the best endpoint management software to include in this list, I considered common buyer needs and pain points like device security and ease of integration. I also used the following framework to keep my evaluation structured and fair:
Core Functionality (25% of total score)
To be considered for inclusion in this list, each solution had to fulfill these common use cases:
- Manage device inventory
- Deploy software updates
- Enforce security policies
- Monitor device health
- Provide remote support
Additional Standout Features (25% of total score)
To help further narrow down the competition, I also looked for unique features, such as:
- Automated threat detection
- Cross-platform compatibility
- Customizable dashboards
- Integration with third-party apps
- Advanced reporting tools
Usability (10% of total score)
To get a sense of the usability of each system, I considered the following:
- Intuitive user interface
- Easy navigation
- Minimal learning curve
- Responsive design
- Clear layout and design
Onboarding (10% of total score)
To evaluate the onboarding experience for each platform, I considered the following:
- Availability of training videos
- Interactive product tours
- Access to webinars
- Comprehensive templates
- Supportive chatbots
Customer Support (10% of total score)
To assess each software provider’s customer support services, I considered the following:
- 24/7 availability
- Multichannel support
- Knowledgeable staff
- Response time
- Availability of FAQs
Value For Money (10% of total score)
To evaluate the value for money of each platform, I considered the following:
- Competitive pricing
- Feature set for price
- Scalability of pricing plans
- Free trial availability
- Discounts for annual billing
Customer Reviews (10% of total score)
To get a sense of overall customer satisfaction, I considered the following when reading customer reviews:
- User satisfaction ratings
- Commonly mentioned pros
- Commonly mentioned cons
- Frequency of updates
- Overall recommendation rate
How to Choose Endpoint Management Software
It’s easy to get bogged down in long feature lists and complex pricing structures. To help you stay focused as you work through your unique software selection process, here’s a checklist of factors to keep in mind:
| Factor | What to Consider |
|---|---|
| Scalability | Can the software grow with your organization? Consider current needs and future expansion. Look for flexible user additions and adaptable pricing. |
| Integrations | Does it connect with your existing systems? Check compatibility with your current IT infrastructure and third-party applications. |
| Customizability | Can you tailor it to fit your workflows? Seek options for adjusting settings, layouts, and reports to match your processes. |
| Ease of use | Is it user-friendly for your team? Evaluate the learning curve and interface simplicity to ensure quick adoption. |
| Implementation and onboarding | How smooth is the setup process? Investigate available support during installation and initial training resources. |
| Cost | Does it fit your budget? Compare pricing models, hidden fees, and potential long-term costs against your financial plan. |
| Security safeguards | Are your devices protected? Look for encryption, regular updates, and compliance with data protection standards. |
What Is Endpoint Management Software?
Endpoint management software is a tool that helps IT teams manage and secure devices connected to a network. IT professionals and system administrators commonly use these tools to ensure security and compliance across all devices. Device management, security enforcement, and software updates help with maintaining control and protection over network endpoints. For organizations seeking broader protection, unified threat management solutions can complement endpoint tools by addressing network-wide security challenges. Overall, these tools provide peace of mind by safeguarding data and simplifying device management.
Features
When selecting endpoint management software, keep an eye out for the following key features:
- Device inventory management: Keeps track of all devices in your network, providing a comprehensive view of assets for better control and organization.
- Software deployment: Enables automatic installation and updates of software across devices, saving time and ensuring all systems are up-to-date.
- Security policy enforcement: Implements and monitors security protocols to protect devices from threats and ensure compliance with company standards.
- Remote support: Offers tools for IT teams to access and troubleshoot devices remotely, reducing downtime and improving efficiency.
- Automated threat detection: Identifies and alerts on potential security risks, allowing for quick response and protection of data.
- Cross-platform compatibility: Supports a variety of operating systems and devices, ensuring seamless integration within diverse IT environments.
- Customizable dashboards: Provides flexible reporting and monitoring options tailored to specific organizational needs.
- Integration with third-party apps: Facilitates connection with other software solutions, enhancing functionality and workflow efficiency.
- Advanced reporting tools: Delivers detailed insights and analytics on device performance and security, aiding in informed decision-making.
- User-friendly interface: Ensures ease of use and quick adoption by IT teams, minimizing training time and maximizing productivity.
Benefits
Implementing endpoint management software provides several benefits for your team and your business. Here are a few you can look forward to:
- Increased security: Automated threat detection and security policy enforcement help protect devices from vulnerabilities and data breaches.
- Time savings: Features like software deployment and remote support reduce manual tasks and speed up resolution times for IT issues.
- Improved compliance: Ensures devices meet organizational and regulatory standards through consistent monitoring and enforcement.
- Better device tracking: Device inventory management provides a clear view of all assets, aiding in efficient resource allocation and planning.
- Enhanced productivity: User-friendly interfaces and customizable dashboards allow IT teams to work more efficiently with minimal learning curves.
- Cost efficiency: By automating processes and reducing downtime, organizations can lower operational costs and maximize their IT budget.
- Informed decision-making: Advanced reporting tools offer insights into device performance and security, supporting strategic planning and improvements.
Costs and Pricing
Selecting endpoint management software requires an understanding of the various pricing models and plans available. Costs vary based on features, team size, add-ons, and more. The table below summarizes common plans, their average prices, and typical features included in endpoint management software solutions:
Plan Comparison Table for Endpoint Management Software
| Plan Type | Average Price | Common Features |
|---|---|---|
| Free Plan | $0 | Basic device management, limited software deployment, and essential security features. |
| Personal Plan | $5-$25/user/month | Device management, remote support, software updates, and basic reporting tools. |
| Business Plan | $25-$50/user/month | Advanced device management, automated threat detection, customizable dashboards, and integration options. |
| Enterprise Plan | $50+/user/month | Comprehensive security features, cross-platform compatibility, detailed analytics, and premium support. |
Endpoint Management Software FAQs
Here are some answers to common questions about endpoint management software:
How does endpoint management software improve security?
Endpoint management software enhances security by enforcing policies that protect devices from unauthorized access and threats. It manages software updates and patches, reducing vulnerabilities. It also provides tools for monitoring and responding to security incidents, ensuring your network remains secure.
Can endpoint management software integrate with existing systems?
Yes, most endpoint management tools offer integrations with existing IT infrastructure. They can connect with security systems, help desks, and other IT management tools. Check compatibility with your current systems to ensure smooth operation and maximize efficiency.
What factors should I consider when choosing endpoint management software?
Consider factors like scalability, integrations, and ease of use. Evaluate the software’s ability to meet your organization’s current and future needs. Look for solutions that offer strong security features and are easy for your team to adopt.
How does endpoint management software help with compliance?
Endpoint management software aids compliance by monitoring devices for adherence to industry standards and regulations. It provides audit trails and reports, helping you demonstrate compliance. This reduces the risk of penalties and ensures your organization meets legal requirements.
What support options are typically available with endpoint management software?
Support options vary but often include 24/7 availability, online chat, phone support, and a knowledge base. Some vendors offer dedicated account managers or premium support packages. Consider your team’s needs and the level of support required when evaluating software options.
How do I evaluate the cost-effectiveness of endpoint management software?
Assess cost-effectiveness by comparing pricing plans against the features offered. Consider the total cost of ownership, including any add-ons or hidden fees. Evaluate whether the software’s benefits justify the investment based on your organization’s specific needs and budget.
What’s Next:
If you're in the process of researching endpoint management software, connect with a SoftwareSelect advisor for free recommendations.
You fill out a form and have a quick chat where they get into the specifics of your needs. Then you'll get a shortlist of software to review. They'll even support you through the entire buying process, including price negotiations.